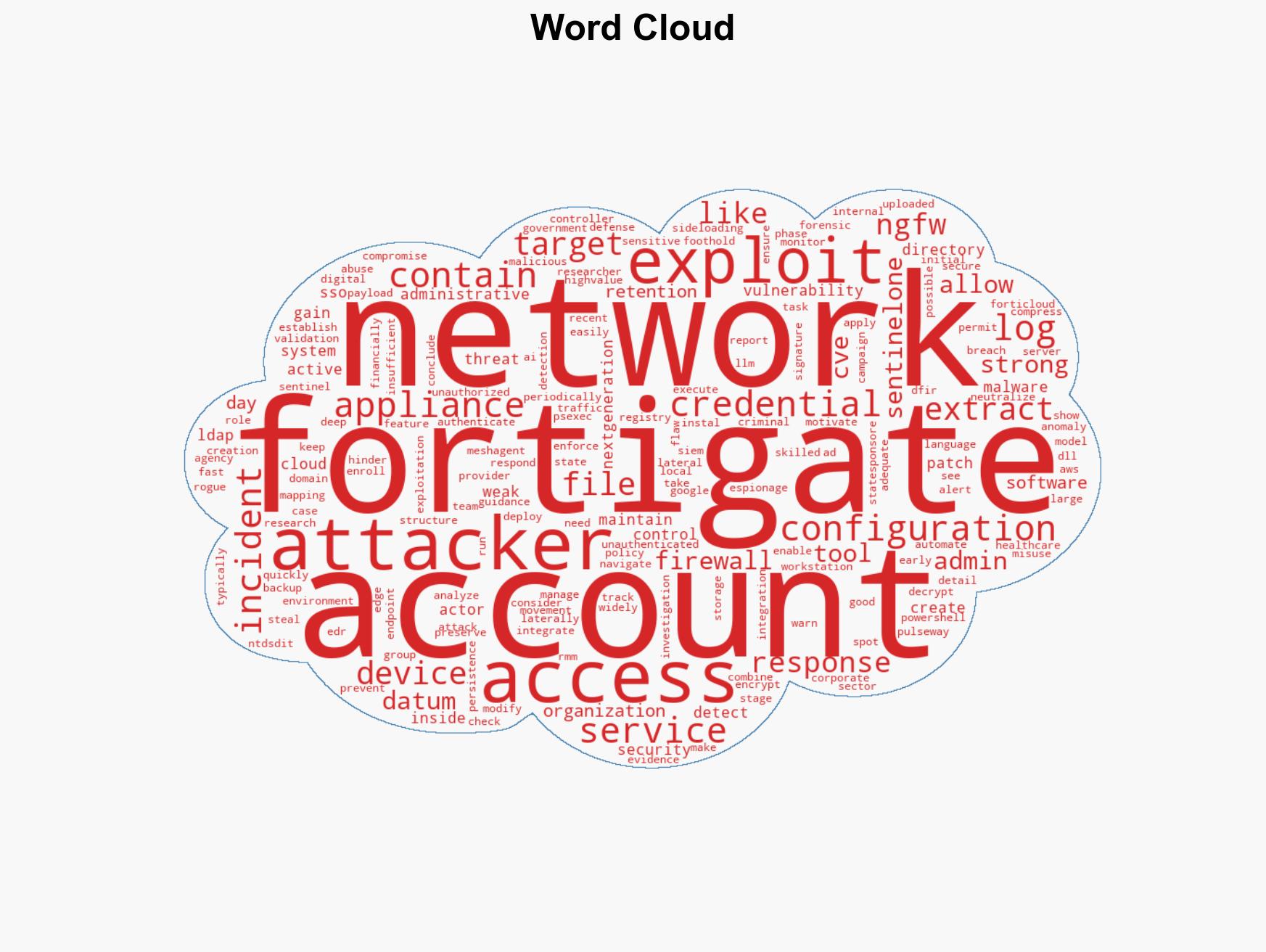
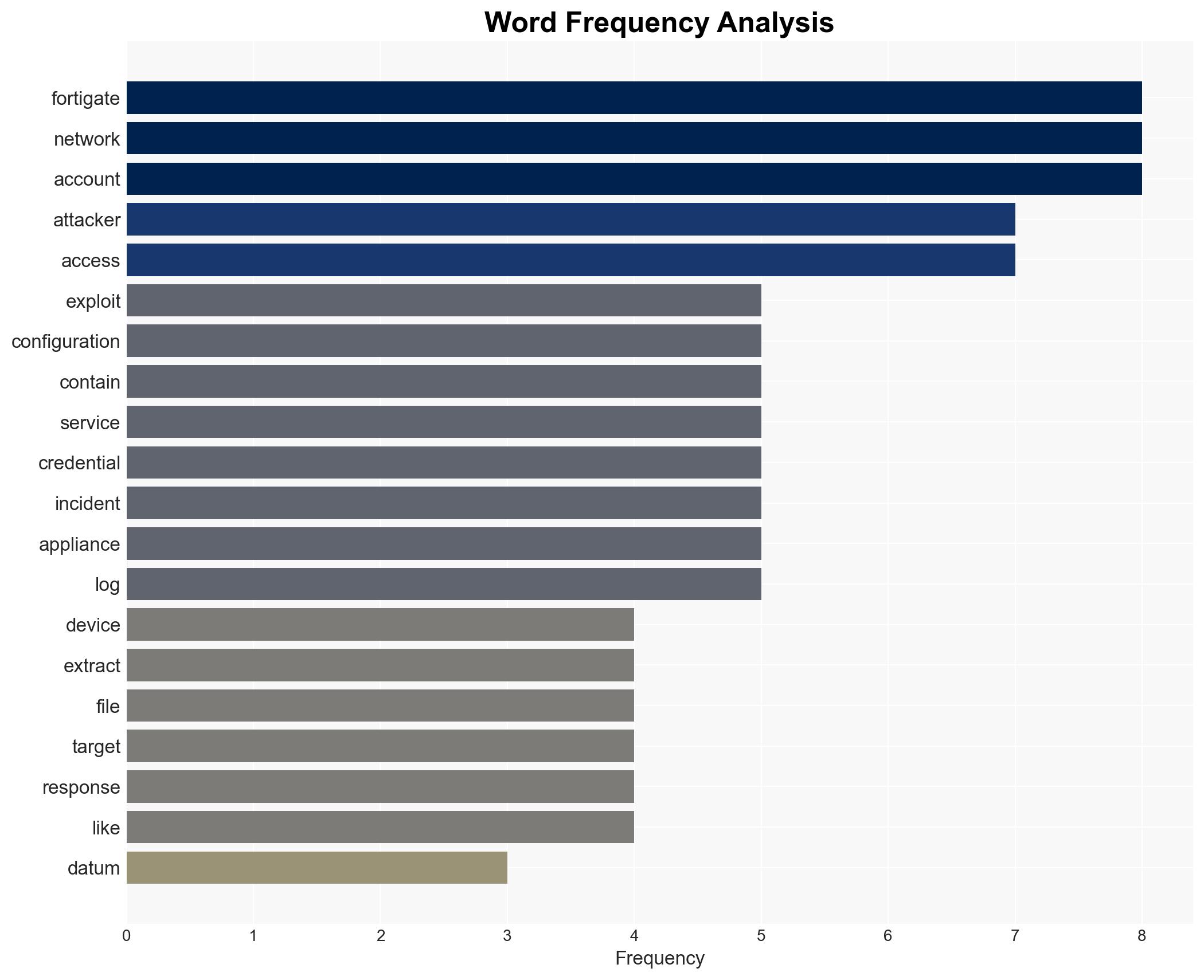
FortiGate Devices Targeted by Attackers to Steal Sensitive Network Configuration Data
Published on: 2026-03-10
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Attackers exploit FortiGate devices to access sensitive network information
1. BLUF (Bottom Line Up Front)
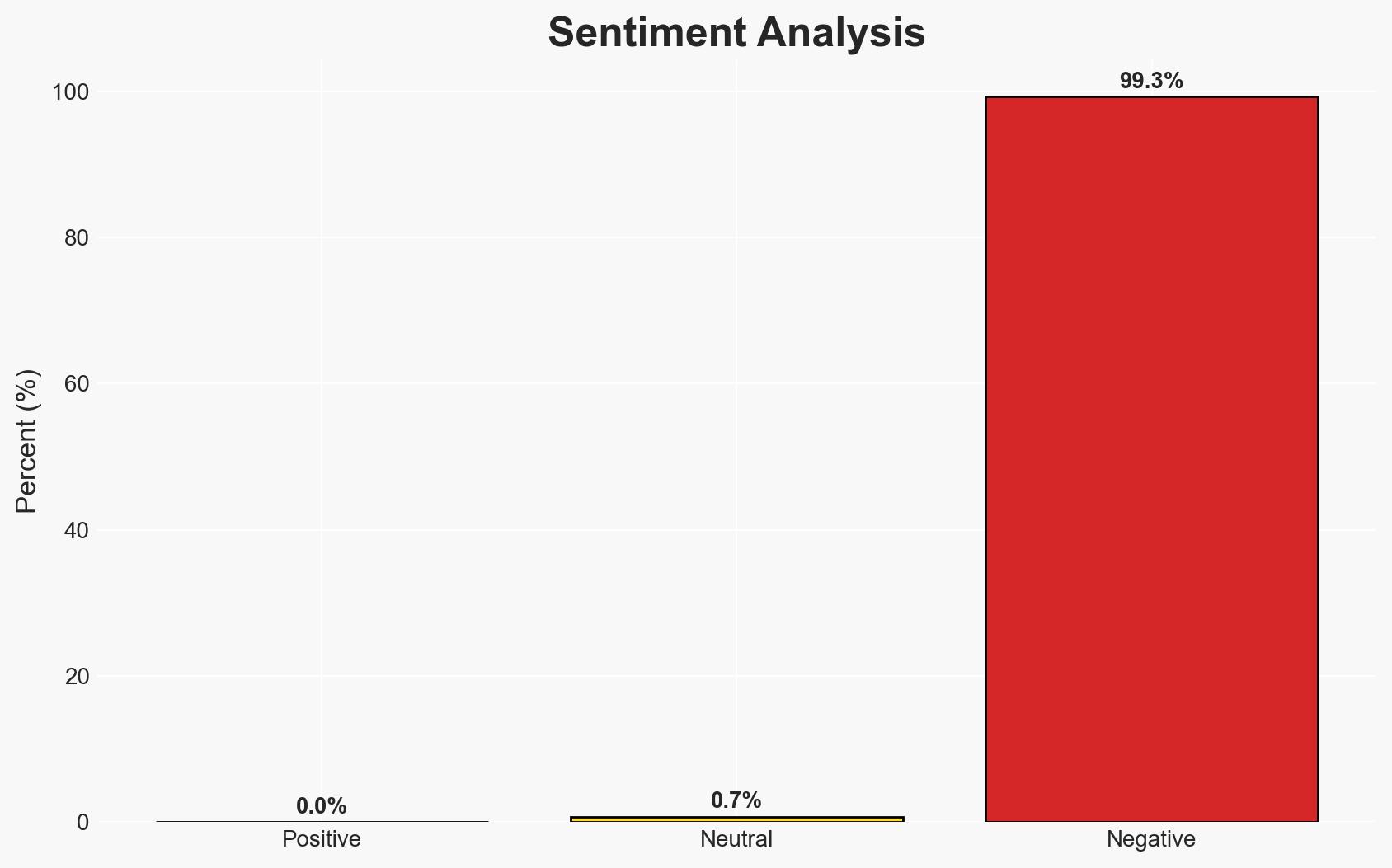
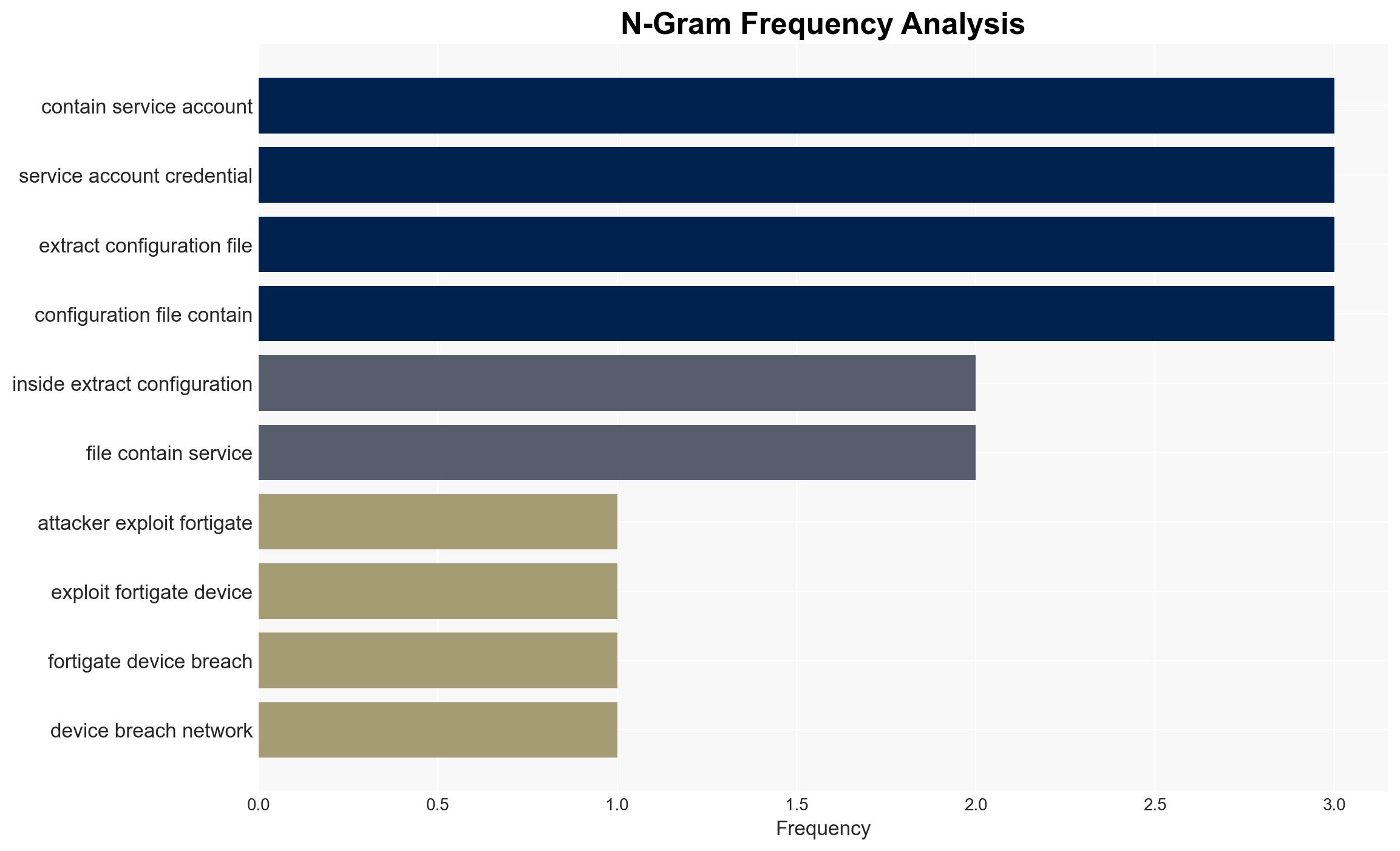
Attackers are exploiting vulnerabilities and weak credentials in FortiGate devices to gain unauthorized access to sensitive network information, affecting sectors such as healthcare, government, and managed service providers. The most likely hypothesis is that both state-sponsored and financially motivated actors are involved, leveraging AI tools to facilitate these intrusions. Overall confidence in this assessment is moderate due to incomplete information on the attackers’ identities and methods.
2. Competing Hypotheses
