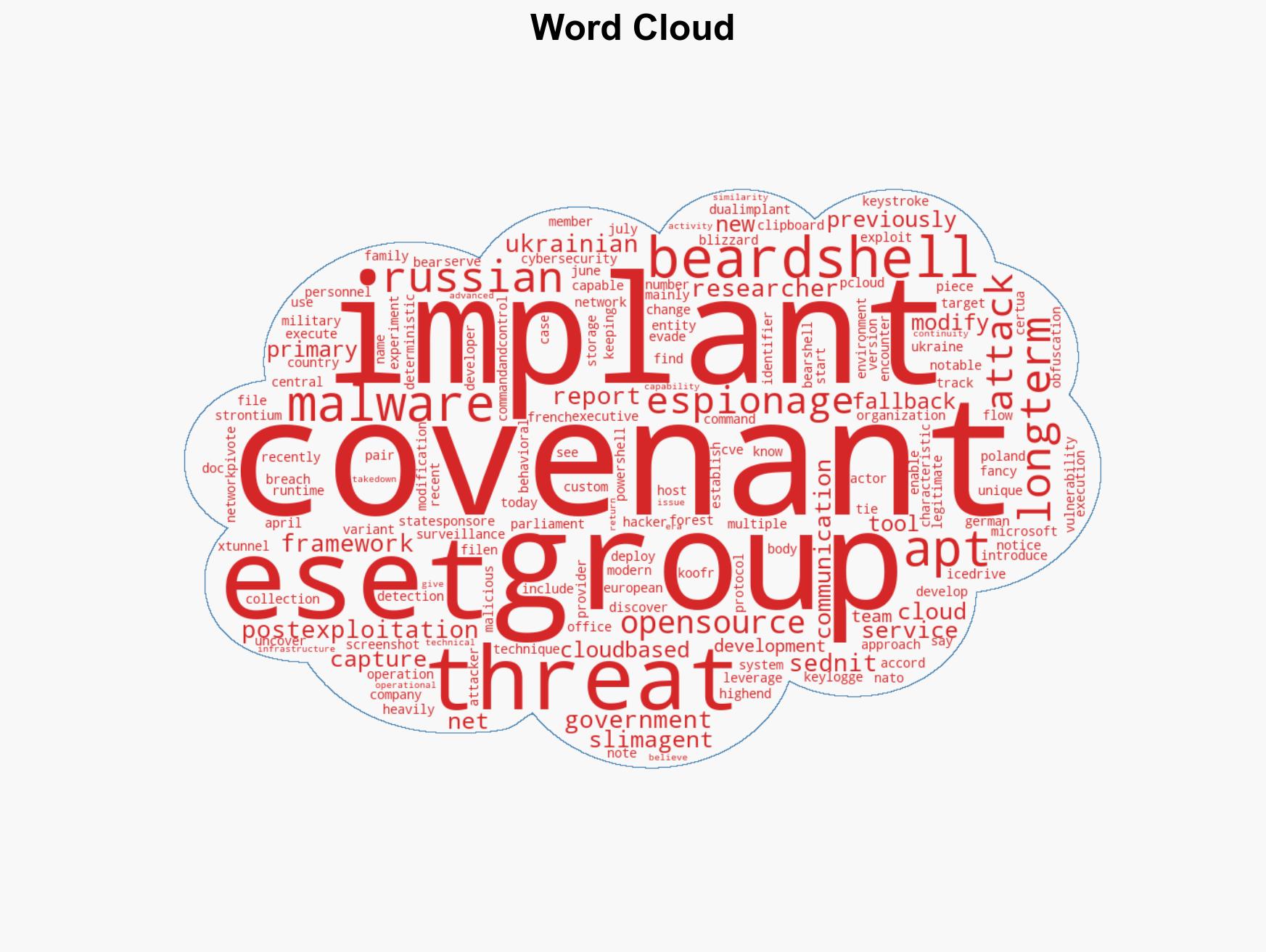
APT28 Utilizes Tailored Version of Covenant Framework for Espionage Against Ukrainian Targets
Published on: 2026-03-10
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: APT28 hackers deploy customized variant of Covenant open-source tool
1. BLUF (Bottom Line Up Front)
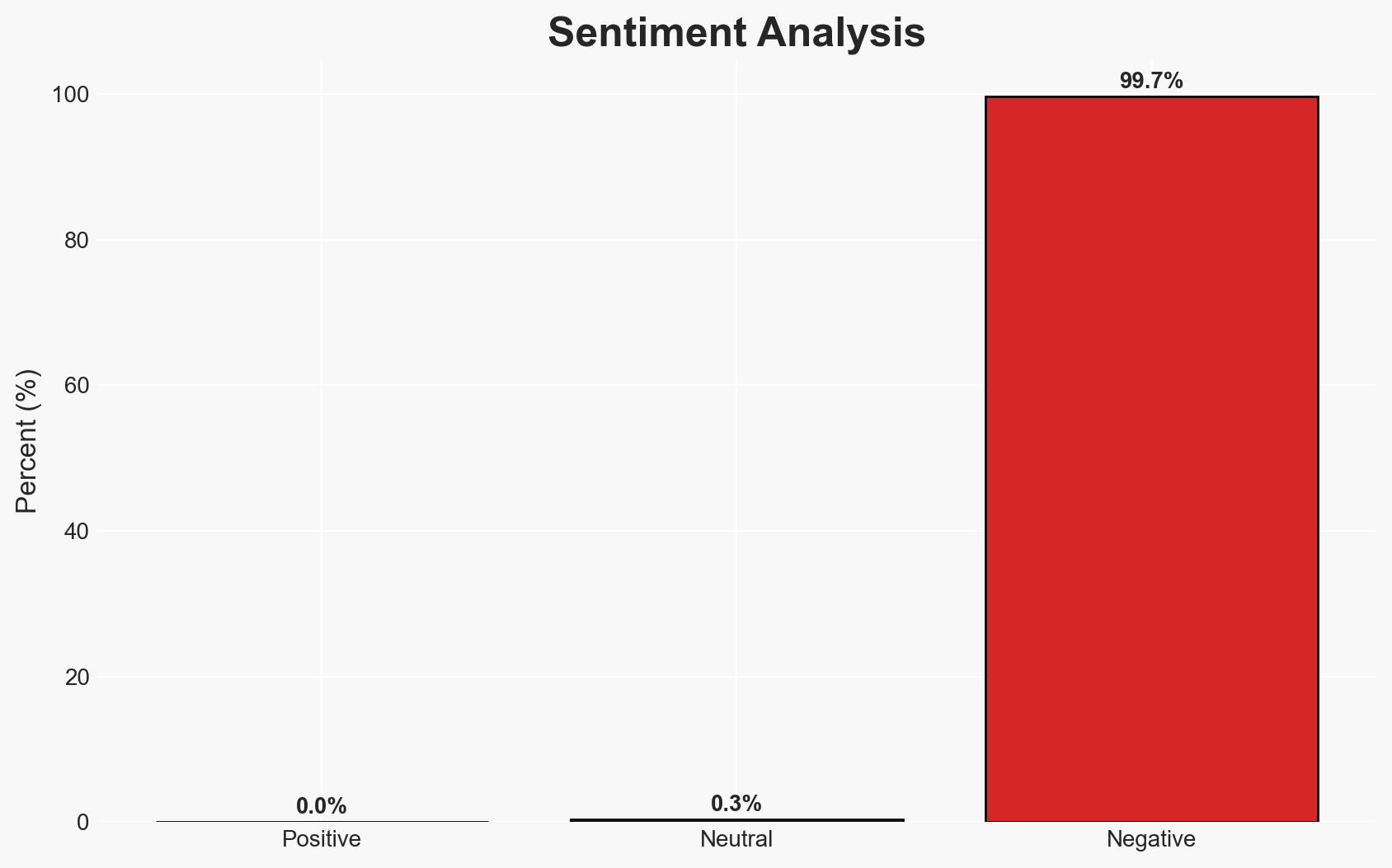
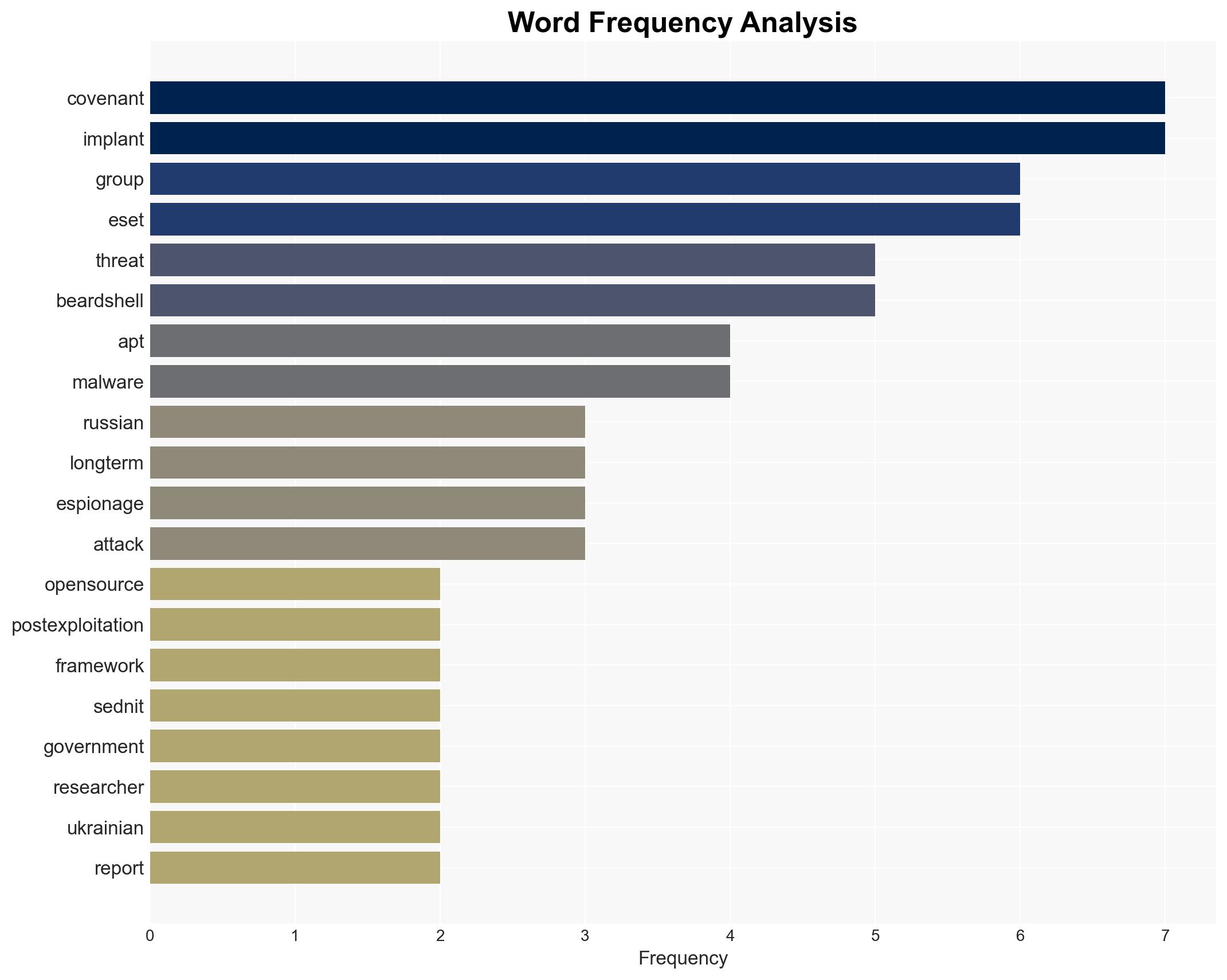
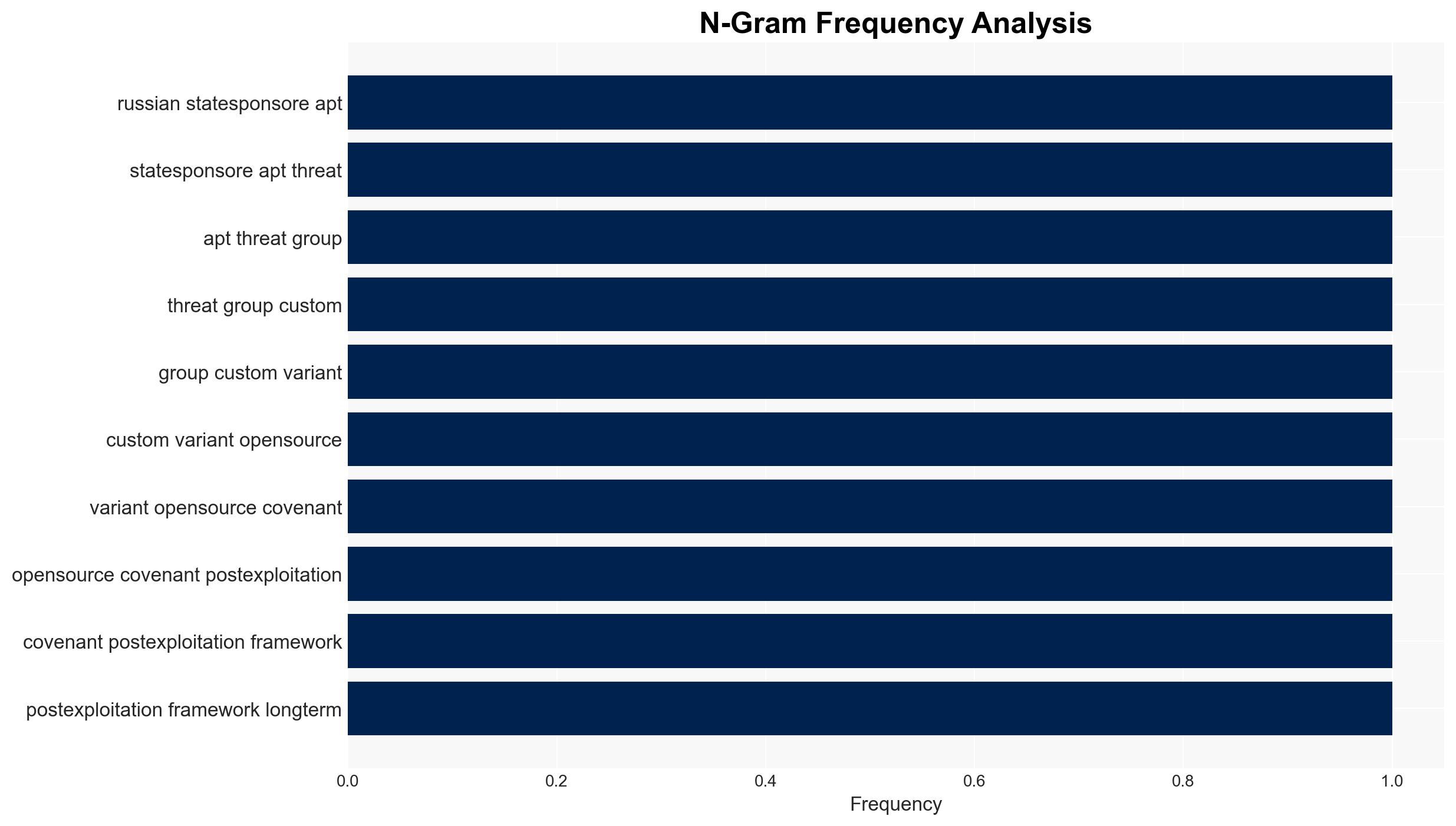
The Russian state-sponsored APT28 group is employing a customized version of the Covenant framework for espionage operations targeting Ukrainian military and government entities. This development highlights APT28’s continued capability to adapt and enhance its cyber tools for strategic advantage. The primary hypothesis is that APT28 aims to maintain long-term surveillance capabilities in Ukraine. Overall confidence in this assessment is moderate due to existing information gaps and potential deception risks.
2. Competing Hypotheses
