Unauthorized drone incursion prompts shelter-in-place order at Barksdale Air Force Base amid heightened alert
Published on: 2026-03-11
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Mystery drone triggers terror alert shelter-in-place at nuclear-capable US Air Force base
1. BLUF (Bottom Line Up Front)
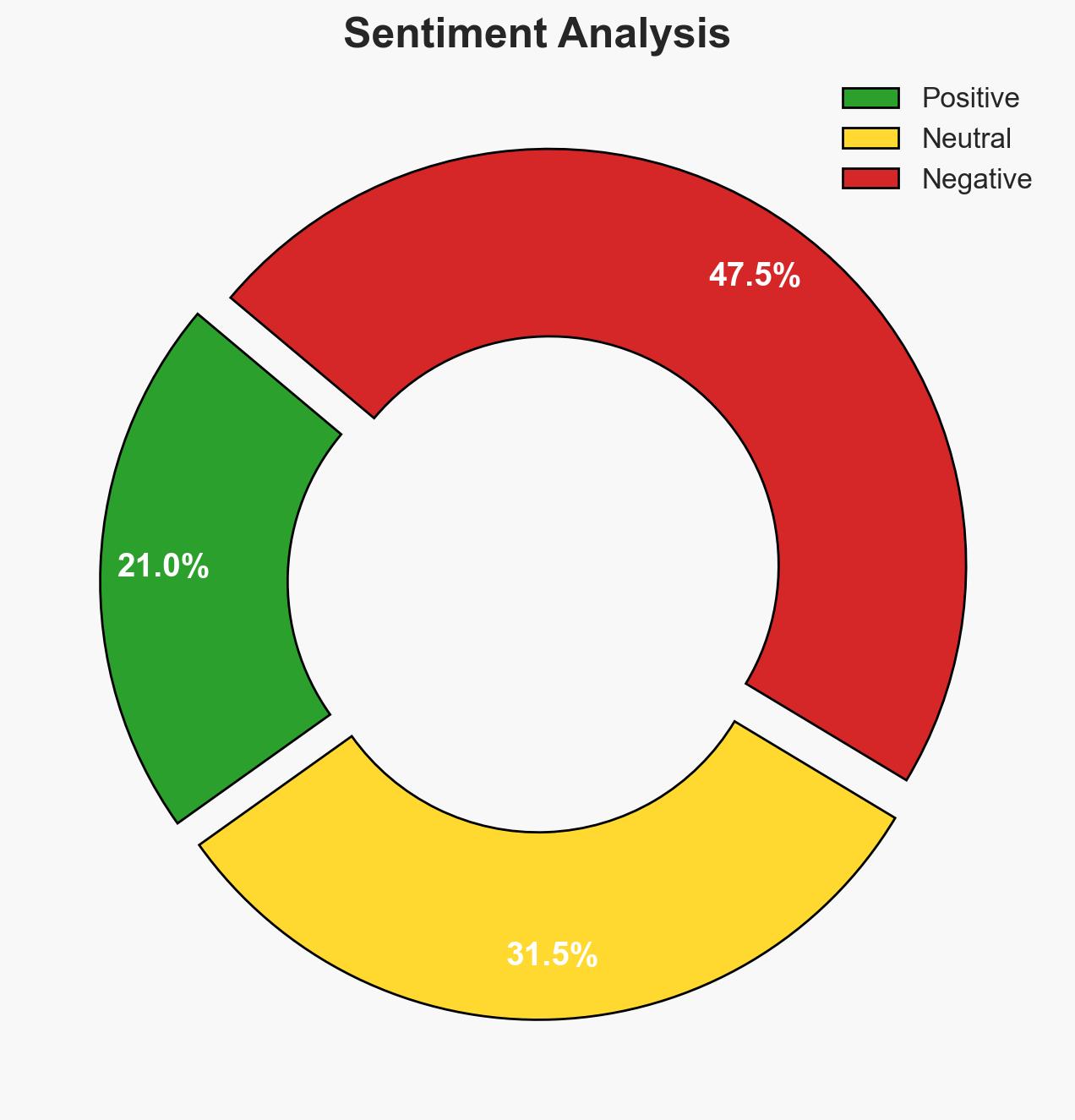
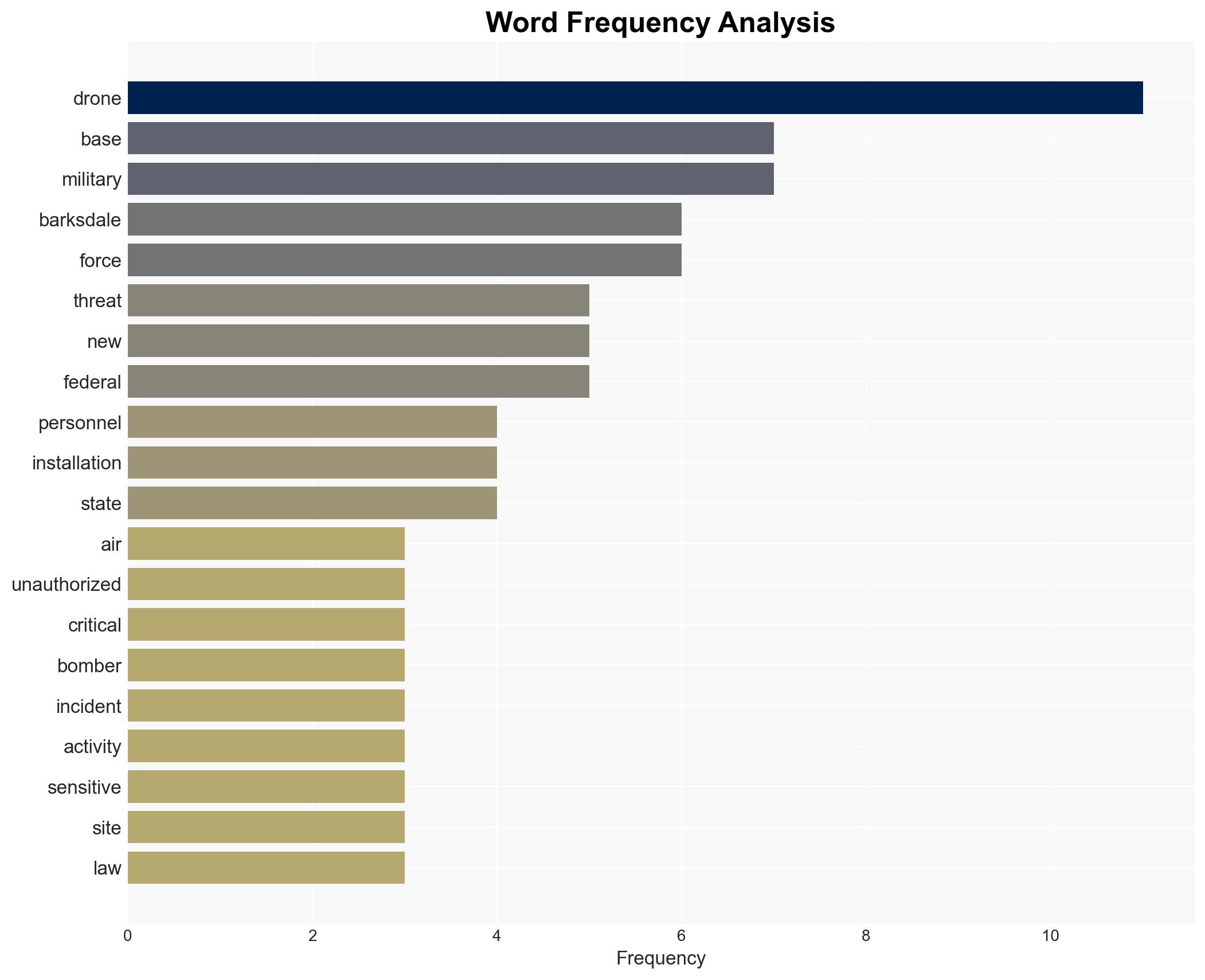
The unauthorized drone incident at Barksdale Air Force Base represents a significant security breach, highlighting vulnerabilities in the protection of critical military assets. The most likely hypothesis is that this was an intelligence-gathering operation by a non-state actor or foreign adversary. This incident affects U.S. national security and military readiness, with moderate confidence in this assessment.
