Trump Administration Unveils Comprehensive Cyber Strategy to Strengthen U.S. Digital Defense and Dominance
Published on: 2026-03-07
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
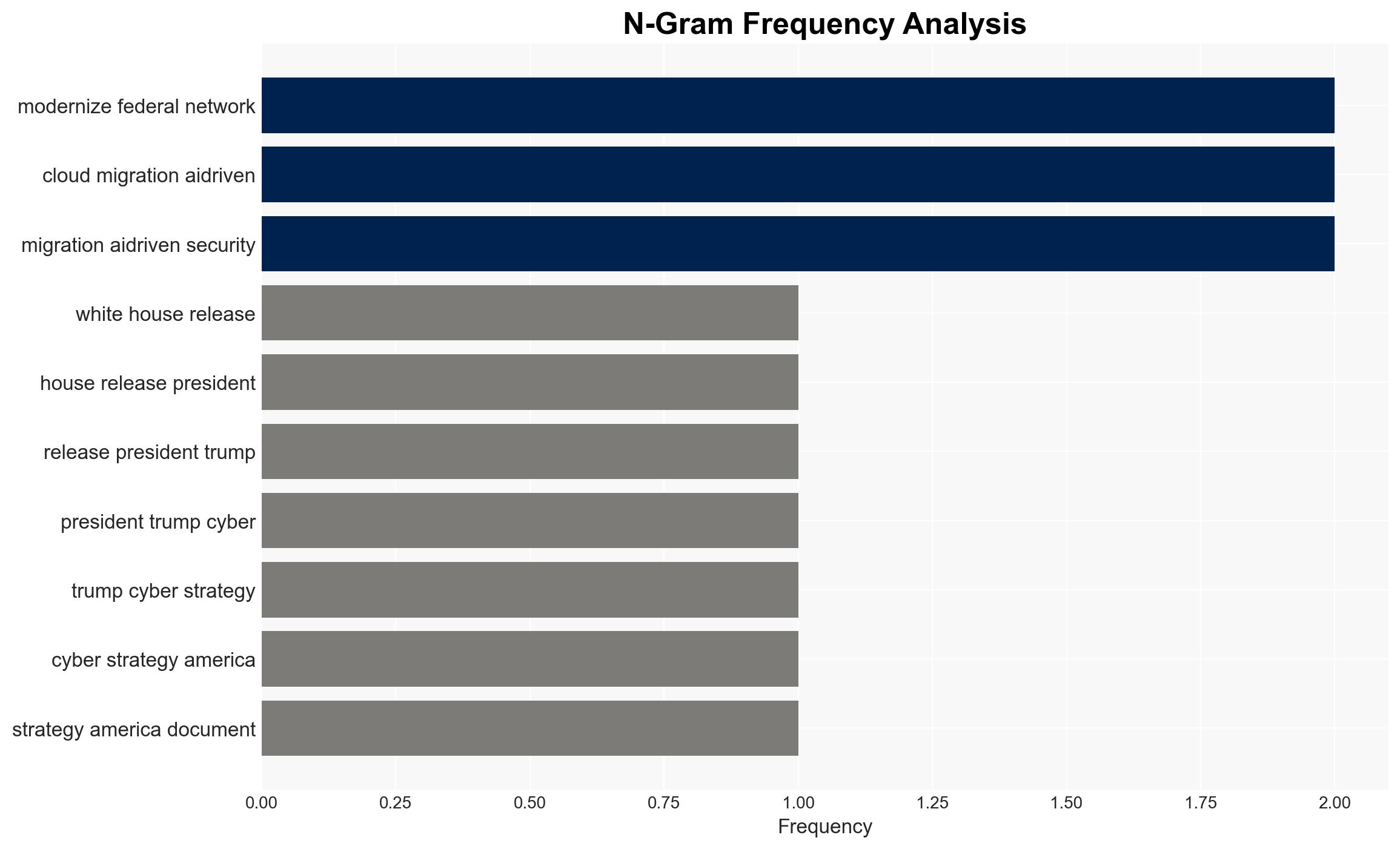
Intelligence Report: Reading White House President Trumps Cyber Strategy for America March 2026
1. BLUF (Bottom Line Up Front)
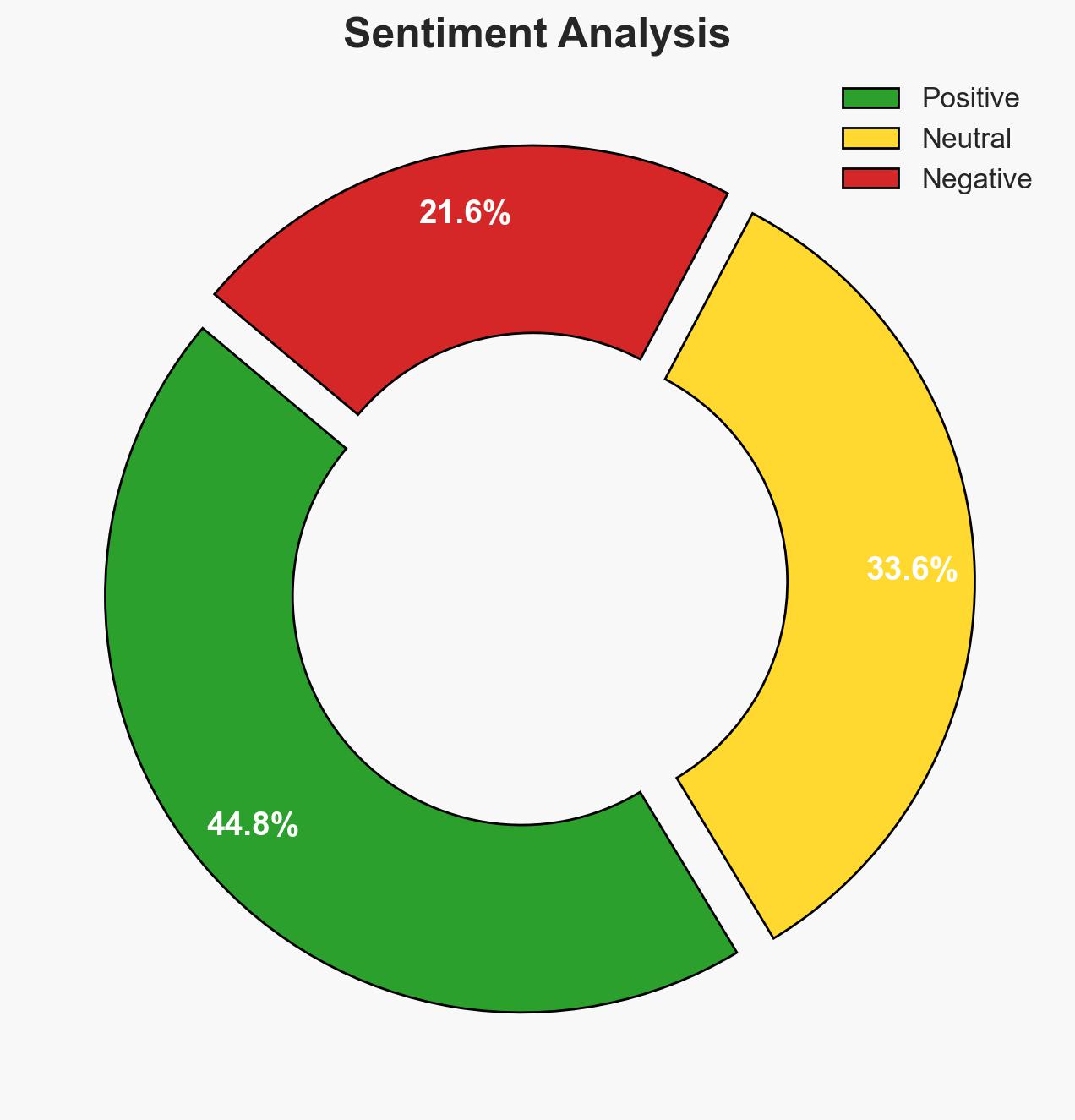
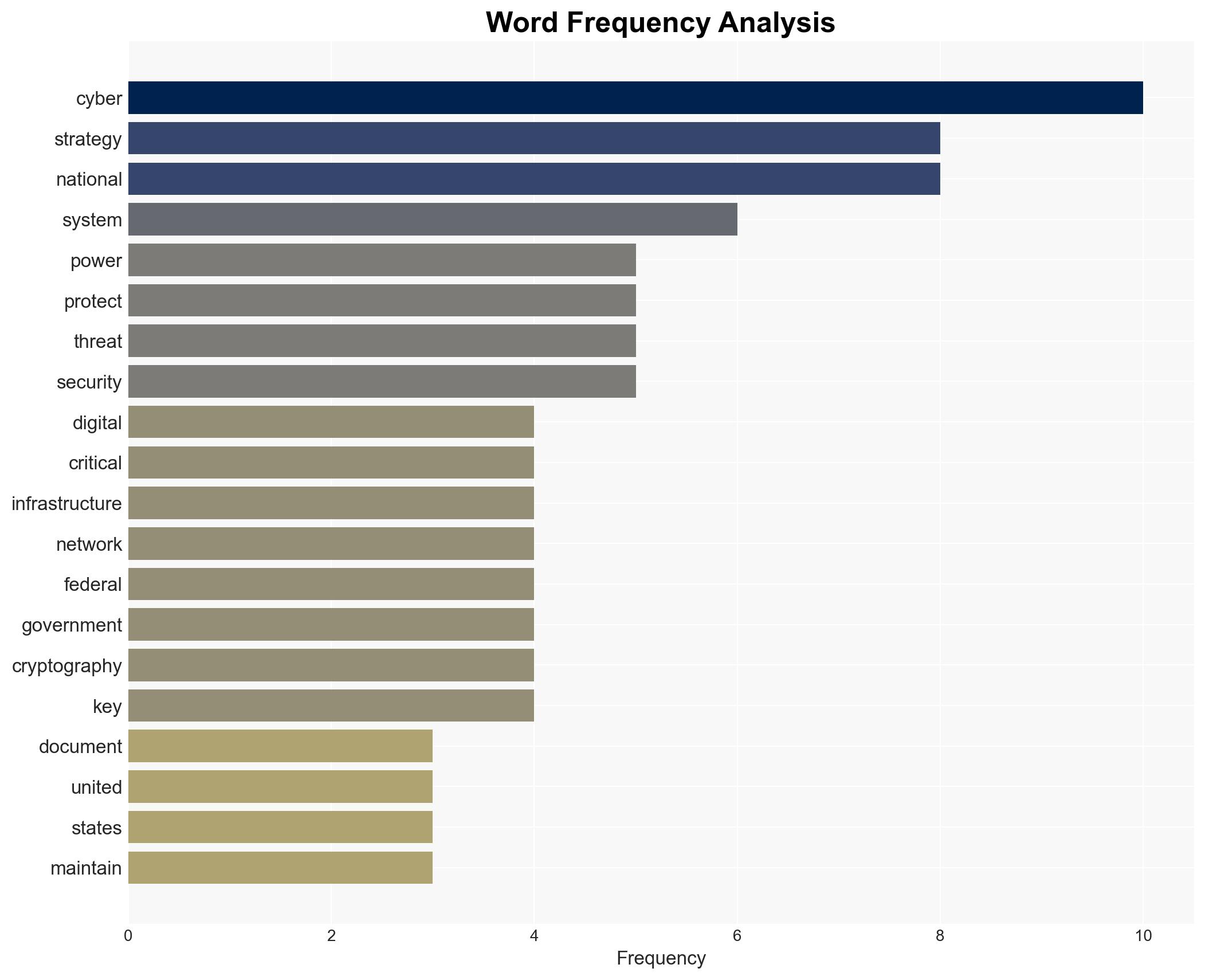
The release of President Trump’s Cyber Strategy for America marks a significant shift in U.S. policy, framing cyberspace as a strategic domain for national power projection. The strategy’s emphasis on technological superiority and workforce development is likely to enhance U.S. cyber capabilities. However, the effectiveness of these measures depends on overcoming potential implementation challenges. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: The strategy will successfully enhance U.S. cyber capabilities and deter adversaries through its comprehensive approach. This is supported by the