CISA mandates urgent patch for n8n RCE vulnerability amid active exploitation threats
Published on: 2026-03-11
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
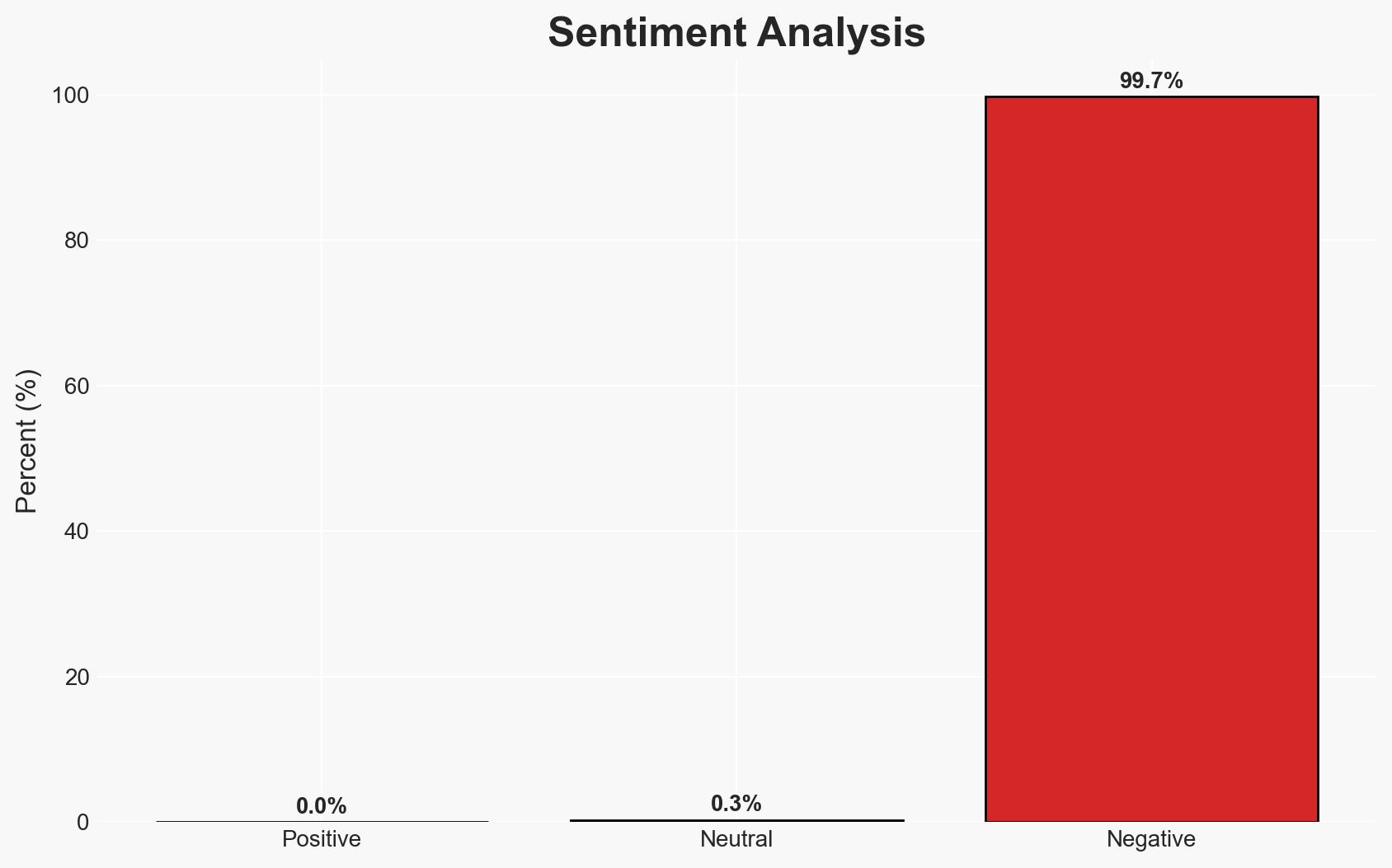
Intelligence Report: CISA orders feds to patch n8n RCE flaw exploited in attacks
1. BLUF (Bottom Line Up Front)
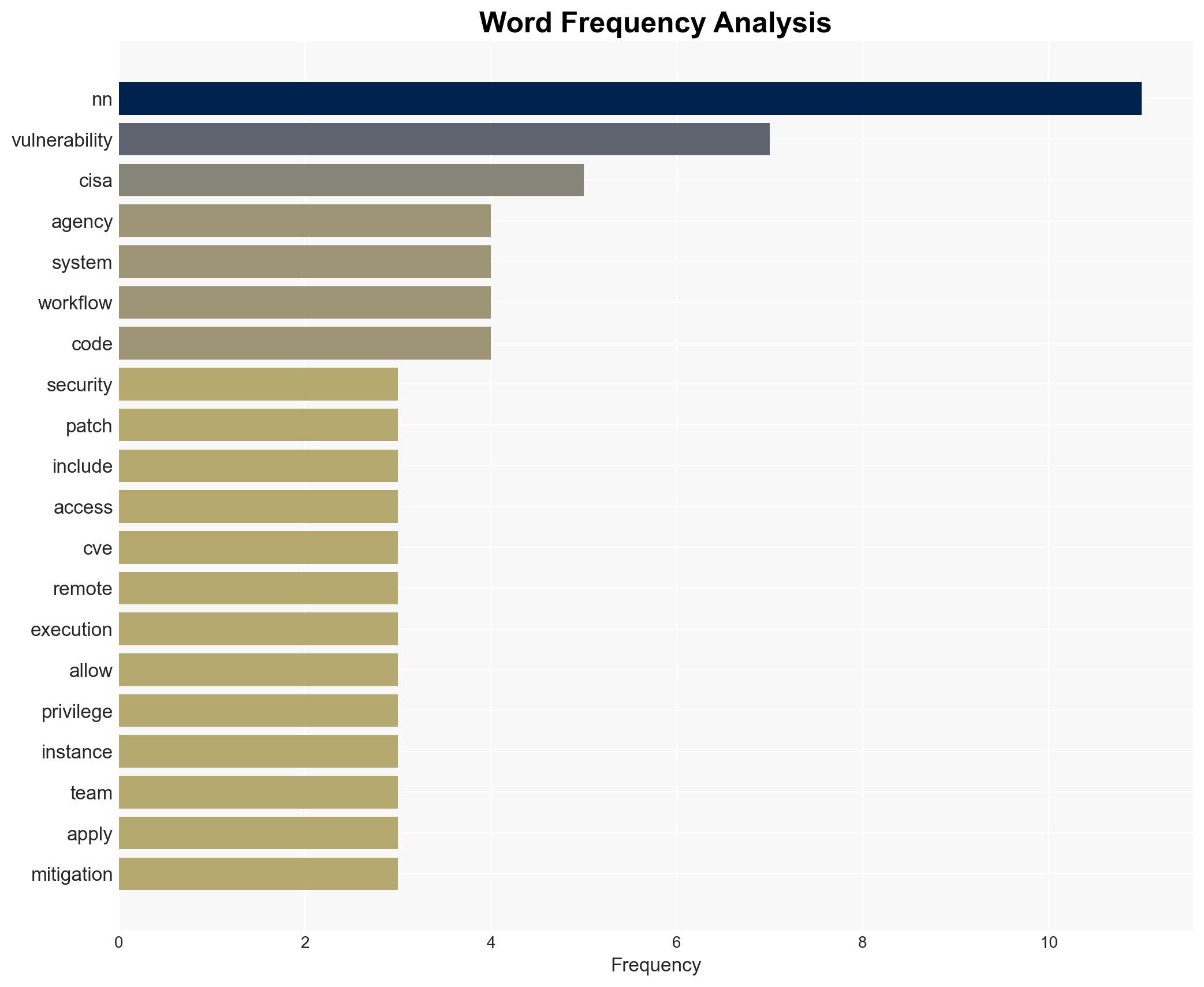
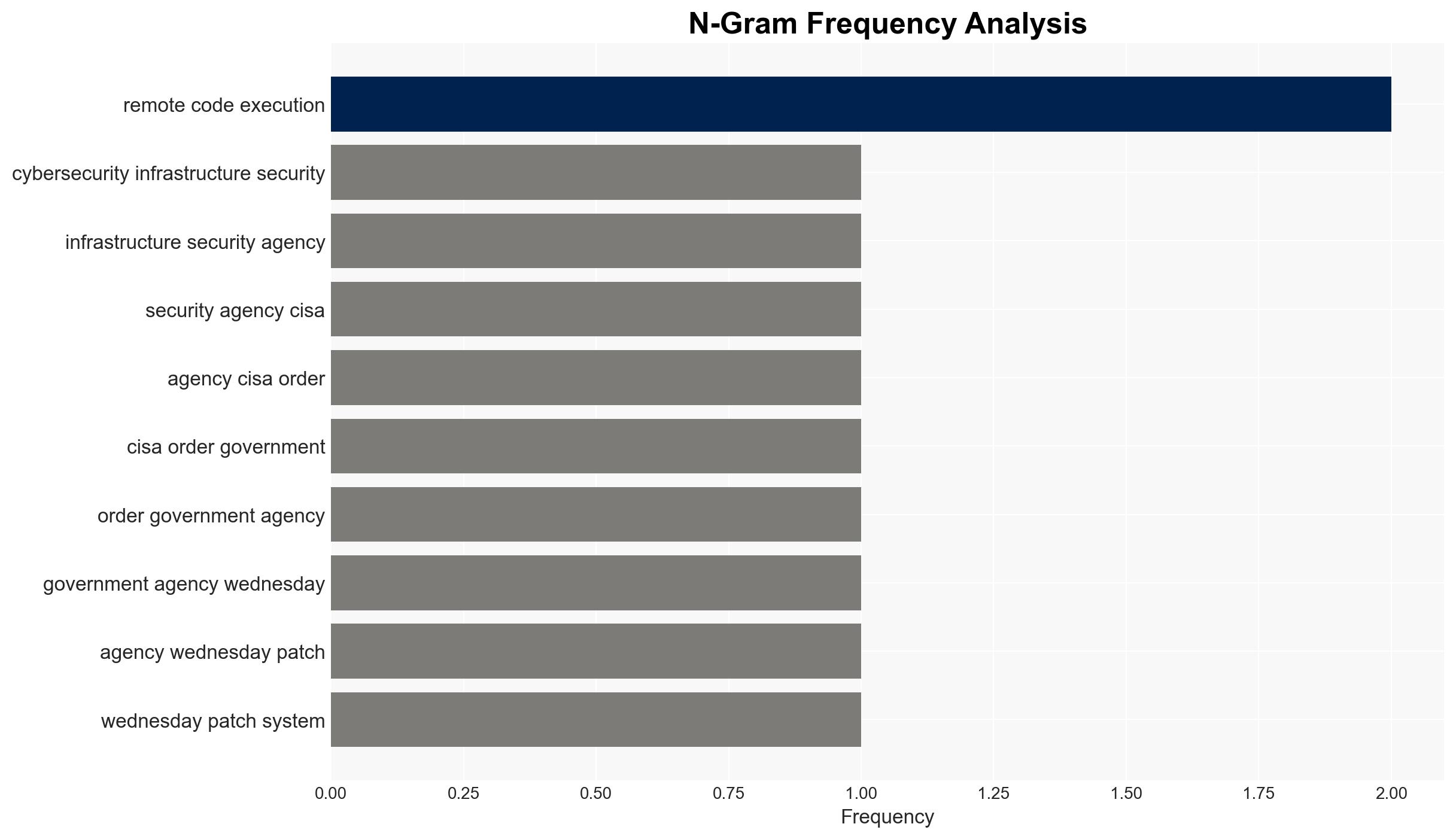
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has mandated federal agencies to patch a critical vulnerability in the n8n platform due to its active exploitation. This vulnerability poses significant risks to sensitive data and system integrity. The most likely hypothesis is that threat actors are leveraging this flaw for unauthorized access and data manipulation. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: Threat actors are actively exploiting the n8n vulnerability to gain unauthorized access to sensitive data and execute arbitrary code. This is supported by