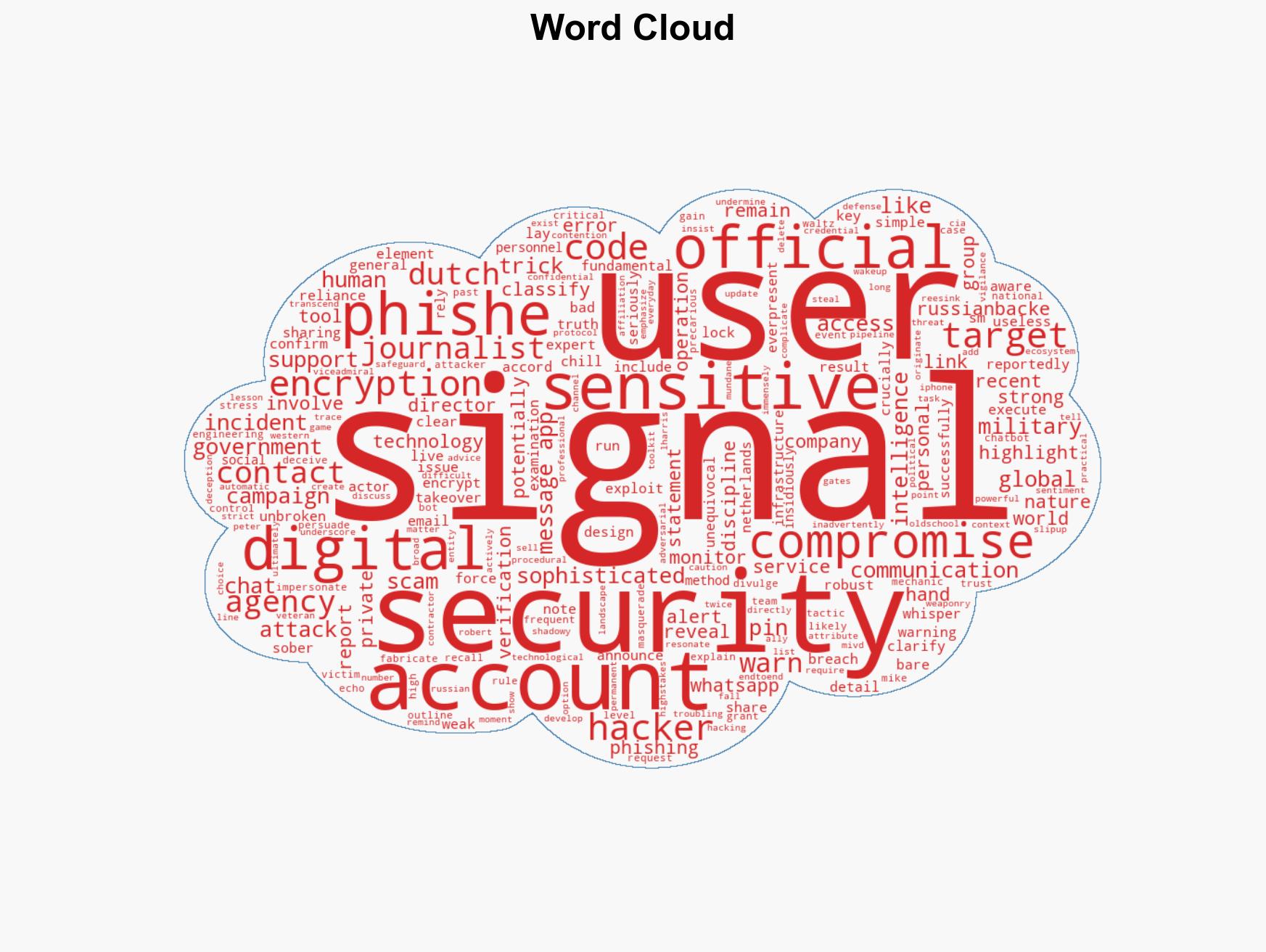
Global Phishing Attack Targets Signal Accounts of Officials and Journalists, Exploiting Human Vulnerability
Published on: 2026-03-10
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
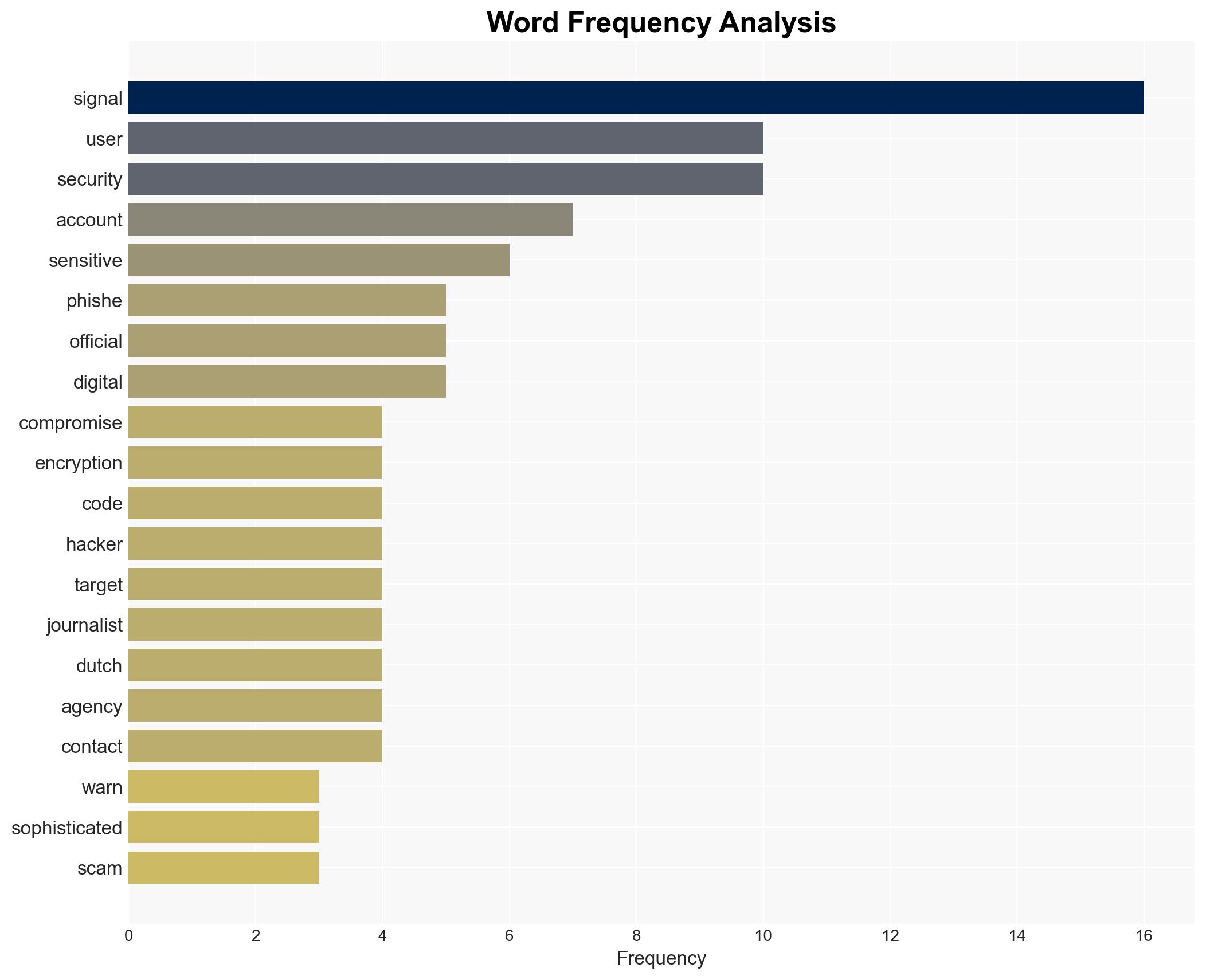
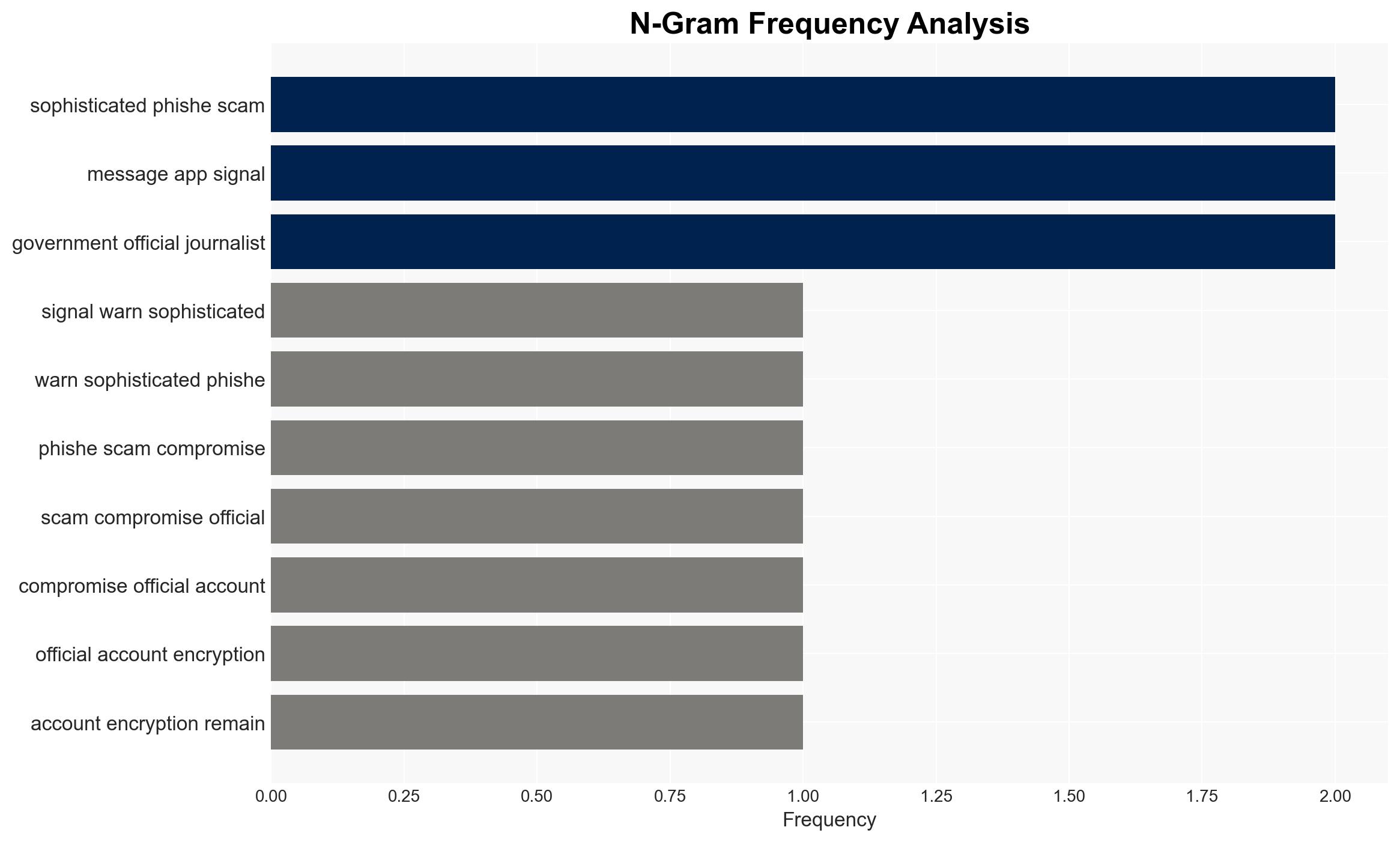
Intelligence Report: Sophisticated phishing campaign compromises Signal accounts of officials and journalists worldwide
1. BLUF (Bottom Line Up Front)
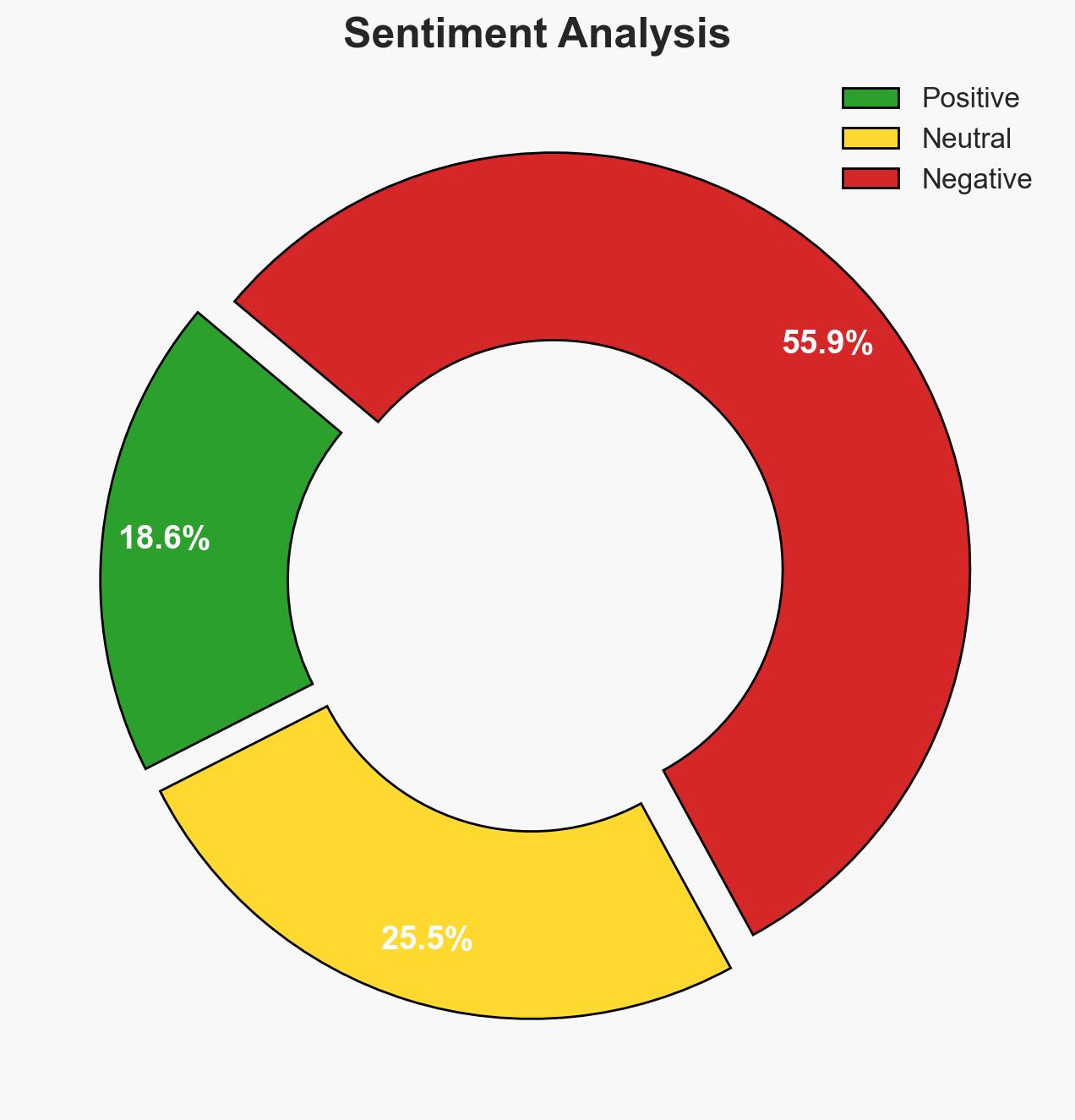
A sophisticated phishing campaign has compromised the Signal accounts of government officials and journalists worldwide. The campaign, reportedly backed by Russian hackers, exploits human error rather than technical vulnerabilities in encryption. This incident underscores the persistent threat of social engineering attacks. Overall confidence in this assessment is moderate due to the reliance on reports from intelligence agencies and the absence of direct evidence from the attackers.
2. Competing Hypotheses
