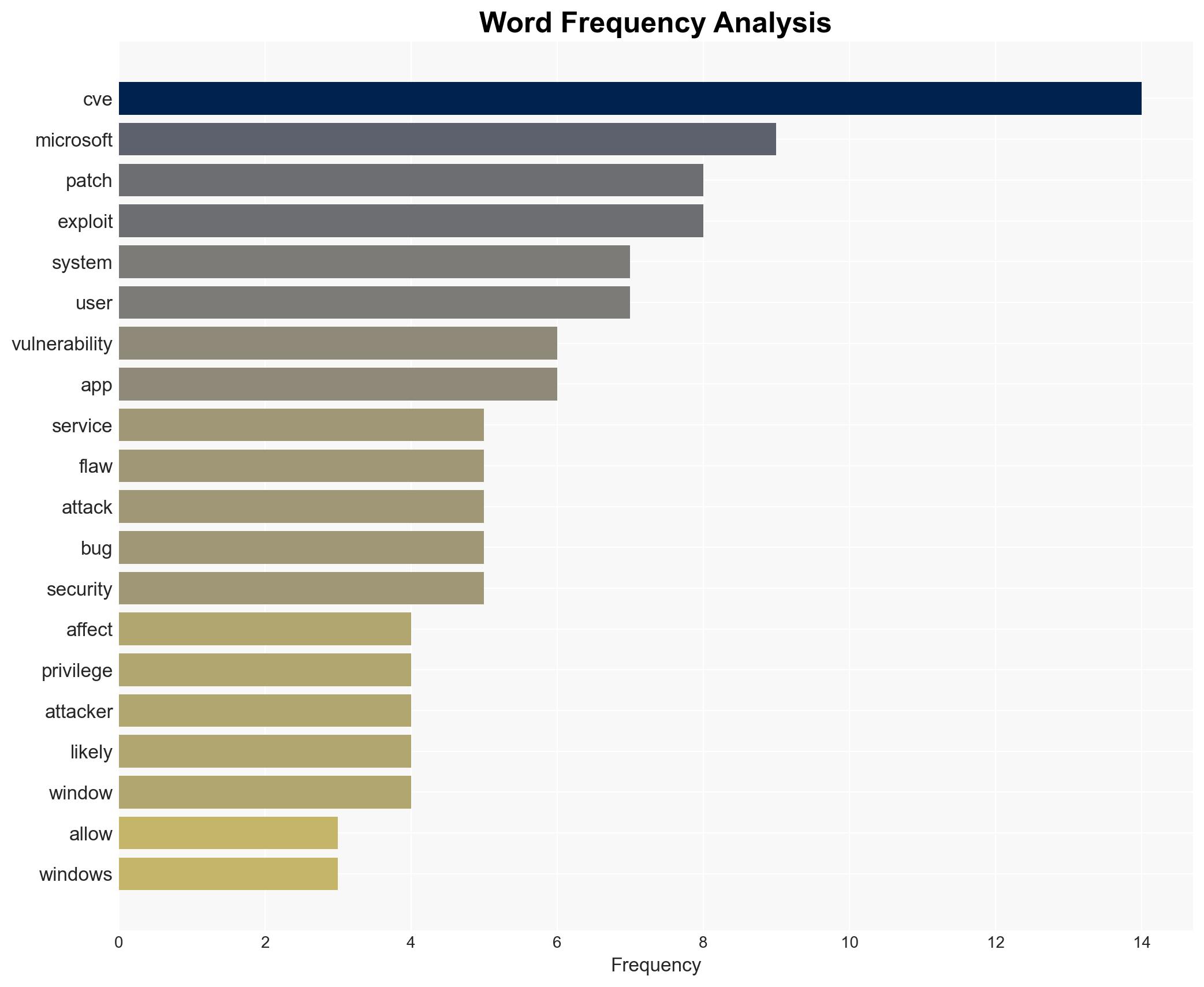
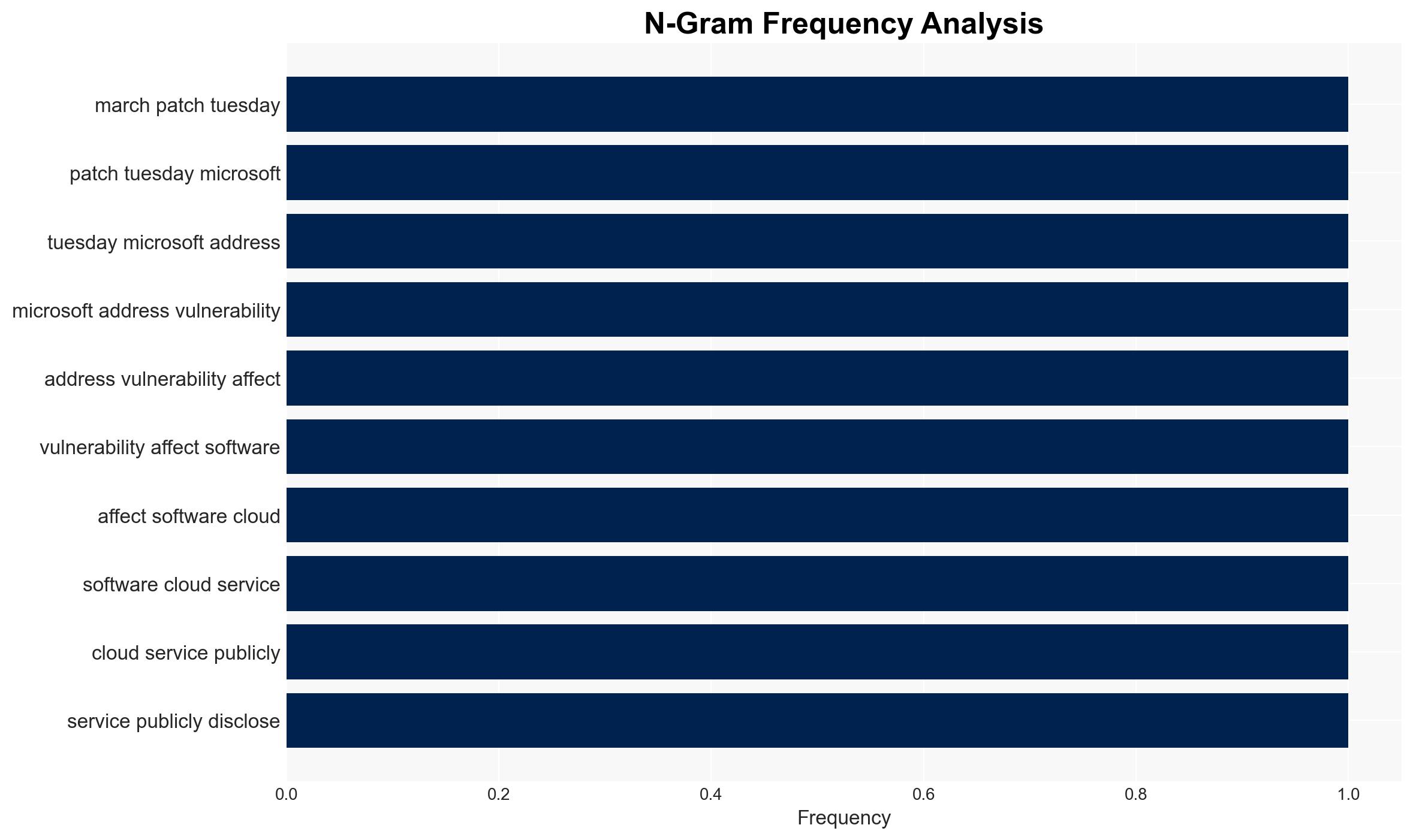
Microsoft addresses over 80 vulnerabilities, highlighting six with heightened exploitation risk
Published on: 2026-03-11
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Microsoft patches 80 vulnerabilities six flagged as more likely to be exploited
1. BLUF (Bottom Line Up Front)
Microsoft has patched over 80 vulnerabilities, with six identified as more likely to be exploited, posing significant risks to systems running Windows software. These vulnerabilities, particularly those enabling privilege escalation to SYSTEM level, could be targeted by threat actors to gain control over affected systems. The rapid deployment of patches is crucial to maintain system integrity. Overall confidence in this assessment is moderate due to incomplete data on exploitation attempts.
2. Competing Hypotheses
- Hypothesis A: The vulnerabilities will be actively exploited by threat actors due to their potential to grant SYSTEM-level access, which is highly desirable for bypassing security measures. Supporting evidence includes the nature of the vulnerabilities and their potential impact. Key uncertainties include the speed and extent of patch deployment.
- Hypothesis B: The vulnerabilities will not be widely exploited due to prompt patching by organizations and the complexity of exploiting some of these flaws. Supporting evidence includes Microsoft’s assessment of some vulnerabilities as “less likely” to be exploited. However, this is contradicted by the potential attack surface and the value of SYSTEM access.
- Assessment: Hypothesis A is currently better supported due to the high value of SYSTEM-level access and the vast attack surface. Indicators such as reports of active exploitation or delays in patch deployment could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Organizations will prioritize patch deployment; threat actors have the capability to exploit these vulnerabilities; Microsoft’s assessments of exploitation likelihood are accurate.
- Information Gaps: Data on the speed of patch deployment across different sectors; intelligence on threat actor intentions and capabilities.
- Bias & Deception Risks: Potential bias in Microsoft’s assessment of exploitation likelihood; possible underreporting of exploitation attempts.
4. Implications and Strategic Risks
This development could lead to increased cyber threats if patches are not deployed swiftly, potentially affecting critical infrastructure and sensitive data.
- Political / Geopolitical: Potential for state-sponsored actors to exploit vulnerabilities for espionage or disruption.
- Security / Counter-Terrorism: Increased risk of cyber attacks on critical infrastructure, potentially impacting national security.
- Cyber / Information Space: Elevated threat landscape with potential for widespread exploitation if patches are delayed.
