Microsoft Addresses 84 Vulnerabilities in March Update, Including Two Public Zero-Day Flaws
Published on: 2026-03-11
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Microsoft Patches 84 Flaws in March Patch Tuesday Including Two Public Zero-Days
1. BLUF (Bottom Line Up Front)
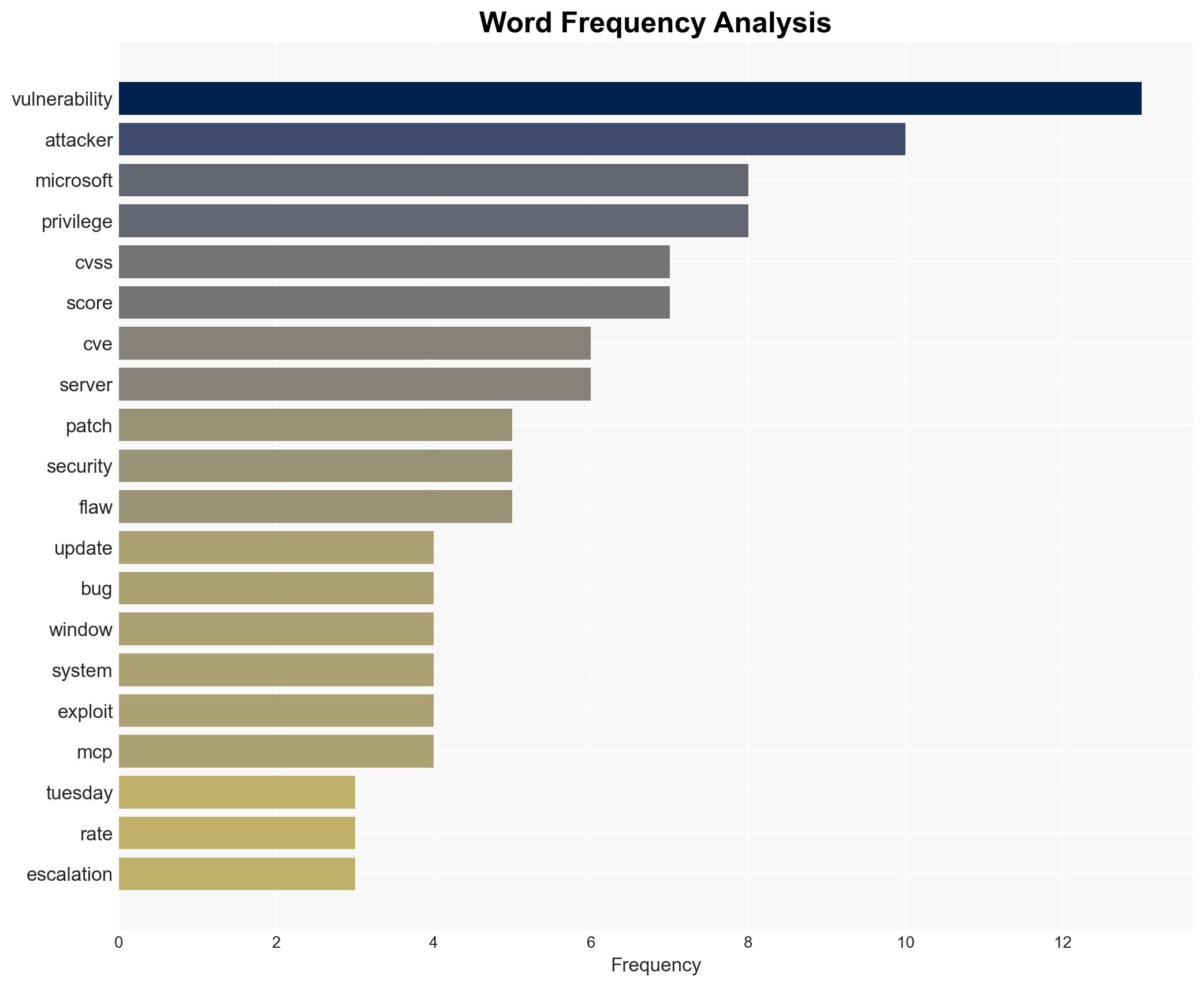
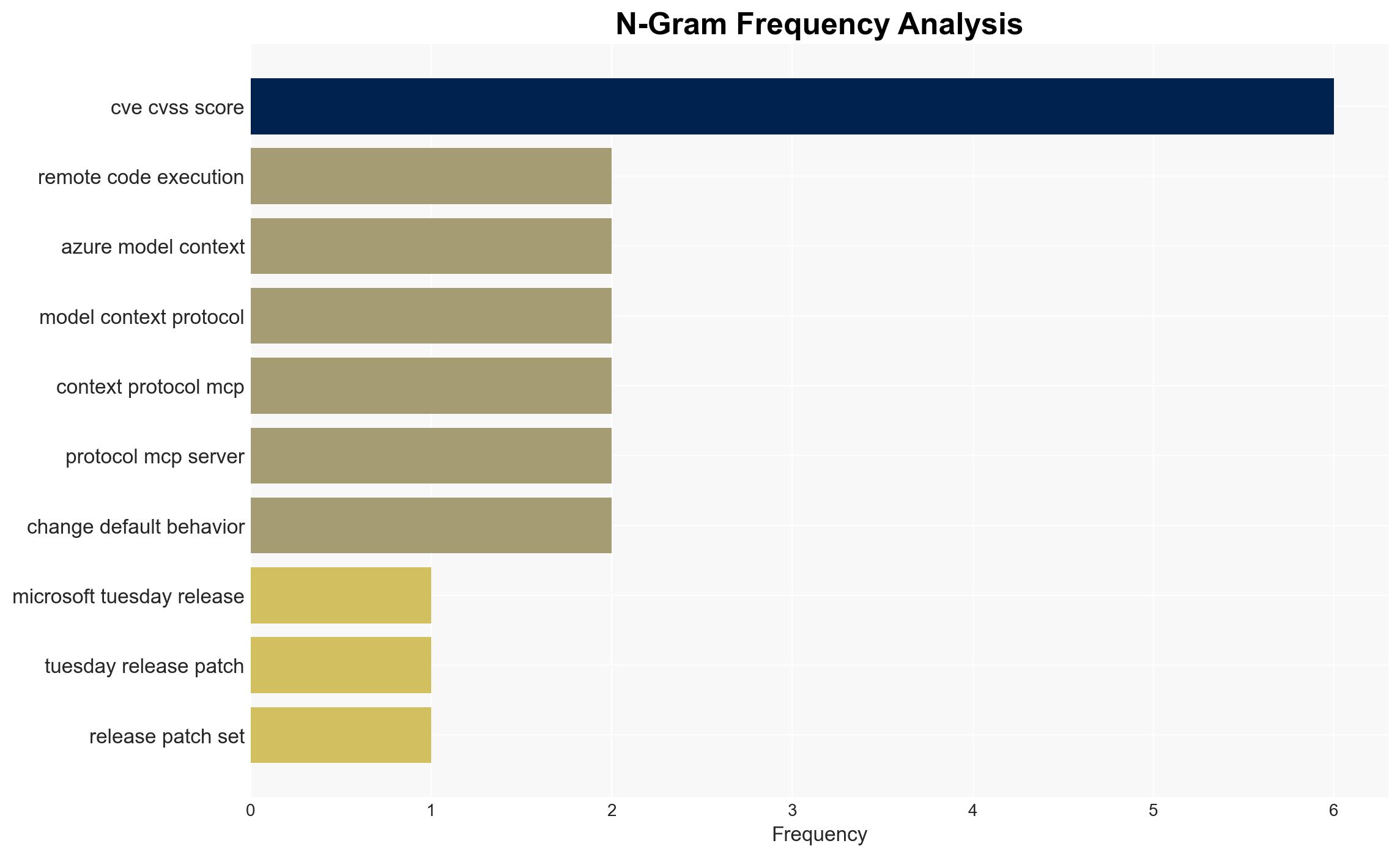
Microsoft’s March Patch Tuesday addressed 84 security vulnerabilities, including two publicly disclosed zero-days. The majority of these vulnerabilities are privilege escalation flaws, posing significant risks if exploited by threat actors. Organizations using affected Microsoft products should prioritize patching to mitigate potential threats. Overall confidence in this assessment is moderate due to limited information on active exploitation.
2. Competing Hypotheses
- Hypothesis A: The vulnerabilities, particularly the privilege escalation flaws, are likely to be exploited by threat actors for post-compromise activities. Supporting evidence includes the high number of privilege escalation vulnerabilities and historical patterns of exploitation. Key uncertainties include the current level of exploitation in the wild.
- Hypothesis B: The vulnerabilities will have limited exploitation due to rapid patch deployment by organizations. This hypothesis is supported by Microsoft’s prompt patch release and the lack of immediate reports of widespread exploitation. However, this assumes effective patch management across all affected organizations.
- Assessment: Hypothesis A is currently better supported due to the nature and number of privilege escalation vulnerabilities, which are attractive targets for threat actors. Indicators that could shift this judgment include reports of active exploitation or widespread patch adoption.
3. Key Assumptions and Red Flags
- Assumptions: Organizations will prioritize patching critical vulnerabilities; threat actors have the capability to exploit these flaws; Microsoft patches are effective in mitigating the vulnerabilities.
- Information Gaps: Lack of data on the current exploitation status of the vulnerabilities; insufficient details on the effectiveness of patches in diverse environments.
