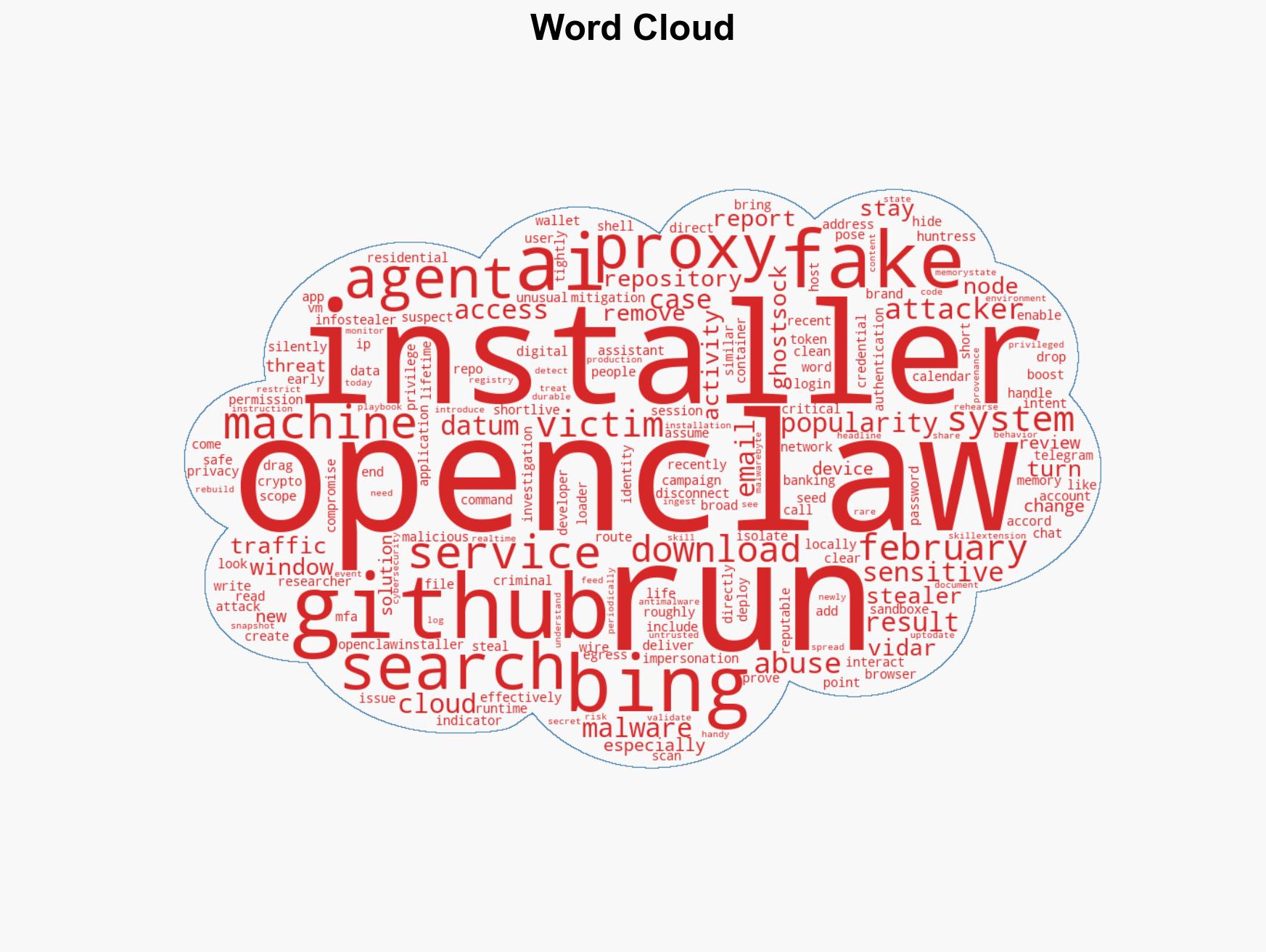
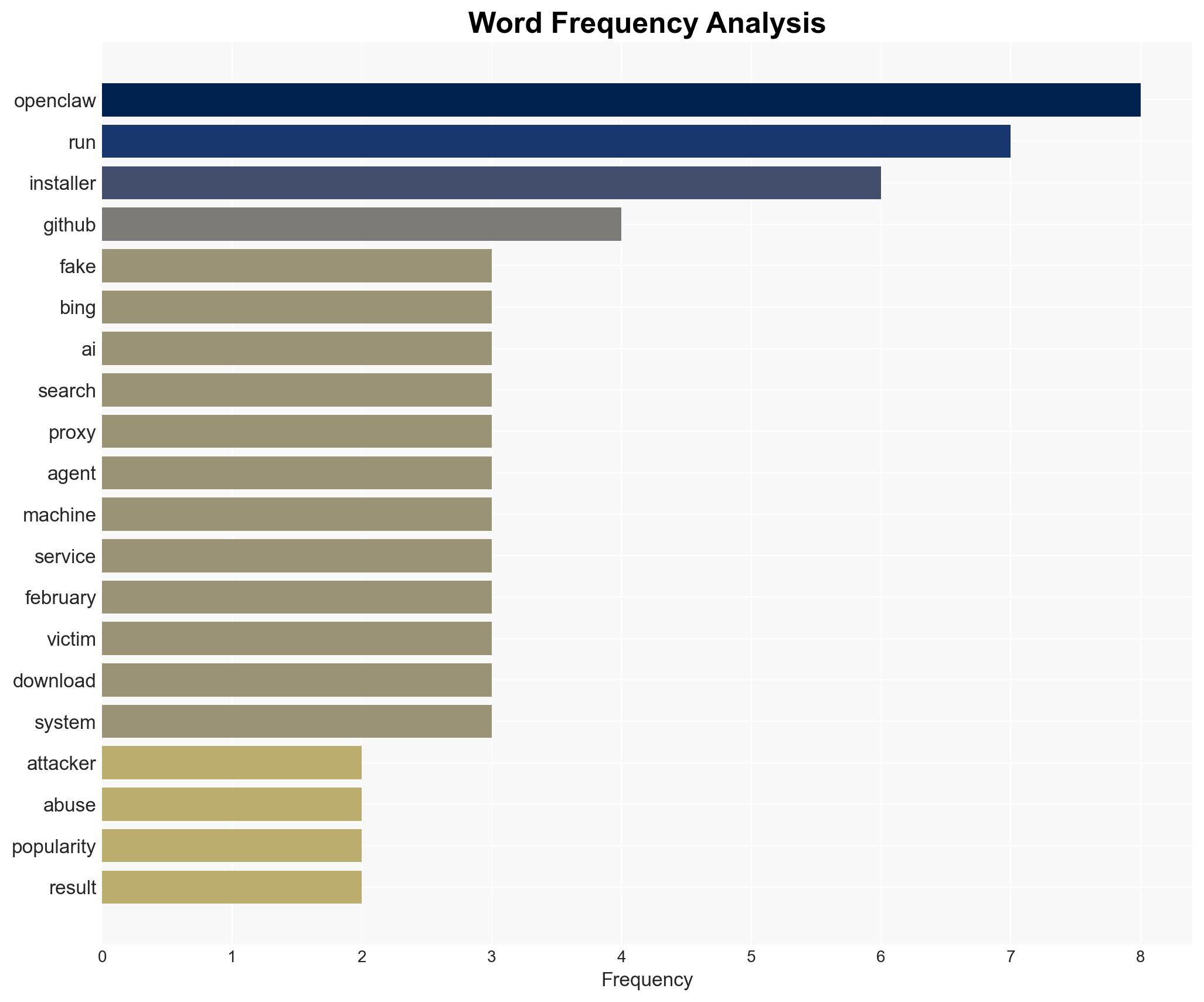
Fake OpenClaw Installers Misleadingly Promoted via Bing, Delivering Malware Instead of Legit Software
Published on: 2026-03-06
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Beware of fake OpenClaw installers even if Bing points you to GitHub
1. BLUF (Bottom Line Up Front)
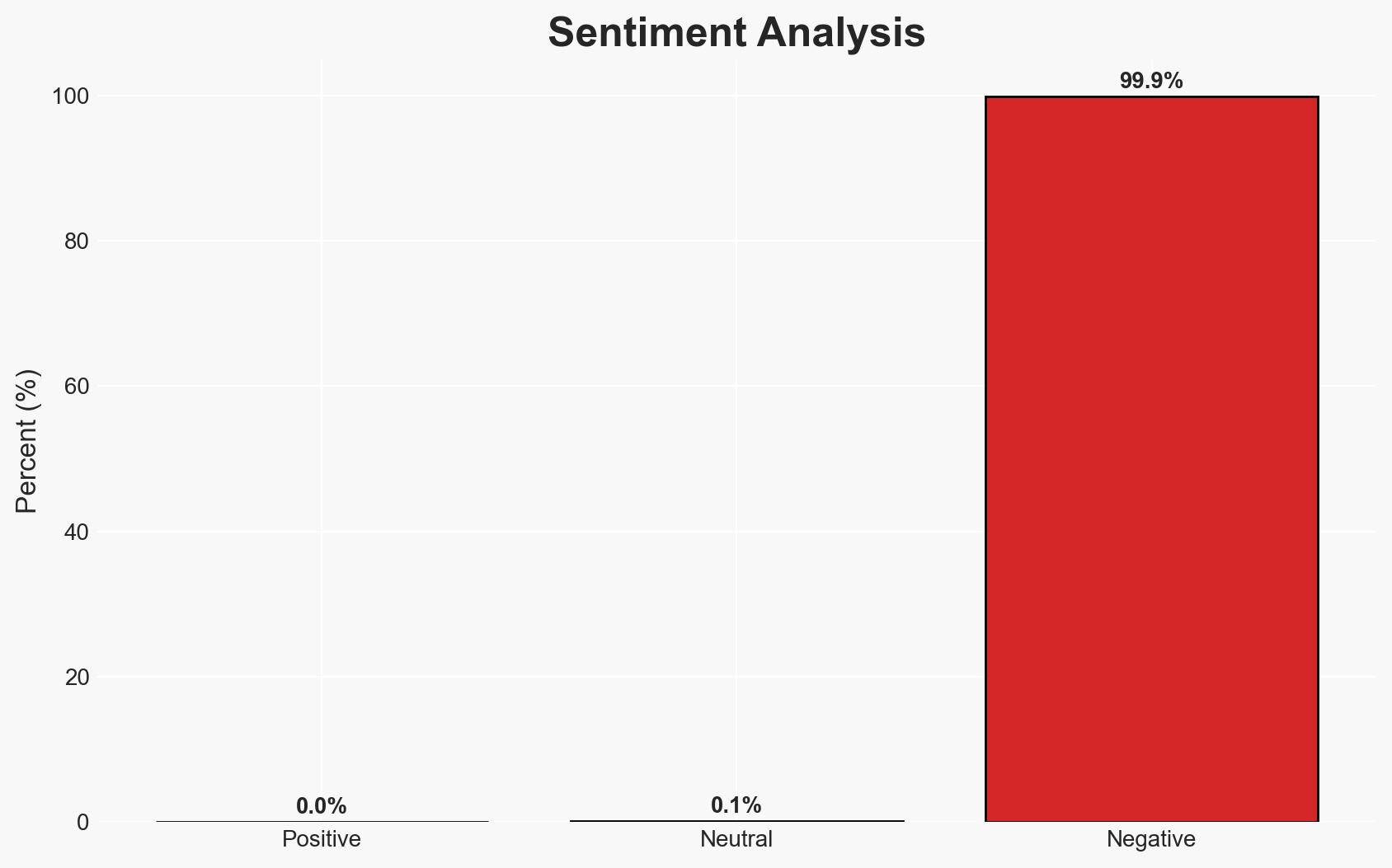
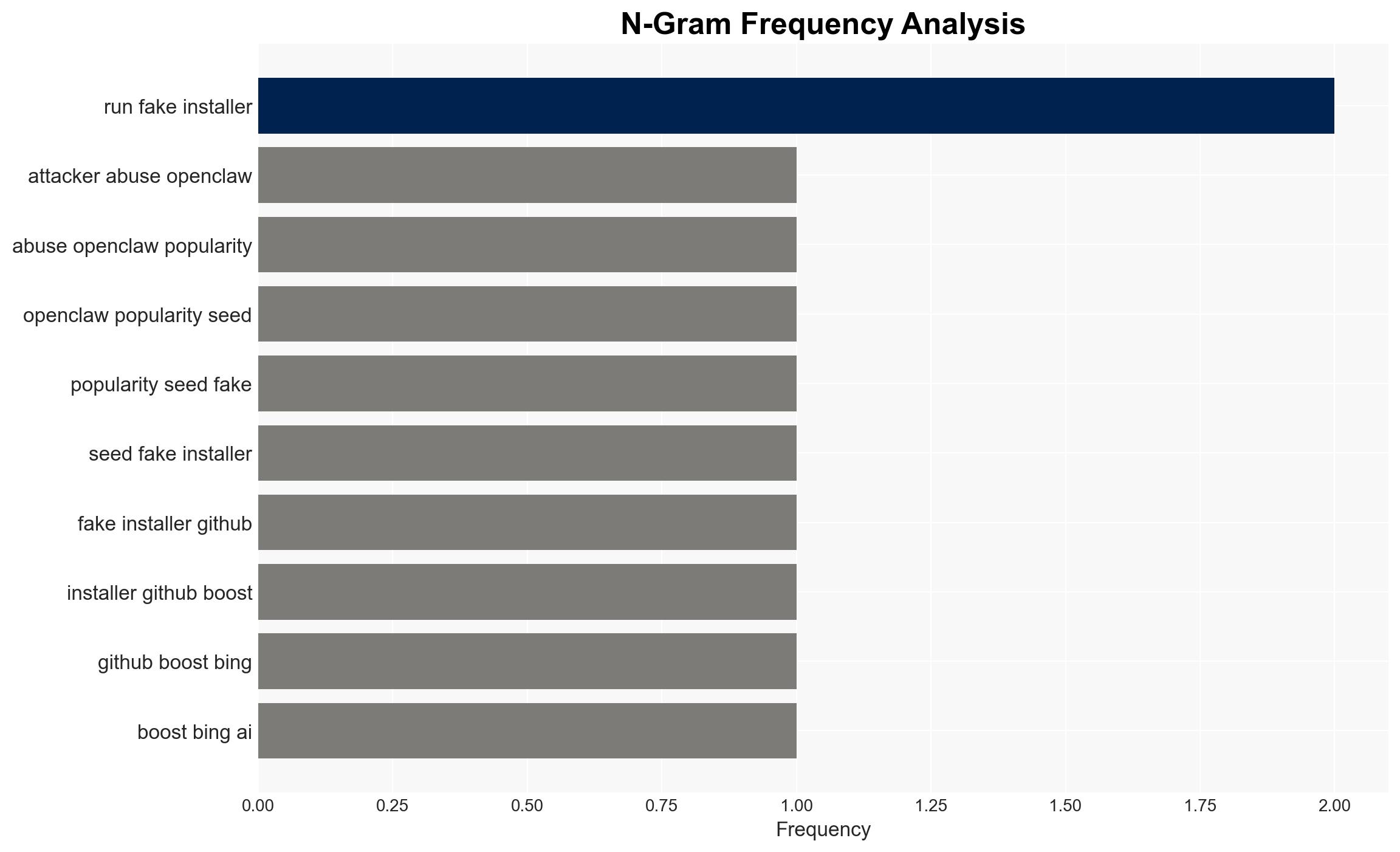
Malicious actors have exploited the popularity of OpenClaw by creating fake installers on GitHub, which are promoted through Bing search results, to distribute infostealers and proxy malware. This campaign primarily affects users seeking OpenClaw installations, potentially compromising their systems. The most supported hypothesis is that this is a financially motivated cybercrime operation. Overall confidence in this judgment is moderate.
2. Competing Hypotheses