- Hypothesis A: APT28 is using the customized Covenant framework primarily to enhance its espionage capabilities against Ukrainian targets, leveraging advanced techniques for long-term surveillance. Supporting evidence includes the use of modified implants and cloud-based communication protocols. Key uncertainties include the full scope of targets and potential undisclosed capabilities.
- Hypothesis B: APT28’s deployment of the Covenant framework is a broader strategy to test and refine new cyber tools for use against a wider range of NATO and European targets. While this is plausible given APT28’s history, there is less direct evidence supporting this hypothesis compared to the focused operations in Ukraine.
- Assessment: Hypothesis A is currently better supported due to specific evidence of targeting Ukrainian military and government entities. Indicators that could shift this judgment include evidence of similar operations in other regions or against other strategic targets.
3. Key Assumptions and Red Flags
- Assumptions: APT28 remains aligned with Russian state objectives; the group has the technical capability to modify and deploy advanced cyber tools; Ukraine remains a primary target due to ongoing geopolitical tensions.
- Information Gaps: Details on the full range of targets and the extent of data compromised; potential undisclosed capabilities of the modified Covenant framework.
- Bias & Deception Risks: Potential cognitive bias towards assuming Russian state involvement without direct evidence; source bias from cybersecurity firms with vested interests; possible deception by APT28 to mislead attribution efforts.
4. Implications and Strategic Risks
This development could exacerbate tensions between Russia and Ukraine, with potential spillover effects on NATO relations. The enhanced capabilities of APT28 may lead to increased cyber threats across Europe.
- Political / Geopolitical: Escalation in cyber operations could lead to diplomatic confrontations or sanctions against Russia.
- Security / Counter-Terrorism: Increased cyber threat level for Ukrainian and potentially NATO-aligned entities.
- Cyber / Information Space: Potential for broader cyber campaigns targeting critical infrastructure and information systems.
- Economic / Social: Disruption of government operations and potential economic impacts in targeted regions.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of APT28 activities; increase cybersecurity measures for Ukrainian and NATO networks; engage in diplomatic channels to address potential escalations.
- Medium-Term Posture (1–12 months): Develop resilience measures and cybersecurity partnerships; invest in threat intelligence capabilities to anticipate future APT28 operations.
- Scenario Outlook:
- Best: Successful deterrence and mitigation efforts lead to decreased APT28 activity.
- Worst: Expanded cyber operations by APT28 result in significant disruptions and geopolitical tensions.
- Most-Likely: Continued targeted operations in Ukraine with potential expansion to other strategic targets.
6. Key Individuals and Entities
- APT28 (Fancy Bear, Forest Blizzard, Strontium, Sednit)
- Ukrainian military and government entities
- Cybersecurity firm ESET
- CERT-UA
7. Thematic Tags
cybersecurity, cyber-espionage, APT28, Ukraine, Russian state-sponsored, Covenant framework
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us