Iran’s Cyber Threat Persists Amid Conflict, Experts Warn of Evolving Hacking Tactics
Published on: 2026-03-06
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Iran hacking capability still a threat despite war damage Experts
1. BLUF (Bottom Line Up Front)
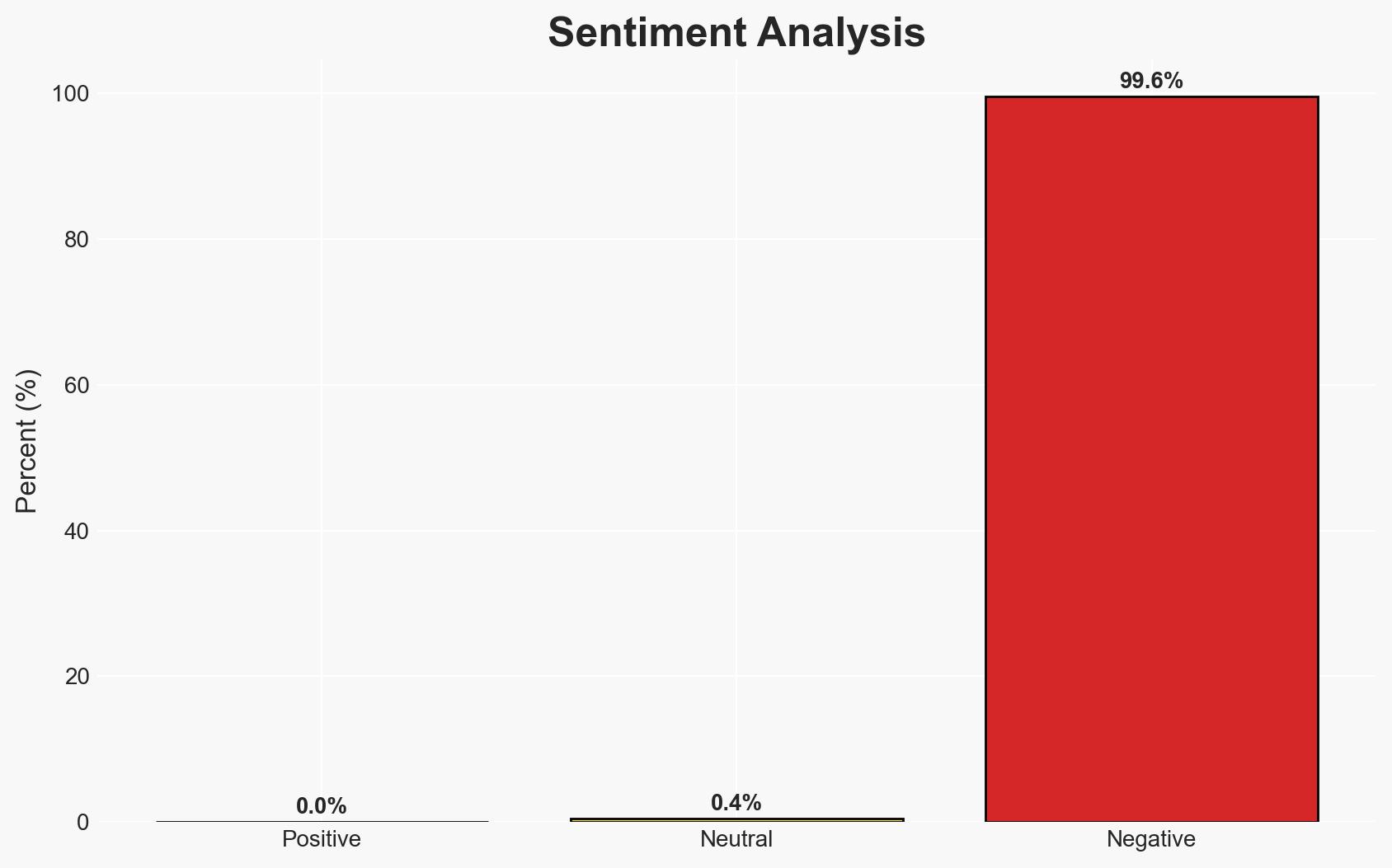
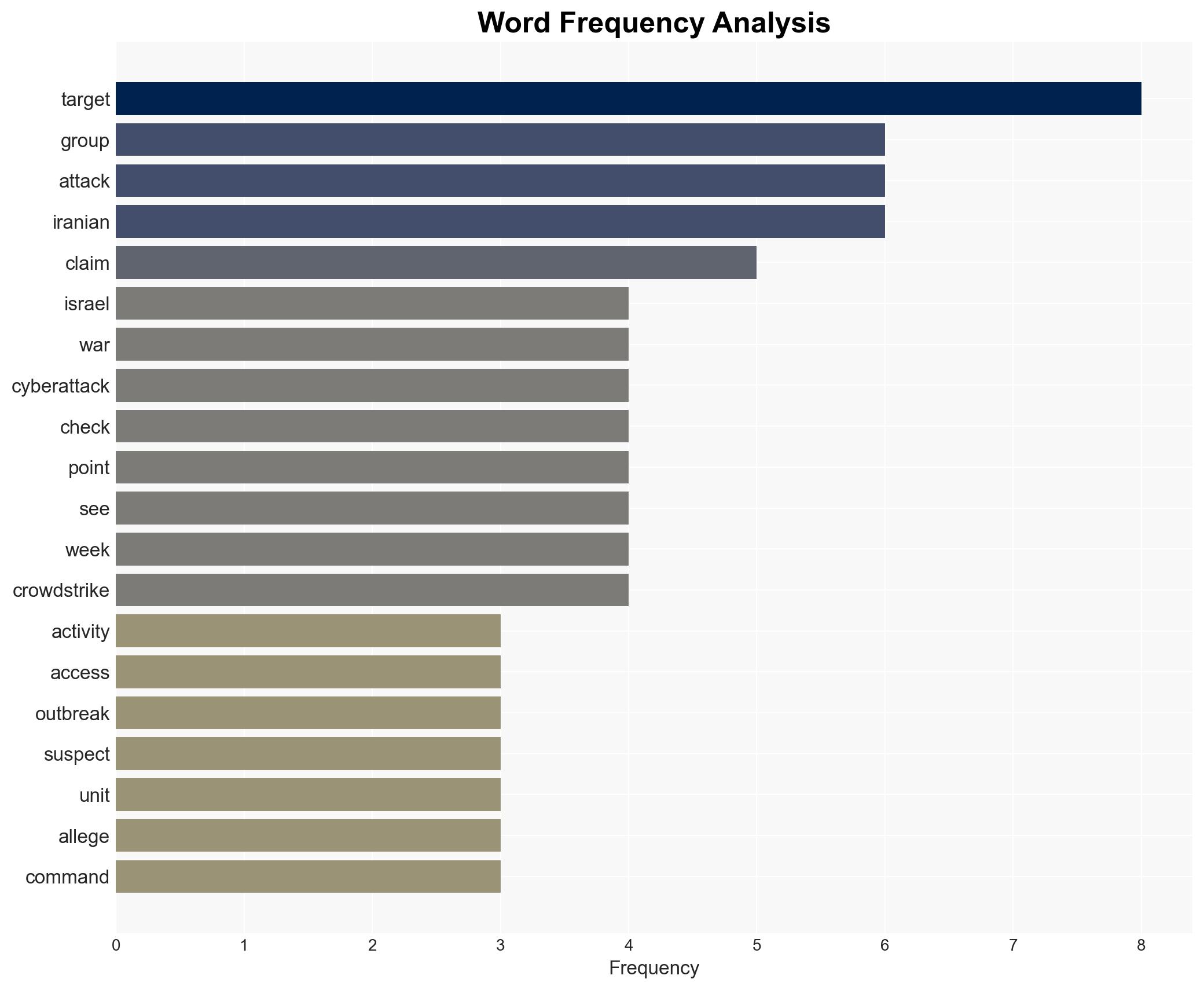
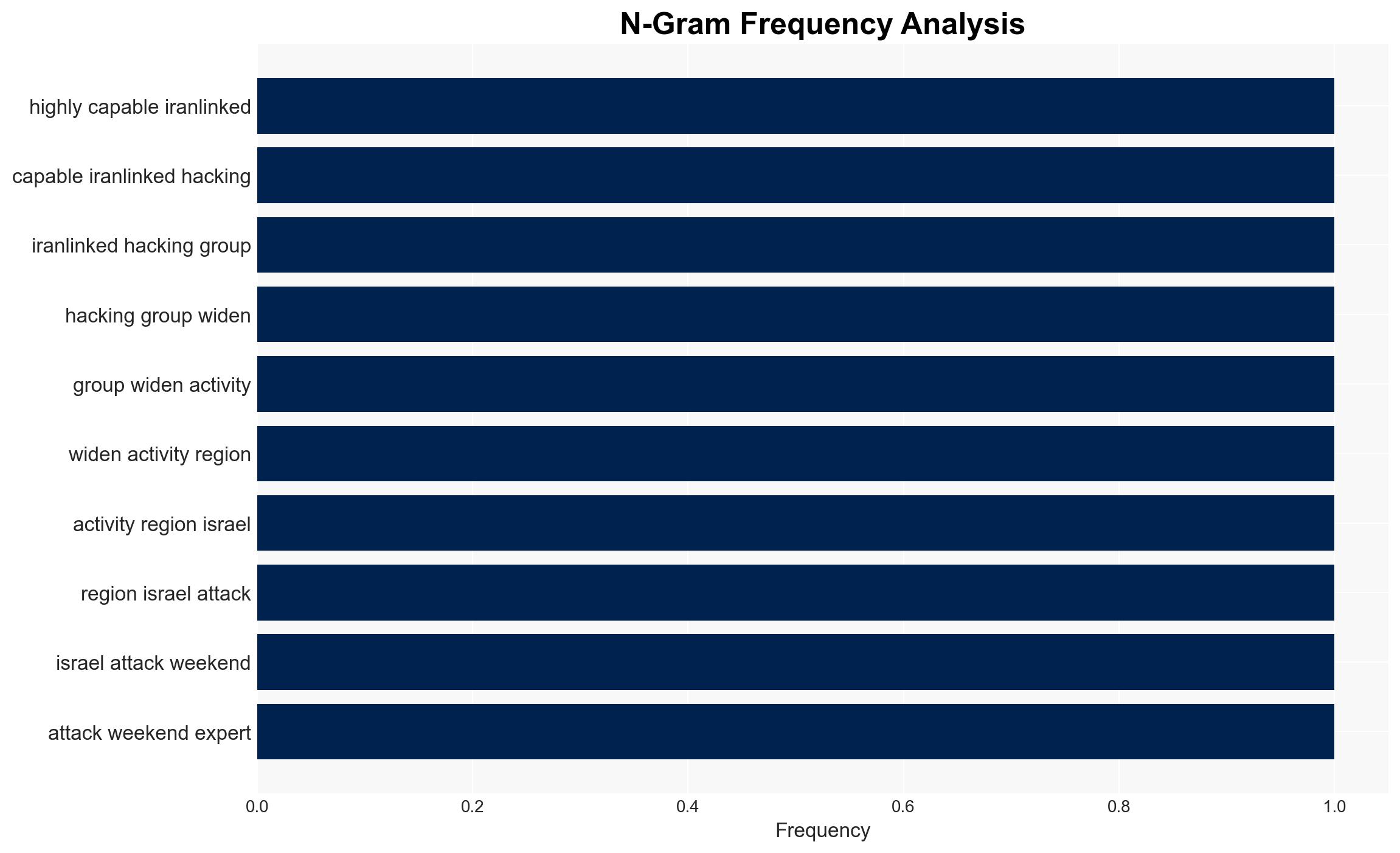
Despite recent military actions against Iran, its cyber capabilities remain a significant threat, particularly to regional adversaries like Israel. Iranian cyber operations have adapted to exploit vulnerabilities in civilian infrastructure, such as emergency alert systems and surveillance networks. This assessment is made with moderate confidence due to ongoing conflict and limited visibility into Iranian cyber strategy adjustments.
