Oyo Residents Block Highway in Protest Against Rising Kidnapping and Banditry Threats
Published on: 2026-03-11
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Commuters stranded as Oyo community protests kidnapping banditry
1. BLUF (Bottom Line Up Front)
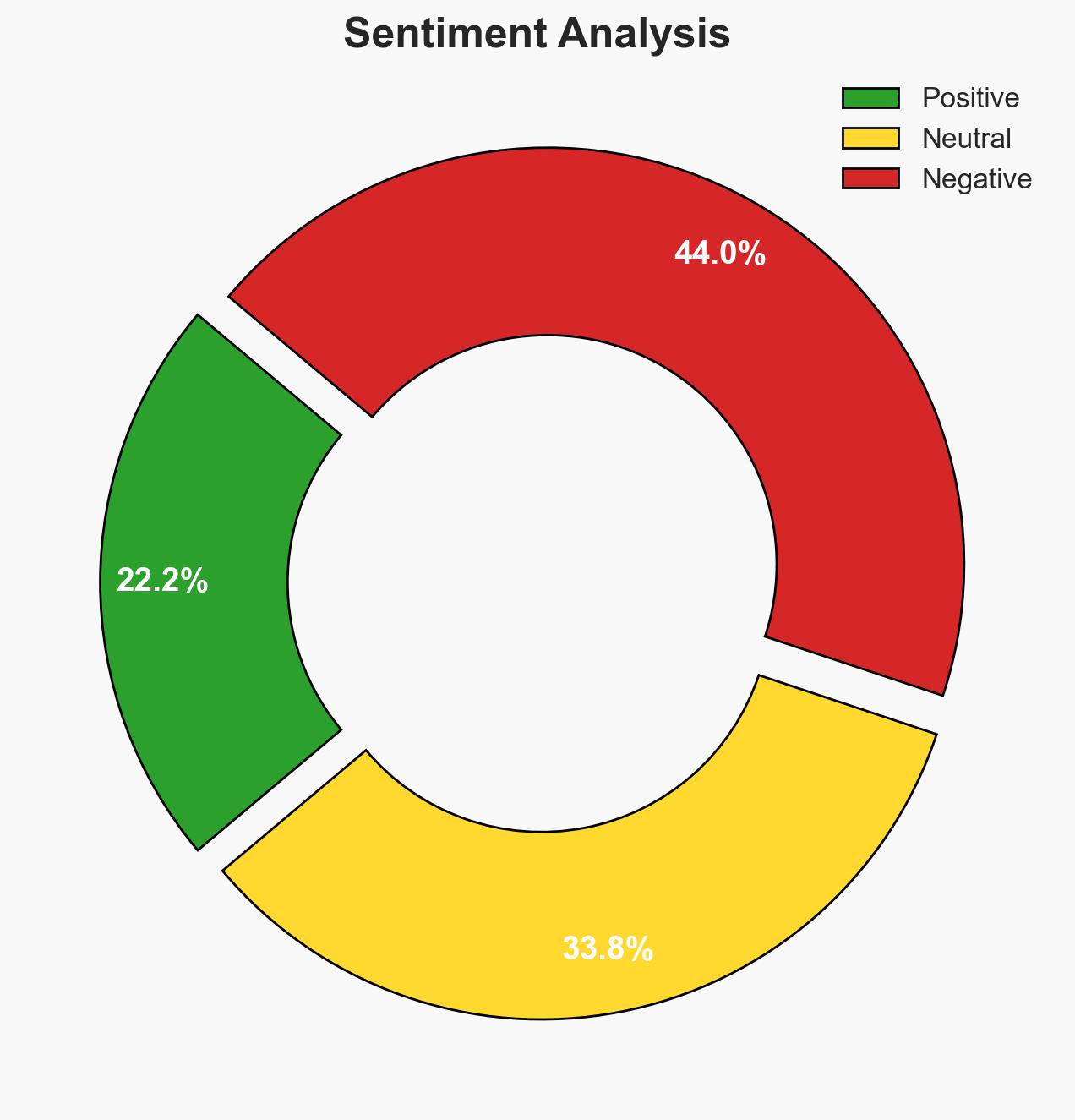
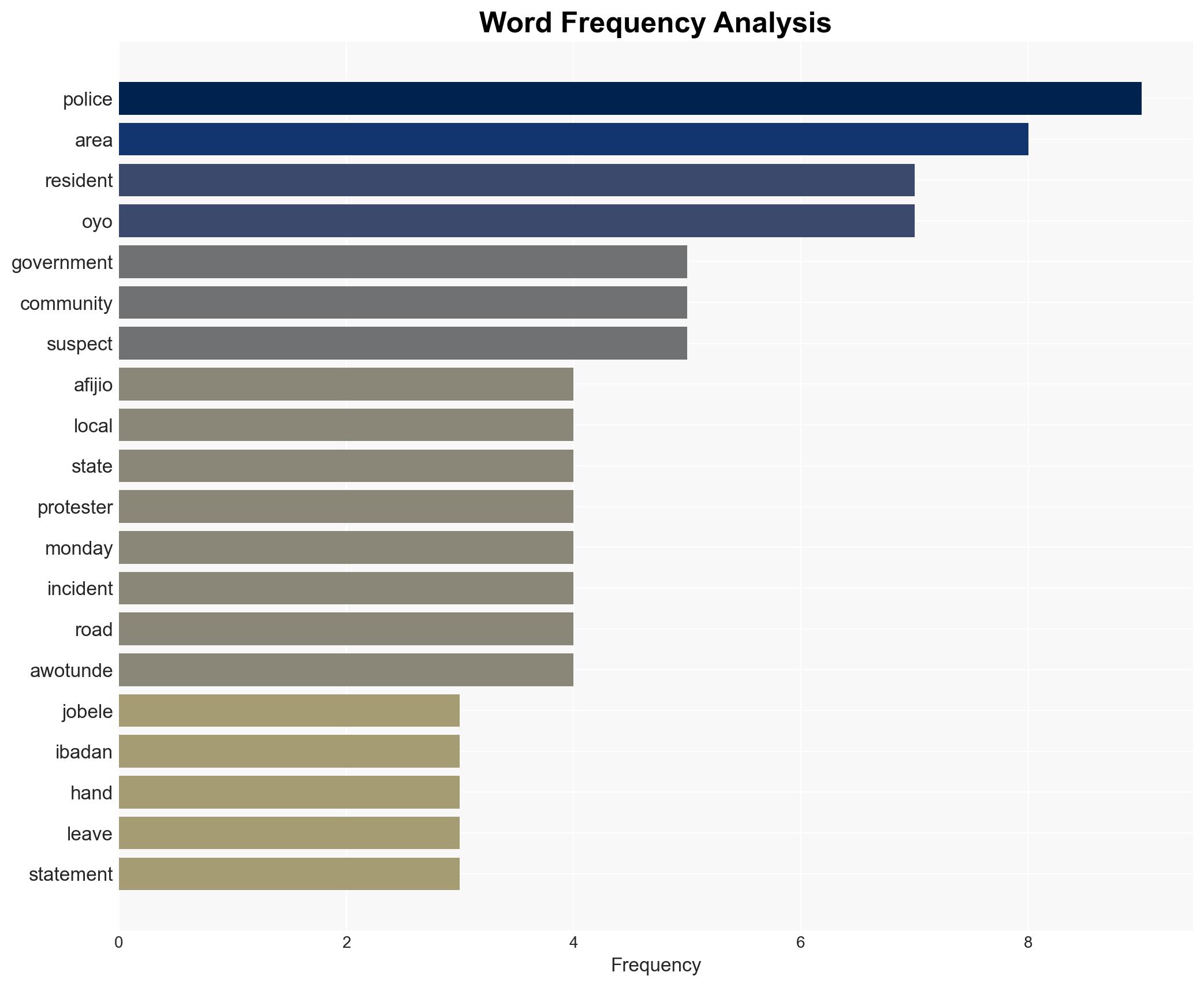
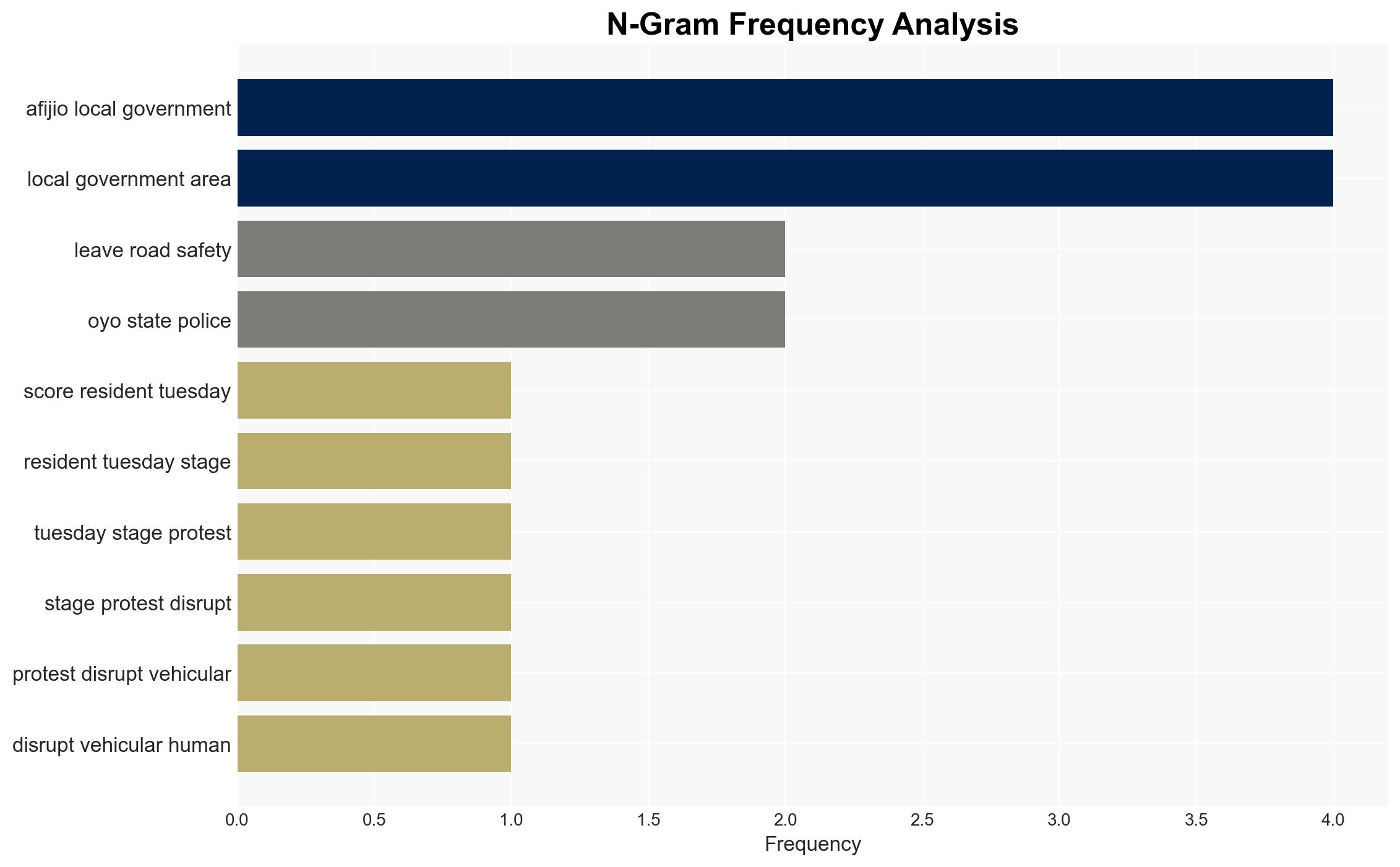
The protest in Oyo State highlights escalating insecurity due to frequent kidnappings and banditry, with community trust in law enforcement severely eroded. The most likely hypothesis is that local criminal groups are exploiting weak security measures, leading to public unrest. This situation affects local residents, commuters, and law enforcement agencies. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: The rise in kidnappings and banditry is primarily due to local criminal groups exploiting inadequate security infrastructure. Supporting evidence includes the frequency of incidents and the community’s proactive measures such as organizing vigilante watches. Contradicting evidence is the lack of detailed information on the criminal groups involved.
