US contractor L3Harris suspected of developing iPhone hacking tools exploited by Russian and Chinese operativ…
Published on: 2026-03-10
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: US military contractor likely built iPhone hacking tools used by Russian spies in Ukraine
1. BLUF (Bottom Line Up Front)
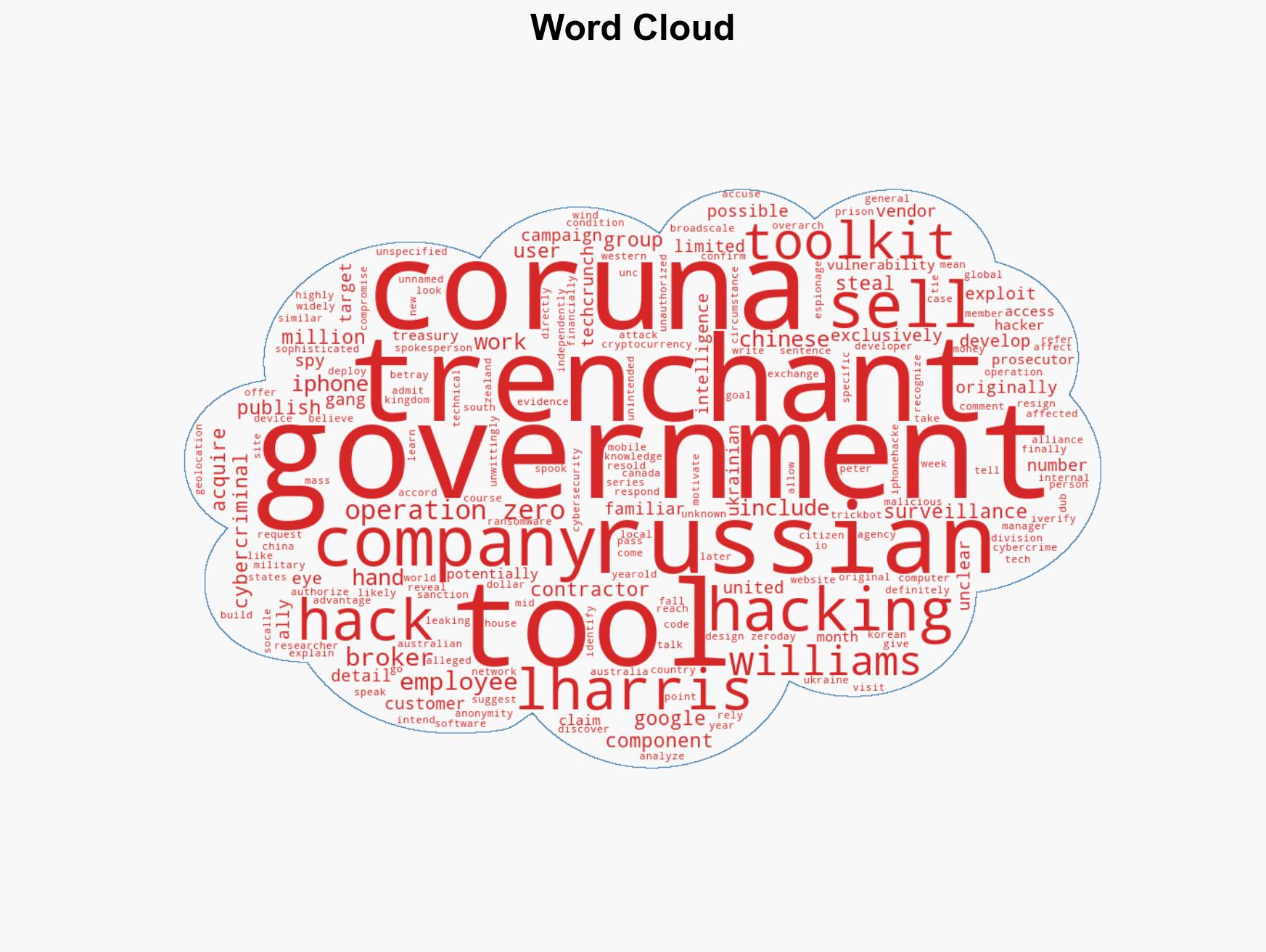
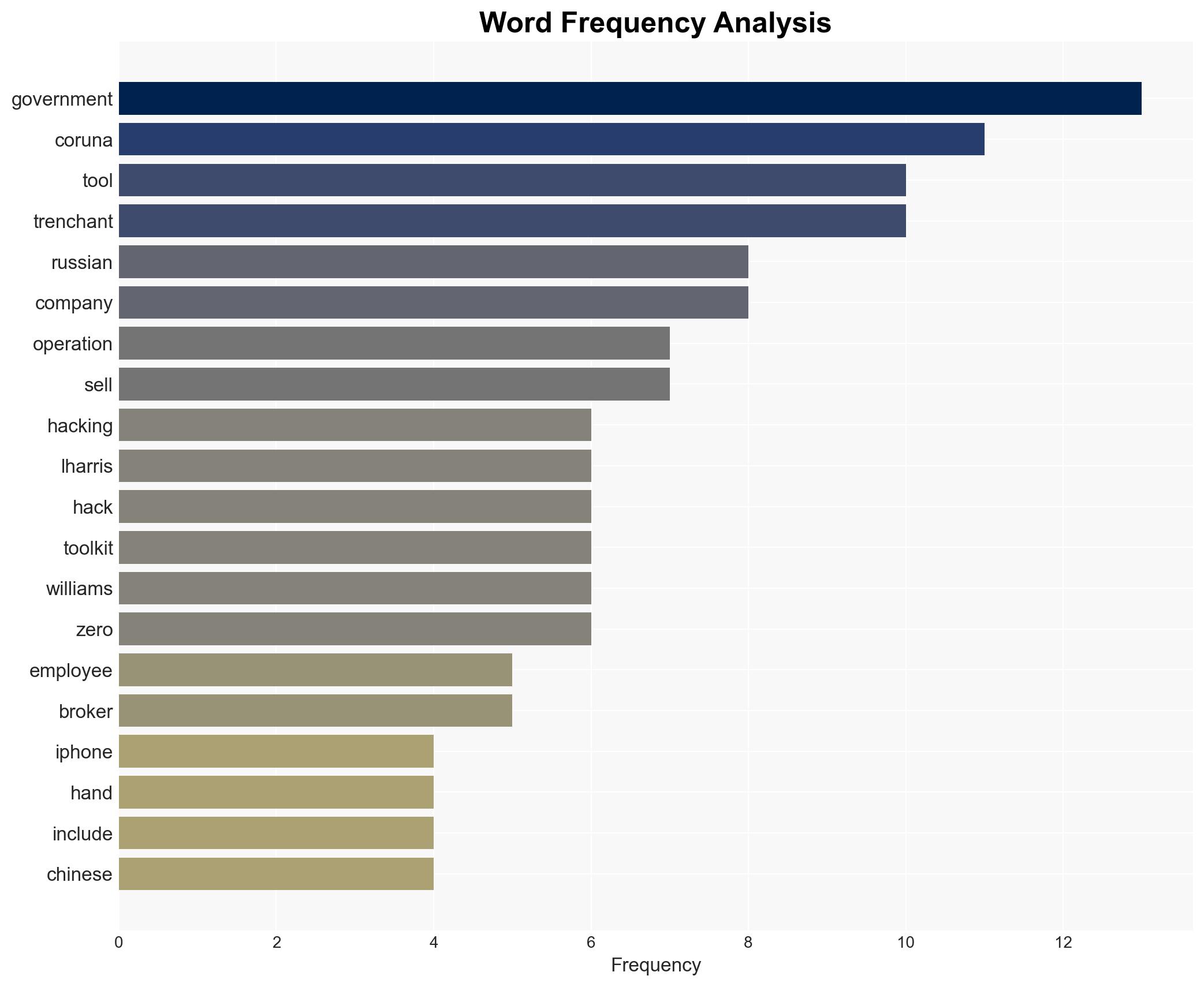
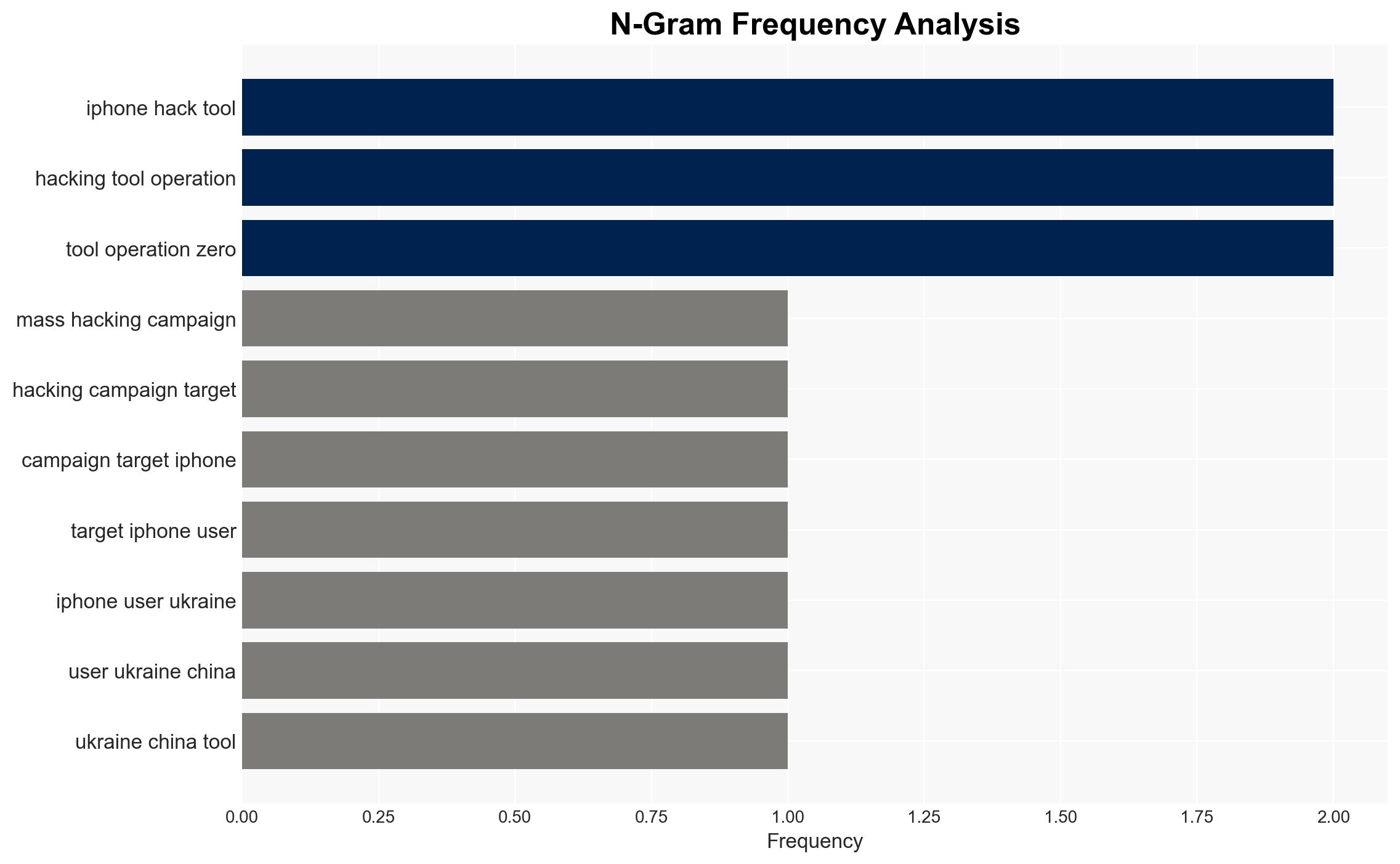
The iPhone hacking toolkit “Coruna,” likely developed by L3Harris, has been used by Russian and Chinese actors, posing significant cybersecurity threats. This incident highlights vulnerabilities in the control of cyber tools initially intended for Western intelligence. Moderate confidence is placed in the assessment due to the lack of direct evidence linking L3Harris to the toolkit’s proliferation.
2. Competing Hypotheses
- Hypothesis A: Coruna was developed by L3Harris and leaked to foreign actors due to inadequate security protocols. Supporting evidence includes former employees’ testimonies and technical similarities. However, uncertainties remain about the exact pathway of the leak.
