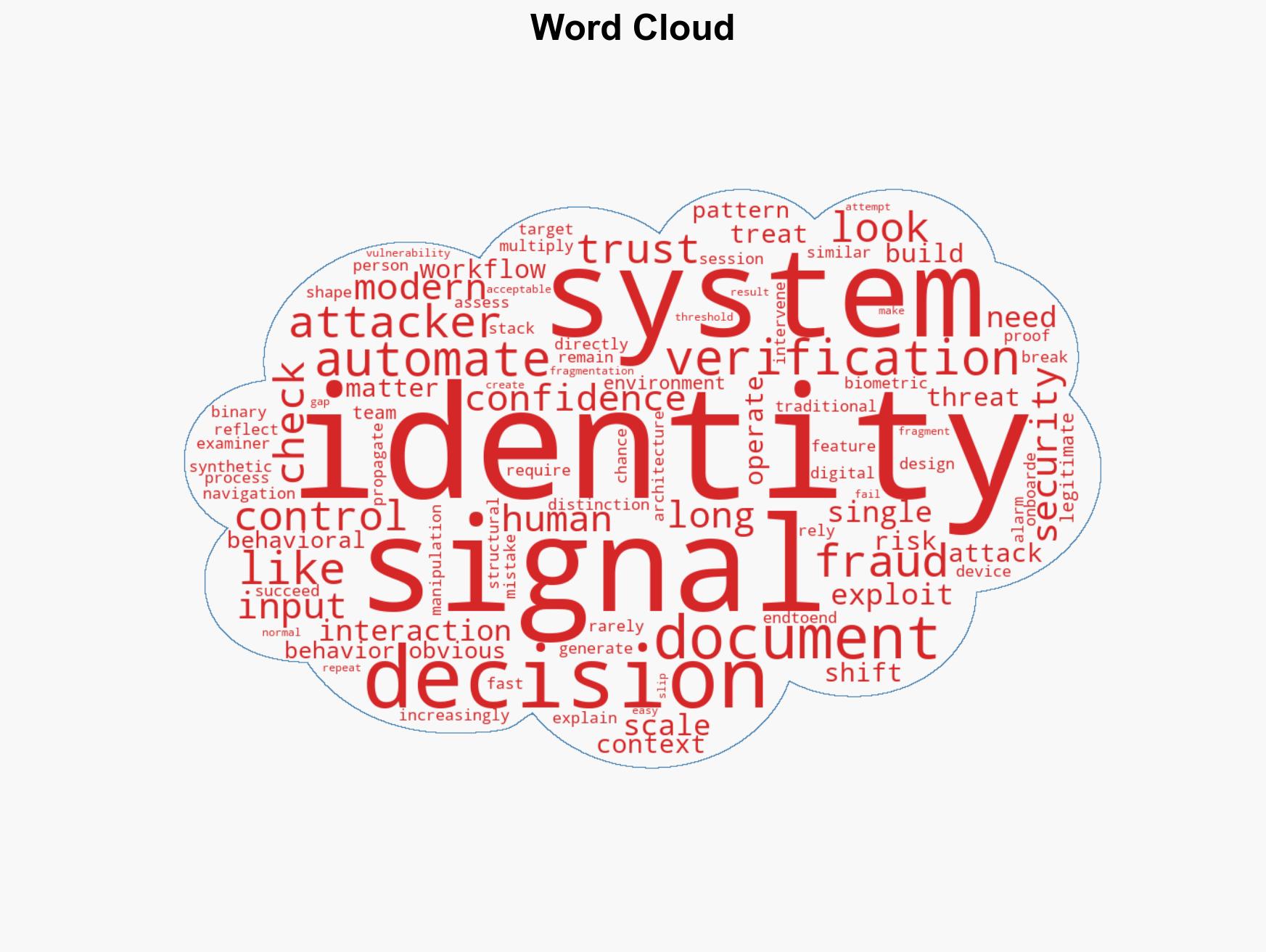
Evolving Identity Threats: From Document Forgery to AI-Driven Signal Manipulation
Published on: 2026-03-11
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Expanded Identity Attack Vectors From Document Fraud to Signal Manipulation
1. BLUF (Bottom Line Up Front)
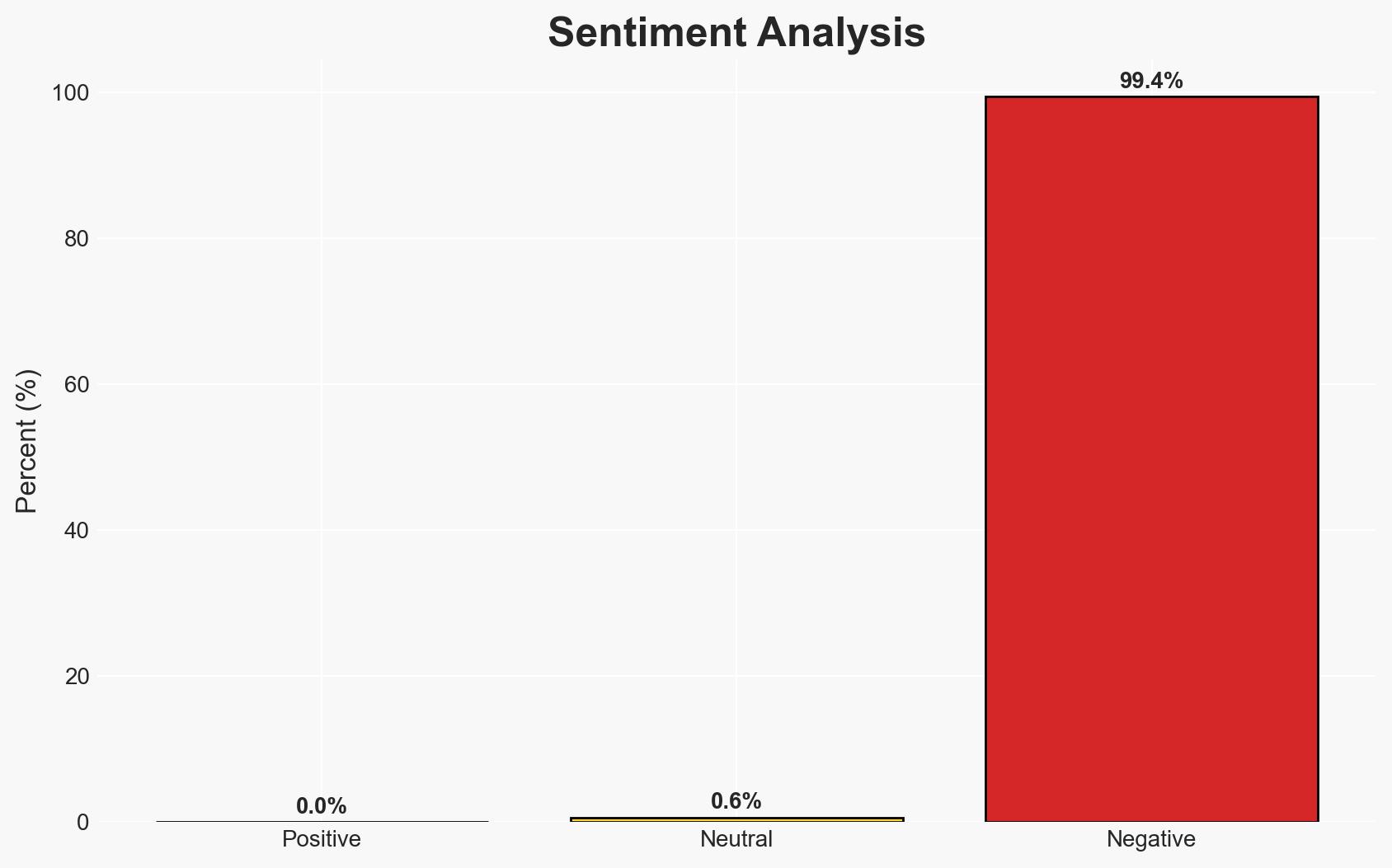
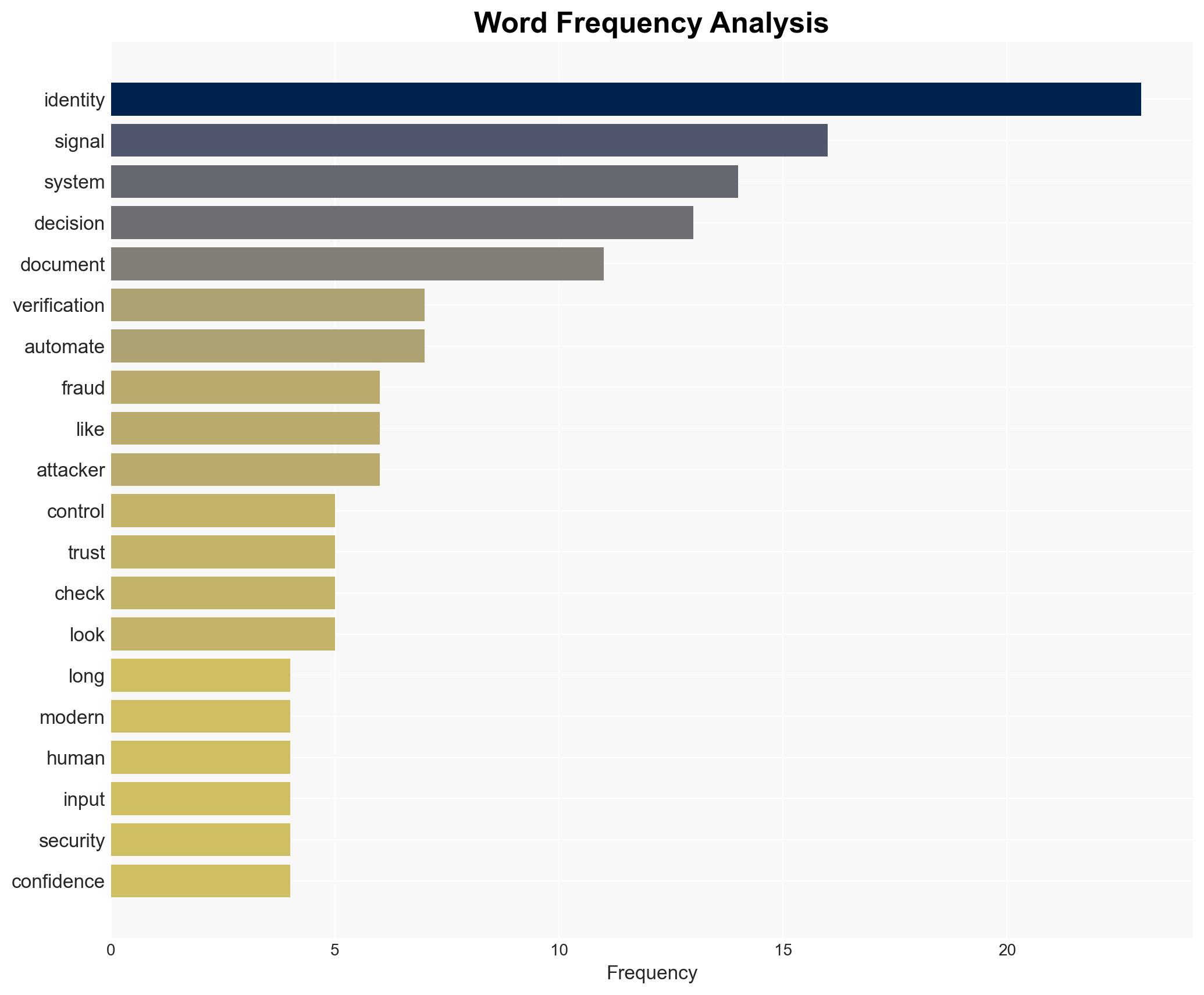
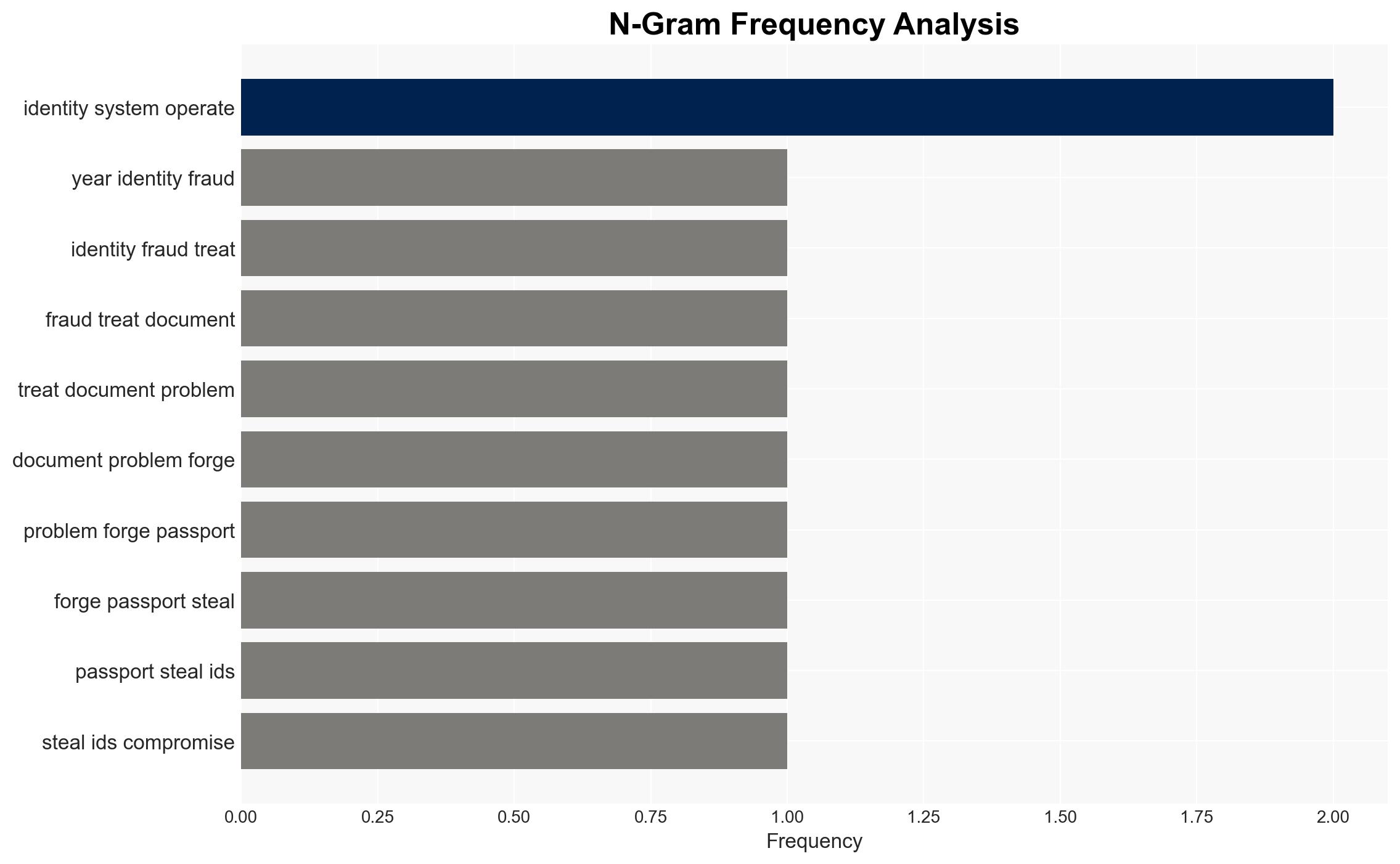
The threat landscape for identity fraud has evolved from document-centric attacks to include sophisticated signal manipulation tactics such as deepfakes and biometric fraud. This shift affects digital identity verification systems globally, increasing the complexity of threat detection. Overall, there is moderate confidence in the assessment that AI-assisted signal manipulation is now a mainstream threat to identity systems.
2. Competing Hypotheses
- Hypothesis A: AI-assisted signal manipulation is now as prevalent as traditional document fraud, driven by the increased reliance on automated identity verification