U.S. Military Implements Cyber Operations as Key Component of New Strategy Against Iran
Published on: 2026-03-11
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Trumps New Cyber-First War Strategy
1. BLUF (Bottom Line Up Front)
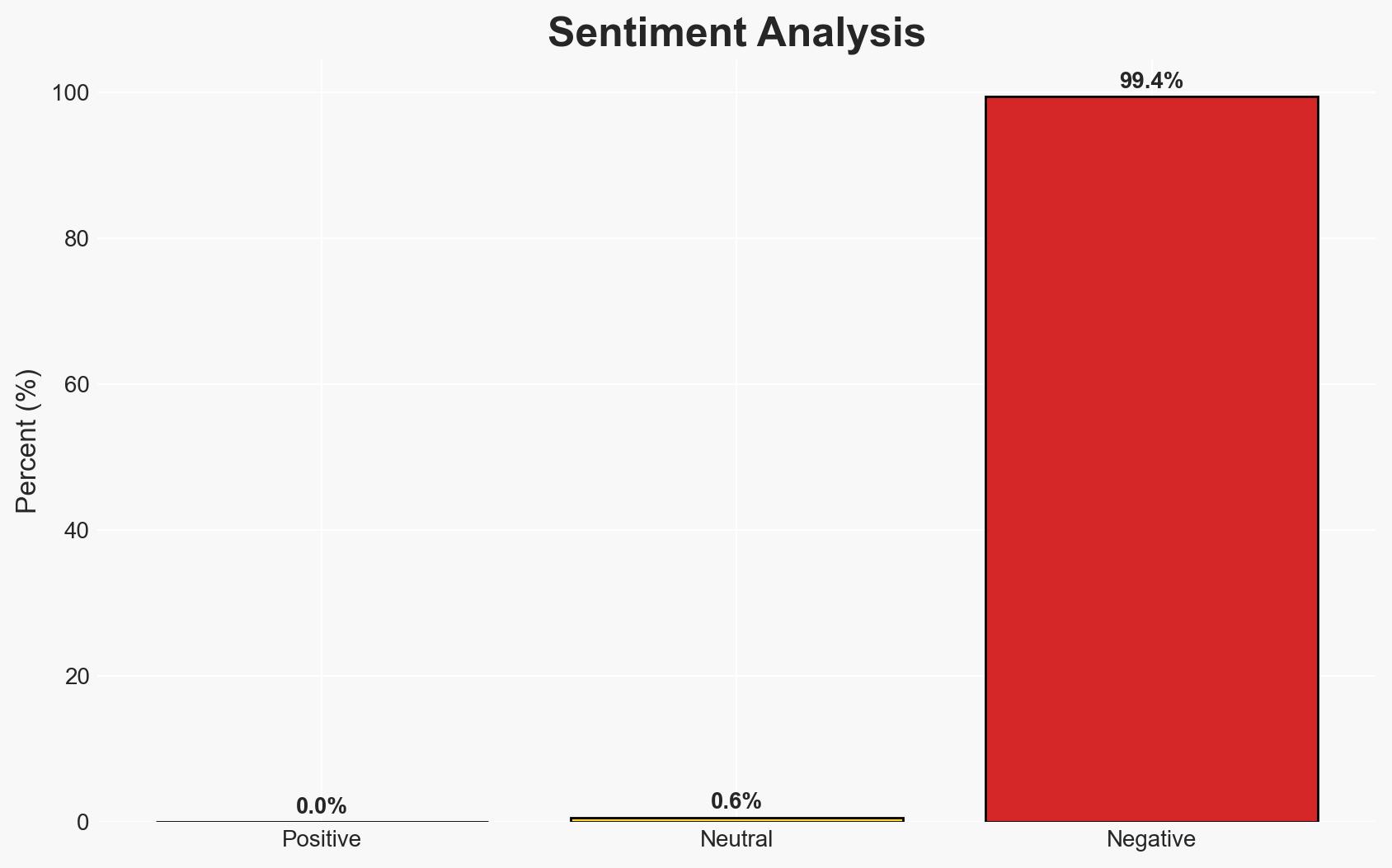
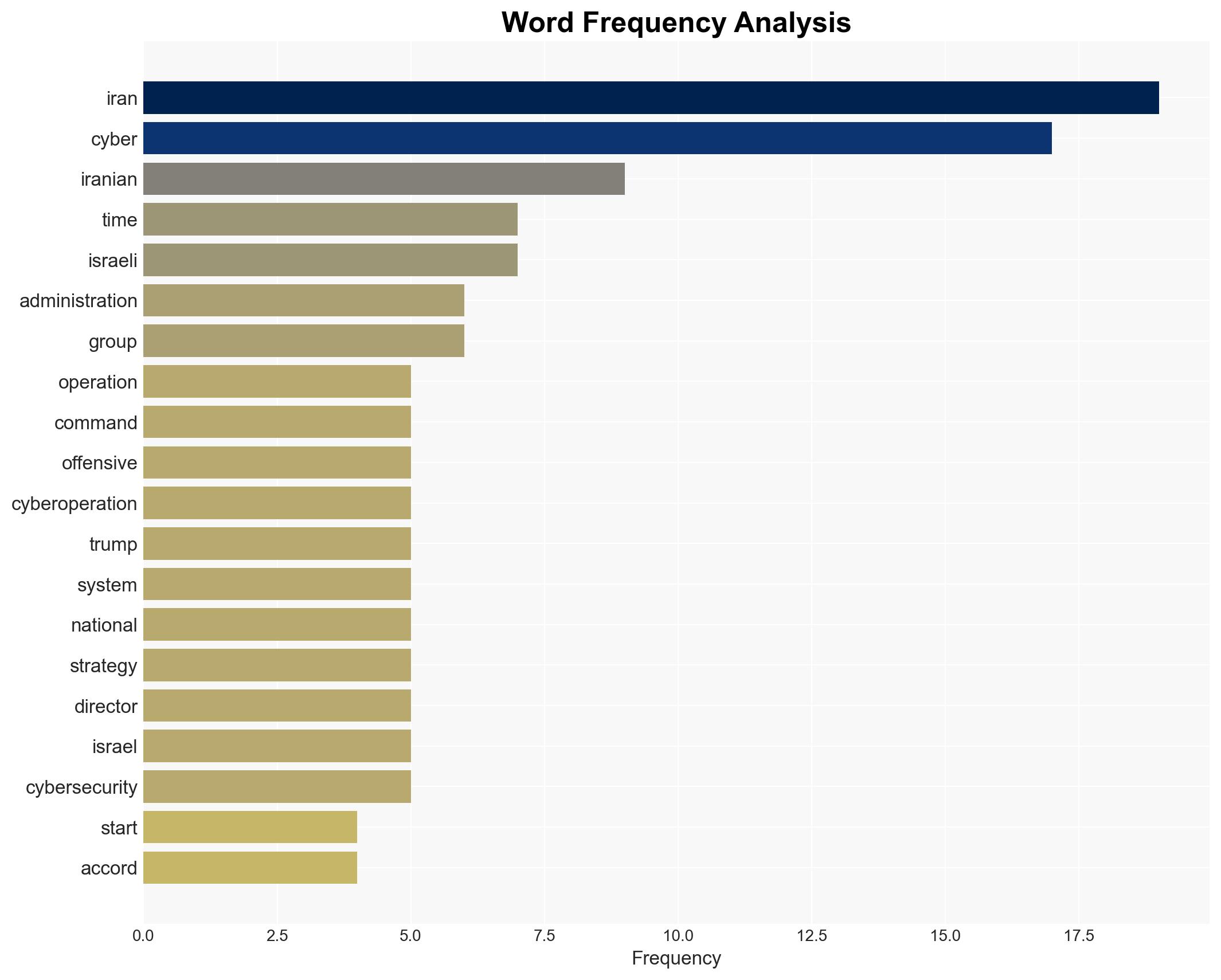
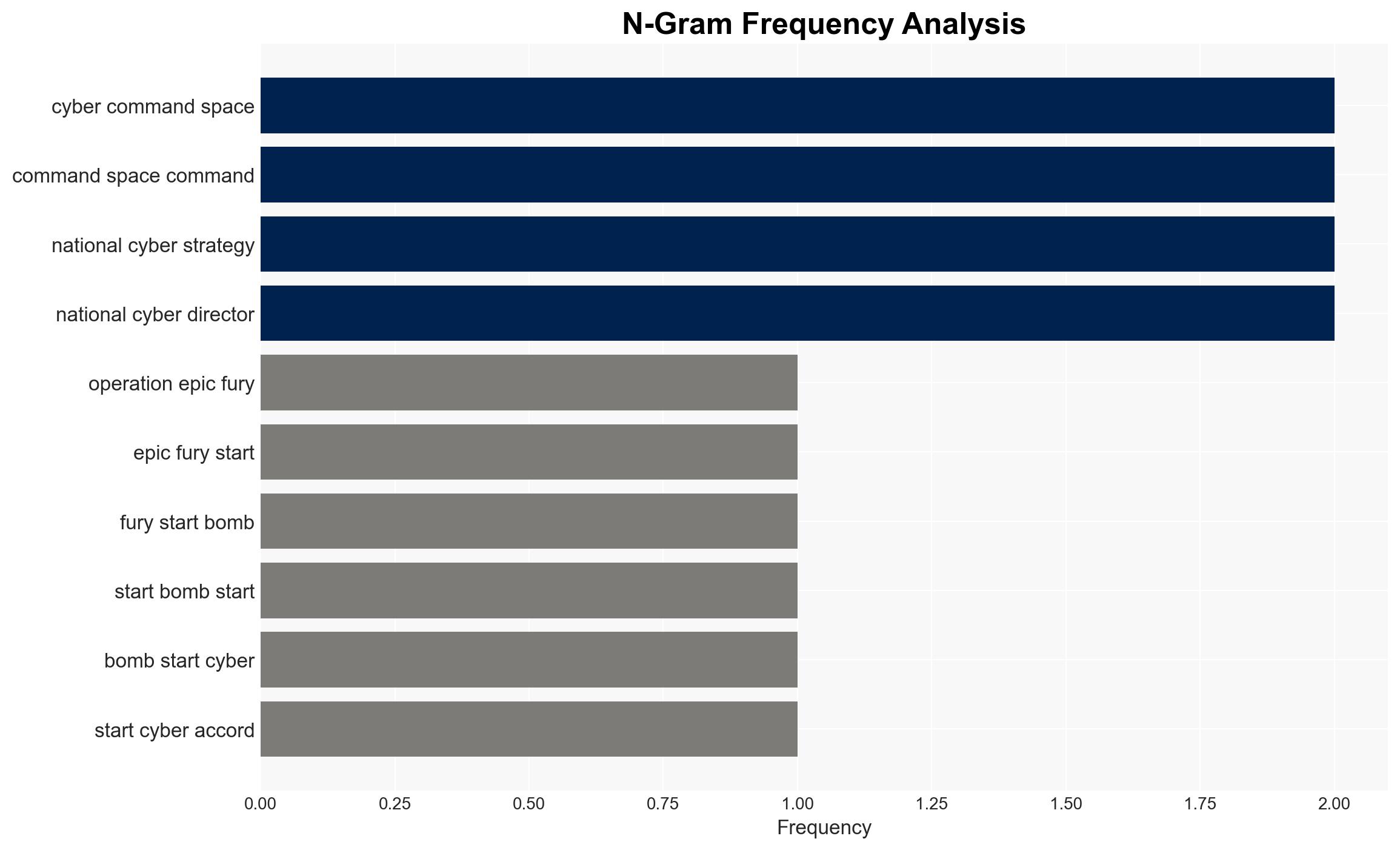
The Trump administration’s new cyber-first war strategy emphasizes offensive cyberoperations as a primary tool in military engagements, notably against Iran and Venezuela. This approach aims to disrupt adversaries’ capabilities before kinetic actions. The strategy may alter global cyber norms and provoke adversarial responses. Overall confidence in this assessment is moderate, given the limited public details on specific operations and effects.
2. Competing Hypotheses
- Hypothesis A: The cyber-first strategy is primarily a deterrent measure to reshape adversary behavior by showcasing U.S. cyber capabilities. Evidence includes public acknowledgment of cyber operations and strategic doctrine emphasizing deterrence. However, the effectiveness of deterrence through cyber means remains uncertain.
