Western Australia Auditor General Warns of Inadequate Security in Microsoft 365 Across State Agencies
Published on: 2026-03-10
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: WA auditor flags weak Microsoft 365 security controls across state entities
1. BLUF (Bottom Line Up Front)
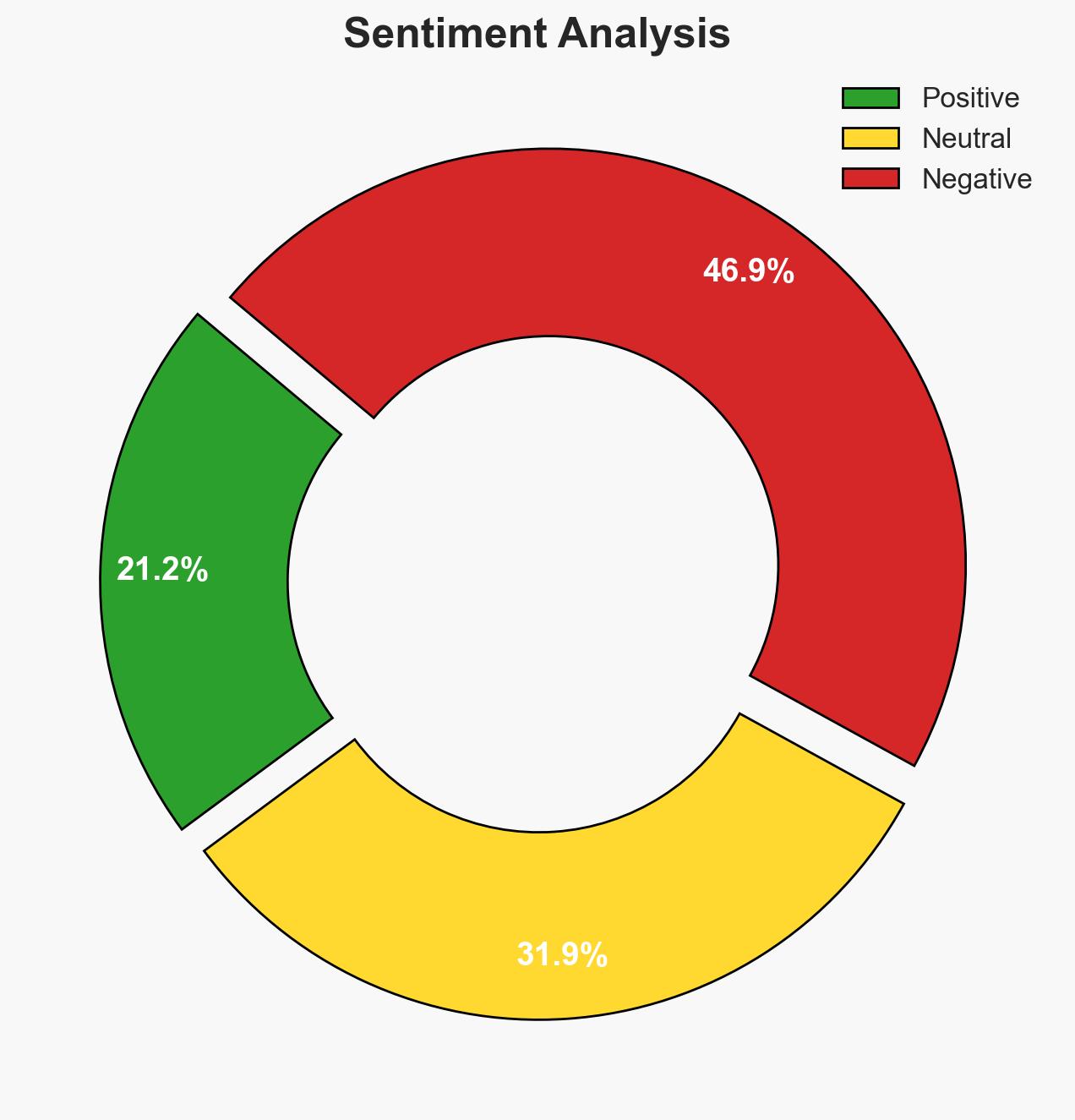
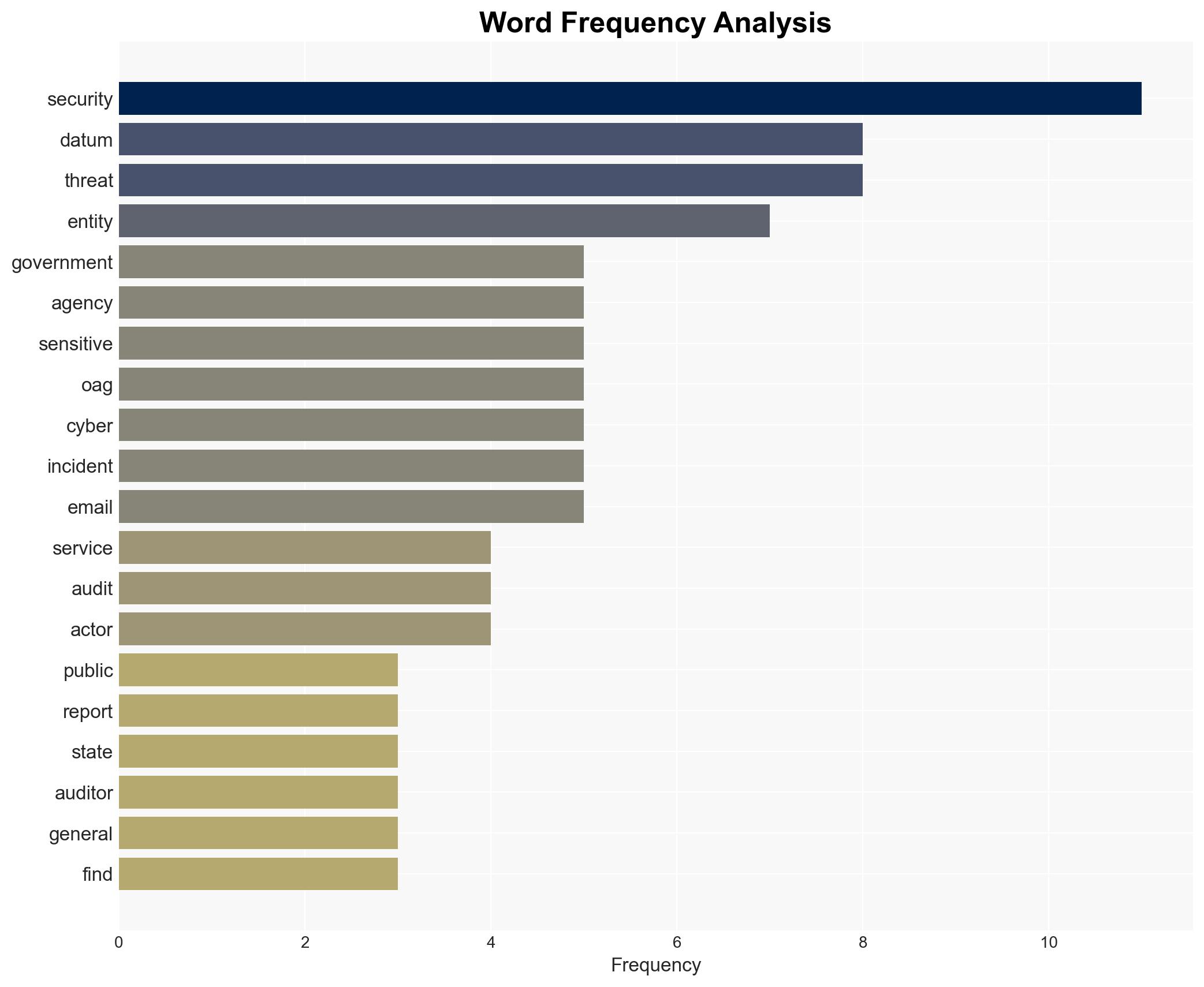
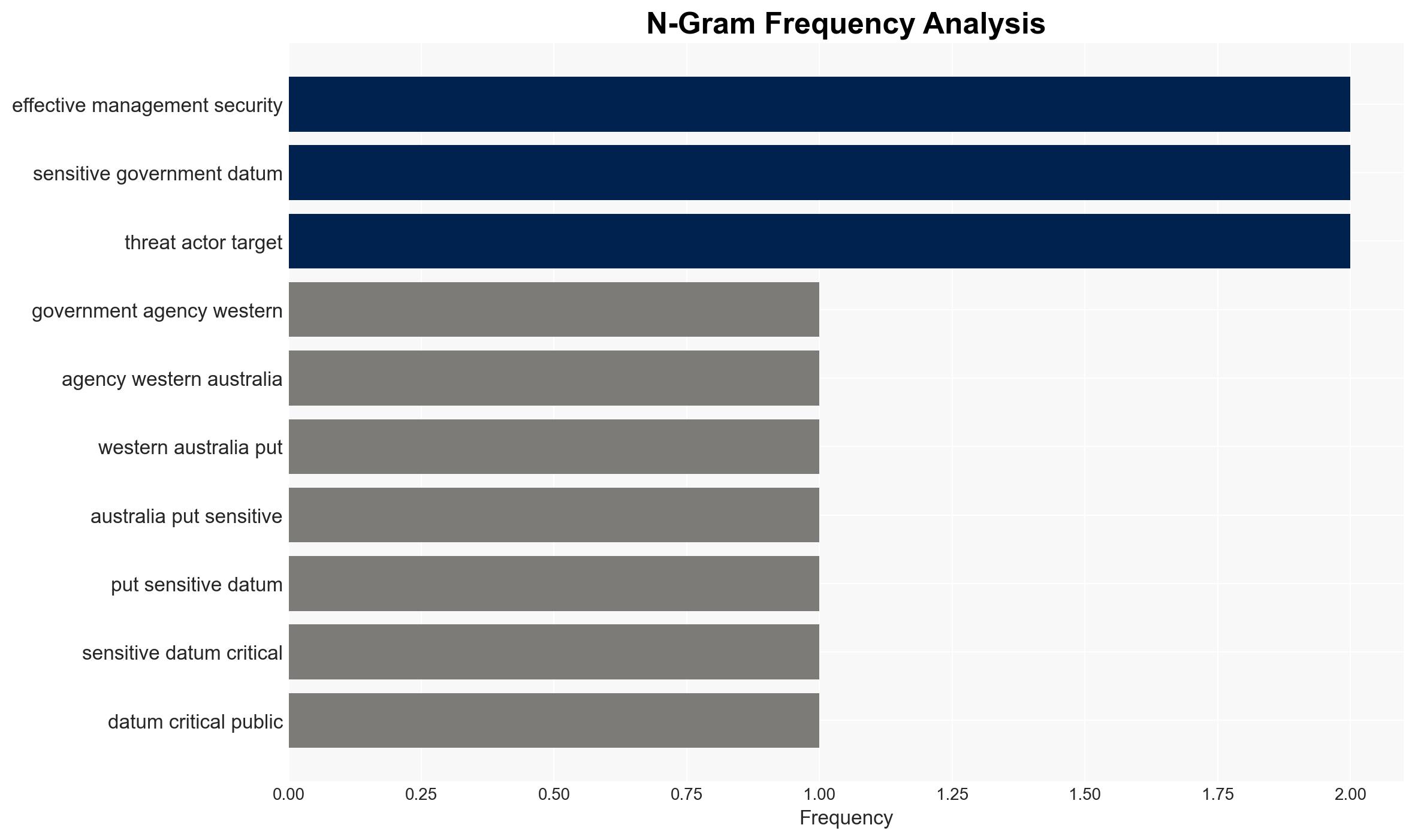
The Western Australia Office of the Auditor General (OAG) has identified significant vulnerabilities in Microsoft 365 security configurations across several state government agencies, increasing the risk of cyber incidents and data breaches. The most likely hypothesis is that these vulnerabilities stem from inadequate governance and technical oversight, affecting sensitive data and critical public services. Overall confidence in this assessment is moderate due to the lack of specific agency identification and comprehensive data.
2. Competing Hypotheses
