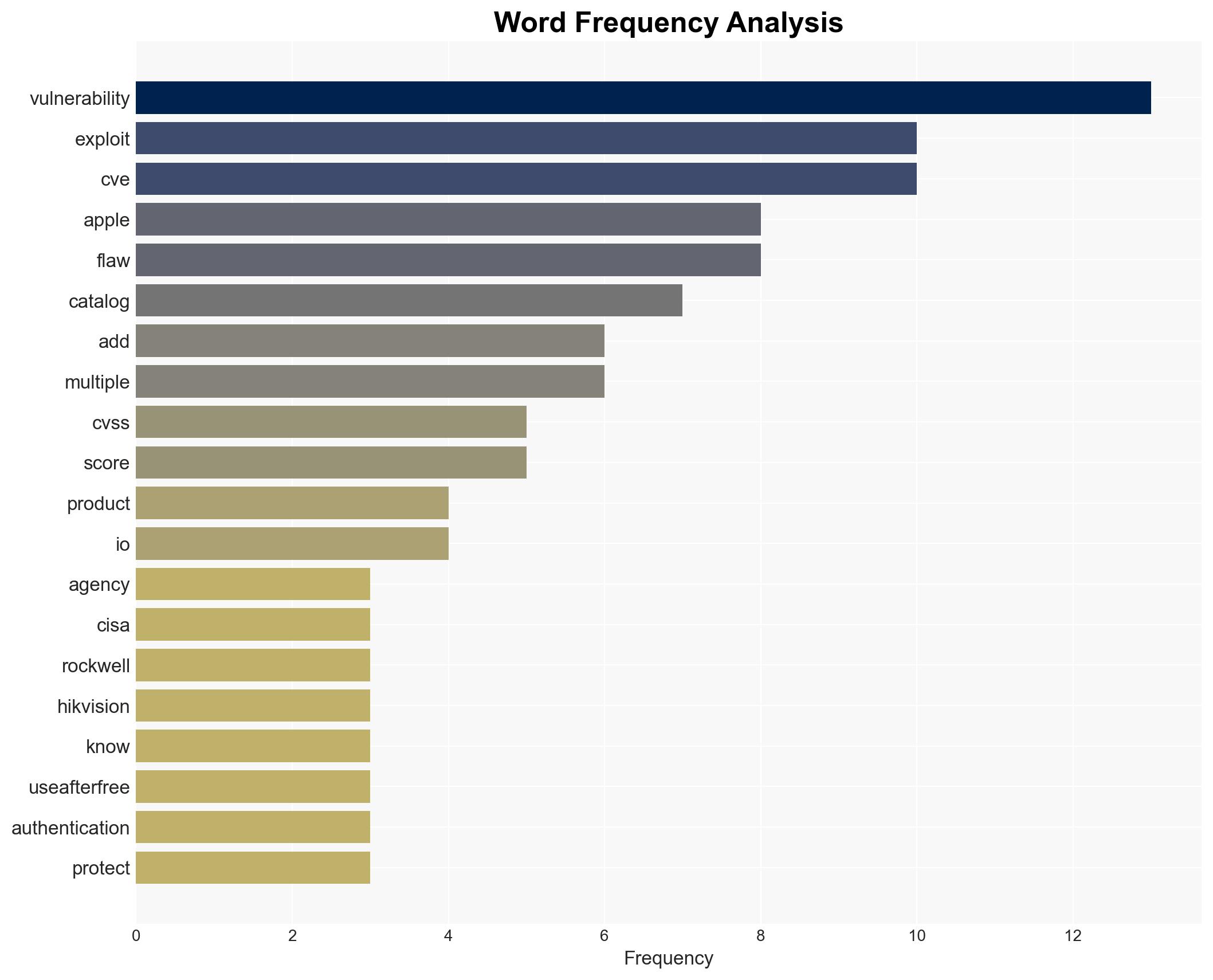
CISA Includes Vulnerabilities from Apple, Rockwell, and Hikvision in Its Exploited Vulnerabilities List
Published on: 2026-03-06
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
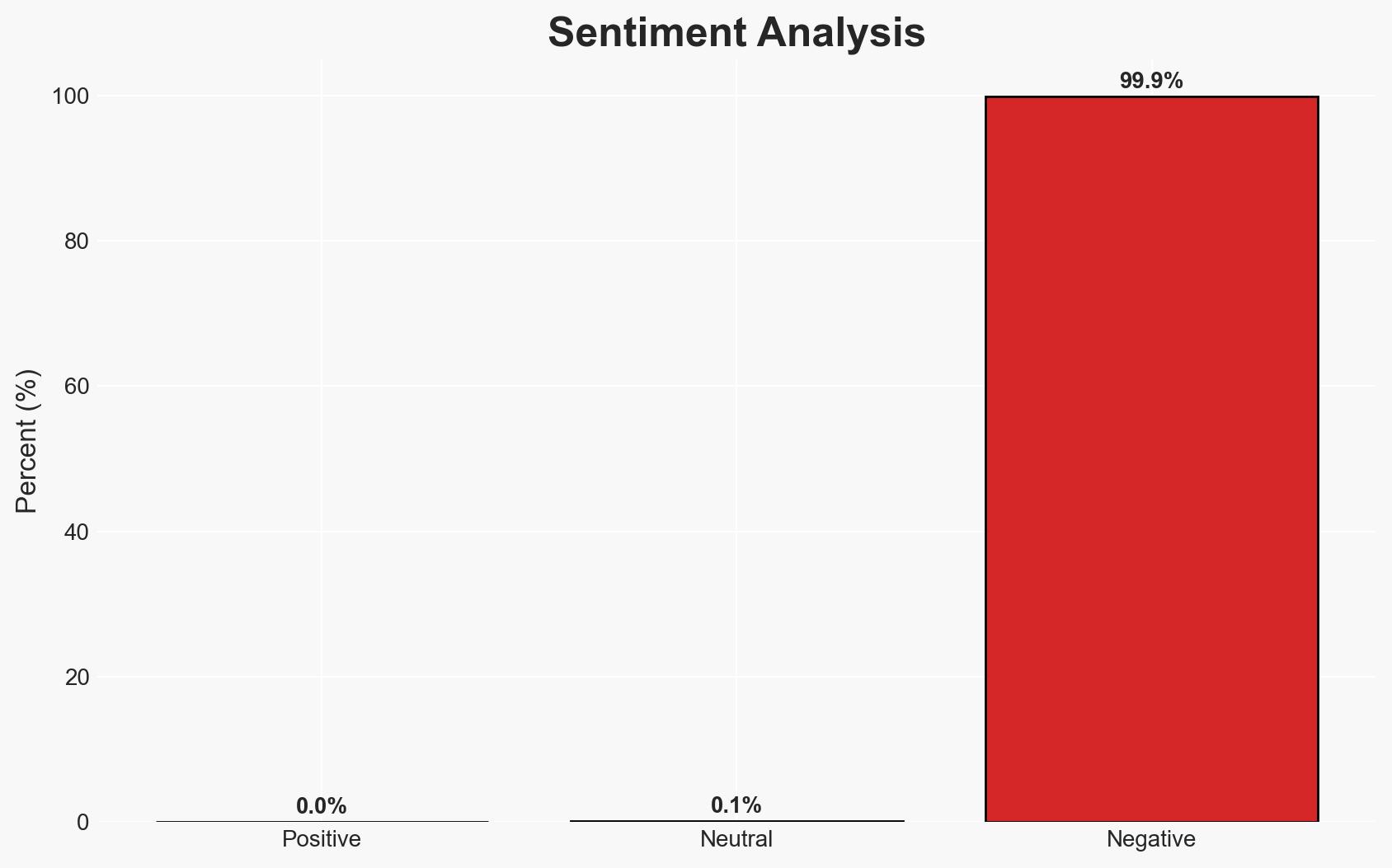
Intelligence Report: US CISA adds Apple Rockwell and Hikvision flaws to its Known Exploited Vulnerabilities catalog
1. BLUF (Bottom Line Up Front)
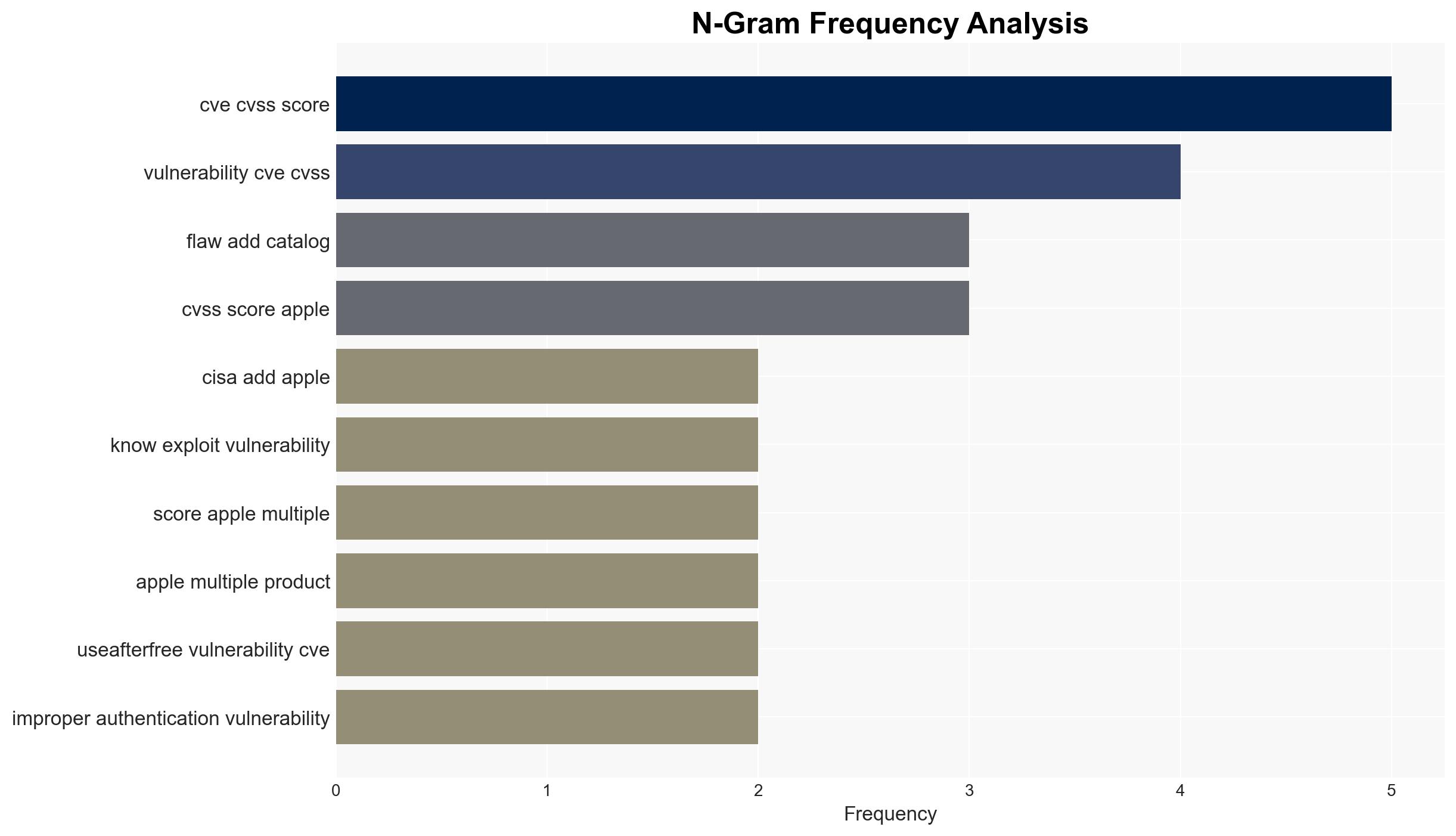
The addition of vulnerabilities from Apple, Rockwell, and Hikvision to the CISA Known Exploited Vulnerabilities catalog highlights ongoing threats to cybersecurity across multiple sectors. The most likely hypothesis is that these vulnerabilities are being actively exploited by both state and non-state actors, posing significant risks to industrial, consumer, and national security. This assessment is made with moderate confidence due to the presence of known exploitation activities and the involvement of sophisticated threat actors.
2. Competing Hypotheses