- Hypothesis B: The strategy is an escalation of cyber warfare, aiming to gain tactical advantages in conflicts without full-scale military engagement. This is supported by the use of cyber operations preceding kinetic actions. Contradictory evidence includes potential diplomatic fallout and international norms against cyber warfare.
- Assessment: Hypothesis A is currently better supported, as the strategy’s public articulation suggests a focus on deterrence. Key indicators that could shift this judgment include increased frequency of cyber operations and international responses.
3. Key Assumptions and Red Flags
- Assumptions: The U.S. has the capability to effectively disrupt adversary systems; adversaries will perceive these actions as deterrents; cyber operations can be controlled to avoid unintended escalation.
- Information Gaps: Specific details on the cyber operations’ scope and impact; adversaries’ internal assessments and responses; long-term strategic objectives of the U.S. cyber strategy.
- Bias & Deception Risks: Potential overconfidence in cyber capabilities; public statements may be intended to mislead adversaries or domestic audiences; reliance on limited sources may skew understanding of operations’ effectiveness.
4. Implications and Strategic Risks
The cyber-first strategy could redefine military engagement norms and provoke adversarial cyber responses, potentially escalating conflicts. It may also influence global cyber policy and alliances.
- Political / Geopolitical: Potential for increased tensions with adversaries like Iran and Venezuela; challenges to international cyber norms.
- Security / Counter-Terrorism: Shifts in threat landscapes as adversaries adapt to U.S. cyber tactics; potential for retaliatory cyber attacks.
- Cyber / Information Space: Increased focus on cyber defense and resilience; potential for misinformation campaigns exploiting cyber operations.