2. Competing Hypotheses
- Hypothesis A: Iran’s cyber capabilities are significantly degraded due to recent US and Israeli military actions. Supporting evidence includes reports of connectivity loss and operational disruptions. However, the continuation of sophisticated phishing campaigns and surveillance breaches suggests resilience.
- Hypothesis B: Iran’s cyber capabilities remain largely intact and adaptable, leveraging existing infrastructure and exploiting new vulnerabilities. Evidence includes recent phishing attacks and surveillance camera breaches across multiple countries. Contradictory evidence is the reported impact of military strikes on connectivity.
- Assessment: Hypothesis B is currently better supported, as recent cyber activities indicate ongoing operational capability. Key indicators that could shift this judgment include confirmed reports of sustained operational disruptions or a significant decrease in attack frequency.
3. Key Assumptions and Red Flags
- Assumptions: Iran prioritizes cyber operations as a strategic tool; Iranian cyber groups have sufficient resources to maintain operations despite military setbacks; regional adversaries remain primary targets.
- Information Gaps: Detailed impact of military strikes on specific Iranian cyber infrastructure; internal Iranian decision-making regarding cyber operations post-strike.
- Bias & Deception Risks: Potential over-reliance on Israeli and Western sources; possibility of Iranian misinformation campaigns exaggerating or downplaying capabilities.
4. Implications and Strategic Risks
The persistence of Iranian cyber threats could exacerbate regional tensions and complicate diplomatic resolutions. Cyber operations may serve as a force multiplier for kinetic actions, influencing both strategic and tactical decisions.
- Political / Geopolitical: Increased cyber activity could lead to heightened tensions between Iran and regional adversaries, potentially triggering retaliatory measures.
- Security / Counter-Terrorism: Enhanced cyber capabilities may support asymmetric warfare tactics, complicating defense and counter-terrorism efforts.
- Cyber / Information Space: Continued exploitation of civilian infrastructure vulnerabilities could undermine public trust and create informational chaos.
- Economic / Social: Persistent cyber threats may deter foreign investment and strain regional economies, impacting social stability.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of Iranian cyber activities, particularly targeting civilian infrastructure; strengthen cybersecurity defenses in vulnerable sectors.
- Medium-Term Posture (1–12 months): Develop regional cybersecurity partnerships to share intelligence and best practices; invest in resilience measures for critical infrastructure.
- Scenario Outlook:
- Best: Diplomatic engagements lead to de-escalation and reduced cyber threats.
- Worst: Escalation of cyber and kinetic attacks destabilizes the region.
- Most-Likely: Continued low to moderate intensity cyber operations with periodic spikes in activity.