2. Competing Hypotheses
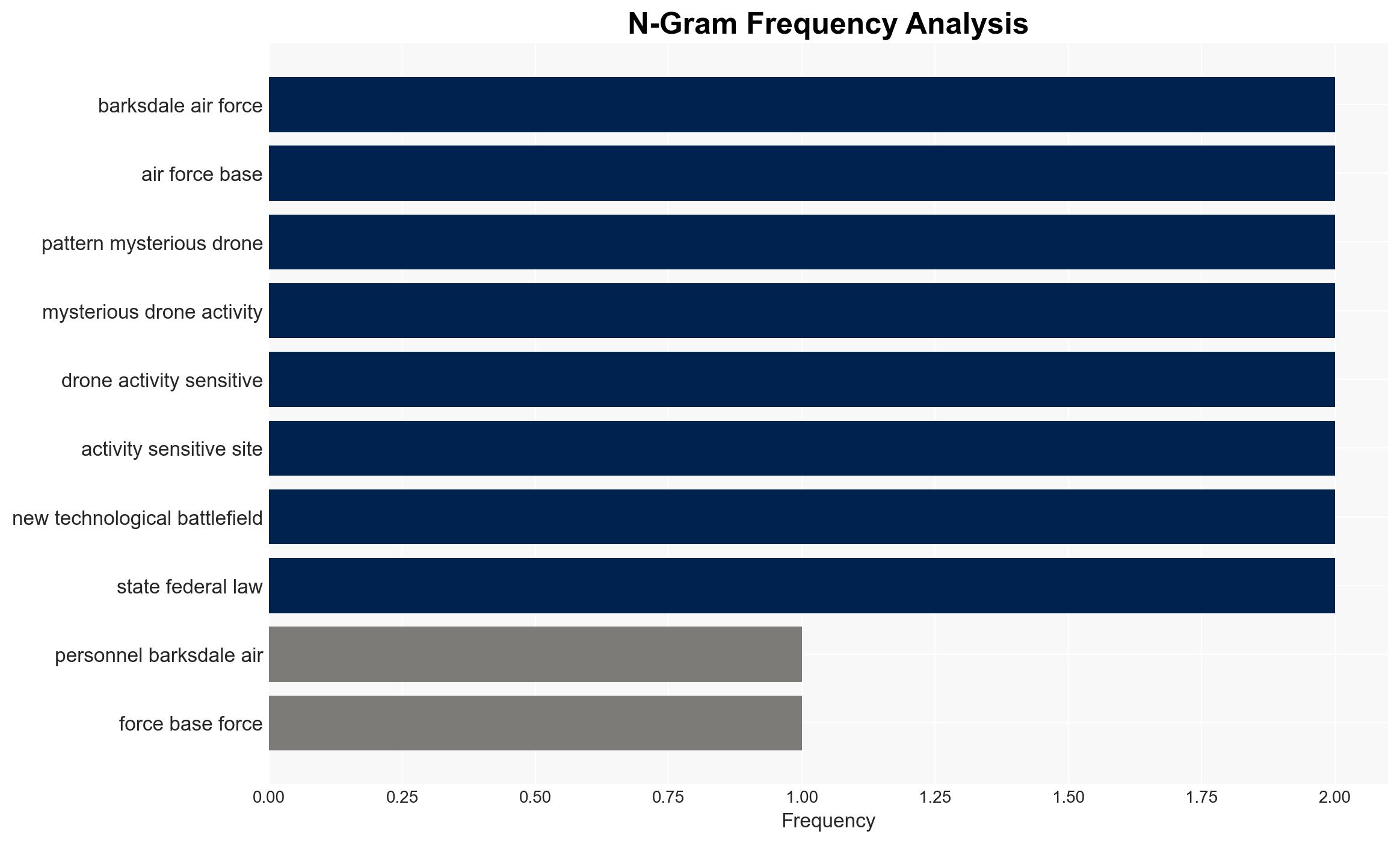
- Hypothesis A: The drone was operated by a foreign adversary or non-state actor conducting reconnaissance on U.S. military capabilities. This is supported by the strategic importance of Barksdale AFB and the pattern of similar incidents. However, the lack of direct attribution or recovered drone data creates uncertainty.
- Hypothesis B: The drone was operated by a civilian or hobbyist unaware of the legal restrictions. This is contradicted by the pattern of drone activity over sensitive sites and the elevated threat level response, suggesting a more deliberate action.
- Assessment: Hypothesis A is currently better supported due to the strategic nature of the target and the pattern of similar incidents. Key indicators that could shift this judgment include the recovery of the drone or credible intelligence linking the activity to a specific actor.
3. Key Assumptions and Red Flags
- Assumptions: The drone was intentionally targeting Barksdale AFB; the operator had knowledge of the base’s strategic value; the incident is part of a broader pattern of surveillance.
- Information Gaps: Identity of the drone operator; technical capabilities of the drone; any recovered data from the drone.
- Bias & Deception Risks: Confirmation bias towards foreign adversary involvement; potential misinformation from public or media sources; deception by the drone operator to obscure true intent.
4. Implications and Strategic Risks
This development underscores the evolving threat landscape involving unmanned aerial systems and their potential use in intelligence operations against critical U.S. military assets.
- Political / Geopolitical: Potential escalation in U.S. counter-drone measures and diplomatic tensions if foreign involvement is confirmed.
- Security / Counter-Terrorism: Increased security protocols at military installations; potential for copycat incidents.
- Cyber / Information Space: Risk of cyber operations linked to drone activity; potential for disinformation campaigns exploiting the incident.
- Economic / Social: Limited direct economic impact; potential public concern over national security vulnerabilities.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance drone detection and mitigation capabilities at military installations; conduct a thorough investigation to identify the operator.
- Medium-Term Posture (1–12 months): Develop inter-agency protocols for drone threat response; invest in research and development of counter-drone technologies.