- Economic / Social: Possible economic impact due to disruptions in business operations and increased costs for cybersecurity measures.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Ensure rapid deployment of patches across all systems; increase monitoring for signs of exploitation; disseminate threat intelligence to relevant stakeholders.
- Medium-Term Posture (1–12 months): Develop resilience measures, enhance cybersecurity training, and strengthen partnerships with cybersecurity firms and government agencies.
- Scenario Outlook:
- Best Case: Rapid patch deployment prevents significant exploitation; threat landscape stabilizes.
- Worst Case: Widespread exploitation leads to significant disruptions and data breaches.
- Most-Likely: Some exploitation occurs, but impact is mitigated by effective patch management and response strategies.
6. Key Individuals and Entities
- Microsoft
- Trend Micro’s Zero Day Initiative
- Immersive
- Marcin Wiązowski
- Dustin Childs
- Ben McCarthy
7. Thematic Tags
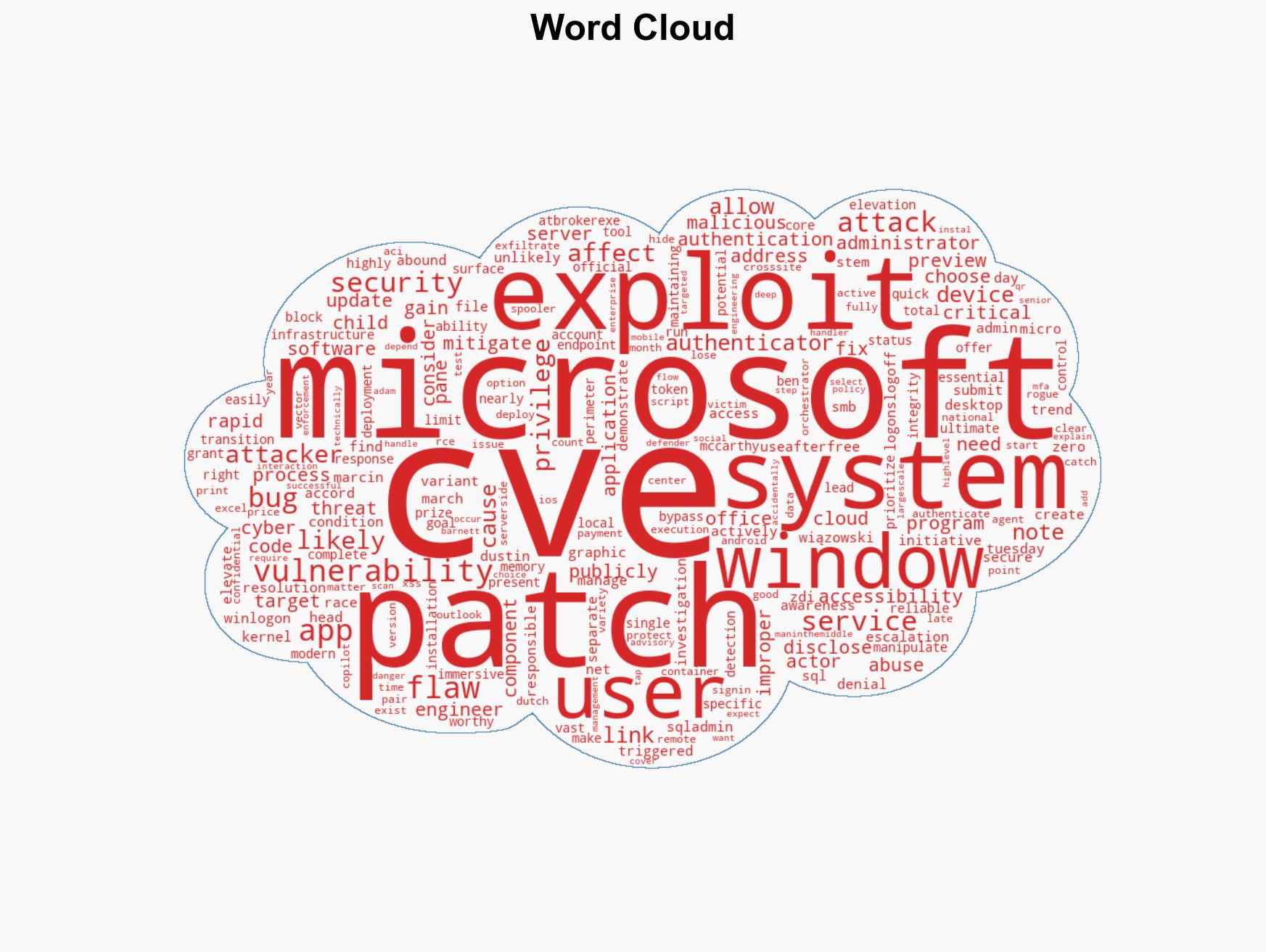
cybersecurity, vulnerability management, privilege escalation, Microsoft, patch deployment, threat actors, system integrity
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us