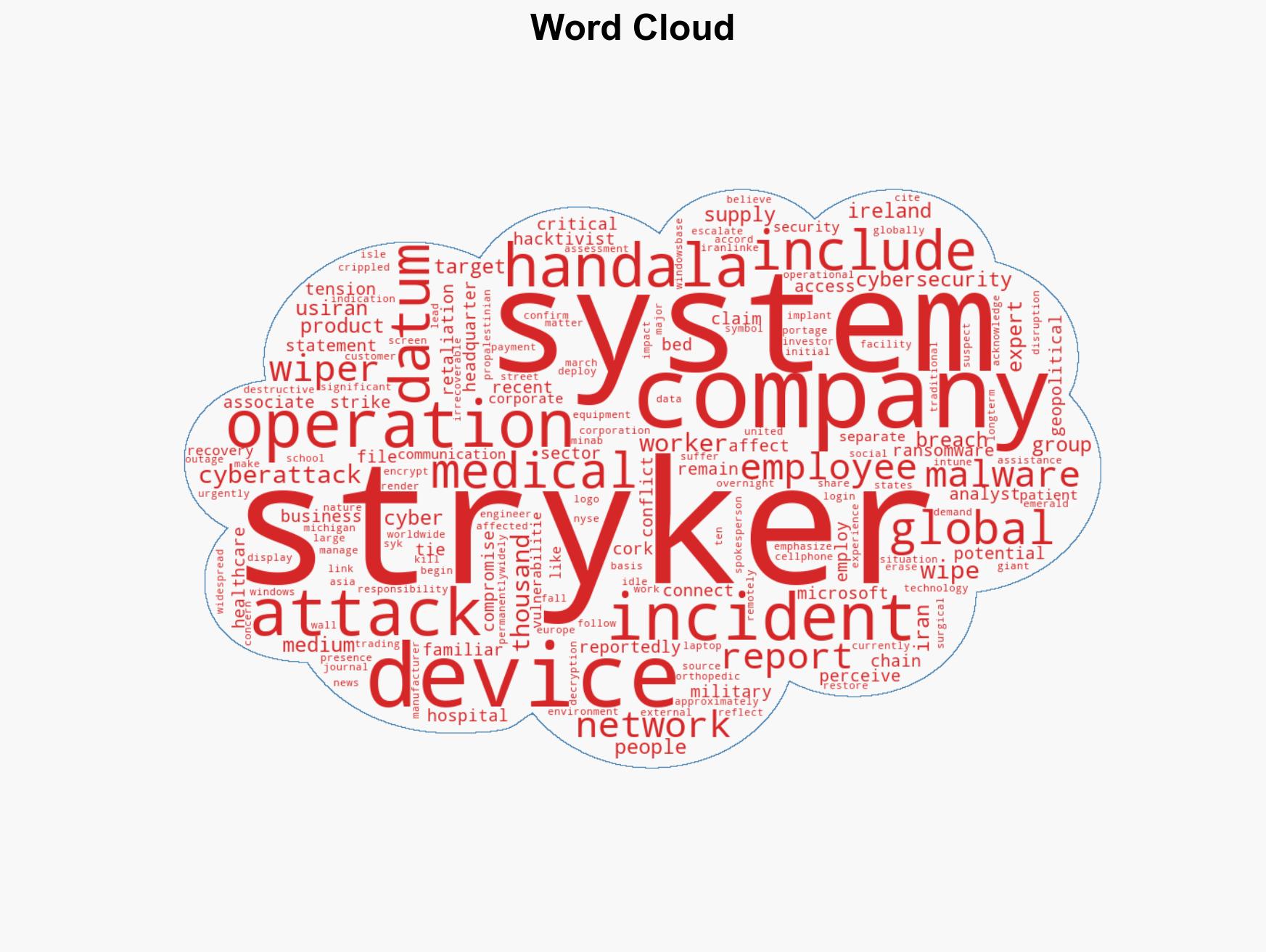
Stryker Corporation Faces Major Cyberattack Linked to Iranian Hacktivists Amid Rising U.S.-Iran Tensions
Published on: 2026-03-11
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: What is Stryker Cyberattack Stryker Corporation Hit by Suspected Iran-Linked Cyberattack
1. BLUF (Bottom Line Up Front)
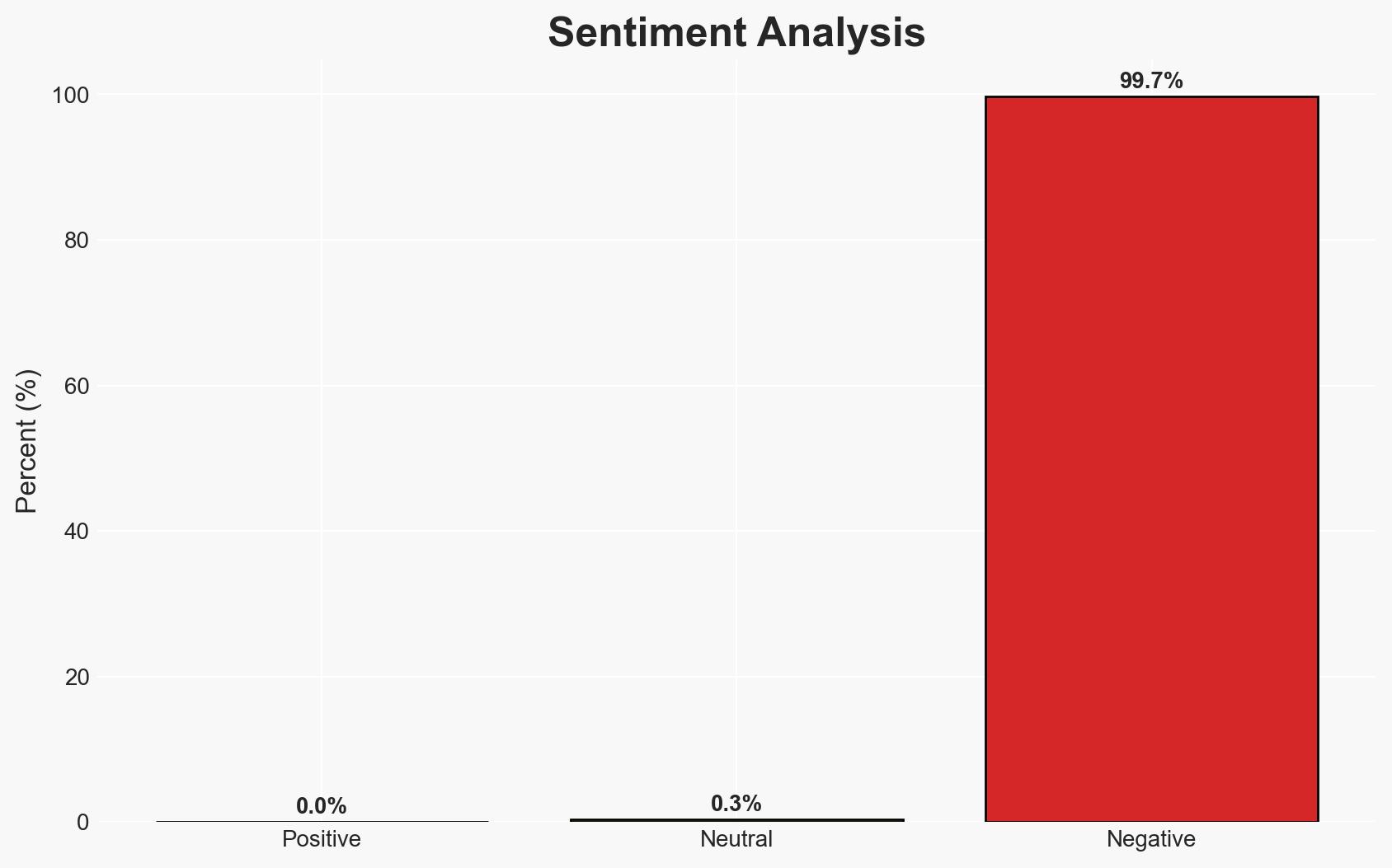
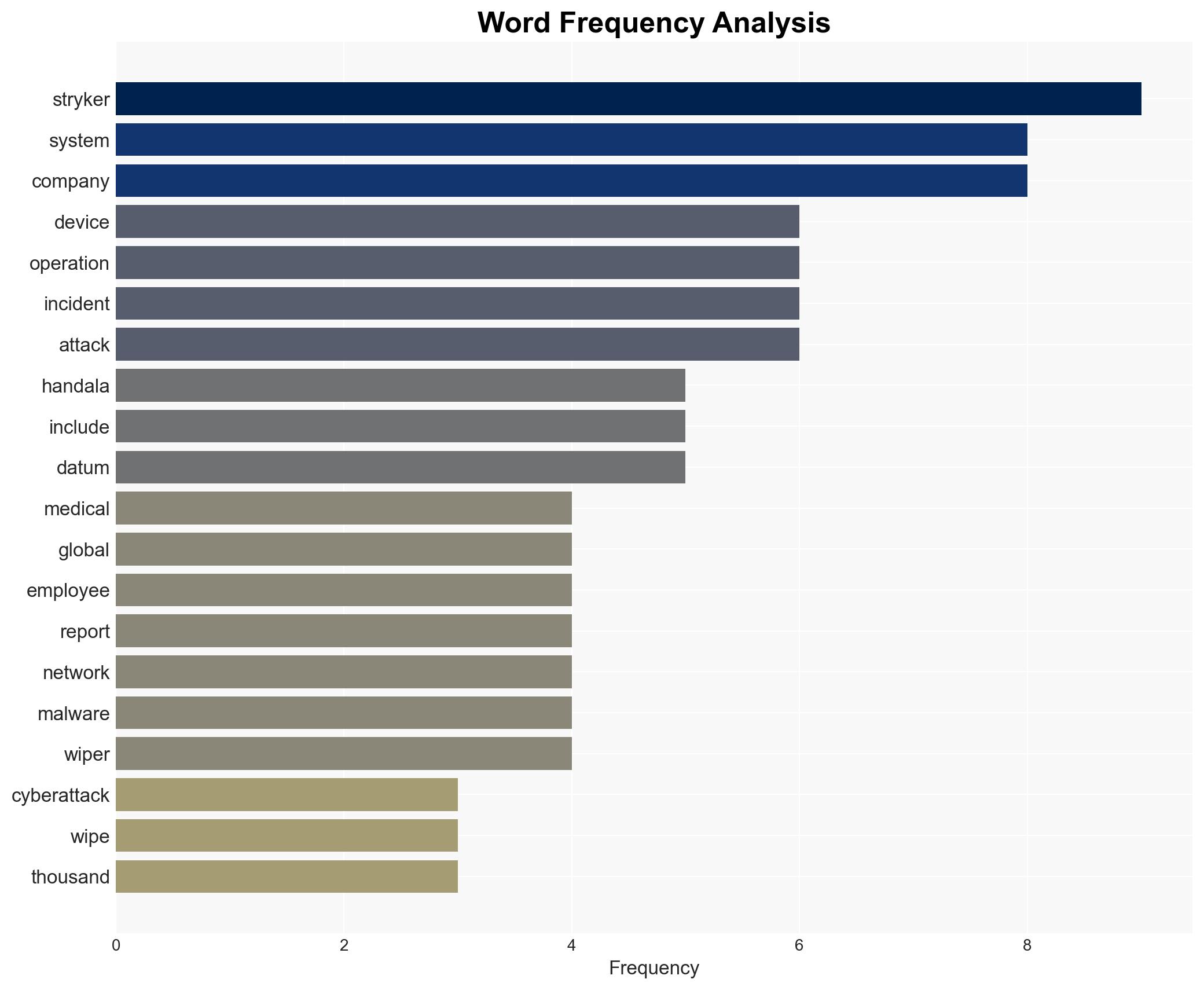
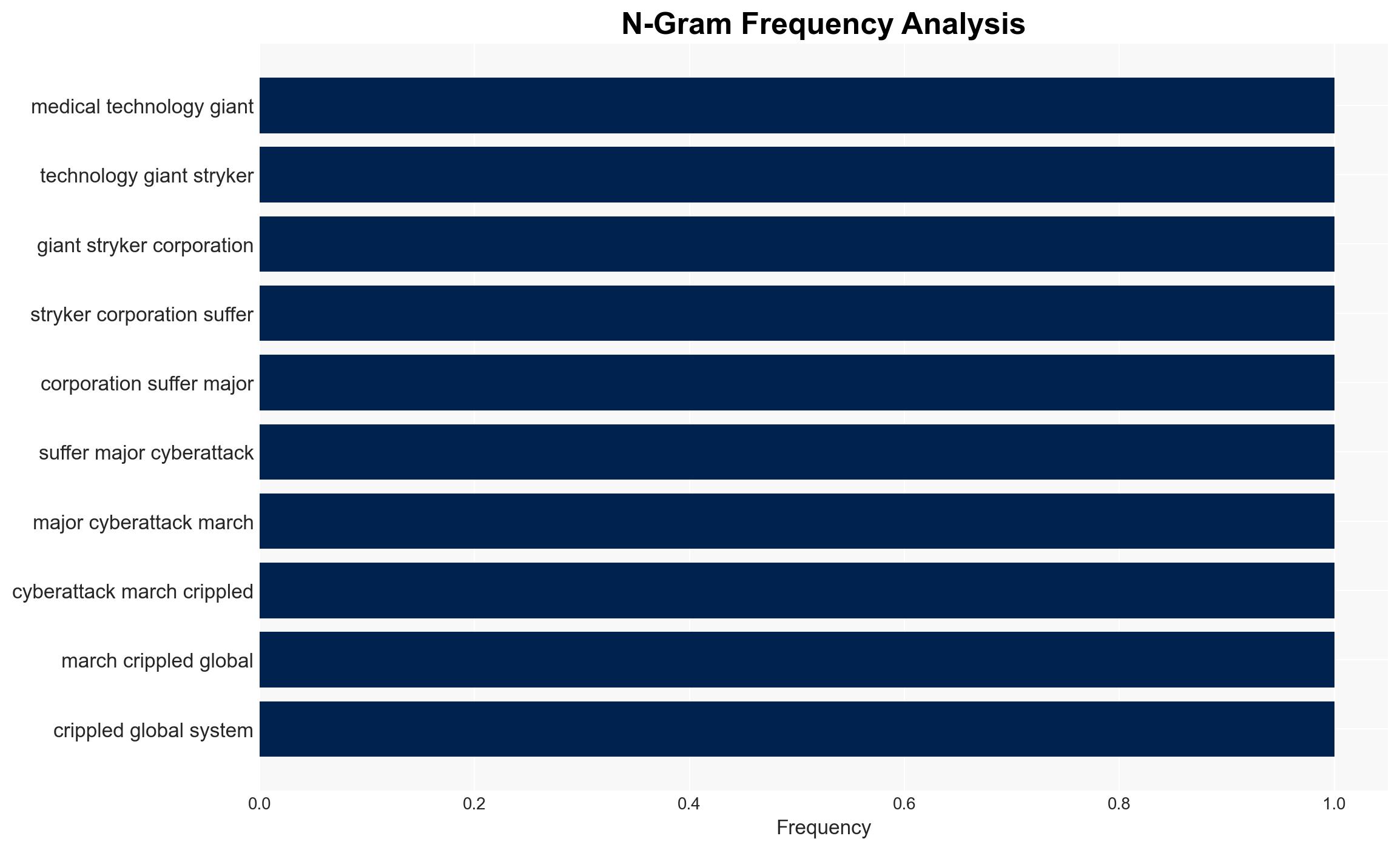
The cyberattack on Stryker Corporation, attributed to the pro-Palestinian hacktivist group Handala, likely linked to Iran, resulted in significant operational disruptions. This incident reflects a potential escalation in retaliatory cyber operations amid U.S.-Iran tensions. The overall confidence level in this assessment is moderate, given the current evidence and attribution claims.
2. Competing Hypotheses
- Hypothesis A: The attack was conducted by Handala, with Iranian support, as retaliation for U.S. military actions. This is supported by Handala’s claim of responsibility and the geopolitical context. However, the lack of direct evidence linking Iran to the attack introduces uncertainty.