- Hypothesis B: Coruna was independently developed or acquired by Russian or Chinese actors through espionage or cyber infiltration. This is less supported due to the specific technical details linking it to L3Harris, but cannot be entirely ruled out.
- Assessment: Hypothesis A is currently better supported due to corroborative testimonies and technical evidence. Indicators such as new disclosures from L3Harris or further technical analysis could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: L3Harris developed Coruna; the toolkit was intended for use by Five Eyes members; security protocols were insufficient to prevent unauthorized access.
- Information Gaps: Precise details on how Coruna was transferred to Russian and Chinese actors; confirmation of L3Harris’s role in the toolkit’s development.
- Bias & Deception Risks: Potential bias from former employees with grievances; risk of misinformation from involved parties to obscure true origins.
4. Implications and Strategic Risks
This development could exacerbate tensions between Western and Eastern cyber actors, leading to increased cyber espionage and retaliatory measures. It may also prompt a reevaluation of cybersecurity protocols among Western contractors.
- Political / Geopolitical: Potential diplomatic strains between the U.S. and its allies with Russia and China.
- Security / Counter-Terrorism: Heightened threat environment for Western entities, particularly in cyber defense.
- Cyber / Information Space: Increased cyber operations targeting Western infrastructure; potential for further leaks.
- Economic / Social: Potential economic impacts from cyber theft and espionage; erosion of trust in tech contractors.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a thorough audit of L3Harris’s security protocols; enhance monitoring of cyber tool dissemination.
- Medium-Term Posture (1–12 months): Strengthen partnerships with Five Eyes for joint cybersecurity initiatives; develop resilience measures against similar threats.
- Scenario Outlook: Best: Improved security measures prevent further leaks. Worst: Continued proliferation of hacking tools leads to major cyber incidents. Most-Likely: Incremental improvements in security with occasional breaches.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, espionage, hacking tools, L3Harris, Five Eyes, cyber-espionage, geopolitical tensions
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us