- Hypothesis B: The incidents are isolated and exaggerated by community perceptions and media reports, possibly due to isolated failures in law enforcement response. Supporting evidence includes the release of a suspect without explanation, which could indicate procedural issues rather than systemic criminal activity.
- Assessment: Hypothesis A is currently better supported due to the consistent pattern of incidents and community actions. Key indicators that could shift this judgment include verified intelligence on organized criminal networks or improved law enforcement responses reducing incident frequency.
3. Key Assumptions and Red Flags
- Assumptions: The community’s reports are accurate; law enforcement is currently ineffective; criminal groups are local and not transnational; community actions are spontaneous and not externally influenced.
- Information Gaps: Detailed profiles of the criminal groups; law enforcement internal reports; broader regional security assessments.
- Bias & Deception Risks: Potential bias in community reports due to fear and frustration; media sensationalism; possible misinformation from released suspect.
4. Implications and Strategic Risks
This development could lead to increased community unrest and potential escalation if security measures are not improved. The erosion of trust in law enforcement may lead to further civil disobedience or vigilante justice.
- Political / Geopolitical: Potential for political pressure on local government to enhance security measures.
- Security / Counter-Terrorism: Increased risk of vigilantism and potential for criminal groups to exploit unrest.
- Cyber / Information Space: Potential for misinformation campaigns to exacerbate tensions.
- Economic / Social: Disruption of local economy and social cohesion due to ongoing insecurity and protests.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Increase law enforcement presence; engage community leaders to restore trust; monitor for misinformation.
- Medium-Term Posture (1–12 months): Develop community-police partnerships; enhance intelligence capabilities; implement community awareness programs.