6. Key Individuals and Entities
- Islamic Revolutionary Guard Corps (IRGC)
- Ministry of Intelligence and Security (Iran)
- Unit 42 (Cyberintelligence Company)
- Check Point (Israeli Cybersecurity Firm)
- Gil Messing (Check Point Chief of Staff)
- James Sullivan (RUSI Cyber and Tech Chief)
7. Thematic Tags
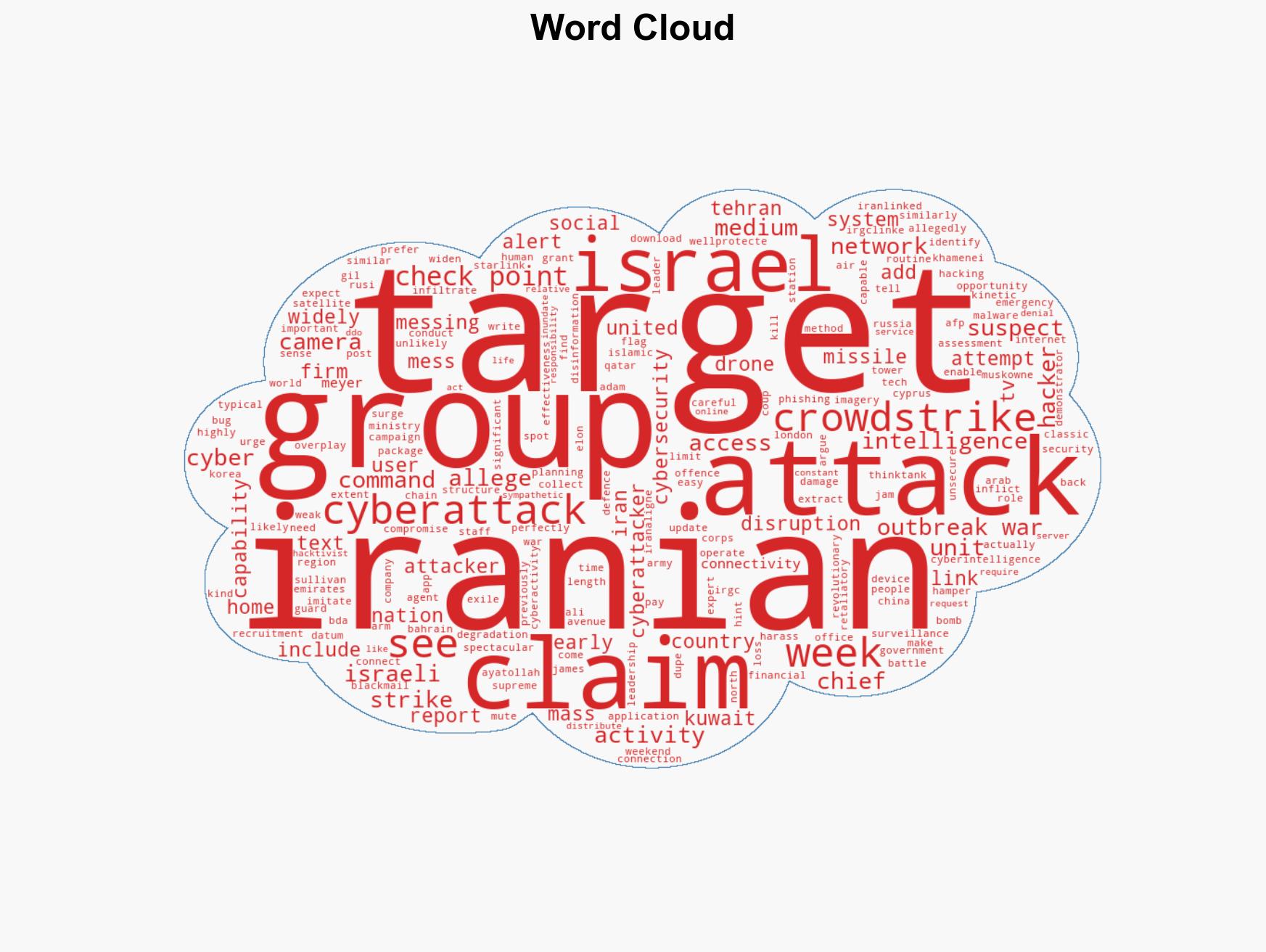
cybersecurity, cyber-espionage, regional security, Iran-Israel conflict, cyber warfare, information security, Middle East stability, asymmetric warfare
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us