strategy’s detailed policy pillars and focus on technological and workforce development. However, uncertainties include the feasibility of implementation and potential bureaucratic resistance.
- Hypothesis B: The strategy will face significant implementation challenges, limiting its effectiveness. This is supported by historical difficulties in inter-agency coordination and the complexity of modernizing federal networks. Contradicting evidence includes the administration’s commitment to prioritizing cyber initiatives.
- Assessment: Hypothesis A is currently better supported due to the strategy’s comprehensive nature and alignment with current technological trends. Key indicators that could shift this judgment include delays in policy implementation or failure to secure necessary funding.
3. Key Assumptions and Red Flags
- Assumptions: The strategy will receive adequate funding; inter-agency cooperation will be effective; technological advancements will continue at the current pace; adversaries will respond predictably to deterrence measures.
- Information Gaps: Specific details on funding allocation and timelines for implementation; adversaries’ potential countermeasures; private sector’s readiness to collaborate.
- Bias & Deception Risks: Potential overconfidence in technological solutions; source bias from government documents; adversaries may engage in deception to mislead U.S. cyber operations.
4. Implications and Strategic Risks
The strategy could significantly alter the cyber landscape, affecting both national and international dynamics. Its success or failure will influence U.S. geopolitical standing and cyber deterrence capabilities.
- Political / Geopolitical: Potential escalation in cyber conflicts; shifts in alliances based on technological capabilities.
- Security / Counter-Terrorism: Enhanced capabilities may deter state-sponsored and criminal cyber activities; potential for increased cyber retaliation.
- Cyber / Information Space: Increased focus on offensive cyber operations; potential for adversaries to develop countermeasures.