- Scenario Outlook: Best: Improved security and restored trust; Worst: Escalation to widespread unrest; Most-Likely: Continued low-level incidents with sporadic protests.
6. Key Individuals and Entities
- Dolapo Awotunde, Ward 8 representative
- Local law enforcement agencies
- Community vigilante groups
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
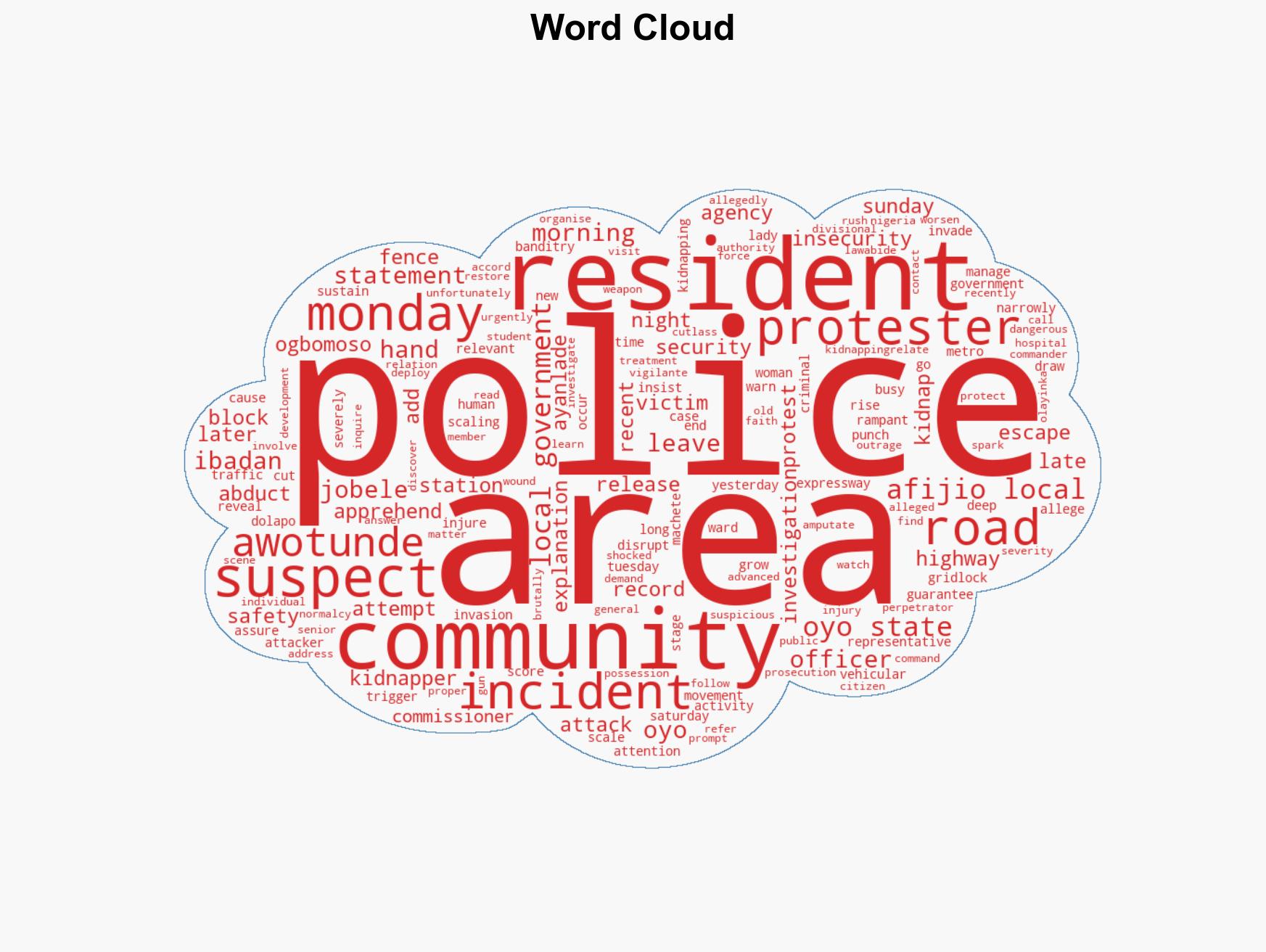
national security threats, kidnapping, banditry, community unrest, law enforcement, vigilante justice, public safety, Nigeria
Structured Analytic Techniques Applied
- Cognitive Bias Stress Test: Expose and correct potential biases in assessments through red-teaming and structured challenge.
- Bayesian Scenario Modeling: Use probabilistic forecasting for conflict trajectories or escalation likelihood.
- Network Influence Mapping: Map relationships between state and non-state actors for impact estimation.
Explore more:
National Security Threats Briefs ·
Daily Summary ·
Support us