- Hypothesis A: State-sponsored groups are primarily responsible for exploiting FortiGate devices, using sophisticated techniques to target critical sectors. This is supported by the strategic targeting of government and healthcare sectors, but contradicted by the involvement of less skilled actors.
- Hypothesis B: A mix of state-sponsored and financially motivated actors, including less skilled individuals using AI tools, are exploiting these vulnerabilities. This hypothesis is supported by the diversity of tools and methods used, as well as the broad range of targeted sectors.
- Assessment: Hypothesis B is currently better supported due to the evidence of varied skill levels and motivations among attackers. Key indicators that could shift this judgment include the identification of specific state actors or financial gains linked to the attacks.
3. Key Assumptions and Red Flags
- Assumptions: FortiGate vulnerabilities are not yet fully patched; attackers have access to AI tools; targeted sectors have weaker cybersecurity postures.
- Information Gaps: Specific identities of the attackers; detailed methods of AI tool usage; extent of data exfiltration.
- Bias & Deception Risks: Potential over-reliance on SentinelOne’s analysis; possibility of attackers planting false flags to mislead attribution.
4. Implications and Strategic Risks
This development could lead to increased cyber threats across critical sectors, potentially destabilizing affected organizations and compromising sensitive data. Over time, this may prompt stricter regulatory measures and heightened cybersecurity investments.
- Political / Geopolitical: Escalation in cyber tensions between nations if state-sponsored involvement is confirmed.
- Security / Counter-Terrorism: Increased operational risks for targeted sectors, necessitating enhanced defensive measures.
- Cyber / Information Space: Potential proliferation of attack techniques among less skilled actors, increasing overall cyber threat landscape.
- Economic / Social: Potential economic impacts on affected sectors due to data breaches and increased cybersecurity costs.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct thorough vulnerability assessments of FortiGate devices; implement strong credential policies; monitor for unusual network activity.
- Medium-Term Posture (1–12 months): Develop partnerships for threat intelligence sharing; invest in AI-driven cybersecurity solutions; enhance incident response capabilities.
- Scenario Outlook:
- Best: Rapid patching and enhanced defenses mitigate threats, reducing successful intrusions.
- Worst: Continued exploitation leads to significant data breaches and geopolitical tensions.
- Most-Likely: Ongoing attacks with gradual improvements in defense, driven by increased awareness and investment.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, network vulnerabilities, state-sponsored attacks, AI tools, FortiGate exploitation, healthcare sector, government agencies
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us