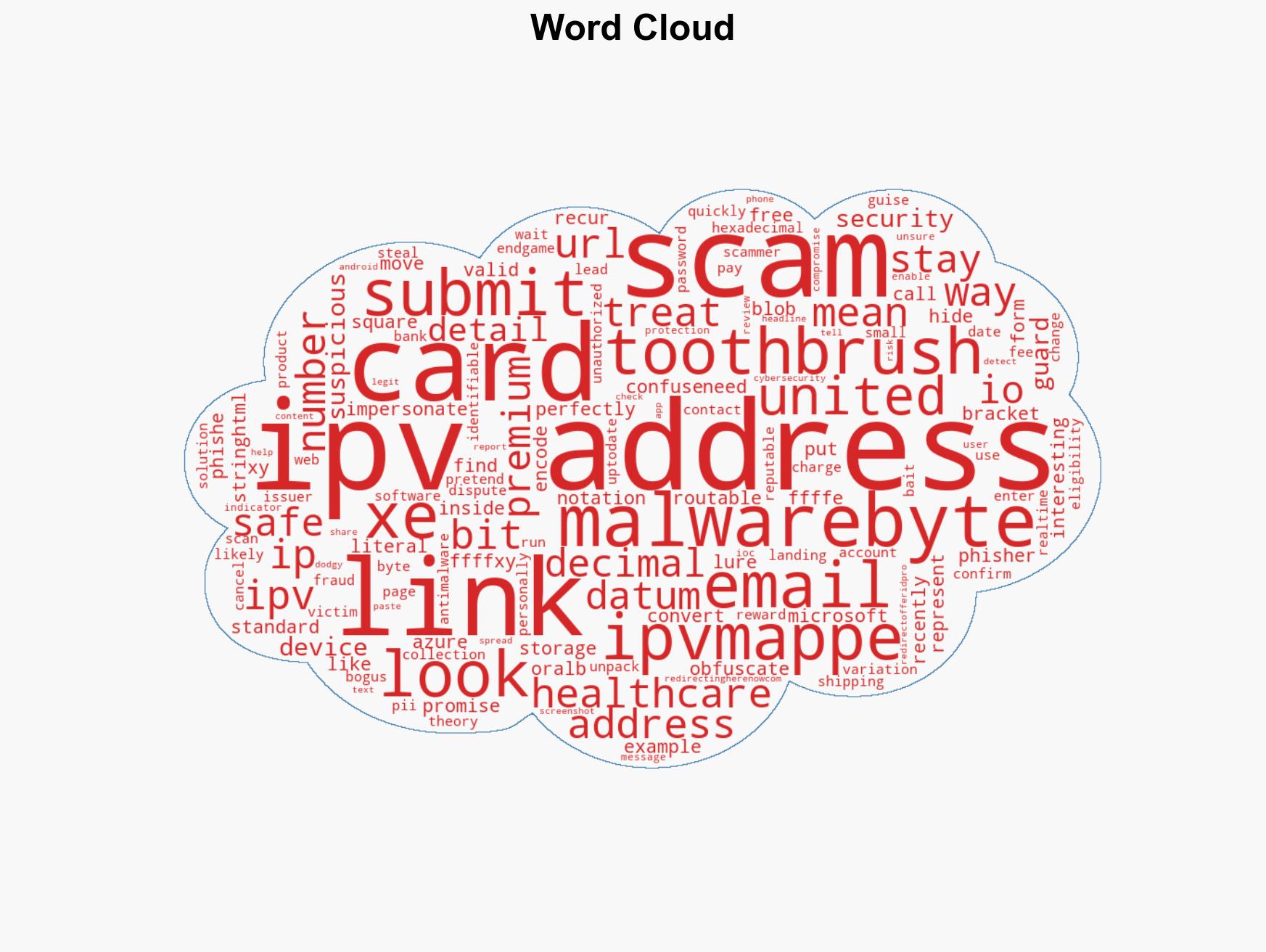
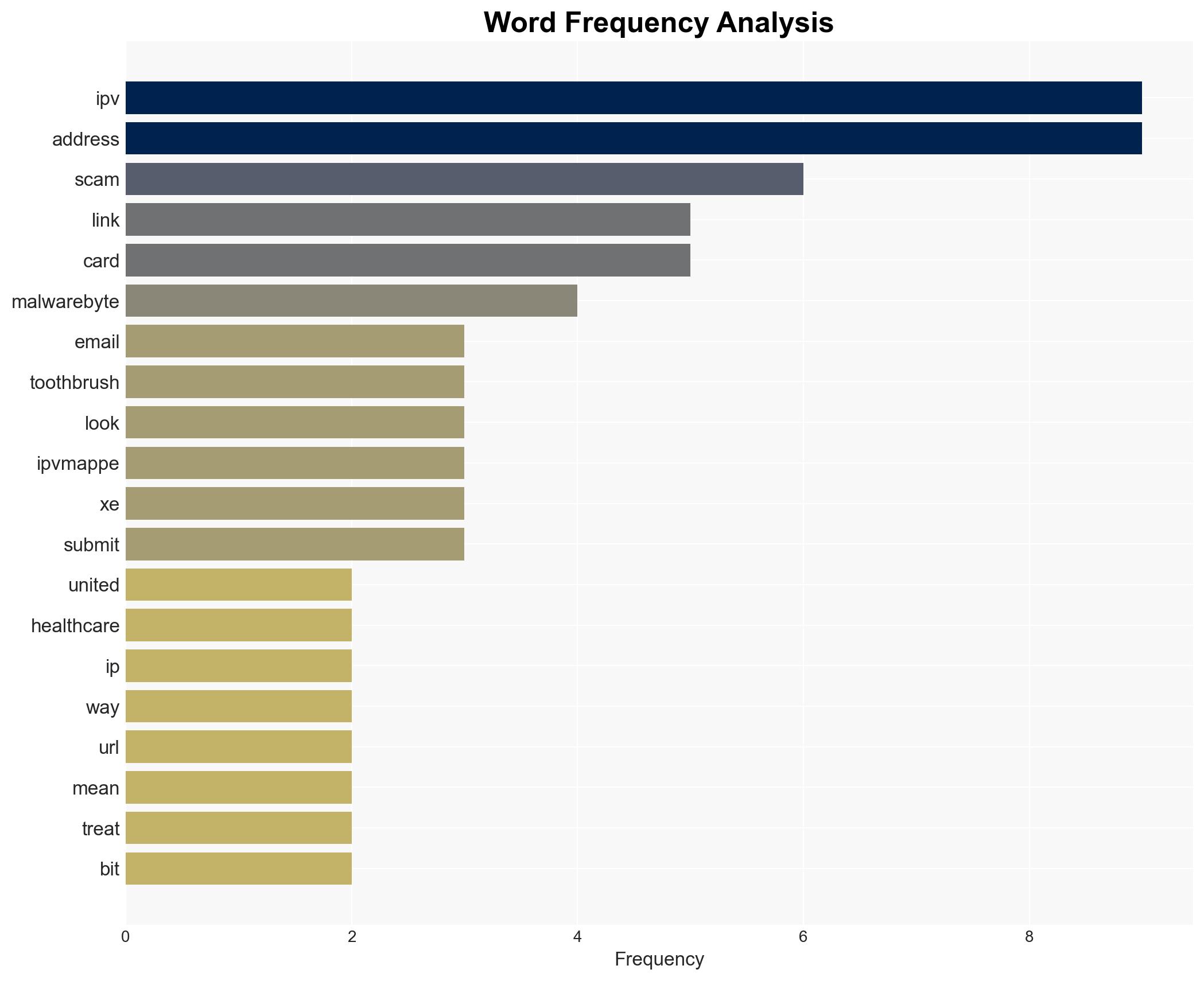
Phishing Scams Use IPv6 Obfuscation in Emails Offering Free Oral-B Toothbrushes
Published on: 2026-03-11
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Phishers hide scam links with IPv6 trick in free toothbrush emails
1. BLUF (Bottom Line Up Front)
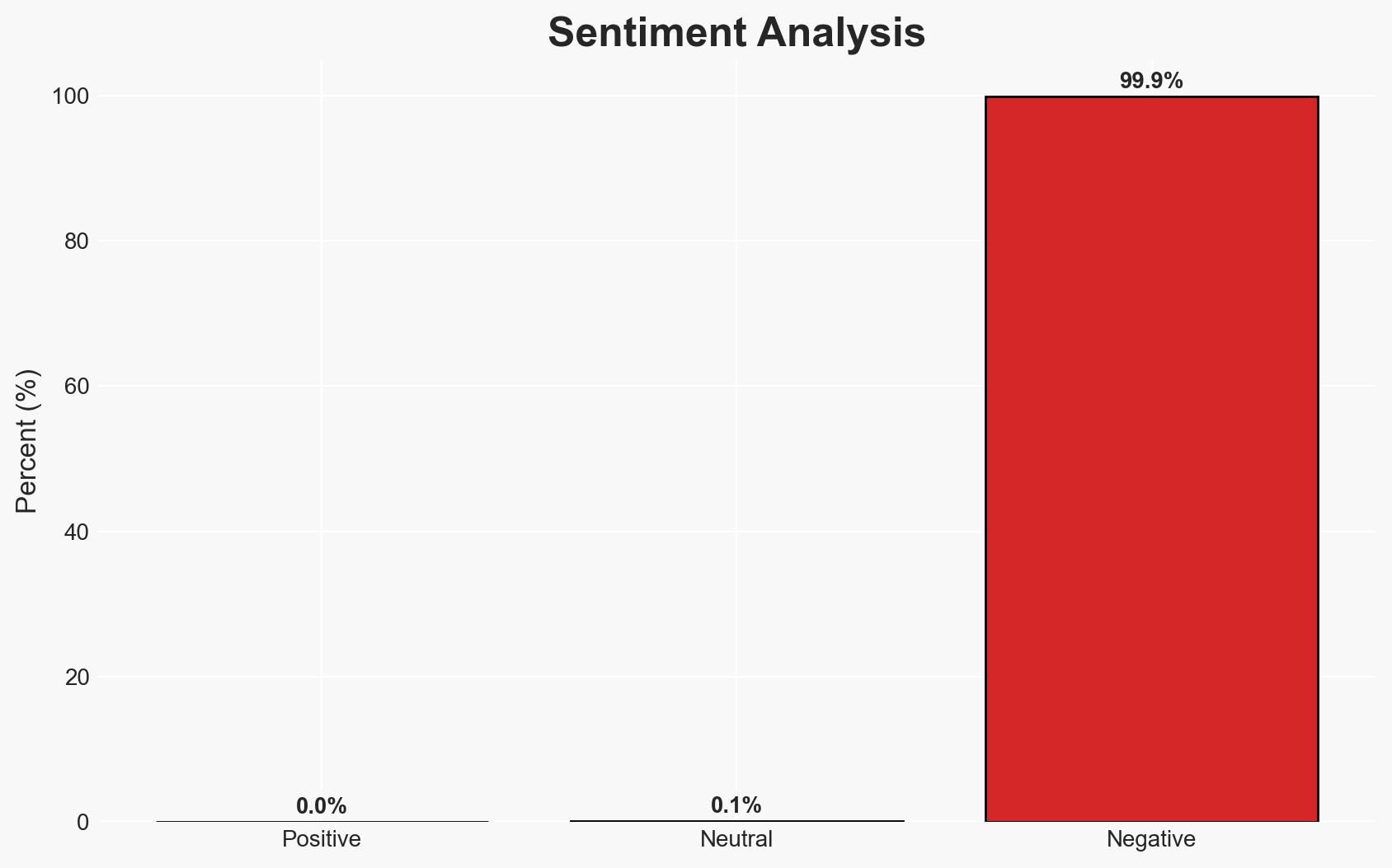
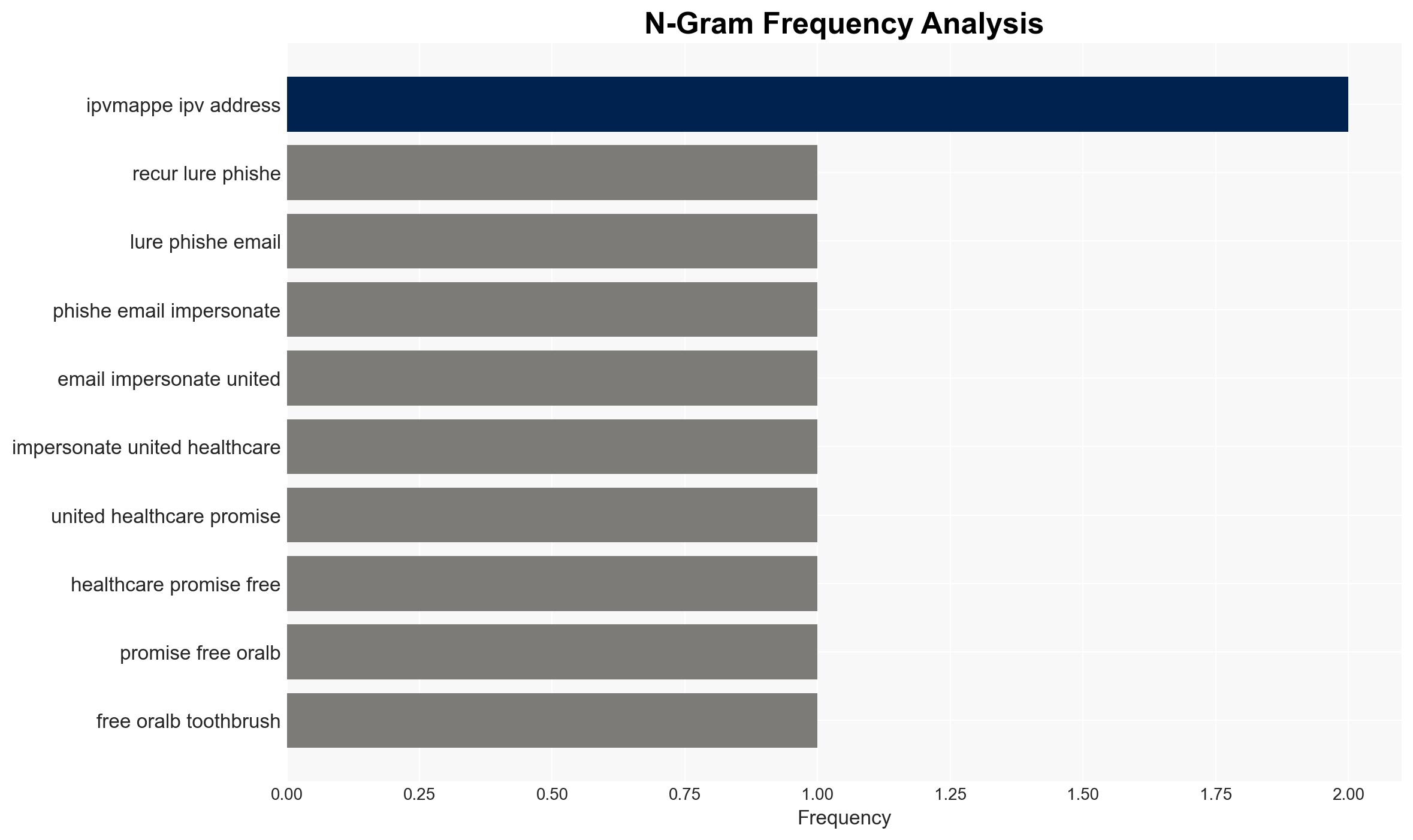
Phishers are employing IPv6-mapped IPv4 addresses to obfuscate links in phishing emails impersonating United Healthcare, aiming to collect personal and financial information. This tactic complicates detection and mitigation efforts, posing a moderate threat to cybersecurity. The most likely hypothesis is that this method is primarily used to evade traditional detection mechanisms. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: Phishers are using IPv6-mapped IPv4 addresses to evade detection by traditional security systems. This hypothesis is supported by the technical complexity of the method, which can confuse automated detection tools. However, the effectiveness of this evasion tactic is not fully confirmed due to limited data on detection rates.
