Coruna Exploits Highlight Advanced Cyber Threats Amid Global Tensions
Published on: 2026-03-11
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Risky Business 828 — The Coruna exploits are truly exquisite
1. BLUF (Bottom Line Up Front)
The Coruna exploits, linked to L3 Harris, suggest sophisticated cyber capabilities potentially used by Russian actors in Ukraine, posing significant security challenges. The Israeli kinetic strike on Iran’s cyber HQ indicates escalating cyber-kinetic conflict dynamics. Moderate confidence in these assessments due to limited corroborative details and potential biases in source reporting.
2. Competing Hypotheses
- Hypothesis A: The Coruna exploits were developed by L3 Harris and used by Russian state actors in Ukraine. This is supported by the association with a known military contractor and the context of ongoing cyber operations in Ukraine. However, the exact deployment and attribution remain uncertain.
- Hypothesis B: The Coruna exploits are a false flag operation intended to mislead attribution efforts. This hypothesis considers the complexity of the exploits and the potential for deception in cyber operations, though lacks direct evidence.
- Assessment: Hypothesis A is currently better supported due to the involvement of L3 Harris, a credible military contractor, and the context of Russian cyber activities in Ukraine. Key indicators that could shift this judgment include new evidence of attribution or technical analysis contradicting current assessments.
3. Key Assumptions and Red Flags
- Assumptions: L3 Harris has the capability to develop such exploits; Russian actors are actively targeting Ukraine; Israeli strikes are directly linked to cyber operations.
- Information Gaps: Detailed technical analysis of the Coruna exploits; clear attribution of the actors using these exploits; comprehensive impact assessment of the Israeli strike on Iran’s cyber capabilities.
- Bias & Deception Risks: Potential bias in attributing cyber capabilities to state actors without conclusive evidence; risk of deception in cyber operations to mislead attribution efforts.