- Hypothesis A: The vulnerabilities are being exploited primarily by state-sponsored actors for espionage and strategic advantage. This is supported by the involvement of Chinese threat actors and the targeting of Ukrainian entities. However, the full scope of state involvement is uncertain.
- Hypothesis B: The vulnerabilities are being exploited by a mix of state and non-state actors, including cybercriminals, for financial gain and broader strategic objectives. Evidence includes the use of exploit kits by surveillance vendors and financial threat actors, indicating a diverse range of exploiters.
- Assessment: Hypothesis B is currently better supported due to the diversity of actors involved and the range of motivations, from financial to strategic. Indicators such as the reuse of zero-day exploits and cross-sector targeting could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The vulnerabilities are not yet patched in all affected systems; threat actors have the capability to exploit these vulnerabilities effectively; CISA’s catalog reflects the most critical current threats.
- Information Gaps: Specific details on the extent of exploitation and the identity of all actors involved; comprehensive data on the impact of these vulnerabilities on affected systems.
- Bias & Deception Risks: Potential bias in threat actor attribution; deception by threat actors to obfuscate true intent or origin.
4. Implications and Strategic Risks
The exploitation of these vulnerabilities could lead to increased cyber incidents, affecting critical infrastructure, private sector operations, and consumer data security. The situation may evolve with new threat actor tactics and broader geopolitical tensions.
- Political / Geopolitical: Escalation in cyber tensions between the US and China; potential diplomatic strains with countries implicated in exploit use.
- Security / Counter-Terrorism: Increased risk of cyber-attacks on critical infrastructure, requiring enhanced defensive measures.
- Cyber / Information Space: Potential for widespread misinformation or disinformation campaigns leveraging compromised systems.