CISA’s urgent directive and the vulnerability’s inclusion in the Known Exploited Vulnerabilities catalog. However, specific attribution to particular threat actors remains uncertain.
- Hypothesis B: The vulnerability is being exploited primarily for reconnaissance and testing by security researchers, rather than malicious actors. This is less supported given the urgency of CISA’s directive and the nature of the vulnerability, which allows for significant system compromise.
- Assessment: Hypothesis A is currently better supported due to the active exploitation reports and the critical nature of the vulnerability. Indicators such as increased unauthorized access attempts or data breaches could further validate this hypothesis.
3. Key Assumptions and Red Flags
- Assumptions: The vulnerability is widespread across federal systems; threat actors are motivated by data theft or system disruption; patching will effectively mitigate the threat.
- Information Gaps: Specific threat actor attribution and their objectives; the extent of exploitation across non-federal systems.
- Bias & Deception Risks: Potential over-reliance on vendor-provided information; confirmation bias towards assuming all exploitation is malicious.
4. Implications and Strategic Risks
The exploitation of the n8n vulnerability could lead to significant data breaches and operational disruptions if not promptly addressed. This development may influence broader cybersecurity postures and policies.
- Political / Geopolitical: Increased pressure on government agencies to enhance cybersecurity measures could lead to policy changes or international cooperation efforts.
- Security / Counter-Terrorism: Potential for increased cyber-attacks targeting critical infrastructure, necessitating heightened vigilance and response capabilities.
- Cyber / Information Space: Escalation in cyber threat activity, with potential misinformation campaigns exploiting perceived vulnerabilities.
