White House Launches Comprehensive Cyber Strategy to Enhance US Defenses and Global Cooperation
Published on: 2026-03-07
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: US White House Unveils ‘Cyber Strategy For America’ To Counter Global Digital Threats
1. BLUF (Bottom Line Up Front)
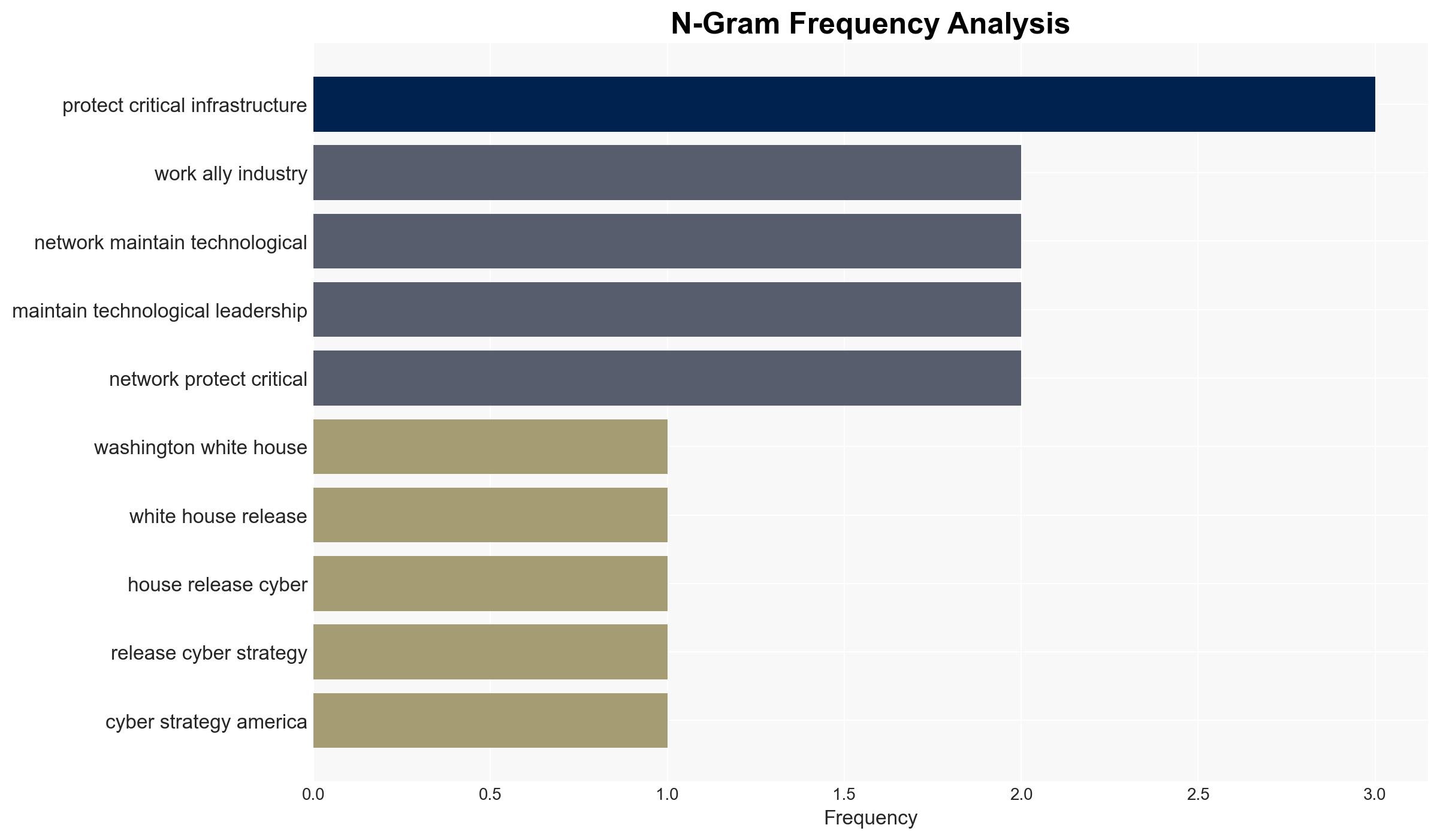
The US White House has released a comprehensive cyber strategy aimed at strengthening national cyber defenses and maintaining technological leadership. The strategy emphasizes collaboration with international allies and the private sector to protect critical infrastructure and digital networks. The most likely hypothesis is that this strategy will enhance US cyber resilience and influence global cyber norms. Overall confidence in this assessment is moderate due to potential implementation challenges and geopolitical resistance.
2. Competing Hypotheses
- Hypothesis A: The strategy will successfully enhance US cyber defenses and influence global cyber norms through international cooperation and advanced technology deployment. Supporting evidence includes the strategy’s focus on partnerships and technological innovation. Contradicting evidence includes potential resistance from rival states and the complexity of coordinating across diverse stakeholders.
- Hypothesis B: The strategy may face significant implementation challenges, limiting its effectiveness in achieving stated goals. Supporting evidence includes historical difficulties in cross-sector coordination and potential geopolitical pushback. Contradicting evidence is the strong political will and resource allocation indicated by the strategy.
- Assessment: Hypothesis A is currently better supported due to the comprehensive nature of the strategy and its alignment with existing US capabilities and alliances. Key indicators that could shift this judgment include changes in international relations or domestic political priorities.
3. Key Assumptions and Red Flags
- Assumptions: The US will maintain its technological leadership; international partners will cooperate effectively; adversaries will not significantly escalate cyber operations in response.