- Economic / Social: Possible impacts on global markets due to instability; domestic concerns over cyber warfare ethics and privacy.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of adversary cyber activities; engage in diplomatic efforts to clarify U.S. intentions and mitigate escalation risks.
- Medium-Term Posture (1–12 months): Develop resilience measures for critical infrastructure; strengthen international partnerships on cyber norms and defense.
- Scenario Outlook: Best: Successful deterrence with minimal escalation; Worst: Escalation into broader cyber conflict; Most-Likely: Continued low-intensity cyber engagements with periodic diplomatic tensions.
6. Key Individuals and Entities
- Gen. Dan Caine, U.S. Joint Chiefs of Staff chair
- U.S. Cyber Command
- U.S. Space Command
- U.S. National Cyber Director Sean Cairncross
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
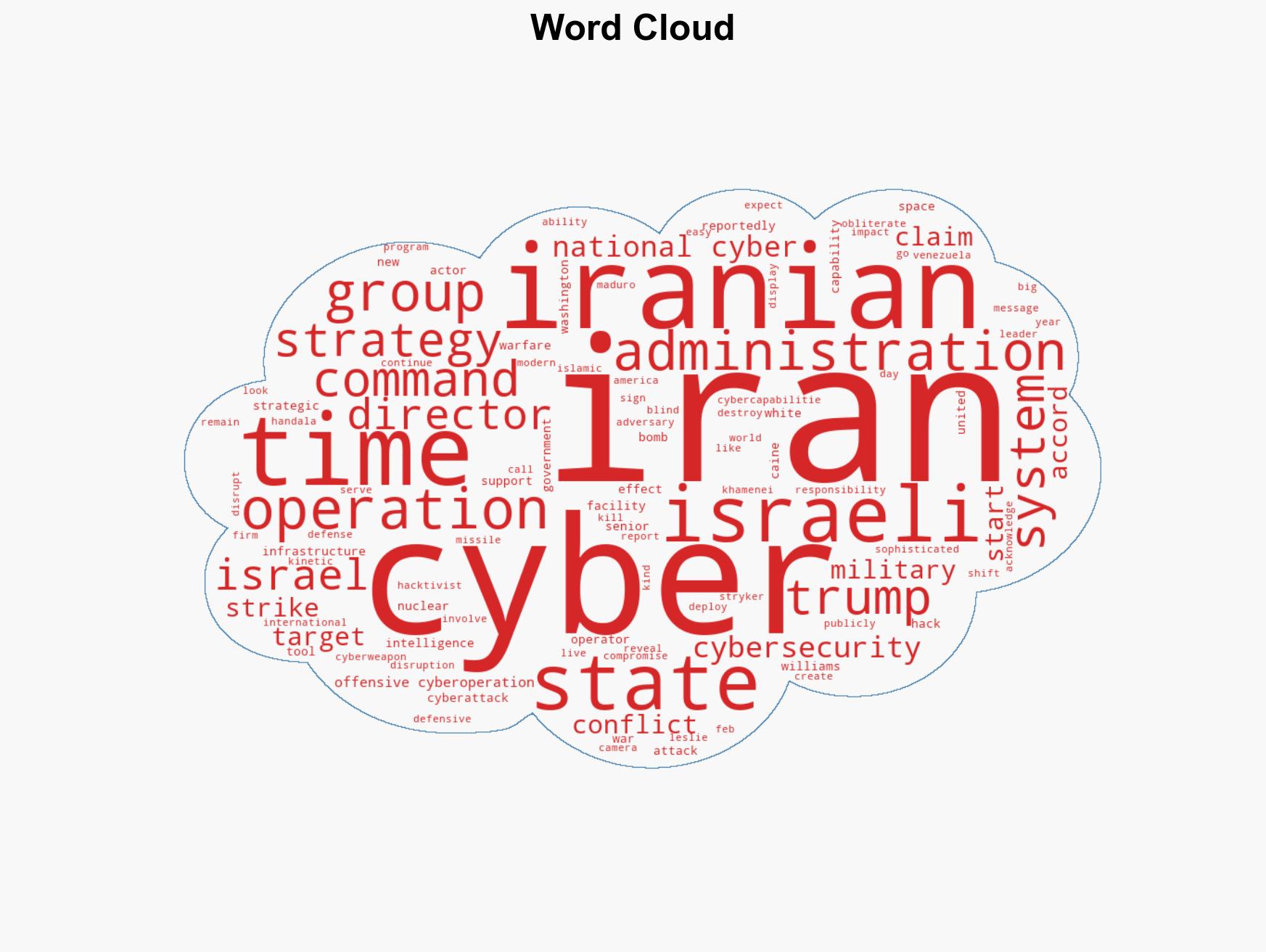
cybersecurity, cyber warfare, deterrence, U.S. military strategy, Iran conflict, Venezuela operations, cyber norms, geopolitical tensions
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us