FBI wiretap network potentially compromised through vendor’s ISP in sophisticated supply chain attack
Published on: 2026-03-10
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
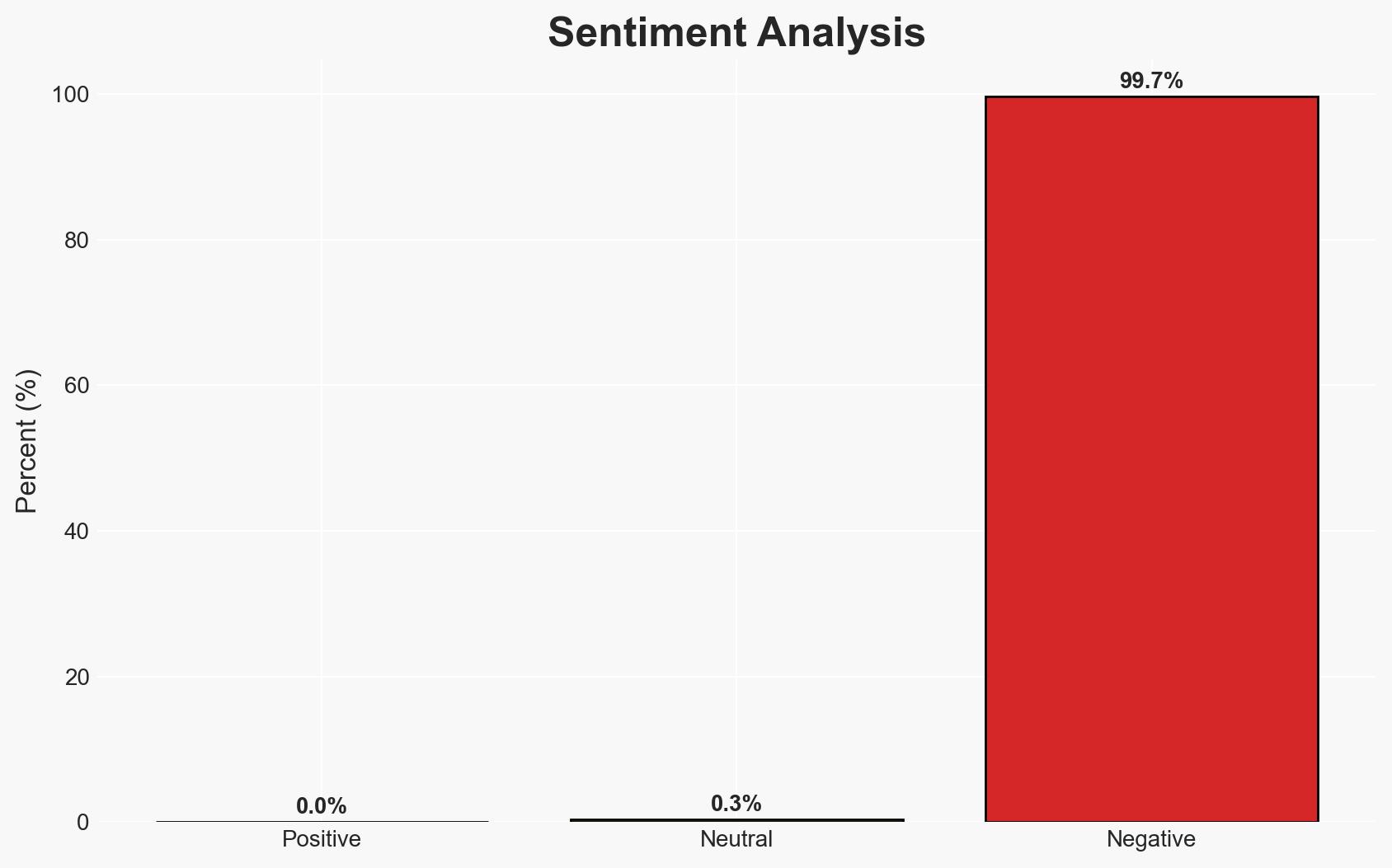
Intelligence Report: Hackers may have breached FBI wiretap network via supply chain
1. BLUF (Bottom Line Up Front)
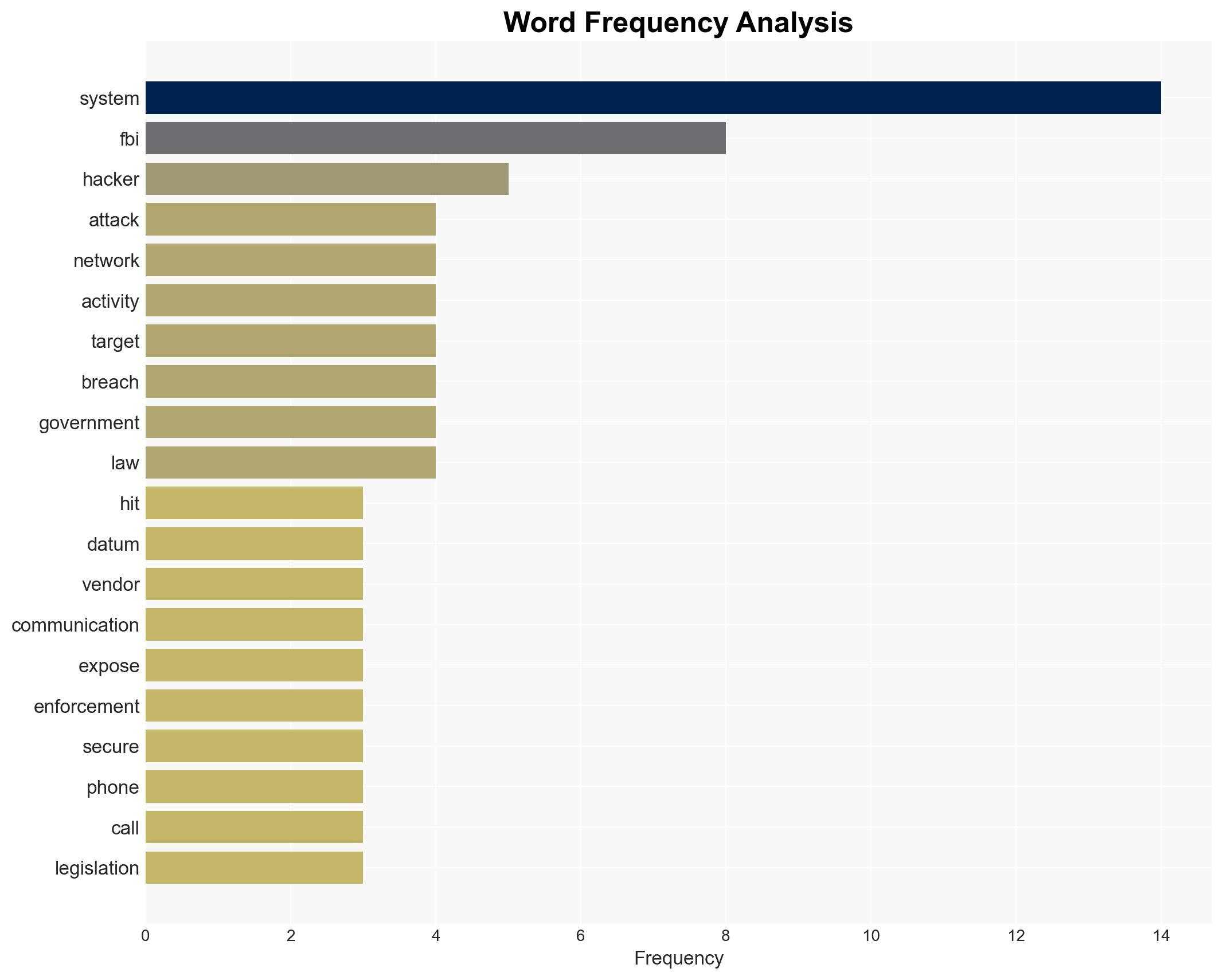
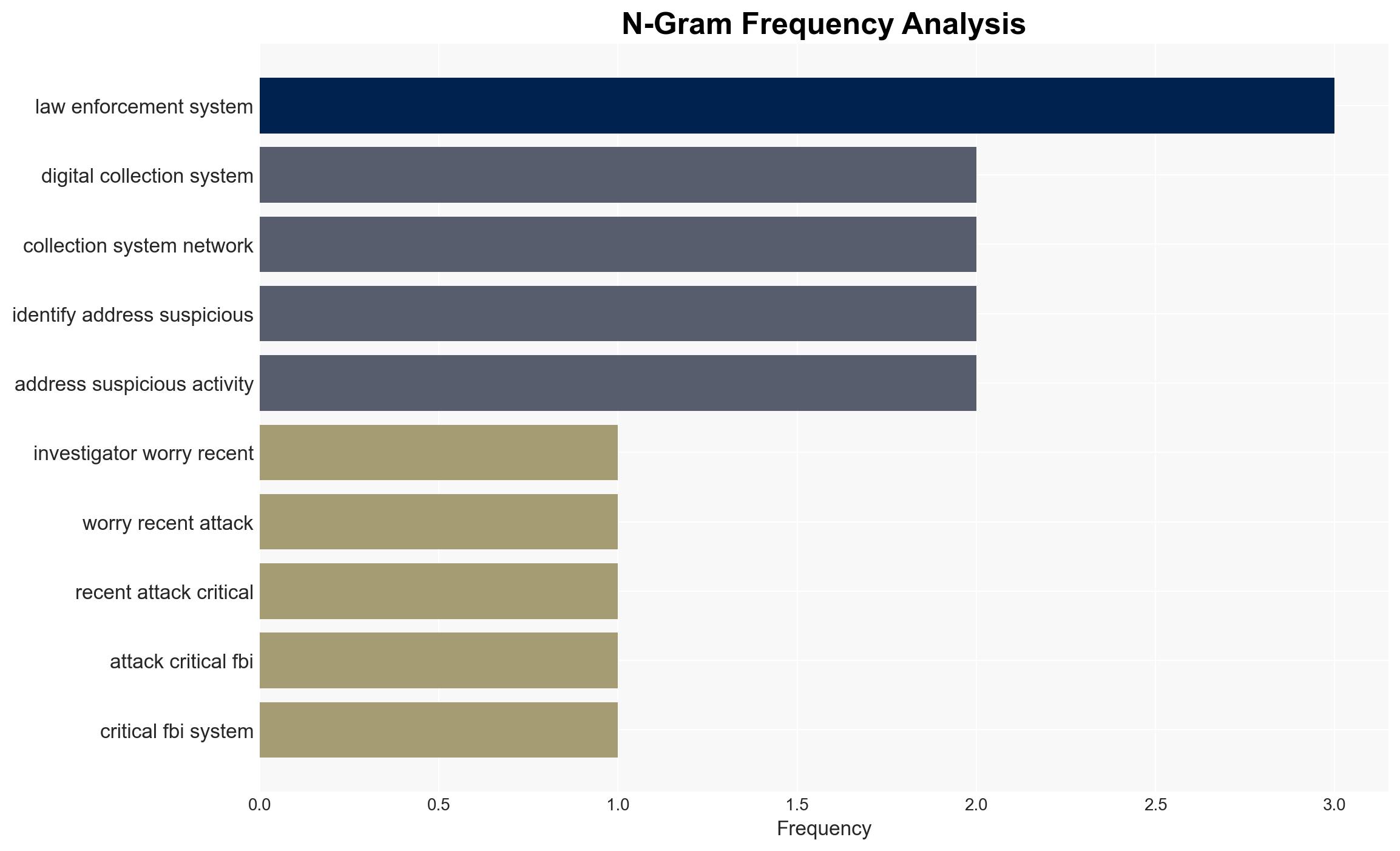
The FBI’s Digital Collection System Network may have been breached through a supply chain vulnerability, potentially involving nation-state actors, with Chinese government-affiliated hackers as a primary suspect. This incident underscores vulnerabilities in critical national security systems and highlights the sophistication of cyber threats. The breach affects sensitive legal and personal data, with moderate confidence in the assessment due to limited public information.
2. Competing Hypotheses