- Hypothesis A: The phishing campaign is a state-sponsored operation by Russian-backed hackers targeting sensitive communications to gather intelligence. This is supported by reports from Dutch intelligence agencies and the pattern of targeting high-value individuals. However, the direct attribution to Russian state actors lacks conclusive evidence.
- Hypothesis B: The campaign is conducted by independent cybercriminals using Russian infrastructure or techniques to obfuscate their identity. This hypothesis is less supported due to the strategic targeting of officials and journalists, which aligns more with state-sponsored objectives.
- Assessment: Hypothesis A is currently better supported due to the alignment of the campaign’s targets with typical state-sponsored intelligence objectives. Indicators such as further intelligence disclosures or technical forensic evidence could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The phishing campaign is primarily motivated by intelligence gathering; the attackers have not compromised Signal’s encryption; the campaign is ongoing and may expand in scope.
- Information Gaps: Lack of direct evidence linking the attackers to Russian state actors; absence of detailed technical analysis of the phishing methods used.
- Bias & Deception Risks: Potential confirmation bias in attributing the attack to Russian actors based on historical patterns; risk of deception by attackers using false flags to mislead attribution.
4. Implications and Strategic Risks
This development could lead to increased scrutiny of encrypted messaging platforms and impact trust in digital communications. It may also prompt further geopolitical tensions if attribution to Russian state actors is confirmed.
- Political / Geopolitical: Potential diplomatic fallout and increased tensions between Russia and affected countries.
- Security / Counter-Terrorism: Heightened risk of compromised communications affecting national security operations.
- Cyber / Information Space: Increased focus on cybersecurity measures and potential regulatory actions on messaging platforms.
- Economic / Social: Possible erosion of trust in digital communication tools, impacting user behavior and platform adoption.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance user awareness campaigns on phishing risks; monitor for further phishing attempts; engage with international partners for intelligence sharing.
- Medium-Term Posture (1–12 months): Develop resilience measures for secure communications; strengthen partnerships with tech companies for rapid response capabilities.
- Scenario Outlook: Best: Phishing campaign is contained with minimal impact. Worst: Widespread compromise of sensitive communications leading to geopolitical crises. Most-Likely: Continued targeted phishing with incremental improvements in user security awareness.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, phishing, state-sponsored hacking, social engineering, encrypted communications, intelligence gathering
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model hostile behavior to identify vulnerabilities.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us