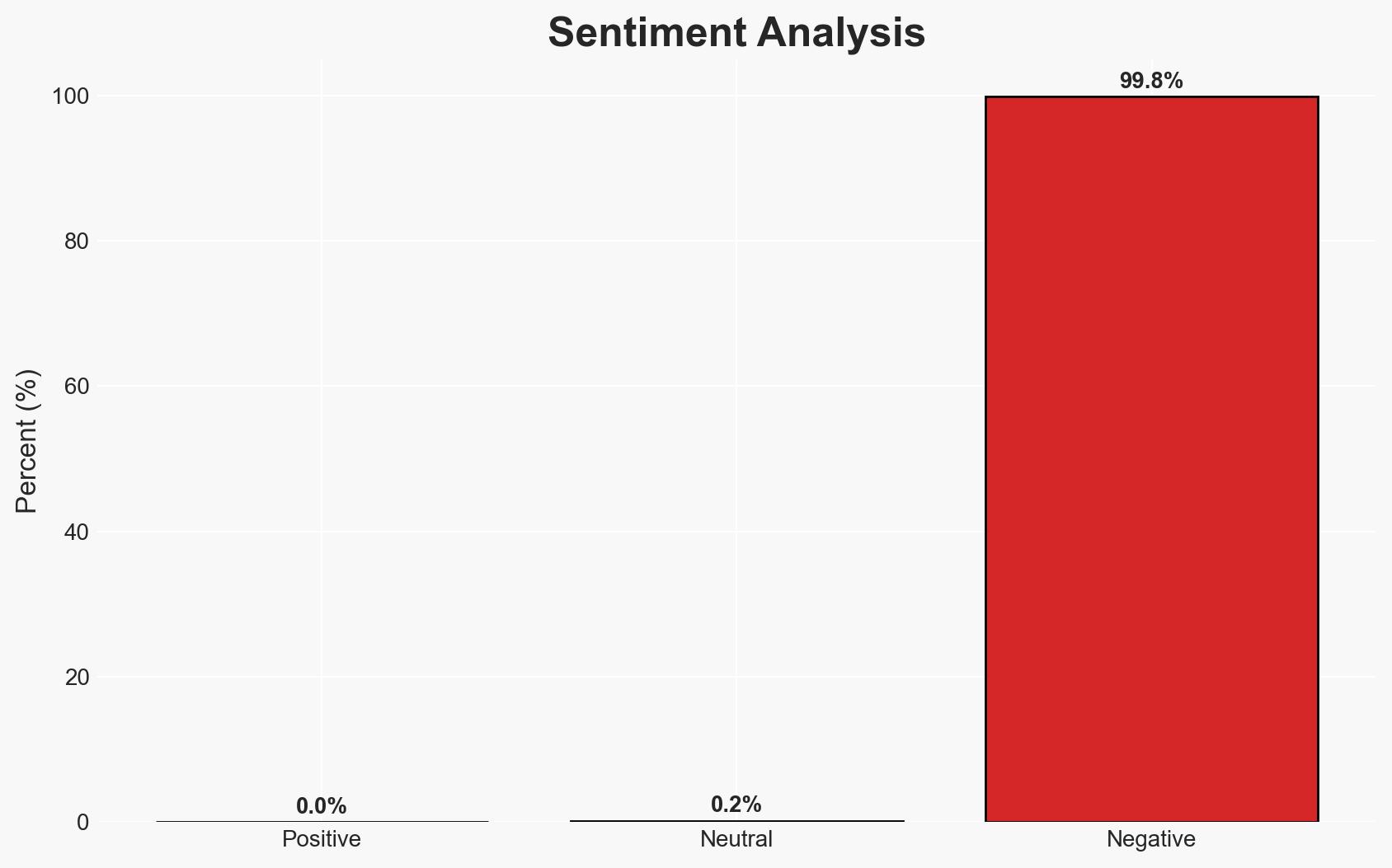
- Bias & Deception Risks: Potential bias in reporting from cybersecurity firms with vested interests in highlighting vulnerabilities; possible underreporting of exploitation by affected organizations.
4. Implications and Strategic Risks
The resolution of these vulnerabilities could influence the cybersecurity landscape by altering threat actor strategies and organizational security postures.
- Political / Geopolitical: Limited direct impact, but potential for increased cyber tensions if state actors exploit these vulnerabilities.
- Security / Counter-Terrorism: Increased risk of cyber-attacks leveraging these vulnerabilities, potentially affecting critical infrastructure.
- Cyber / Information Space: Potential for increased cyber espionage and data breaches if vulnerabilities are exploited before patching.
- Economic / Social: Potential financial losses for businesses due to data breaches or system downtime; increased pressure on IT departments to manage patching.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Organizations should immediately apply the patches, prioritize critical systems, and monitor for signs of exploitation.
