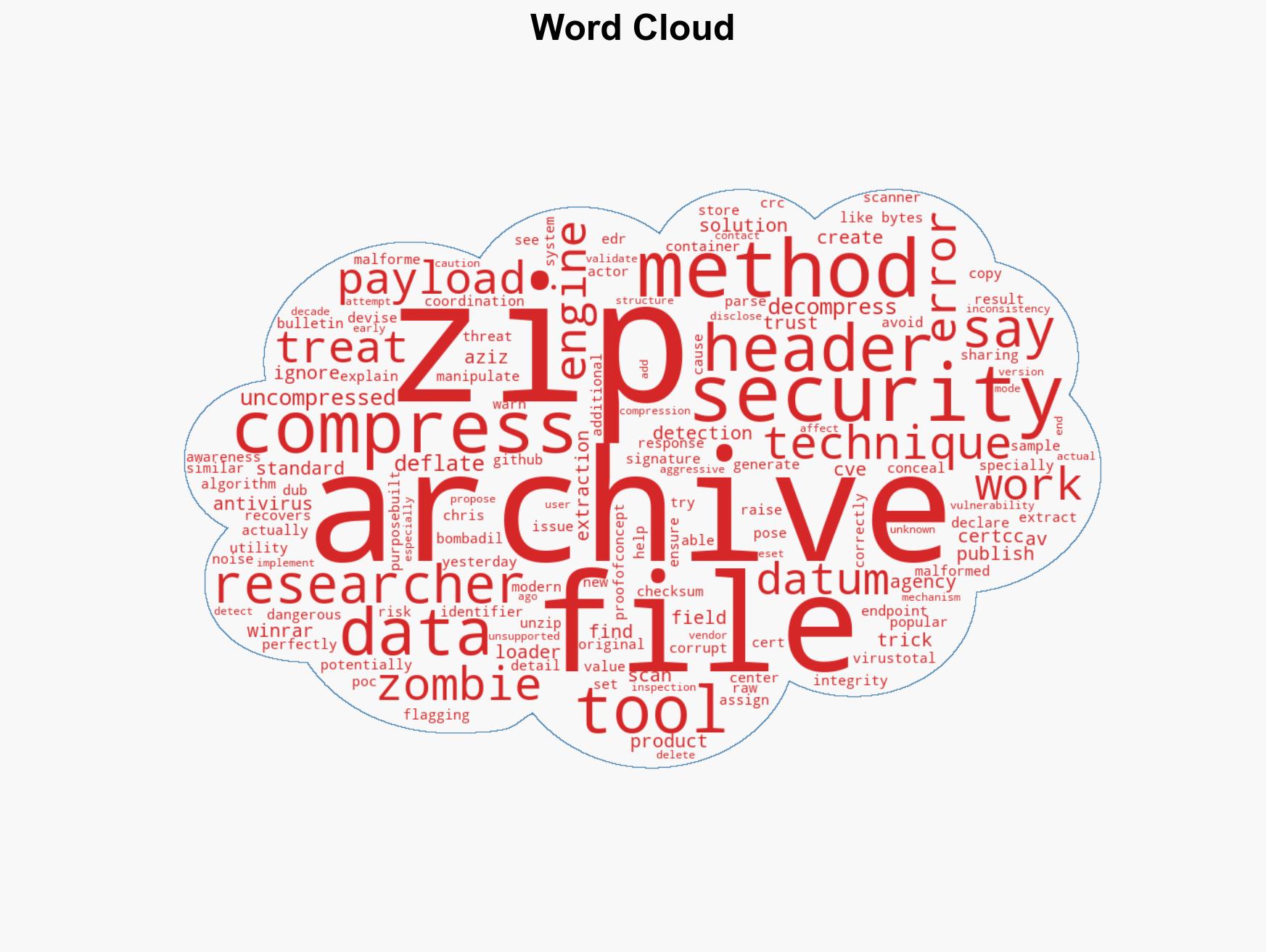
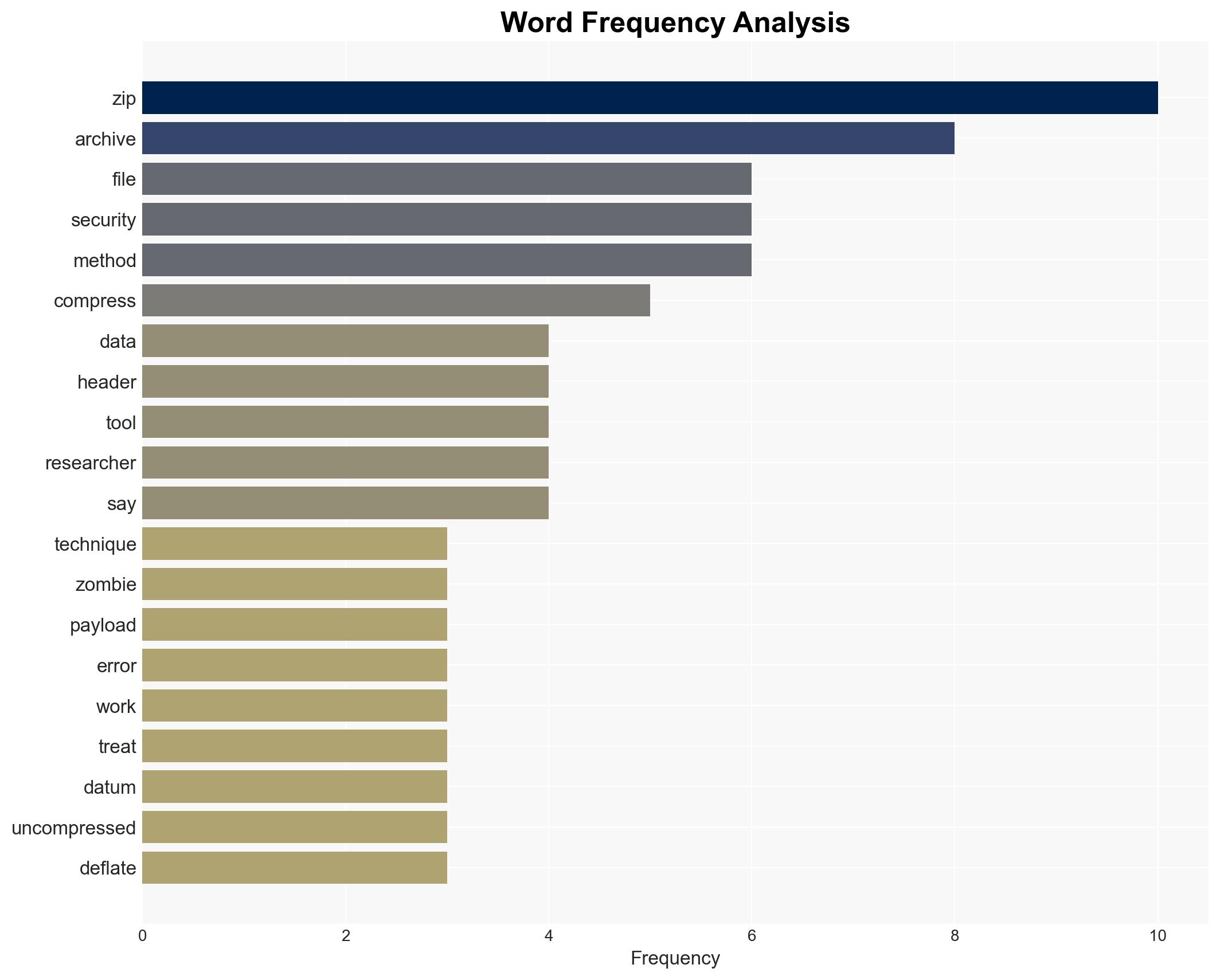
Emerging ‘Zombie ZIP’ method enables malware to bypass antivirus detection through ZIP file manipulation
Published on: 2026-03-10
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: New ‘Zombie ZIP’ technique lets malware slip past security tools
1. BLUF (Bottom Line Up Front)
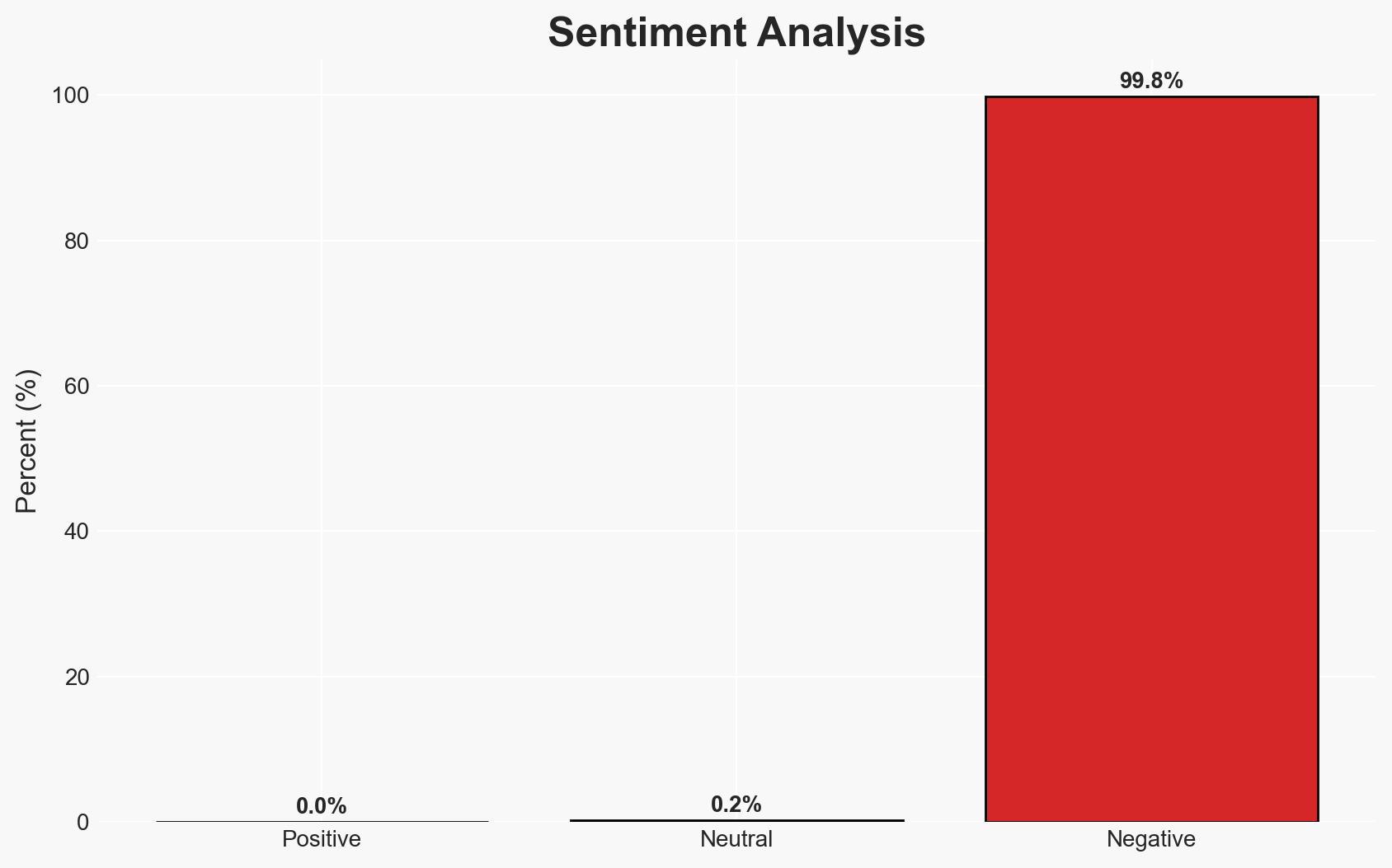
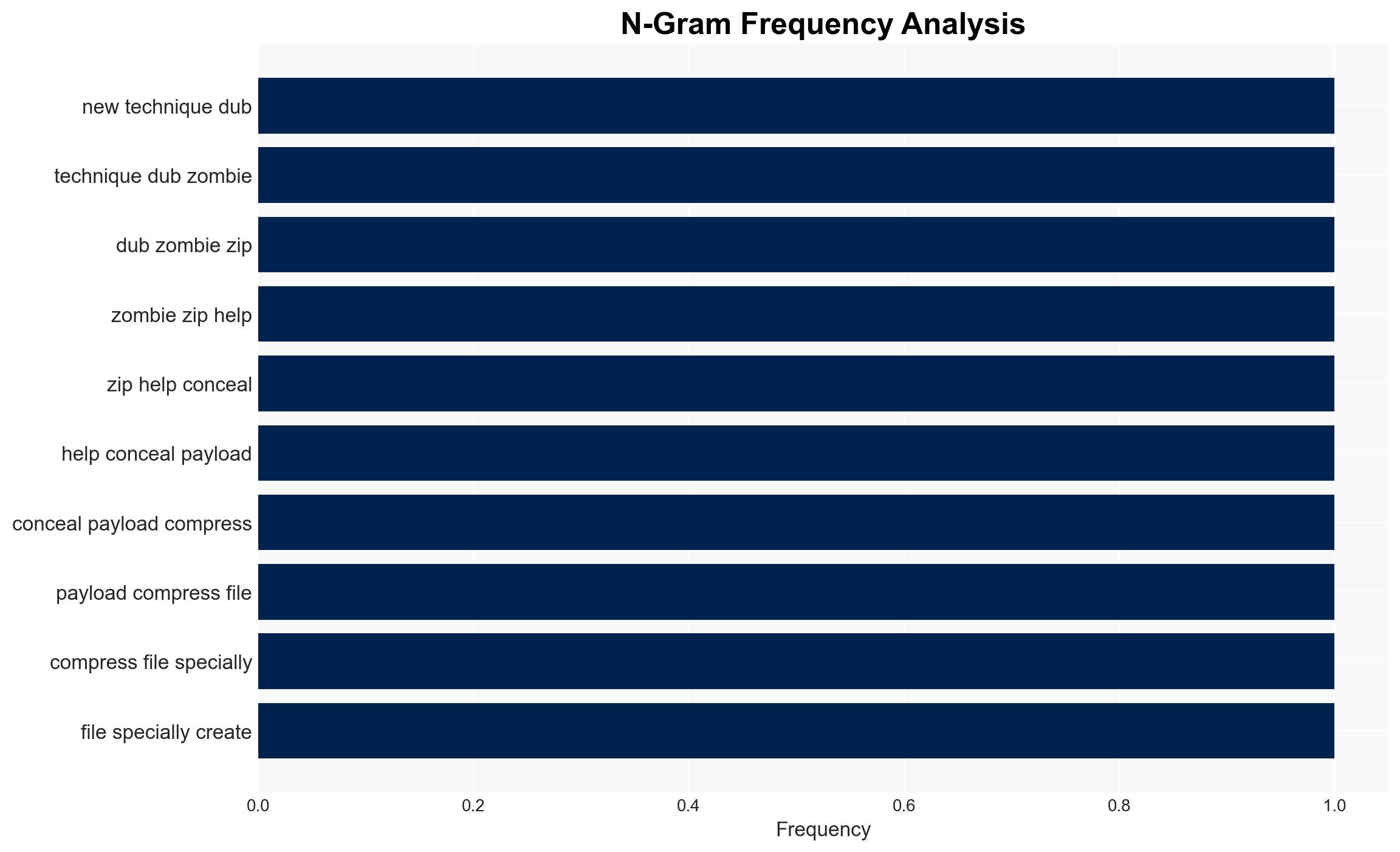
The “Zombie ZIP” technique represents a significant vulnerability in current antivirus and endpoint detection systems, allowing malicious payloads to evade detection. This vulnerability primarily affects cybersecurity defenses across various sectors. Given the technique’s effectiveness against most AV engines, there is a moderate confidence level that it could be exploited by threat actors to bypass security measures.
2. Competing Hypotheses
- Hypothesis A: The “Zombie ZIP” technique will be rapidly adopted by cybercriminals to evade detection, leading to an increase in successful malware attacks. This is supported by the technique’s demonstrated effectiveness against 50 of 51 AV engines. However, uncertainties include the speed of countermeasures by security vendors.