- Economic / Social: Strengthened cybersecurity could protect economic interests; workforce development may boost employment in the tech sector.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Establish clear implementation timelines; engage with private sector partners; monitor adversary responses to the strategy’s release.
- Medium-Term Posture (1–12 months): Develop inter-agency coordination mechanisms; invest in cybersecurity education and training programs; evaluate progress against strategic objectives.
- Scenario Outlook: Best: Successful implementation enhances U.S. cyber dominance. Worst: Implementation failures lead to increased vulnerabilities. Most-Likely: Gradual improvements with some delays and challenges.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
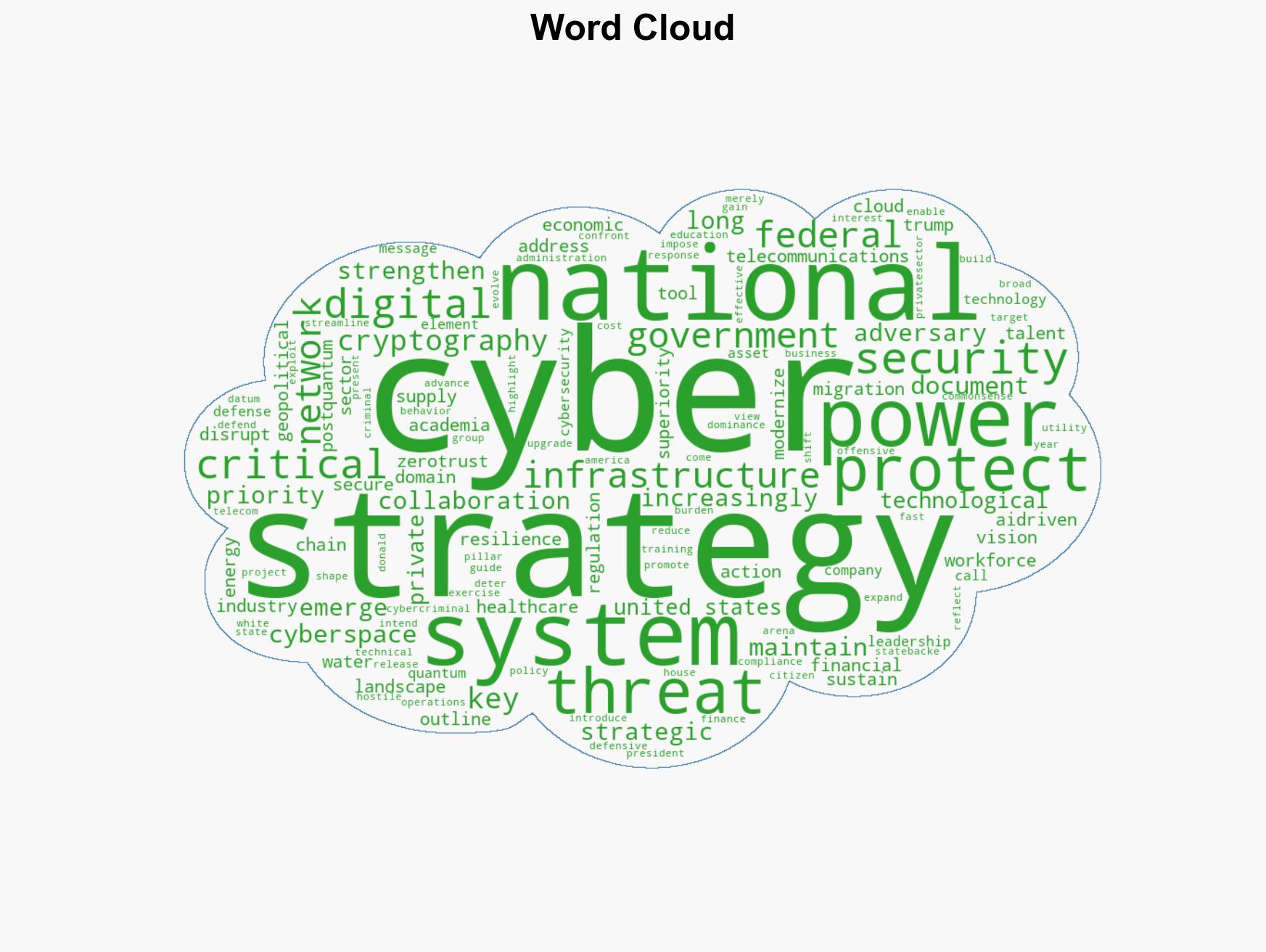
cybersecurity, national security, cyber strategy, technological superiority, critical infrastructure, cyber workforce, cyber deterrence
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us