- Hypothesis B: The attack was independently executed by Handala without state support, motivated purely by ideological alignment with pro-Palestinian causes. This is contradicted by the sophistication of the attack, which suggests potential state-level resources or expertise.
- Assessment: Hypothesis A is currently better supported due to the alignment of the attack with Iranian geopolitical interests and Handala’s historical ties to Iran. Indicators such as further cyber operations linked to Iranian interests could reinforce this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Handala has operational capabilities to execute sophisticated cyberattacks; Iran supports groups aligned with its geopolitical interests; U.S.-Iran tensions influence cyber threat levels.
- Information Gaps: Direct evidence of Iranian involvement; detailed technical analysis of the malware used; comprehensive assessment of data exfiltration impact.
- Bias & Deception Risks: Attribution bias due to geopolitical tensions; potential misinformation from Handala’s public claims; over-reliance on open-source intelligence without corroboration.
4. Implications and Strategic Risks
The Stryker cyberattack may signal a broader trend of retaliatory cyber operations linked to geopolitical conflicts, potentially escalating U.S.-Iran tensions.
- Political / Geopolitical: Increased cyber conflict could exacerbate U.S.-Iran relations, leading to further diplomatic strains or retaliatory actions.
- Security / Counter-Terrorism: Potential for similar attacks on other U.S. or allied entities, raising the threat level for critical infrastructure.
- Cyber / Information Space: Heightened risk of cyber operations targeting sectors perceived as vulnerable or symbolically significant.
- Economic / Social: Disruption to Stryker’s operations may impact healthcare supply chains, investor confidence, and employee morale.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of cyber threats linked to geopolitical tensions; collaborate with cybersecurity firms for threat intelligence sharing; reinforce Stryker’s IT security posture.
- Medium-Term Posture (1–12 months): Develop resilience measures against state-linked cyber threats; engage in international cyber diplomacy to mitigate escalation risks; invest in advanced threat detection capabilities.
- Scenario Outlook:
- Best: De-escalation of U.S.-Iran tensions reduces cyber threat levels.
- Worst: Escalation leads to widespread cyberattacks on critical infrastructure.
- Most-Likely: Continued sporadic cyber incidents with moderate impact, driven by geopolitical dynamics.
6. Key Individuals and Entities
- Handala (pro-Palestinian hacktivist group)
- Stryker Corporation (Medical technology company)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, Iran, hacktivism, geopolitical tensions, U.S.-Iran relations, cyber retaliation, critical infrastructure
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us