- Hypothesis A: The breach was conducted by Chinese state-affiliated hackers exploiting a supply chain vulnerability in an ISP vendor. This is supported by historical patterns of Chinese cyber operations targeting telecommunications and government systems.
- Hypothesis B: The breach was perpetrated by non-state actors or another nation-state using similar tactics, possibly to mislead attribution efforts. This hypothesis is less supported due to the lack of specific evidence pointing to alternative actors.
- Assessment: Hypothesis A is currently better supported due to the alignment with known Chinese cyber tactics and the involvement of high-level US agencies in the investigation. Indicators such as further attribution evidence or a claim of responsibility could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The breach involved sophisticated actors; the FBI’s internal defenses were not directly compromised; the ISP vendor was the primary vector.
- Information Gaps: Specific details on the breach method, the extent of data accessed, and confirmation of the actors involved.
- Bias & Deception Risks: Potential bias in attributing the attack to Chinese actors due to historical precedent; risk of deception by actors using false flags to mislead attribution.
4. Implications and Strategic Risks
This breach could lead to increased scrutiny of supply chain vulnerabilities and heightened tensions in cyber diplomacy. It may also prompt legislative and regulatory responses to bolster cybersecurity.
- Political / Geopolitical: Potential escalation in US-China cyber tensions; increased diplomatic efforts to address cyber threats.
- Security / Counter-Terrorism: Enhanced threat to law enforcement operations and intelligence collection capabilities.
- Cyber / Information Space: Increased focus on securing supply chains and critical infrastructure against sophisticated cyber threats.