- Hypothesis A: The operation is a financially motivated cybercrime campaign aimed at harvesting sensitive data and utilizing compromised systems for proxy services. This is supported by the use of Vidar and GhostSocks, known for data theft and proxy node creation. However, the short duration of the campaign introduces uncertainty about the attackers’ long-term objectives.
- Hypothesis B: The operation is a state-sponsored cyber-espionage effort disguised as a criminal activity to obscure its true intent. This hypothesis is less supported due to the lack of evidence linking the operation to state actors and the typical financial focus of the deployed malware.
- Assessment: Hypothesis A is currently better supported due to the nature of the malware used and the typical patterns of financially motivated cybercrime. Indicators that could shift this judgment include evidence of targeted attacks on specific individuals or organizations with strategic value.
3. Key Assumptions and Red Flags
- Assumptions: The attackers are primarily motivated by financial gain; the campaign’s short duration was due to rapid detection and takedown; the use of Bing and GitHub was opportunistic rather than strategic.
- Information Gaps: The identity of the attackers; the full scope of the campaign’s impact; potential links to broader cybercrime networks.
- Bias & Deception Risks: Confirmation bias towards financial motives due to the malware used; potential underestimation of state actor involvement; reliance on open-source reporting which may miss classified insights.
4. Implications and Strategic Risks
This development highlights vulnerabilities in open-source software distribution and search engine trust, potentially leading to increased scrutiny and security measures in these areas.
- Political / Geopolitical: Increased tensions between tech companies and governments over cybersecurity responsibilities and responses.
- Security / Counter-Terrorism: Potential for similar tactics to be used in more targeted attacks against critical infrastructure or high-value targets.
- Cyber / Information Space: Erosion of trust in open-source platforms and search engines, leading to increased demand for secure software distribution methods.
- Economic / Social: Possible financial losses for individuals and businesses affected by data theft and unauthorized proxy use.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Encourage users to verify software sources, enhance monitoring of GitHub repositories for malicious activity, and collaborate with search engines to identify and remove malicious links.
- Medium-Term Posture (1–12 months): Develop partnerships between tech companies and cybersecurity firms to improve detection and response capabilities; invest in user education on cybersecurity hygiene.
- Scenario Outlook:
- Best: Improved detection and prevention measures lead to a decrease in similar cybercrime campaigns.
- Worst: Attackers adapt tactics, leading to more sophisticated and widespread campaigns.
- Most-Likely: Continued sporadic attempts at similar campaigns with varying success rates.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, cybercrime, malware, open-source security, information security, digital trust, cyber hygiene, software distribution
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us