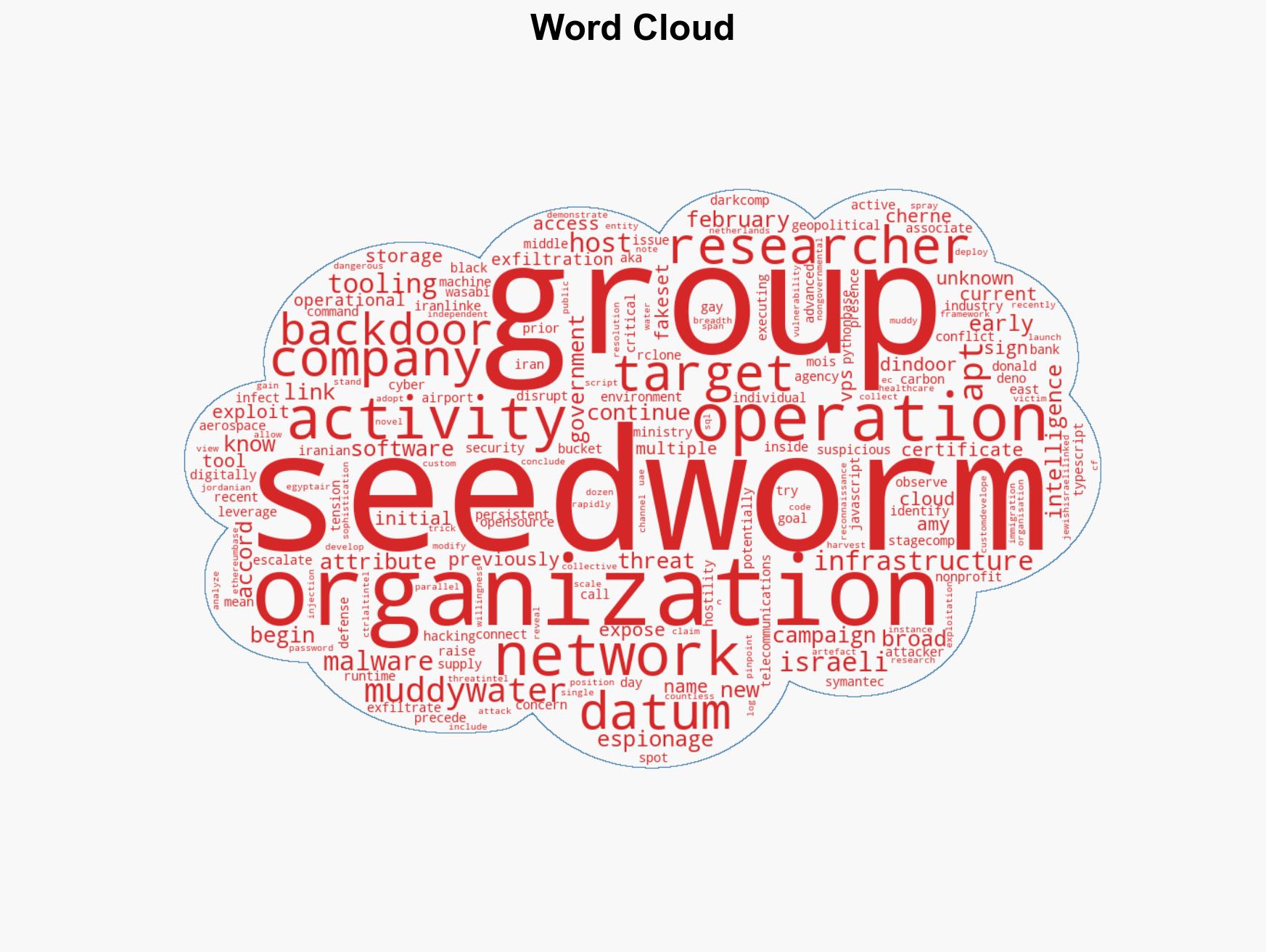
Iranian APT Seedworm Exploits US Critical Infrastructure with New Malware Backdoors
Published on: 2026-03-06
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
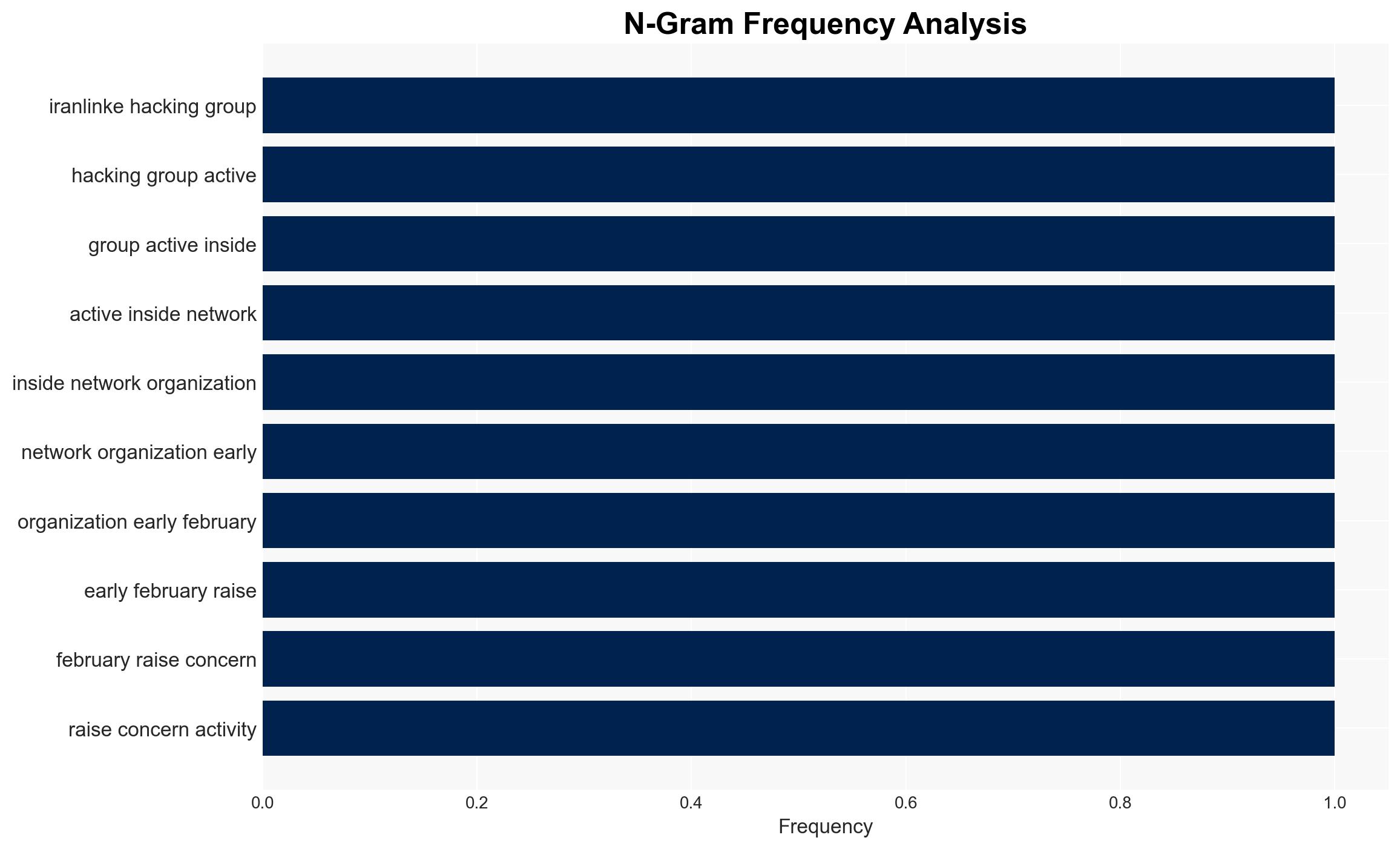
Intelligence Report: Iran-linked APT targets US critical sectors with new backdoors
1. BLUF (Bottom Line Up Front)
An Iran-linked APT group, Seedworm, has infiltrated US critical sectors using new backdoors, potentially positioning itself for broader cyber operations amid rising Middle East tensions. The activity, targeting entities like a US bank and airport, suggests espionage motives. We assess with moderate confidence that this activity is preparatory for potential escalatory actions.
2. Competing Hypotheses
- Hypothesis A: Seedworm’s activity is primarily espionage-focused, aimed at gathering intelligence on US critical sectors and Israeli-linked organizations. Supporting evidence includes the use of backdoors for data exfiltration and targeting entities with strategic value. Key uncertainties include the full extent of data accessed and the ultimate intent behind data collection.
- Hypothesis B: The activity is a precursor to disruptive cyber operations, potentially as a response to geopolitical tensions. While the presence on critical networks supports this, there is limited evidence of destructive payloads or direct attacks thus far.
- Assessment: Hypothesis A is currently better supported due to the observed focus on data exfiltration and lack of immediate disruptive actions. Indicators such as increased network activity or deployment of destructive malware could shift this assessment towards Hypothesis B.
3. Key Assumptions and Red Flags
- Assumptions: Seedworm is acting under the direction or with the approval of Iranian state actors; the primary goal is intelligence collection rather than immediate disruption; current geopolitical tensions will influence cyber operations.
- Information Gaps: Specific methods used for initial network access; the full scope of compromised data; potential links to other Iranian cyber activities.
- Bias & Deception Risks: Attribution bias due to reliance on specific cybersecurity firms; potential for false flag operations or misattribution by Seedworm to obscure true intent.
4. Implications and Strategic Risks
This development could exacerbate geopolitical tensions and lead to increased cyber hostilities, particularly if linked to broader state-sponsored activities.
- Political / Geopolitical: Potential for escalation between the US and Iran, impacting diplomatic relations and regional stability.
- Security / Counter-Terrorism: Increased vigilance required for critical infrastructure protection; potential for retaliatory actions.