- Economic / Social: Potential economic impacts on affected vendors and increased public concern over data privacy and security.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a comprehensive forensic analysis of the breach; enhance monitoring of vendor networks; engage in diplomatic dialogue with China.
- Medium-Term Posture (1–12 months): Develop resilience measures for supply chain security; strengthen partnerships with private sector and international allies; invest in cybersecurity capabilities.
- Scenario Outlook: Best: Strengthened cybersecurity and diplomatic resolutions; Worst: Escalation of cyber conflicts and further breaches; Most-Likely: Incremental improvements in security posture with ongoing cyber threats.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
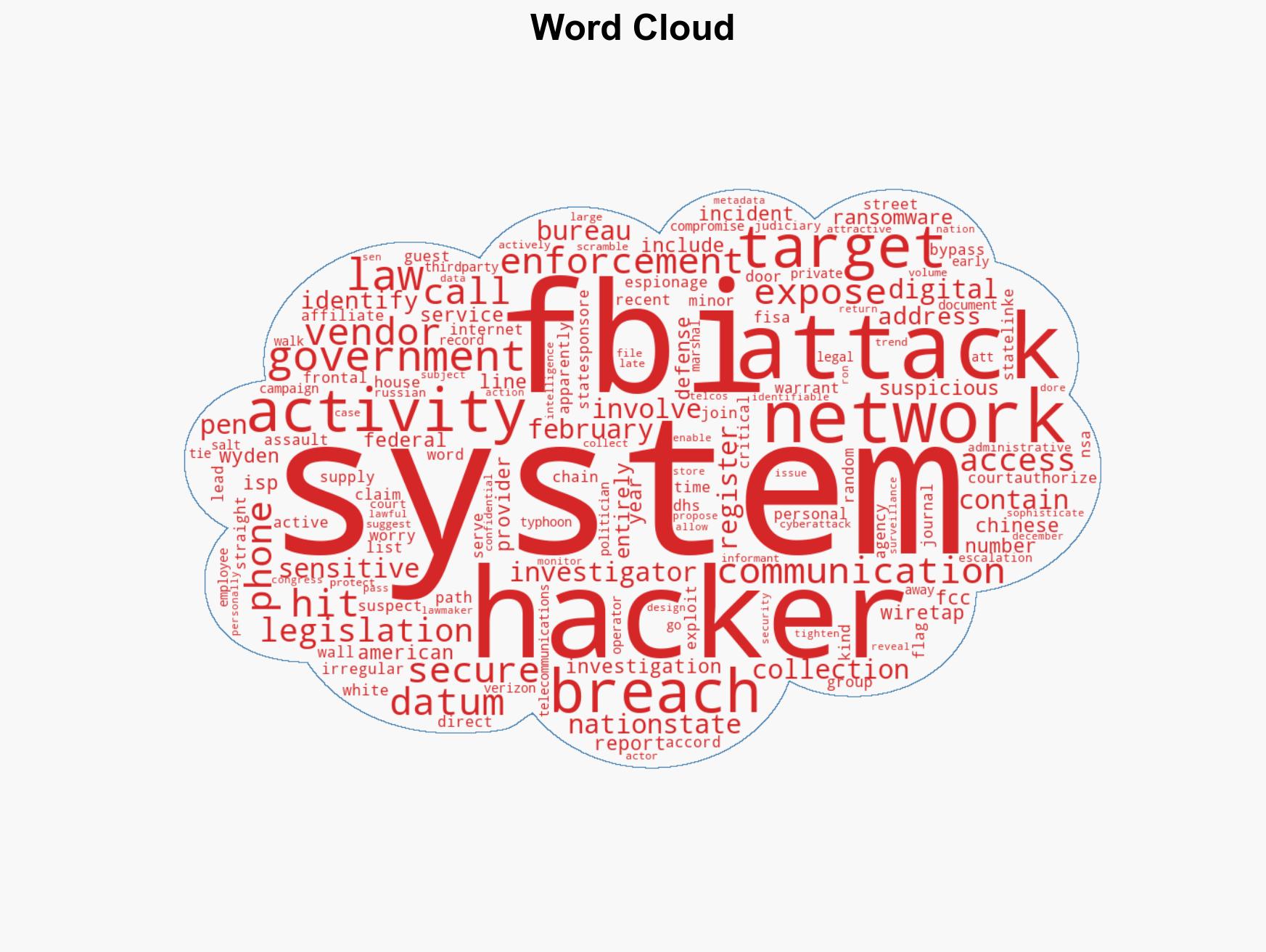
cybersecurity, supply chain, nation-state actors, data breach, FBI, Chinese cyber operations, telecommunications
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us