- Hypothesis A: The vulnerabilities in M365 security are primarily due to inadequate governance and oversight within the agencies. Supporting evidence includes widespread issues in identity and access management, lack of data loss prevention controls, and insufficient security assessments of third-party providers. Key uncertainties include the specific internal processes and resource allocations of the agencies.
- Hypothesis B: The vulnerabilities are primarily due to the inherent complexity and evolving nature of cyber threats that outpace current security measures. This is supported by the evolving threat landscape and the use of sophisticated phishing techniques. However, this does not fully account for the basic security lapses identified.
- Assessment: Hypothesis A is currently better supported due to the direct evidence of governance and technical oversight failures. Indicators that could shift this judgment include new information on the agencies’ internal security policies or external threat actor capabilities.
3. Key Assumptions and Red Flags
- Assumptions: Agencies have the necessary resources but lack effective implementation; cyber threats will continue to evolve; third-party providers are not consistently vetted for security compliance.
- Information Gaps: Specific details on the agencies involved and their internal security protocols; comprehensive threat actor profiles.
- Bias & Deception Risks: Potential bias in the OAG’s report due to non-disclosure of agency names; risk of underestimating the sophistication of threat actors.
4. Implications and Strategic Risks
The identified vulnerabilities could lead to increased cyber incidents affecting government operations, public trust, and data integrity. Over time, this may necessitate significant policy and operational changes.
- Political / Geopolitical: Potential for political fallout if breaches are traced back to inadequate government oversight.
- Security / Counter-Terrorism: Increased risk of exploitation by malicious actors, potentially including state-sponsored entities.
- Cyber / Information Space: Heightened vulnerability to cyber espionage and data manipulation efforts.
