Palo Alto Networks’ Anand Oswal on Evolving Cybersecurity Amid Cloud Migration and Quantum Threats
Published on: 2026-03-10
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: From cloud shifts to quantum readiness Palo Alto Networks Executive Vice President Anand Oswal decodes the future of cybersecurity
1. BLUF (Bottom Line Up Front)
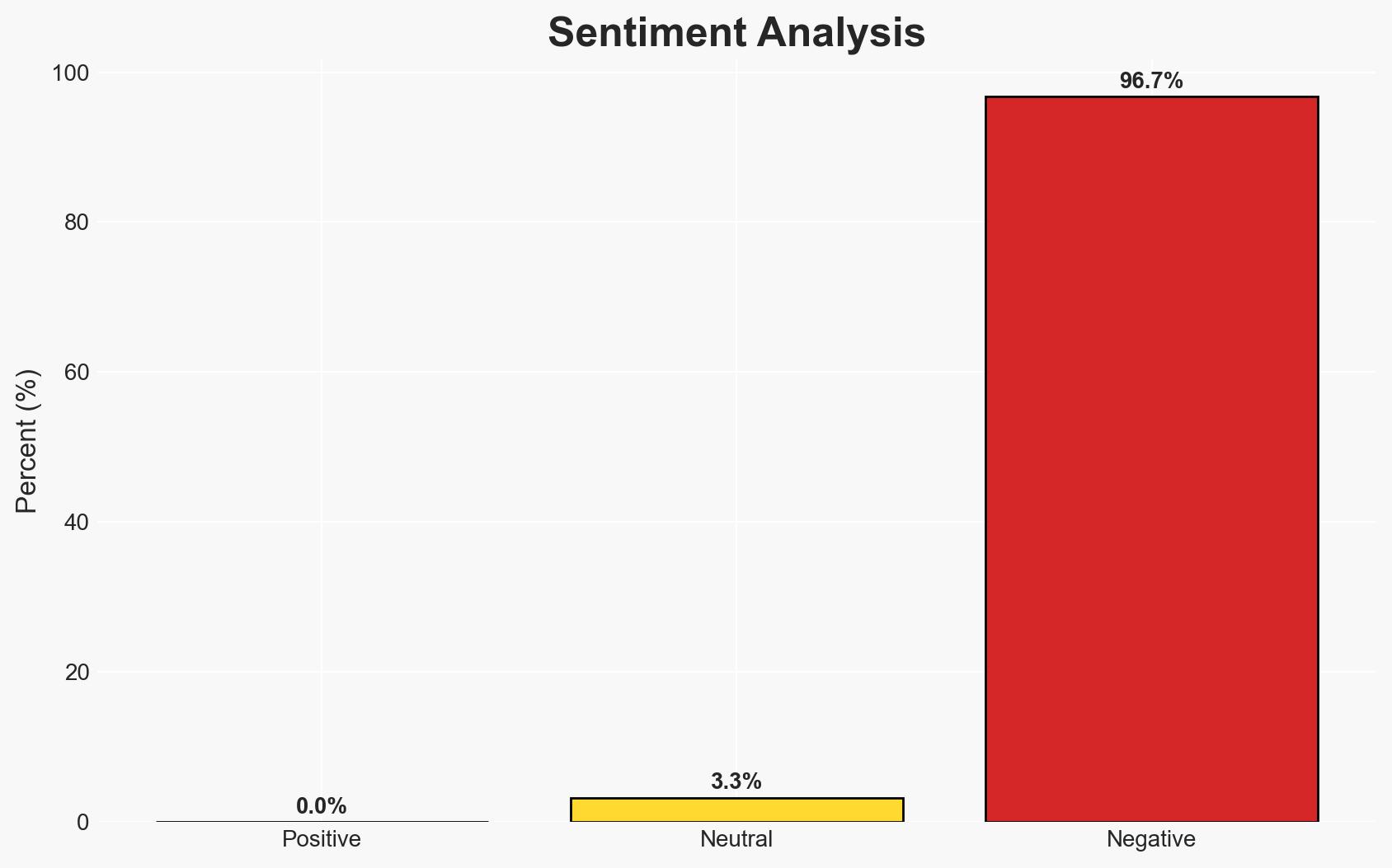
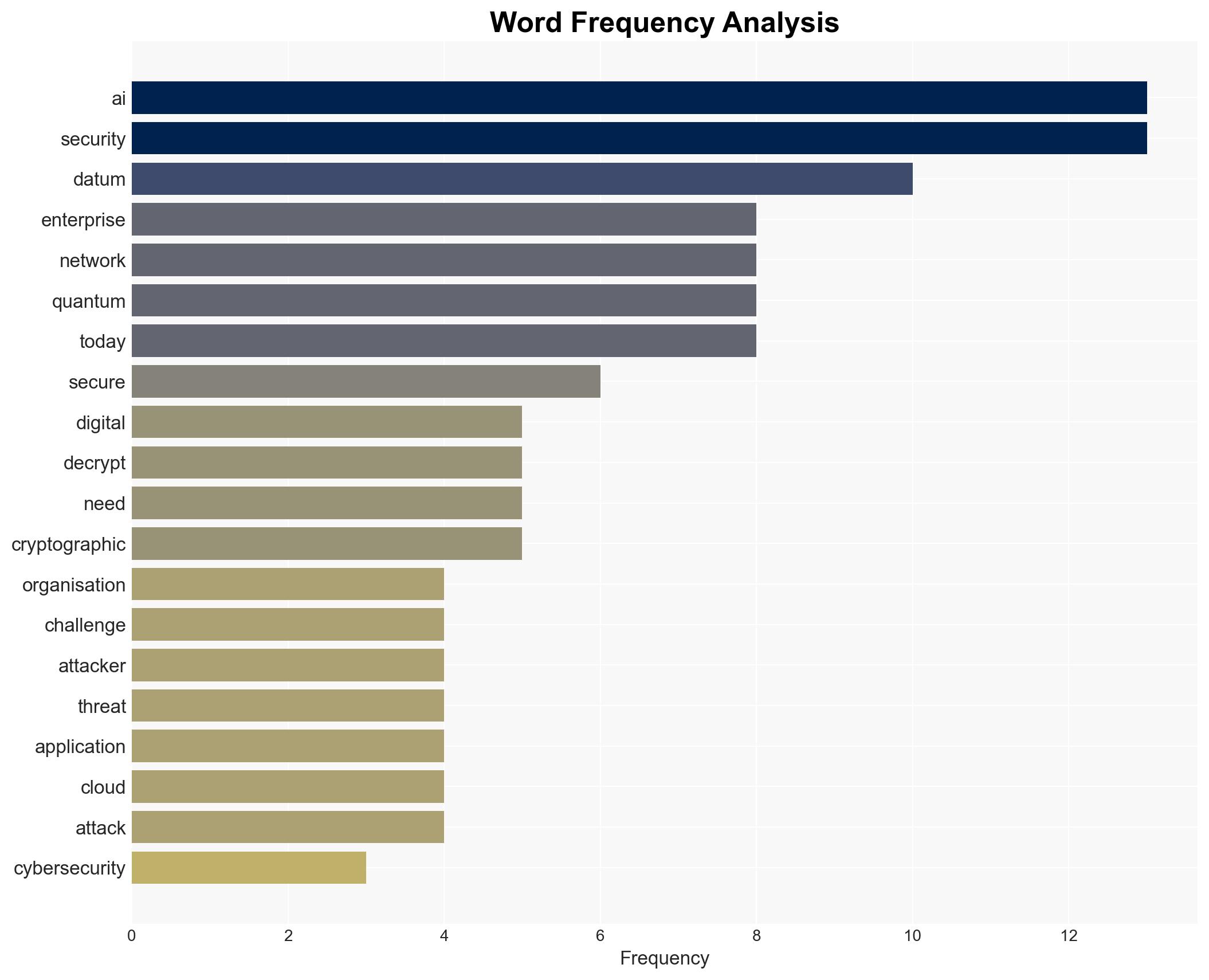
The evolution of cybersecurity is driven by the dissolution of traditional network perimeters and the rise of multi-cloud environments and hybrid work models. Organizations face significant challenges from AI-generated malware and the potential future threat of quantum computing. The most supported hypothesis is that a unified security platform is essential to address these challenges. This assessment is made with moderate confidence, affecting enterprises globally, particularly those in rapidly digitizing markets like India.
2. Competing Hypotheses
- Hypothesis A: The primary challenge for organizations is the complexity of managing security across diverse environments, necessitating a unified platform approach. This is supported by the shift from physical server security to cloud-based applications and distributed workforces. However, the extent to which organizations can effectively implement such platforms remains uncertain.