- Economic / Social: Potential economic impacts due to data breaches or operational downtime, affecting public trust in digital systems.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Agencies should prioritize patching the vulnerability, monitor for signs of exploitation, and implement temporary mitigations where necessary.
- Medium-Term Posture (1–12 months): Develop resilience measures, enhance threat intelligence sharing, and conduct regular security audits to prevent future vulnerabilities.
- Scenario Outlook: Best: Vulnerability patched with minimal impact; Worst: Widespread data breaches and operational disruptions; Most-Likely: Gradual mitigation with some isolated incidents.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
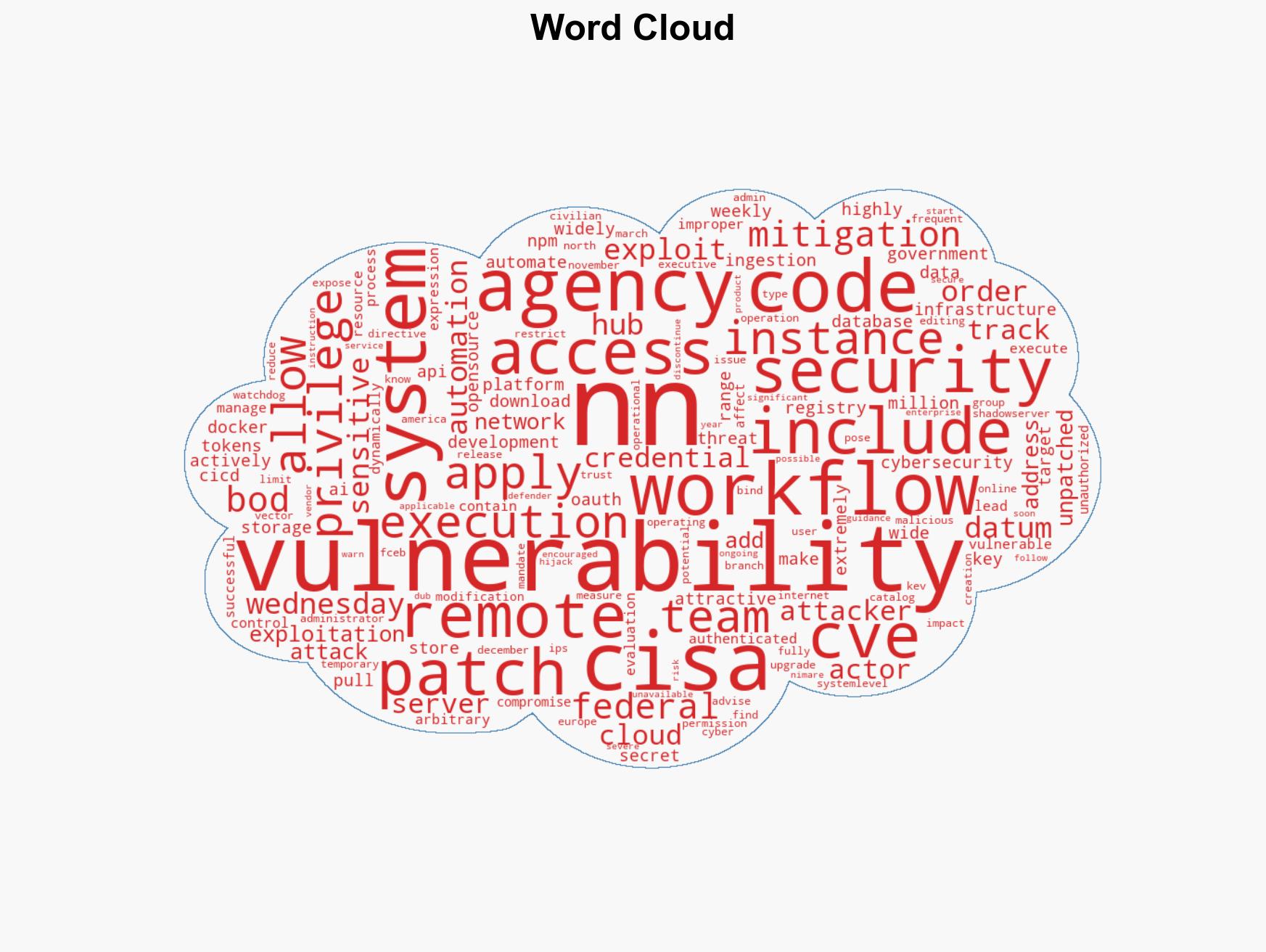
cybersecurity, vulnerability management, federal agencies, data protection, cyber threats, information security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us