4. Implications and Strategic Risks
The developments could lead to increased cyber-kinetic conflict, complicating international relations and security postures. The sophistication of the Coruna exploits may prompt other state and non-state actors to enhance their cyber capabilities, potentially escalating cyber conflicts.
- Political / Geopolitical: Potential escalation in cyber warfare between state actors, affecting diplomatic relations and regional stability.
- Security / Counter-Terrorism: Increased threat of sophisticated cyber attacks on critical infrastructure, necessitating enhanced defensive measures.
- Cyber / Information Space: Potential proliferation of advanced cyber tools among state and non-state actors, increasing the complexity of the cyber threat landscape.
- Economic / Social: Economic impacts from cyber disruptions on critical sectors; potential social unrest from perceived vulnerabilities.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of cyber activities linked to state actors; conduct technical analysis of the Coruna exploits; engage in diplomatic efforts to de-escalate tensions.
- Medium-Term Posture (1–12 months): Strengthen cyber defenses and resilience measures; develop partnerships for intelligence sharing; invest in capability development to counter advanced cyber threats.
- Scenario Outlook:
- Best: De-escalation of cyber-kinetic conflicts through diplomatic engagement.
- Worst: Escalation leading to significant cyber and kinetic confrontations.
- Most-Likely: Continued low-level cyber operations with periodic escalations.
6. Key Individuals and Entities
- L3 Harris (US military contractor)
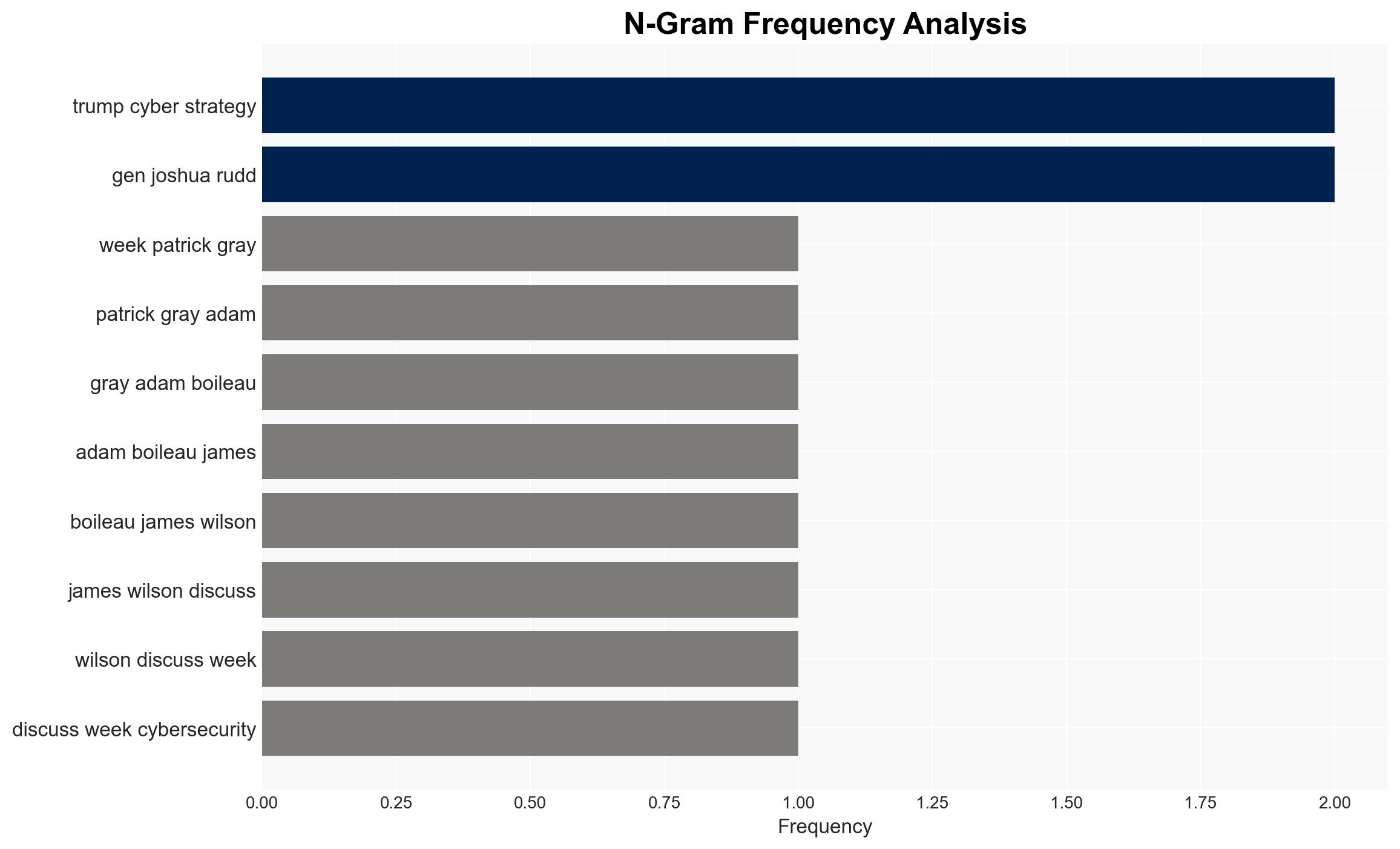
- Lt Gen Joshua Rudd (NSA and Cyber Command head)
- Iranian Cyber HQ
- Israeli Defense Forces
- Russian State Actors
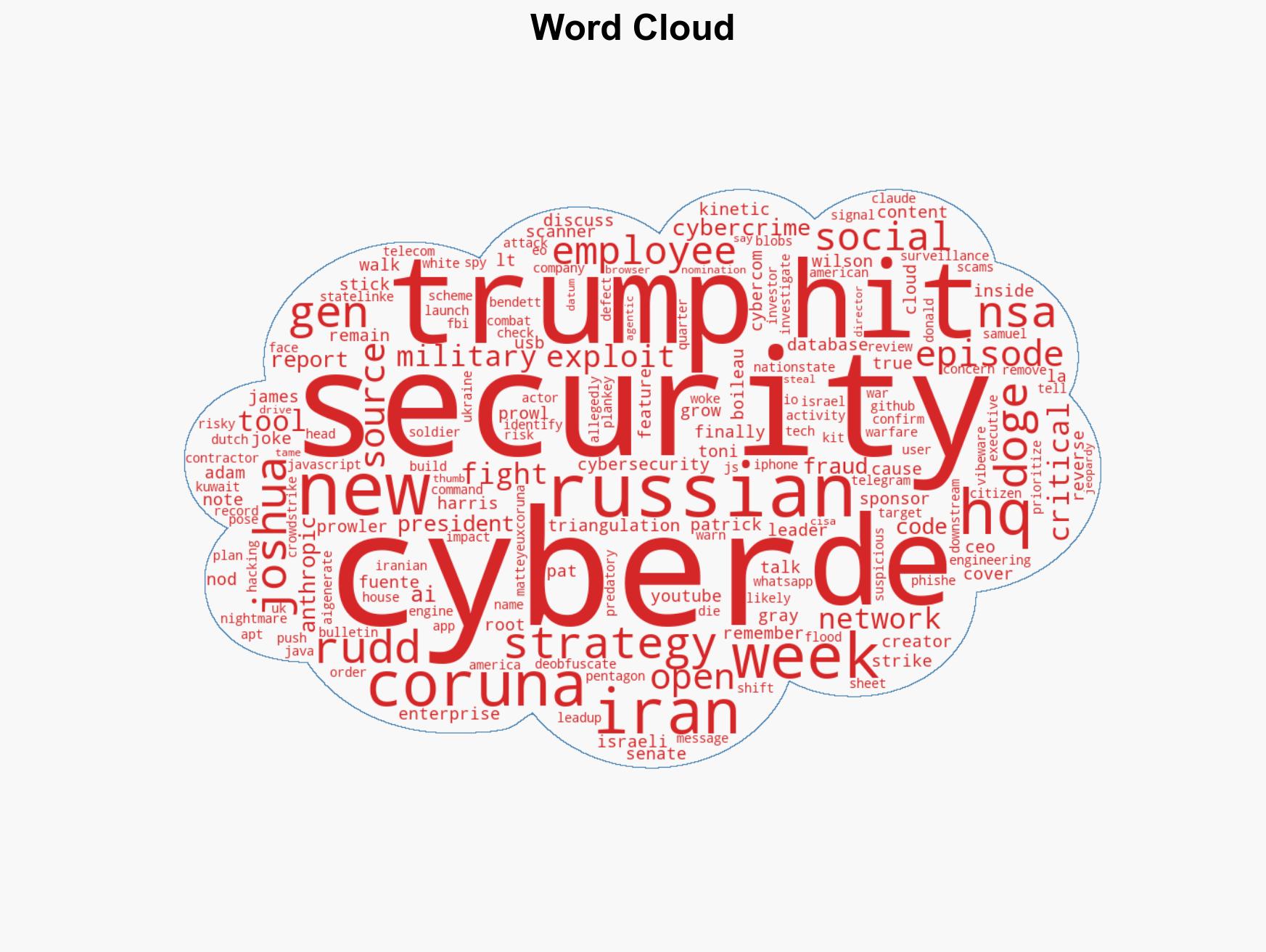
7. Thematic Tags
cybersecurity, cyber-espionage, cyber warfare, state-sponsored hacking, cyber-kinetic conflict, national security, military contractors, geopolitical tensions
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us