Trump Issues Executive Order to Enhance Cybercrime Combat Strategies Against Transnational Criminals
Published on: 2026-03-09
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Trump Signs Order to Bolster Efforts to Combat Cybercrime
1. BLUF (Bottom Line Up Front)
President Trump’s executive order aims to enhance efforts against cybercrime by directing a comprehensive review of tools to combat transnational criminal organizations. The order’s effectiveness is uncertain due to the lack of specific adversary mentions and resource allocations. This initiative could impact US cyber defense posture and international cooperation. Overall confidence in the assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: The executive order will significantly enhance US capabilities to combat cybercrime by streamlining efforts and resources. Supporting evidence includes the directive for a comprehensive review and prioritization of prosecutions. Contradicting evidence includes the absence of specific adversary mentions and resource allocations, which may limit effectiveness.
- Hypothesis B: The executive order will have limited impact due to its broad scope and lack of specific directives. Supporting evidence includes the lack of specific adversary mentions and no clear spending or hiring targets. Contradicting evidence includes the administration’s stated intention to take aggressive action against cyber threats.
- Assessment: Hypothesis B is currently better supported due to the lack of specificity and resource allocation in the order. Key indicators that could shift this judgment include future detailed action plans and resource commitments.
3. Key Assumptions and Red Flags
- Assumptions: The US government has the capability to identify and combat transnational cybercriminal organizations effectively; the executive order will lead to actionable policy changes; international cooperation will be forthcoming.
- Information Gaps: Specific adversary targets, resource allocation details, and metrics for success are not provided.
- Bias & Deception Risks: Potential cognitive bias in overestimating US capabilities; source bias from political motivations in the administration’s narrative; risk of adversarial deception in cyber threat reporting.
4. Implications and Strategic Risks
The executive order could influence US cyber defense strategies and international cybercrime cooperation. However, its broad scope may limit immediate impact.
- Political / Geopolitical: Potential for increased tensions with nations perceived as harboring cybercriminals; opportunity for enhanced international cybercrime cooperation.
- Security / Counter-Terrorism: Possible shifts in threat landscape as cybercriminals adapt to new US policies.
- Cyber / Information Space: Increased focus on AI and reduced regulation could lead to innovation but also vulnerabilities.
- Economic / Social: Potential economic impact from improved cybersecurity measures; social implications if cybercrime targeting individuals is reduced.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor implementation of the executive order; assess international reactions; identify key cybercriminal organizations.
- Medium-Term Posture (1–12 months): Develop partnerships with international allies; invest in AI and cybersecurity workforce; evaluate effectiveness of new policies.
- Scenario Outlook: Best: Enhanced US cyber capabilities and international cooperation. Worst: Limited impact due to lack of specificity and resources. Most-Likely: Incremental improvements with ongoing challenges in implementation.
6. Key Individuals and Entities
- President Donald Trump
- US Attorney General
- Secretaries of Homeland Security and State
- Transnational criminal organizations (not clearly identifiable from open sources in this snippet)
7. Thematic Tags
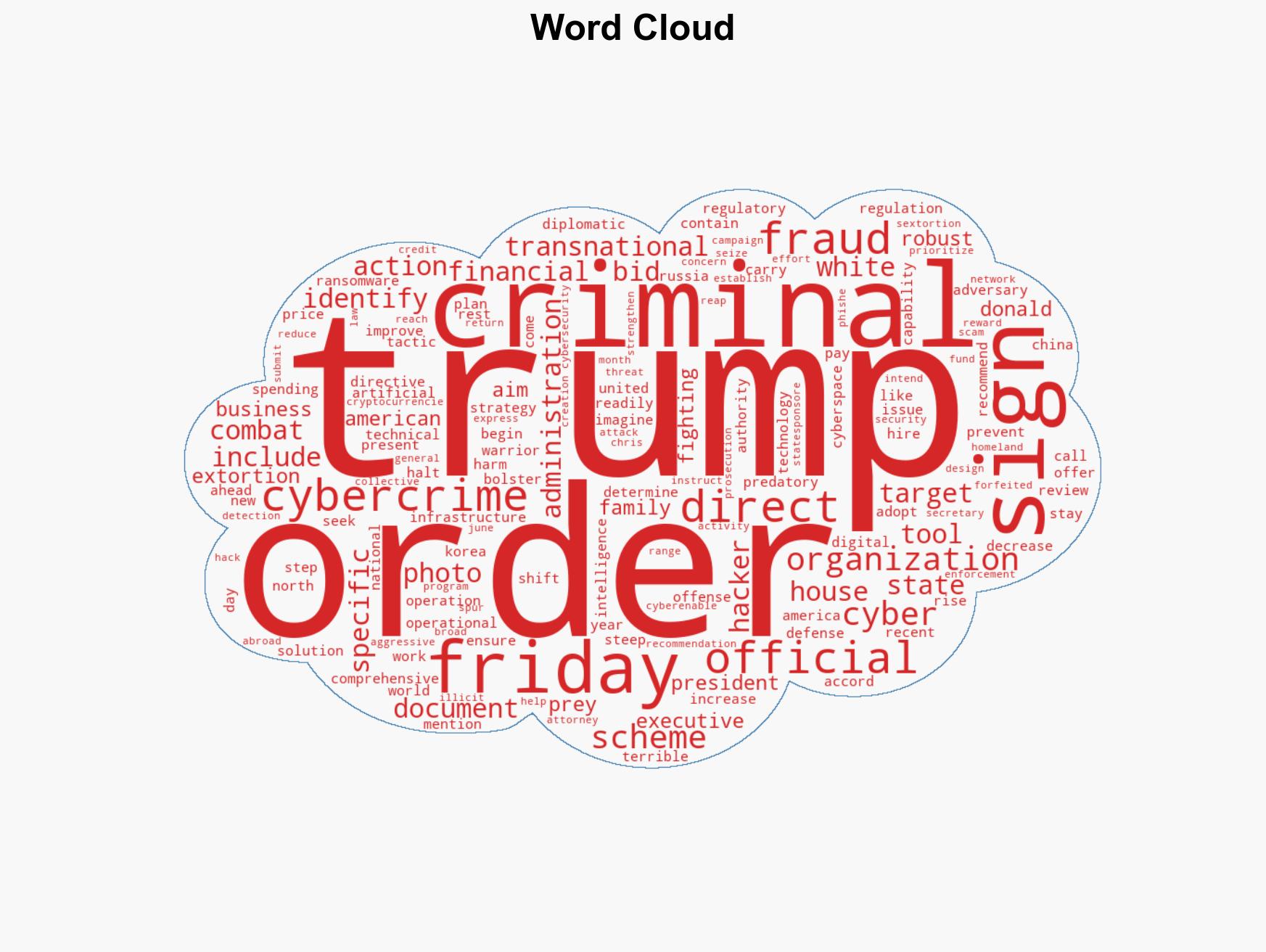
cybersecurity, cybercrime, executive order, transnational criminal organizations, cybersecurity strategy, artificial intelligence, international cooperation, regulatory policy
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us