- Medium-Term Posture (1–12 months): Enhance patch management processes, conduct regular security audits, and invest in threat intelligence capabilities.
- Scenario Outlook:
- Best: Rapid patch adoption leads to minimal exploitation.
- Worst: Widespread exploitation before patches are applied, leading to significant data breaches.
- Most-Likely: Moderate exploitation with some organizations failing to patch promptly.
6. Key Individuals and Entities
- Satnam Narang, Tenable
- James Forshaw, Google Project Zero
- Jacob Ashdown, Immersive
- Microsoft
- XBOW (AI-powered platform)
7. Thematic Tags
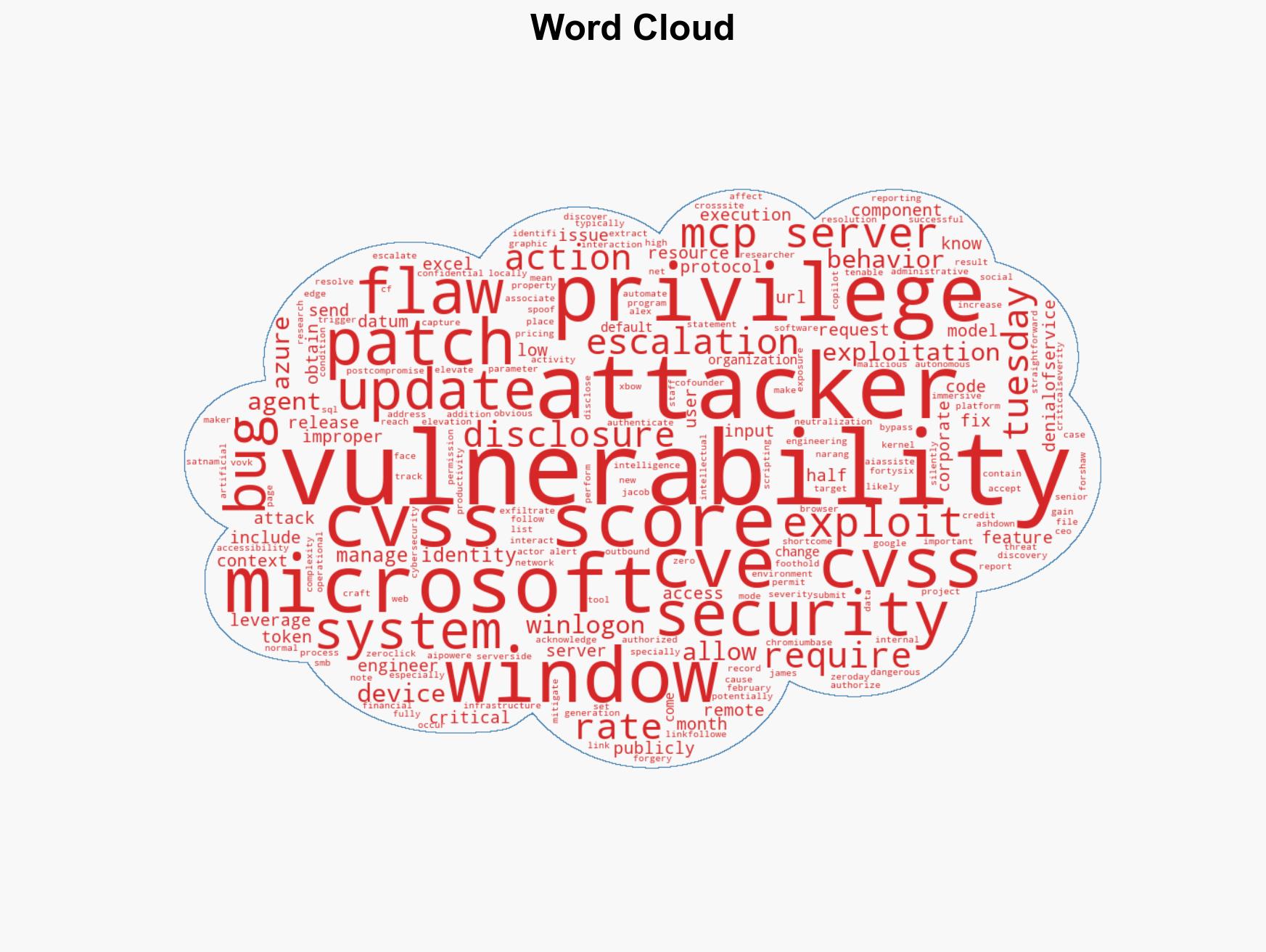
cybersecurity, vulnerability management, zero-day exploitation, patch management, privilege escalation, Microsoft, threat actors
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us