systems. This is supported by similar frequencies of reported incidents across both types of fraud. However, uncertainty remains regarding the full extent of these attacks due to potential underreporting.
- Hypothesis B: Traditional document fraud remains the primary threat, and the perceived rise in signal manipulation is overstated due to heightened media attention and reporting biases. Contradicting evidence includes the consistent reporting of signal manipulation incidents across multiple sources.
- Assessment: Hypothesis A is currently better supported due to the convergence of multiple data points indicating the prevalence of signal manipulation. Key indicators that could shift this judgment include new data on the effectiveness of countermeasures against signal manipulation or a significant increase in traditional document fraud incidents.
3. Key Assumptions and Red Flags
- Assumptions: Automated systems are increasingly used for identity verification; AI capabilities for signal manipulation are accessible to threat actors; traditional document fraud detection remains robust.
- Information Gaps: Comprehensive data on the success rates of signal manipulation attacks; detailed breakdown of the technological capabilities of threat actors.
- Bias & Deception Risks: Potential over-reliance on automated systems may lead to underestimating traditional fraud; media and industry reports may exaggerate the prevalence of new attack vectors.
4. Implications and Strategic Risks
The evolution of identity fraud tactics could lead to increased vulnerabilities in digital identity systems, affecting trust in online transactions and services.
- Political / Geopolitical: Potential for increased international cooperation on cybersecurity standards and identity verification protocols.
- Security / Counter-Terrorism: Enhanced threat environment as terrorist organizations may exploit advanced identity manipulation techniques to bypass security measures.
- Cyber / Information Space: Increased risk of cyber-attacks targeting identity verification systems, necessitating improved cybersecurity measures.
- Economic / Social: Potential economic impacts due to increased fraud losses and the need for investment in more sophisticated verification technologies.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of identity verification systems for signal manipulation attempts; initiate awareness campaigns for stakeholders on emerging threats.
- Medium-Term Posture (1–12 months): Develop partnerships with technology providers to improve AI-based fraud detection capabilities; invest in research for advanced identity verification solutions.
- Scenario Outlook: Best: Robust countermeasures reduce signal manipulation incidents. Worst: Widespread exploitation of identity systems leads to significant economic and security impacts. Most-Likely: Gradual adaptation of systems to new threats, with ongoing challenges in detection and prevention.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, identity fraud, signal manipulation, AI threats, digital verification, biometric fraud, deepfake
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us