Software flaws now dominate cloud breaches, surpassing credential theft as primary attack vector
Published on: 2026-03-11
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Software vulnerabilities push credential abuse aside in cloud intrusions
1. BLUF (Bottom Line Up Front)
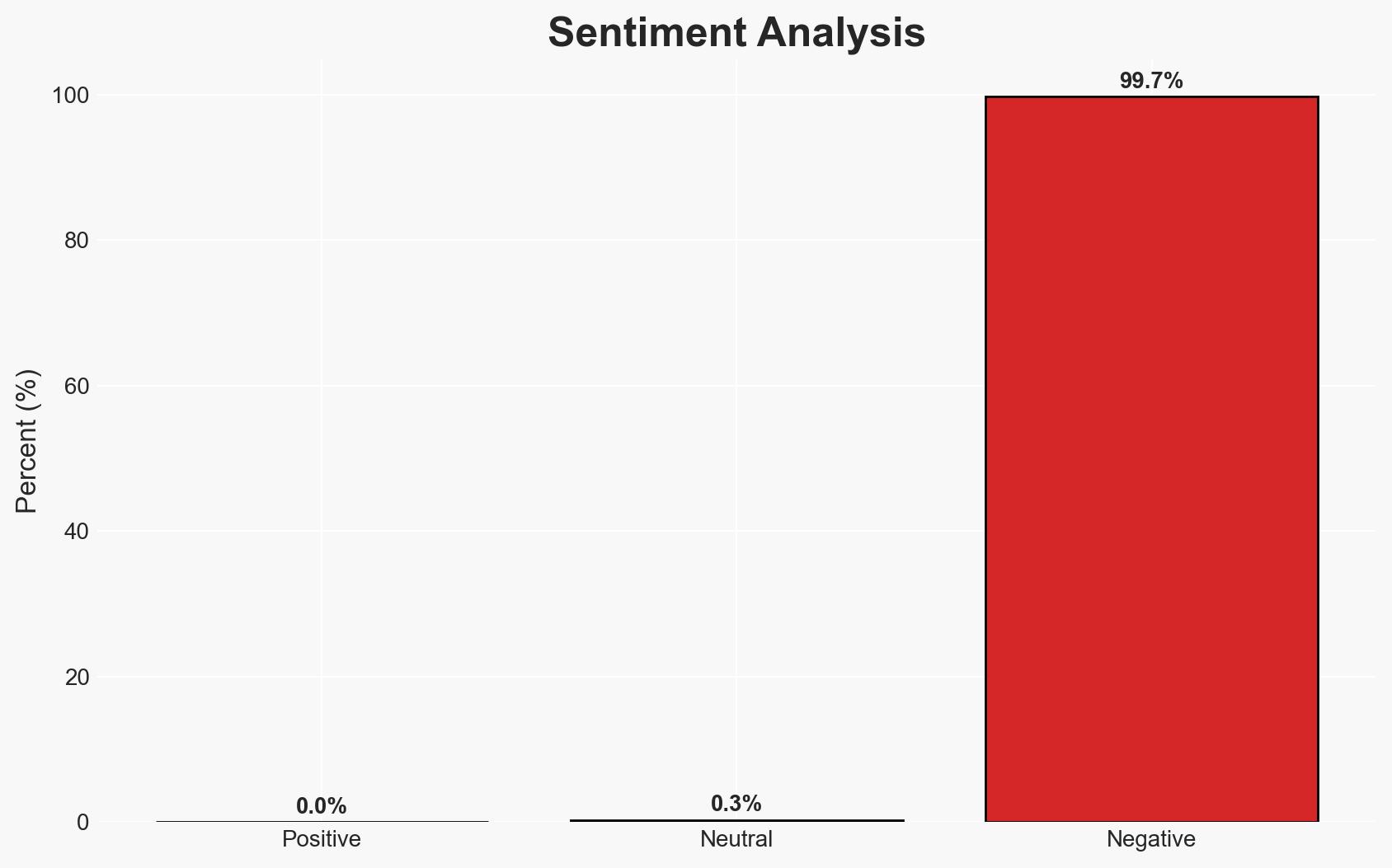
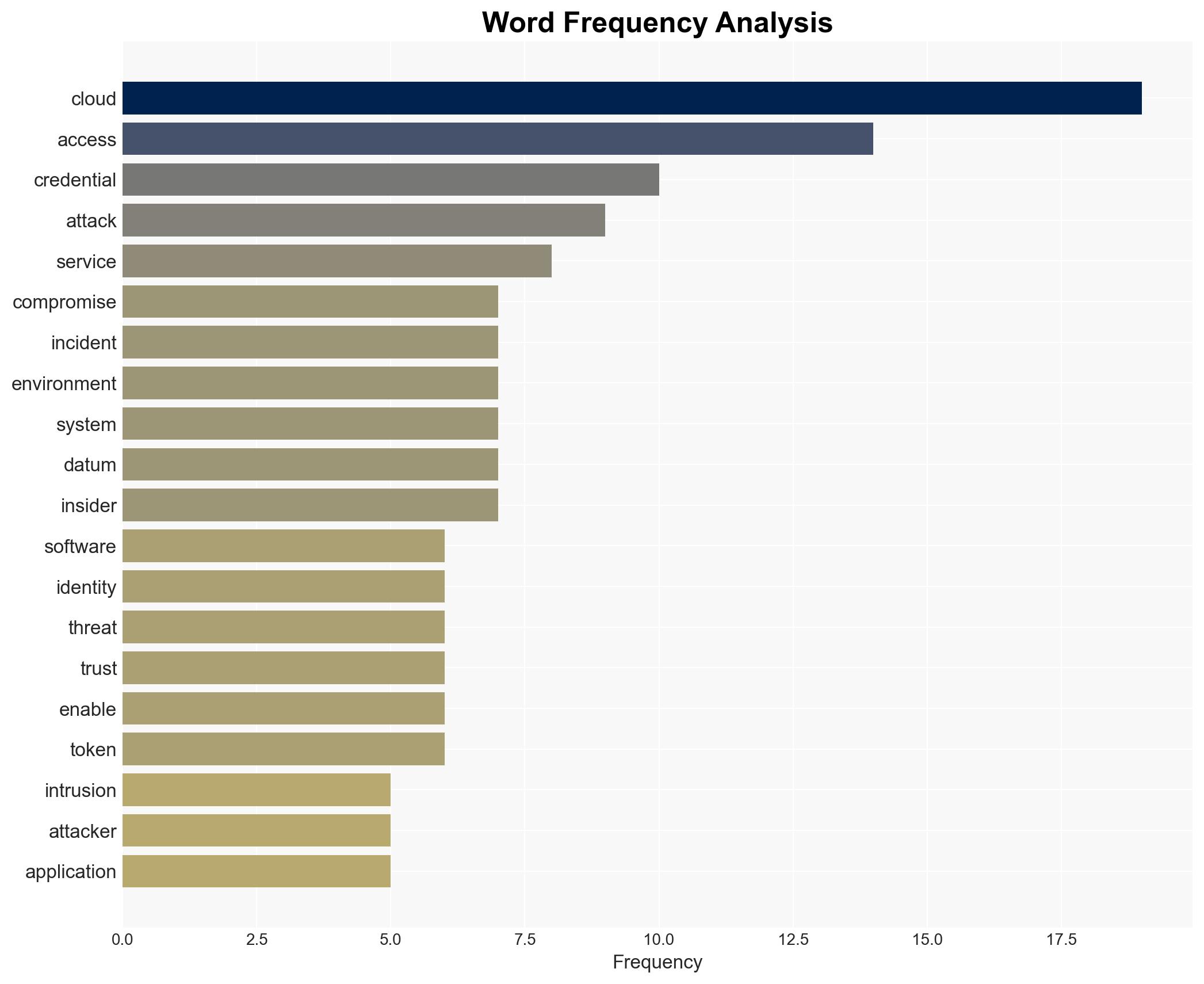
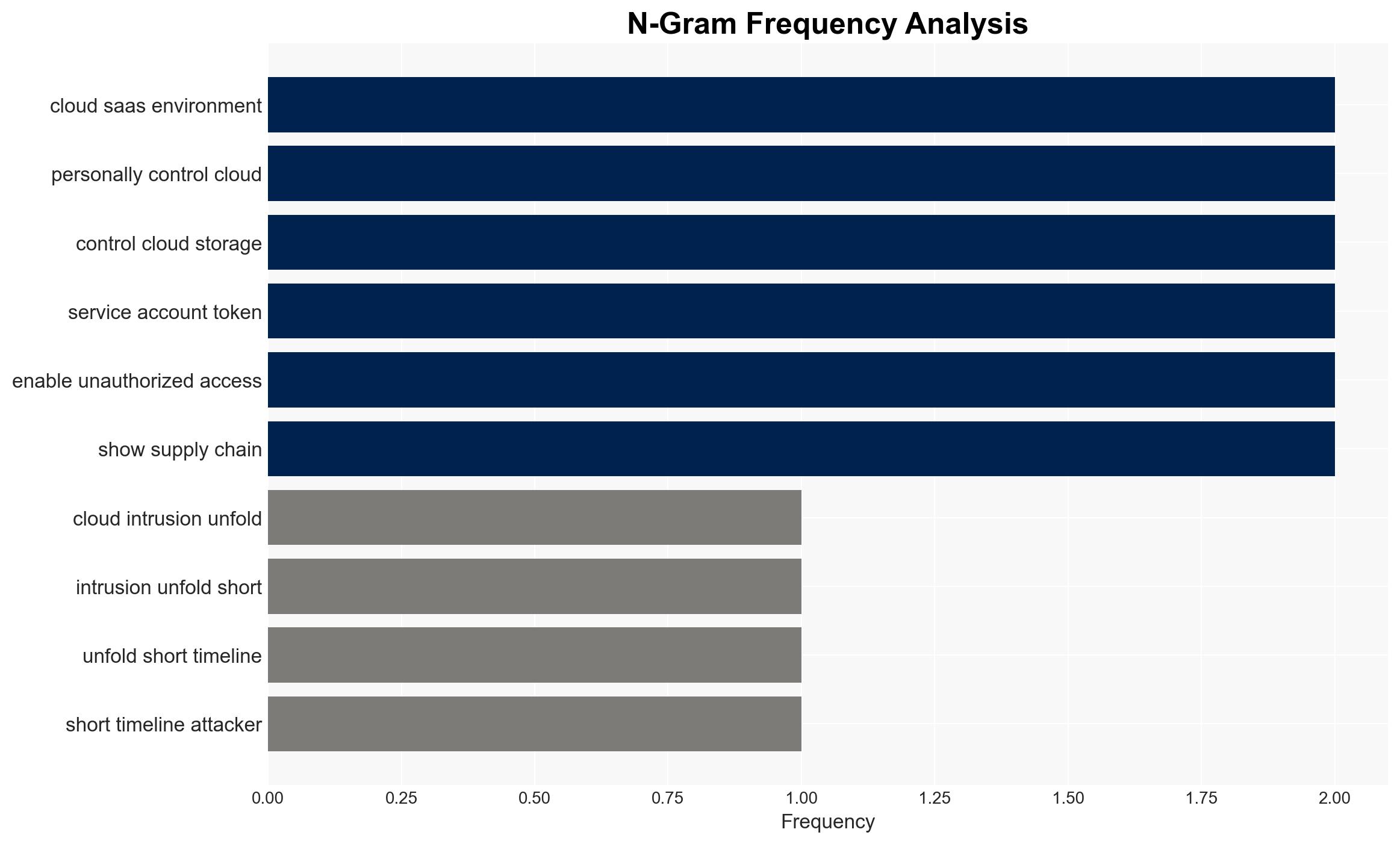
Recent trends indicate a shift in cloud intrusion tactics, with a growing reliance on exploiting software vulnerabilities over credential abuse. This development affects cloud service providers and organizations relying on SaaS platforms, necessitating enhanced application security measures. The overall confidence level in this assessment is moderate, given the evolving nature of cyber threats and the potential for rapid changes in tactics.
2. Competing Hypotheses