- Scenario Outlook:
- Best: Identification and neutralization of the threat with no further incidents.
- Worst: Continued drone incursions leading to compromised military operations.
- Most-Likely: Sporadic incidents prompting incremental security enhancements.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
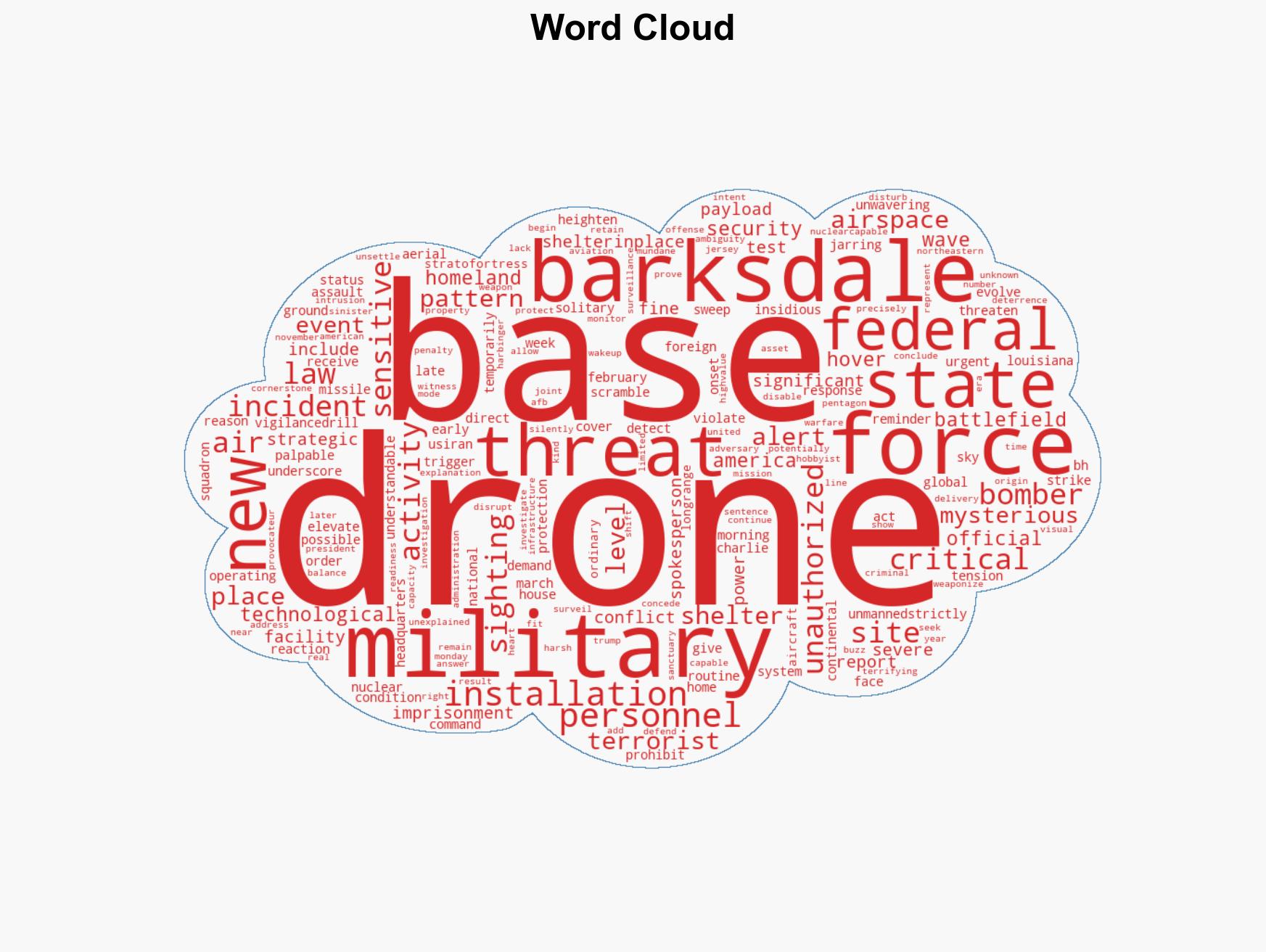
national security threats, counter-terrorism, drone surveillance, military security, national security, airspace violation, intelligence gathering
Structured Analytic Techniques Applied
- Cognitive Bias Stress Test: Expose and correct potential biases in assessments through red-teaming and structured challenge.
- Bayesian Scenario Modeling: Use probabilistic forecasting for conflict trajectories or escalation likelihood.
- Network Influence Mapping: Map relationships between state and non-state actors for impact estimation.
Explore more:
National Security Threats Briefs ·
Daily Summary ·
Support us