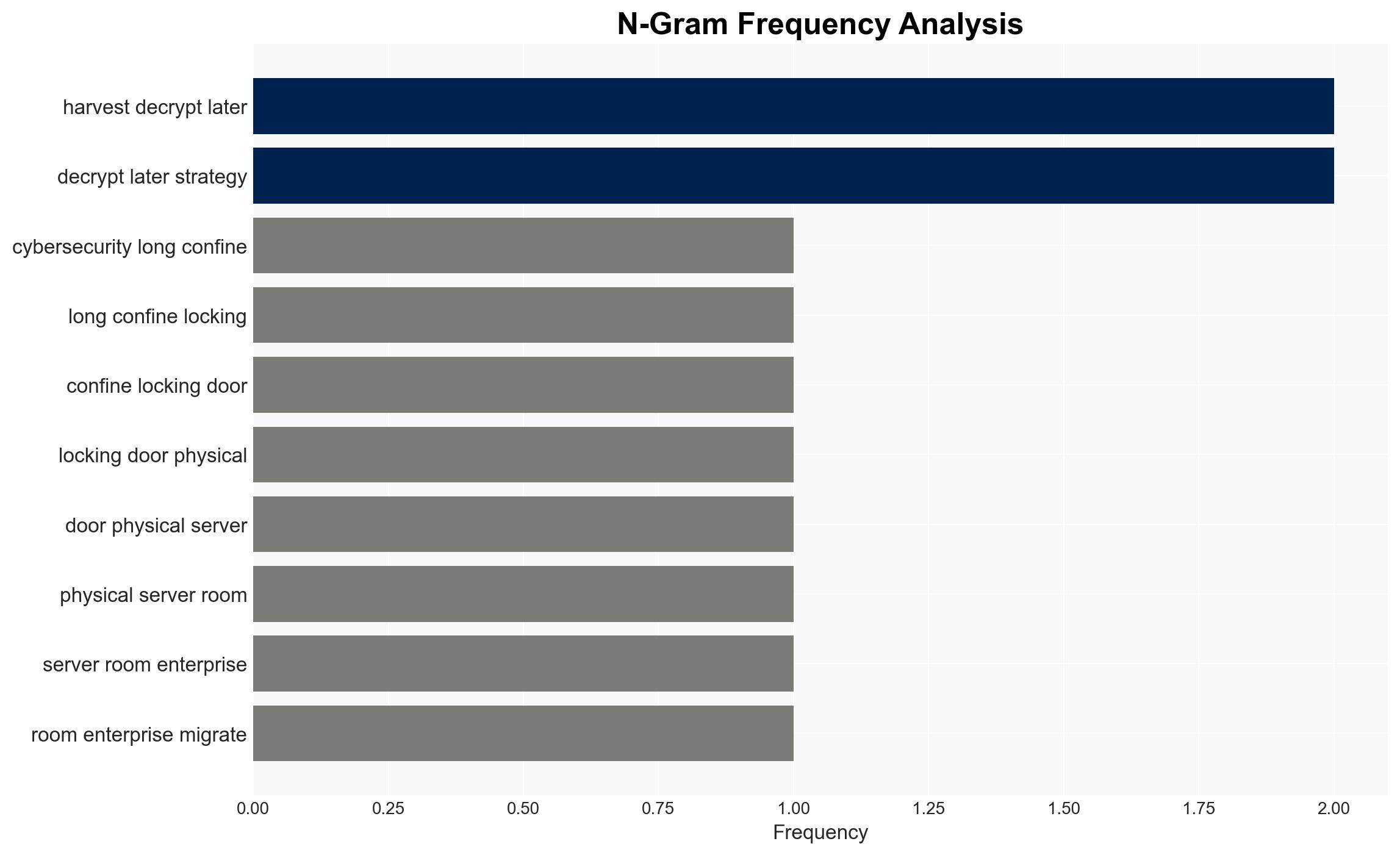
- Hypothesis B: The main threat comes from advanced cyber threats, such as AI-generated malware and future quantum decryption capabilities, which require immediate focus on cryptographic agility and AI defenses. While this is a significant concern, the current capabilities of quantum computing are not yet fully realized.
- Assessment: Hypothesis A is currently better supported due to the immediate need to manage complex, multi-cloud environments and hybrid work models. Indicators that could shift this judgment include breakthroughs in quantum computing or significant AI-driven cyber incidents.
3. Key Assumptions and Red Flags
- Assumptions: Organizations have the resources to transition to unified security platforms; AI and quantum computing will continue to advance rapidly; current cryptographic methods will eventually be vulnerable to quantum decryption.
- Information Gaps: Specific data on the adoption rate of unified security platforms and the current capabilities of quantum computing in decryption.
- Bias & Deception Risks: Potential bias from security vendors promoting unified platforms; overestimation of quantum computing threats due to speculative reporting.
4. Implications and Strategic Risks
The shift towards unified security platforms and the threat of quantum computing will reshape cybersecurity strategies. This evolution will impact various domains as follows:
- Political / Geopolitical: Nations may increase regulatory measures on cybersecurity standards, affecting international tech collaborations.
- Security / Counter-Terrorism: Enhanced cyber defenses could reduce vulnerabilities but may also drive adversaries to develop more sophisticated attack vectors.
- Cyber / Information Space: Increased focus on AI and quantum-resistant cryptography; potential rise in cyber espionage activities targeting cryptographic research.
- Economic / Social: Organizations may face increased costs for security upgrades, potentially impacting smaller enterprises and startups disproportionately.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct an audit of current security measures; prioritize the integration of unified security platforms; monitor developments in quantum computing.
- Medium-Term Posture (1–12 months): Invest in cryptographic agility and AI defenses; establish partnerships with cybersecurity firms; enhance workforce training on emerging threats.
- Scenario Outlook:
- Best: Successful integration of unified platforms leads to robust defenses against emerging threats.
- Worst: Quantum computing advances rapidly, outpacing cryptographic defenses, leading to widespread data breaches.
- Most-Likely: Gradual improvement in security measures with ongoing challenges from AI-driven threats.
6. Key Individuals and Entities
- Anand Oswal, Executive Vice President, Palo Alto Networks
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, AI threats, quantum computing, unified security platforms, multi-cloud environments, cryptographic agility, digital infrastructure
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us