- Hypothesis A: Attackers are increasingly exploiting software vulnerabilities due to the faster timeline between vulnerability disclosure and exploitation. This is supported by the observed shift in initial access methods and the prevalence of remote code execution attacks. However, uncertainties remain regarding the full extent of AI’s role in these exploits.
- Hypothesis B: Credential abuse remains the primary method of cloud intrusion, with software vulnerabilities being a secondary factor. This hypothesis is contradicted by the reported decrease in credential-based attacks and the increased focus on software vulnerabilities.
- Assessment: Hypothesis A is currently better supported due to the documented increase in software-driven access methods and the rapid exploitation of disclosed vulnerabilities. Indicators such as a resurgence in credential-based attacks or new defensive measures could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Organizations will continue to improve credential hygiene; AI will increasingly be used in vulnerability exploitation; cloud service providers will prioritize patching known vulnerabilities.
- Information Gaps: Specific data on the role of AI in recent exploits and the effectiveness of current defensive measures against these tactics.
- Bias & Deception Risks: Potential over-reliance on reports from cloud service providers; risk of underestimating the adaptability of threat actors.
4. Implications and Strategic Risks
The shift towards software vulnerability exploitation in cloud intrusions could lead to increased pressure on software developers and cloud service providers to enhance security measures. This trend may also drive changes in regulatory environments and industry standards.
- Political / Geopolitical: Potential for increased international collaboration on cybersecurity standards and regulations.
- Security / Counter-Terrorism: Enhanced threat landscape requiring updated defensive strategies and threat intelligence sharing.
- Cyber / Information Space: Greater emphasis on application security and rapid patch deployment; potential rise in AI-driven cyber operations.