- Information Gaps: Specific details on resource allocation and timelines for implementation are missing. The extent of international partner commitments is unclear.
- Bias & Deception Risks: Potential for cognitive bias in overestimating US technological superiority; source bias from government statements emphasizing success without acknowledging challenges.
4. Implications and Strategic Risks
This development could lead to enhanced US cyber resilience and influence over global cyber norms, but may also provoke adversarial responses. The strategy’s success depends on effective implementation and international cooperation.
- Political / Geopolitical: Potential for increased tensions with rival states that perceive the strategy as a threat to their cyber capabilities.
- Security / Counter-Terrorism: Improved defenses could deter cyberattacks, but adversaries may seek alternative methods to challenge US interests.
- Cyber / Information Space: The strategy may drive innovation in cybersecurity technologies and practices, influencing global standards.
- Economic / Social: Enhanced cybersecurity could protect critical infrastructure, but implementation costs may impact economic resources.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Establish clear communication channels with international partners and private sector stakeholders to facilitate coordination.
- Medium-Term Posture (1–12 months): Develop metrics to assess strategy implementation and effectiveness; invest in workforce training and technological innovation.
- Scenario Outlook:
- Best: Successful implementation leads to enhanced global cyber norms and reduced cyber threats.
- Worst: Implementation challenges and geopolitical tensions undermine strategy effectiveness.
- Most-Likely: Partial success with improvements in some areas but ongoing challenges in others.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
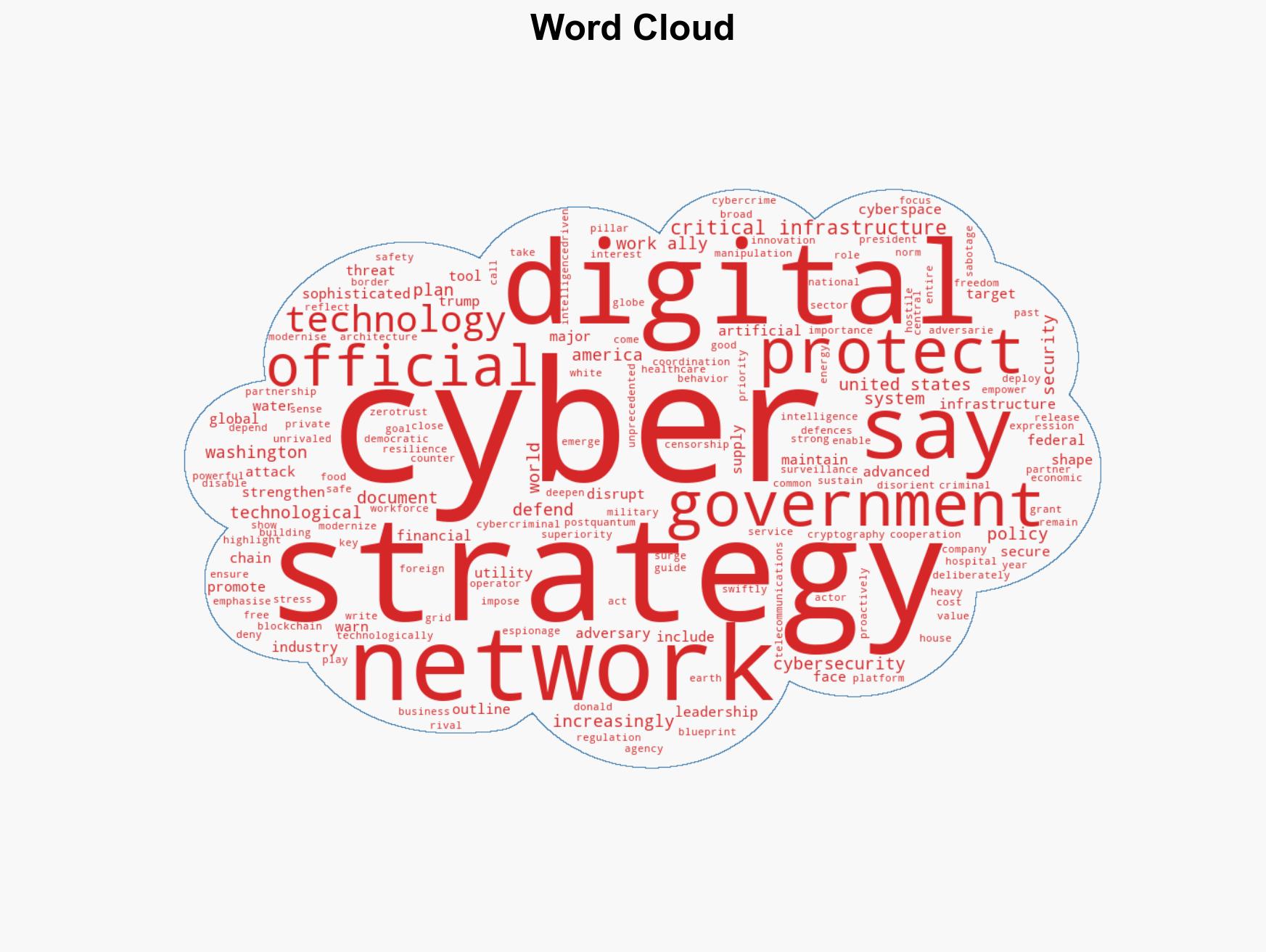
cybersecurity, international cooperation, critical infrastructure, technological innovation, cyber norms, geopolitical tensions, digital resilience
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us