- Economic / Social: Possible economic disruptions due to compromised industrial systems; erosion of public trust in digital security.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Urgent patching of affected systems; enhanced monitoring of known threat actor activities; public awareness campaigns on cybersecurity hygiene.
- Medium-Term Posture (1–12 months): Strengthen international cyber cooperation; invest in advanced threat detection and response capabilities; develop public-private partnerships for cybersecurity resilience.
- Scenario Outlook:
- Best: Rapid patch adoption and international cooperation mitigate threats.
- Worst: Widespread exploitation leads to significant infrastructure disruptions and geopolitical tensions.
- Most-Likely: Continued exploitation by diverse actors with moderate impact on targeted sectors.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
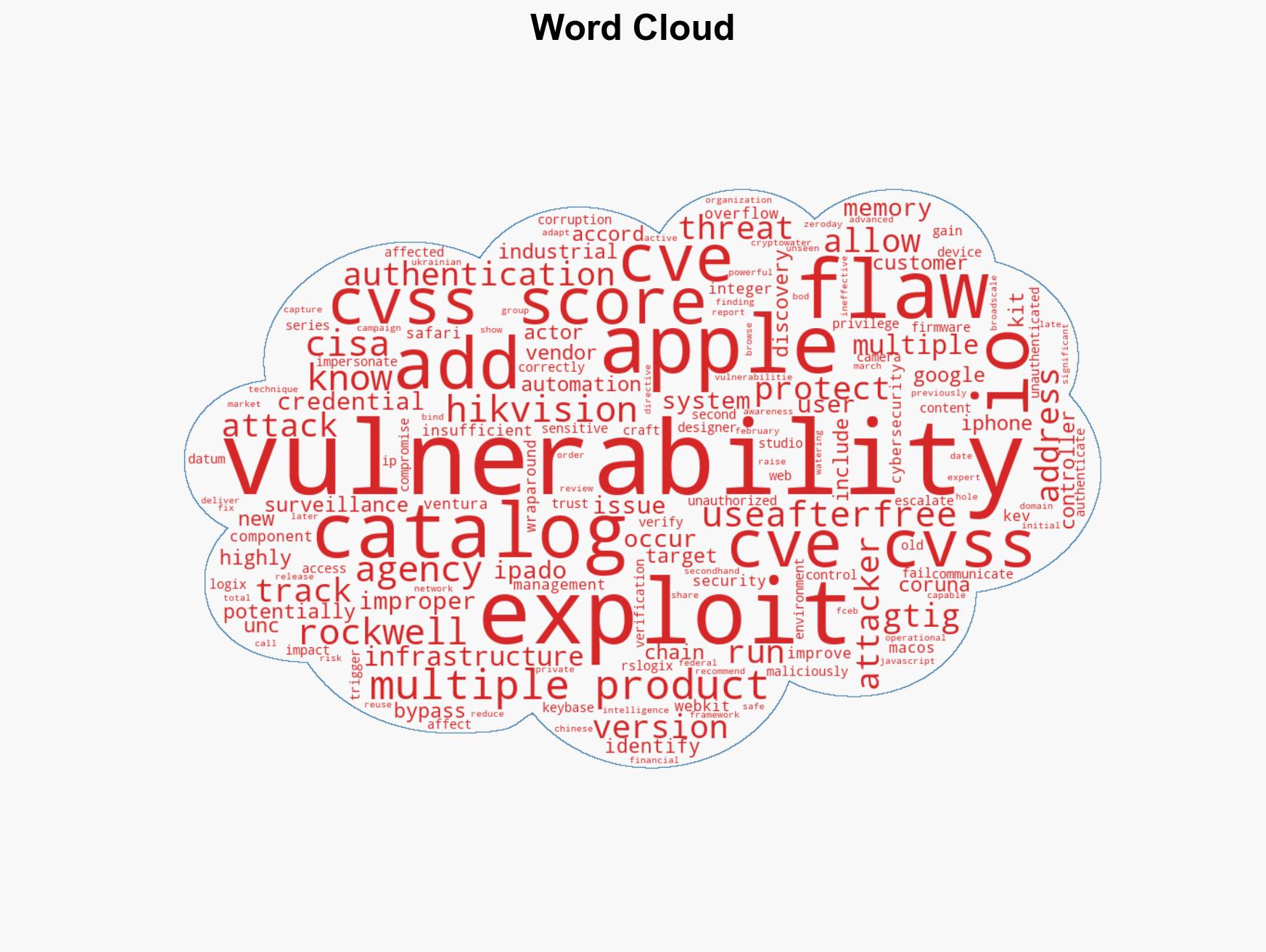
cybersecurity, vulnerabilities, state-sponsored actors, critical infrastructure, cybercrime, espionage, threat intelligence
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us