- Economic / Social: Increased costs for organizations to maintain security compliance; potential disruptions to cloud services affecting business operations.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor vulnerability disclosures closely; prioritize patching and hardening of exposed applications; enhance threat intelligence sharing.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms for AI-driven threat detection; invest in training for rapid incident response; review and update security policies regularly.
- Scenario Outlook:
- Best: Rapid adaptation to new threats leads to decreased successful intrusions.
- Worst: Failure to address vulnerabilities results in widespread data breaches and service disruptions.
- Most-Likely: Continued evolution of threat tactics with incremental improvements in defensive measures.
6. Key Individuals and Entities
- Google Cloud
- Adaptavist
- Matt Saunders, VP DevOps, Adaptavist
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
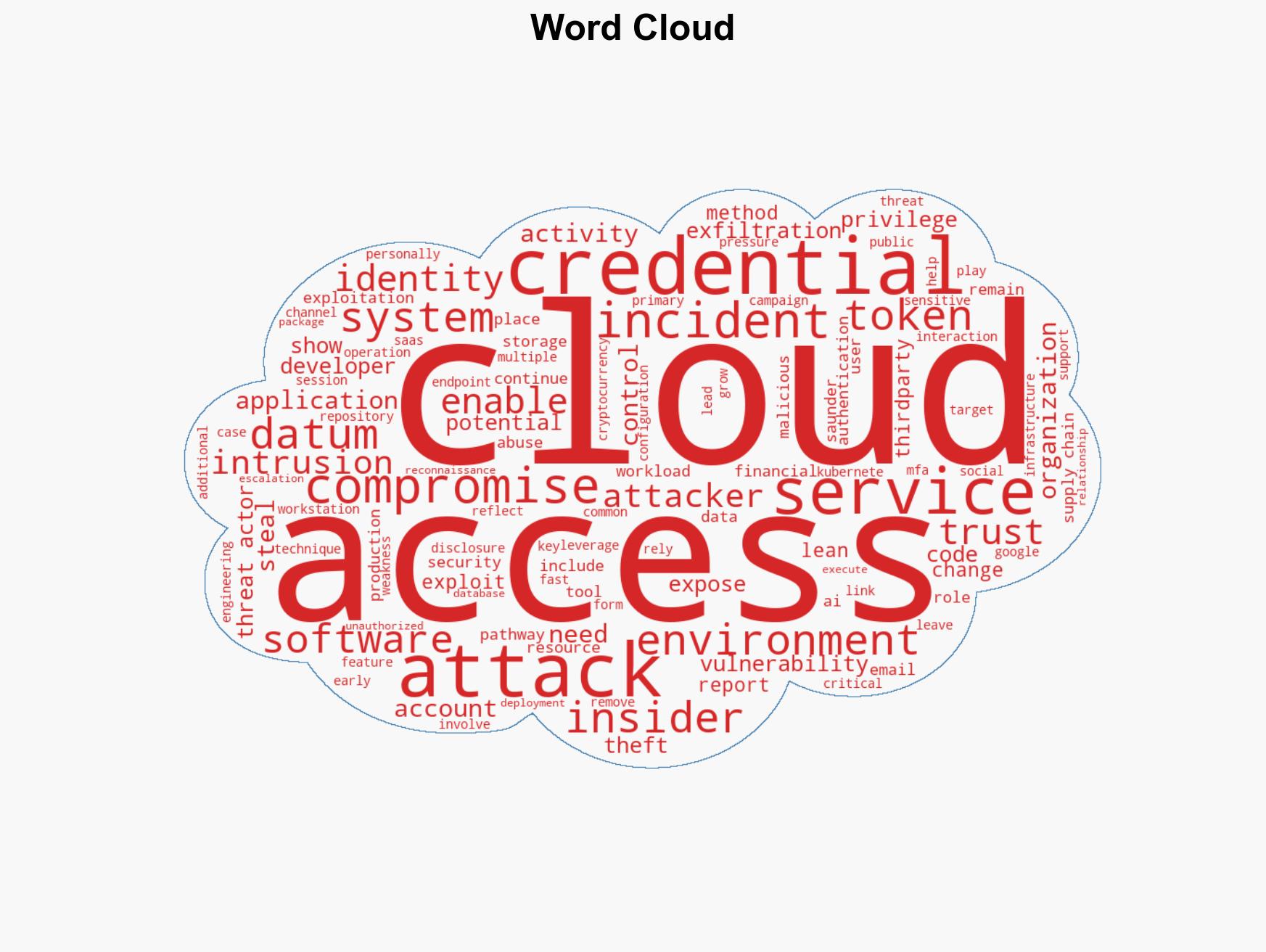
cybersecurity, cloud security, software vulnerabilities, cyber threats, AI exploitation, credential abuse, SaaS environments, threat intelligence
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us