- Hypothesis B: The use of IPv6-mapped IPv4 addresses is a test of new phishing methods rather than a fully operational tactic. This hypothesis is supported by the novelty of the approach and the possibility that phishers are experimenting with different techniques to find the most effective one. Contradicting evidence includes the operational use of these links in active campaigns.
- Assessment: Hypothesis A is currently better supported due to the operational deployment of these tactics in active phishing campaigns, suggesting a deliberate attempt to bypass existing security measures. Key indicators that could shift this judgment include increased detection rates or reports of similar tactics in other campaigns.
3. Key Assumptions and Red Flags
- Assumptions: Phishers have the technical capability to implement IPv6-mapped IPv4 addresses; Security systems are not fully adapted to detect these obfuscation techniques; The primary objective is the collection of PII and financial data.
- Information Gaps: The effectiveness of IPv6 obfuscation in evading detection; The scale and scope of the phishing campaign; The origin and identity of the threat actors.
- Bias & Deception Risks: Potential overestimation of the threat due to novelty bias; Source bias from cybersecurity vendors emphasizing the threat to promote their services; Possible deception by threat actors to mislead analysis.
4. Implications and Strategic Risks
This development could lead to increased sophistication in phishing tactics, challenging existing cybersecurity defenses and requiring adaptation by security professionals.
- Political / Geopolitical: Limited direct implications, but potential for increased regulatory scrutiny on cybersecurity practices.
- Security / Counter-Terrorism: Increased operational complexity in detecting and mitigating phishing threats, potentially diverting resources from other security priorities.
- Cyber / Information Space: Potential proliferation of IPv6-mapped IPv4 techniques across various cyber threat actors, complicating the information security landscape.
- Economic / Social: Potential financial losses for individuals and organizations, leading to decreased trust in digital communications and online services.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of phishing campaigns using IPv6-mapped IPv4 addresses; Educate users on identifying phishing attempts; Coordinate with cybersecurity firms to update detection algorithms.
- Medium-Term Posture (1–12 months): Develop partnerships with tech companies to improve IPv6-related security measures; Invest in research to understand and counteract new phishing techniques; Strengthen public awareness campaigns.
- Scenario Outlook:
- Best: Security systems adapt quickly, reducing the effectiveness of IPv6 obfuscation.
- Worst: Widespread adoption of IPv6 techniques by various threat actors, leading to increased phishing success rates.
- Most-Likely: Gradual adaptation by security systems with intermittent success in phishing campaigns.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, phishing, IPv6, information security, threat detection, personal data protection, cybercrime
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us