- Cyber / Information Space: Heightened risk of cyber espionage and information operations targeting sensitive sectors.
- Economic / Social: Potential economic impacts from compromised sectors, particularly if data breaches affect financial or operational stability.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of critical networks; deploy threat intelligence sharing among affected sectors; conduct vulnerability assessments.
- Medium-Term Posture (1–12 months): Develop resilience measures and incident response capabilities; strengthen international cyber cooperation and information sharing.
- Scenario Outlook:
- Best: Diplomatic resolution reduces cyber hostilities; increased cybersecurity measures deter further intrusions.
- Worst: Escalation leads to significant cyber-attacks on critical infrastructure, causing widespread disruption.
- Most-Likely: Continued espionage activities with occasional disruptive attempts, primarily targeting strategic sectors.
6. Key Individuals and Entities
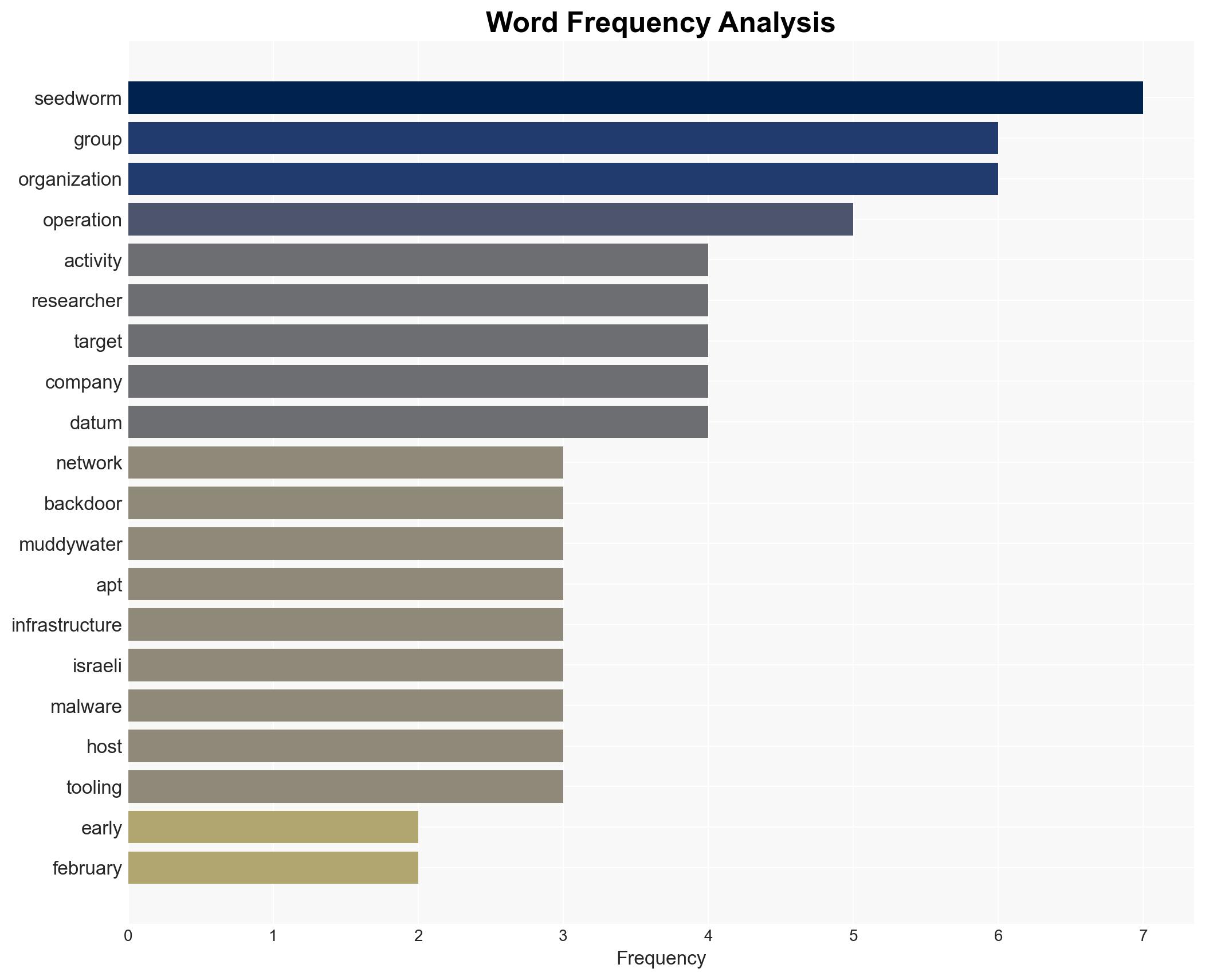
- Seedworm (MuddyWater) APT Group
- Iran’s Ministry of Intelligence and Security (MOIS)
- US bank, US airport, Israeli operations of a US software company
- “Amy Cherne” and “Donald Gay” (certificate names)
7. Thematic Tags
cybersecurity, cyber-espionage, critical infrastructure, Iran, Seedworm, geopolitical tensions, data exfiltration
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us