- Hypothesis B: Security vendors will quickly adapt and update their systems to detect and mitigate the “Zombie ZIP” technique, minimizing its impact. This is contradicted by the historical lag in response to similar vulnerabilities, such as CVE-2004-0935.
- Assessment: Hypothesis A is currently better supported due to the widespread vulnerability across AV engines and the time required for vendors to develop and deploy effective countermeasures. Key indicators that could shift this judgment include rapid vendor response and patch deployment.
3. Key Assumptions and Red Flags
- Assumptions: AV vendors are unaware of the vulnerability; threat actors have the capability to exploit the technique; security updates will not be immediate; the technique will be shared among cybercriminals.
- Information Gaps: The exact timeline for AV vendors to implement fixes; the extent of current exploitation by threat actors; potential undisclosed mitigations by some vendors.
- Bias & Deception Risks: Potential overreliance on the researcher’s findings without independent verification; bias towards assuming widespread exploitation without concrete evidence.
4. Implications and Strategic Risks
The “Zombie ZIP” technique could lead to a significant increase in undetected malware infections, affecting various sectors reliant on AV protection. This development could exacerbate existing cybersecurity challenges and strain resources.
- Political / Geopolitical: Increased cyber threats could escalate tensions between nation-states, particularly if state-sponsored actors exploit the vulnerability.
- Security / Counter-Terrorism: Enhanced risk of cyber-attacks on critical infrastructure and potential use by terrorist groups to disrupt operations.
- Cyber / Information Space: Potential for widespread misinformation campaigns if malicious actors leverage the technique to deploy information-stealing malware.
- Economic / Social: Potential economic impact due to increased cybersecurity incidents and associated costs; public trust in digital security could be undermined.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Encourage AV vendors to prioritize patch development; increase monitoring of suspicious ZIP file activity; educate users on the risks of unknown archive files.
- Medium-Term Posture (1–12 months): Develop partnerships between government and private sector for rapid threat intelligence sharing; invest in advanced detection technologies.
- Scenario Outlook:
- Best: Rapid vendor response mitigates the threat, with minimal exploitation.
- Worst: Widespread adoption by threat actors leads to significant cyber incidents.
- Most-Likely: Gradual increase in exploitation with eventual vendor response reducing impact.
6. Key Individuals and Entities
- Chris Aziz, Bombadil Systems security researcher
- CERT Coordination Center (CERT/CC)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, malware, antivirus, vulnerability, threat detection, cyber defense, information security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us