- Economic / Social: Possible financial losses and erosion of public confidence in government services.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a comprehensive security audit of all state agencies; implement immediate fixes for identified vulnerabilities; enhance monitoring and incident response capabilities.
- Medium-Term Posture (1–12 months): Develop a robust governance framework for M365 security; establish partnerships with cybersecurity experts; invest in staff training and awareness programs.
- Scenario Outlook: Best: Agencies achieve full compliance and reduce vulnerabilities. Worst: Continued breaches lead to significant data loss and public distrust. Most-Likely: Incremental improvements with periodic setbacks due to evolving threats.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
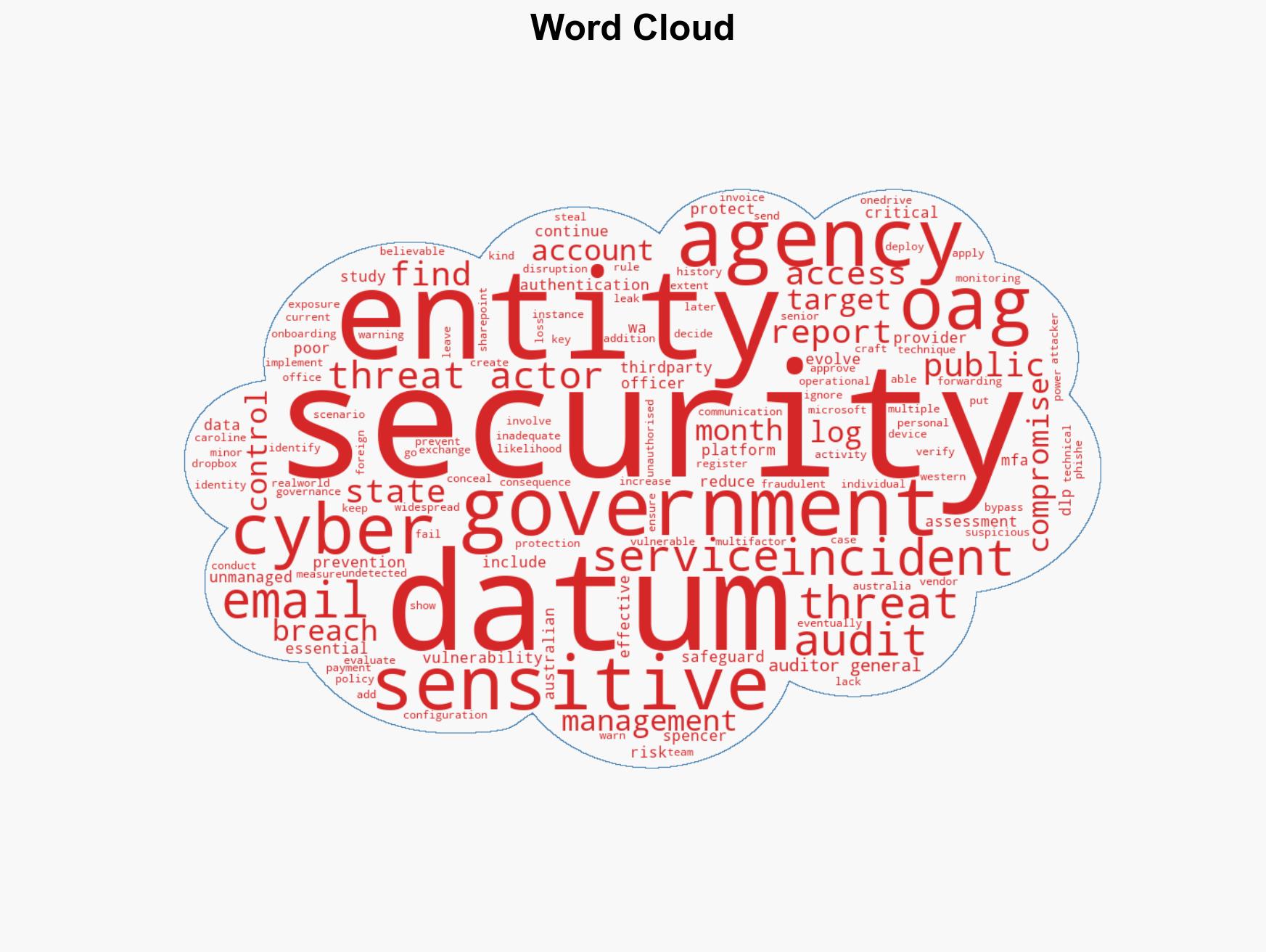
cybersecurity, government oversight, data protection, public sector, cyber threats, information security, risk management
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Forecast futures under uncertainty via probabilistic logic.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us