Stryker Corp Faces Global Disruption from Wiper Malware Attack: Recovery Prospects Under Scrutiny
Published on: 2026-03-11
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: What is wiper malware attack and will Stryker Corp be able to recover from cyberattack Here’s how did medical technology giant come under attack
1. BLUF (Bottom Line Up Front)
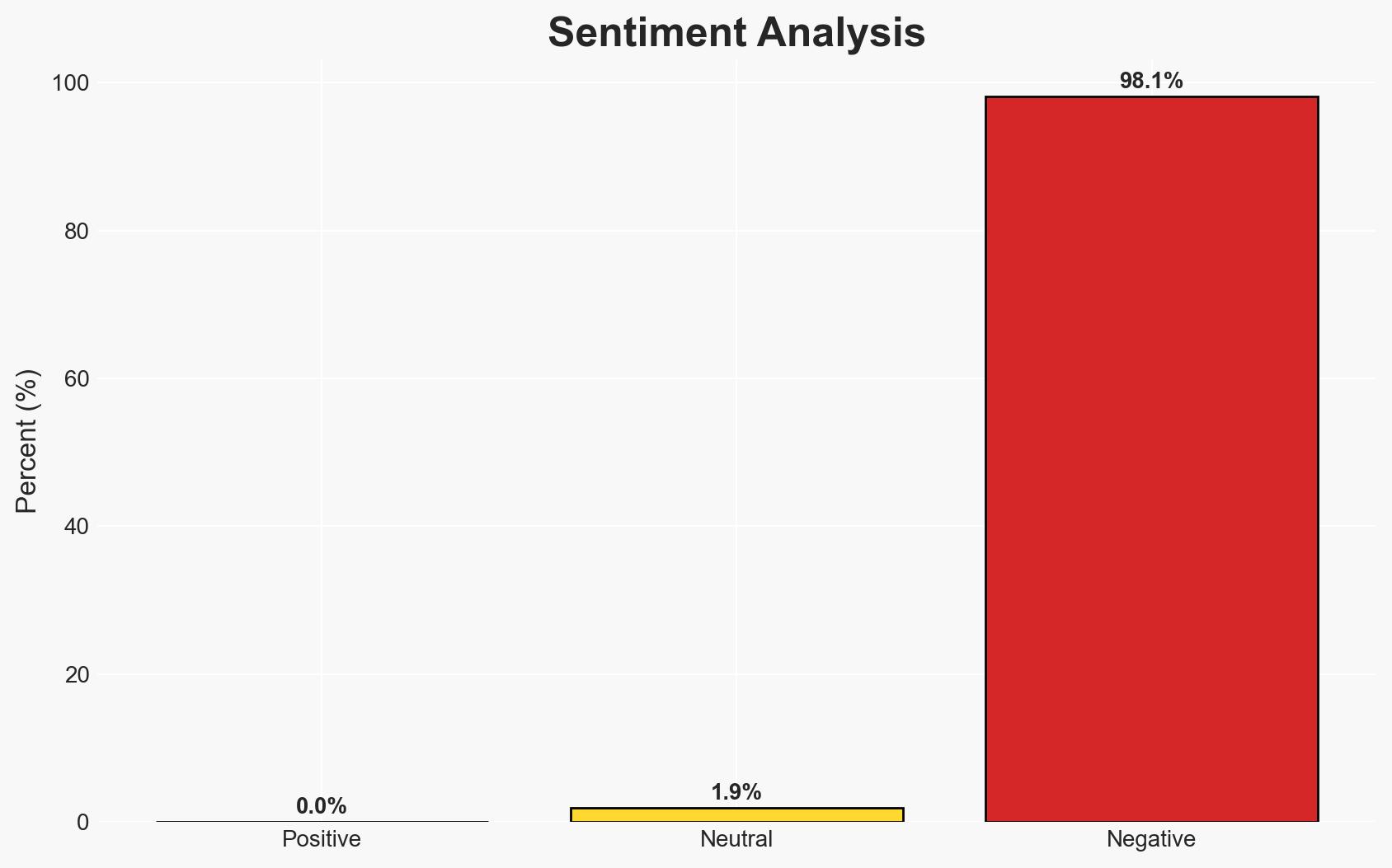
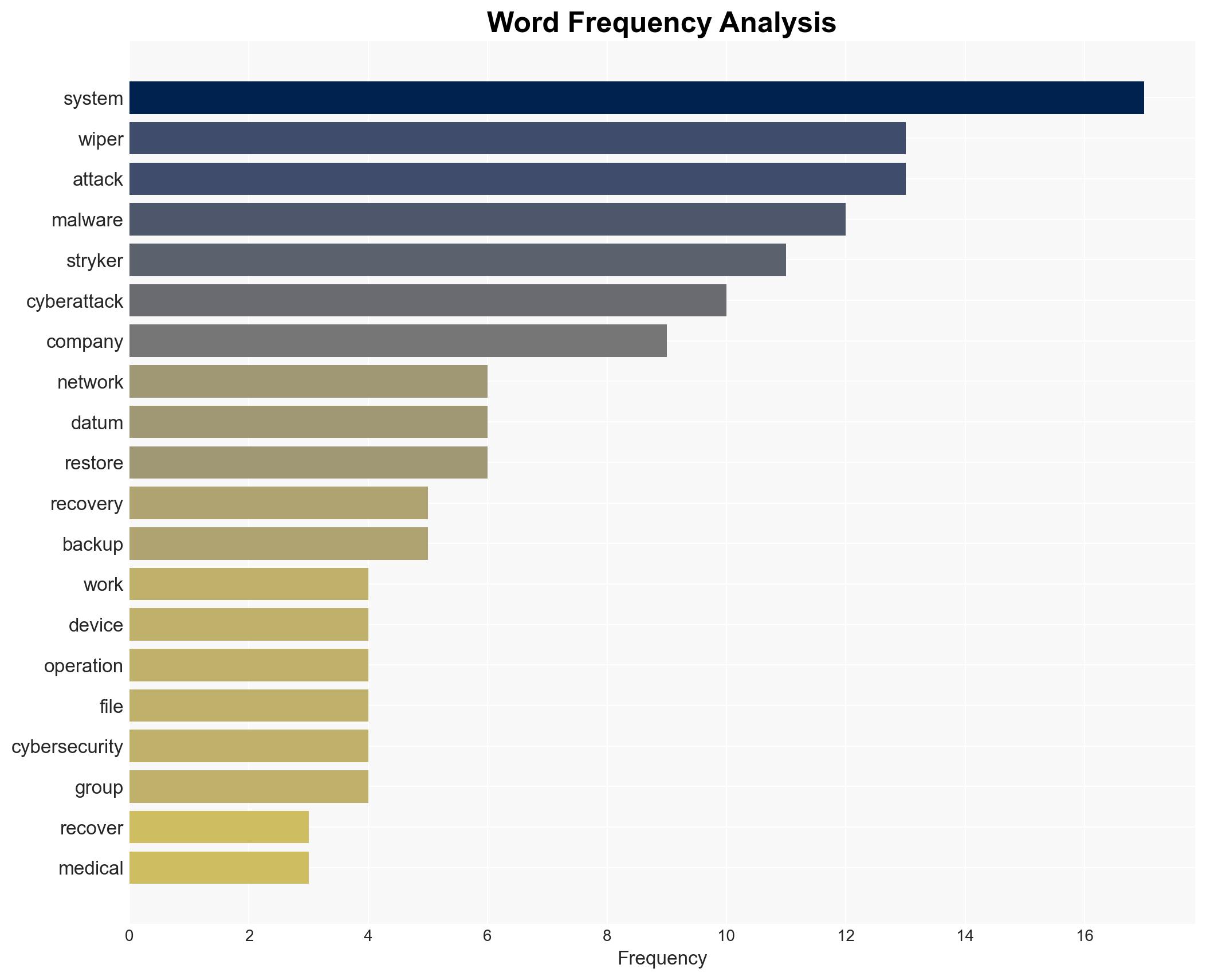
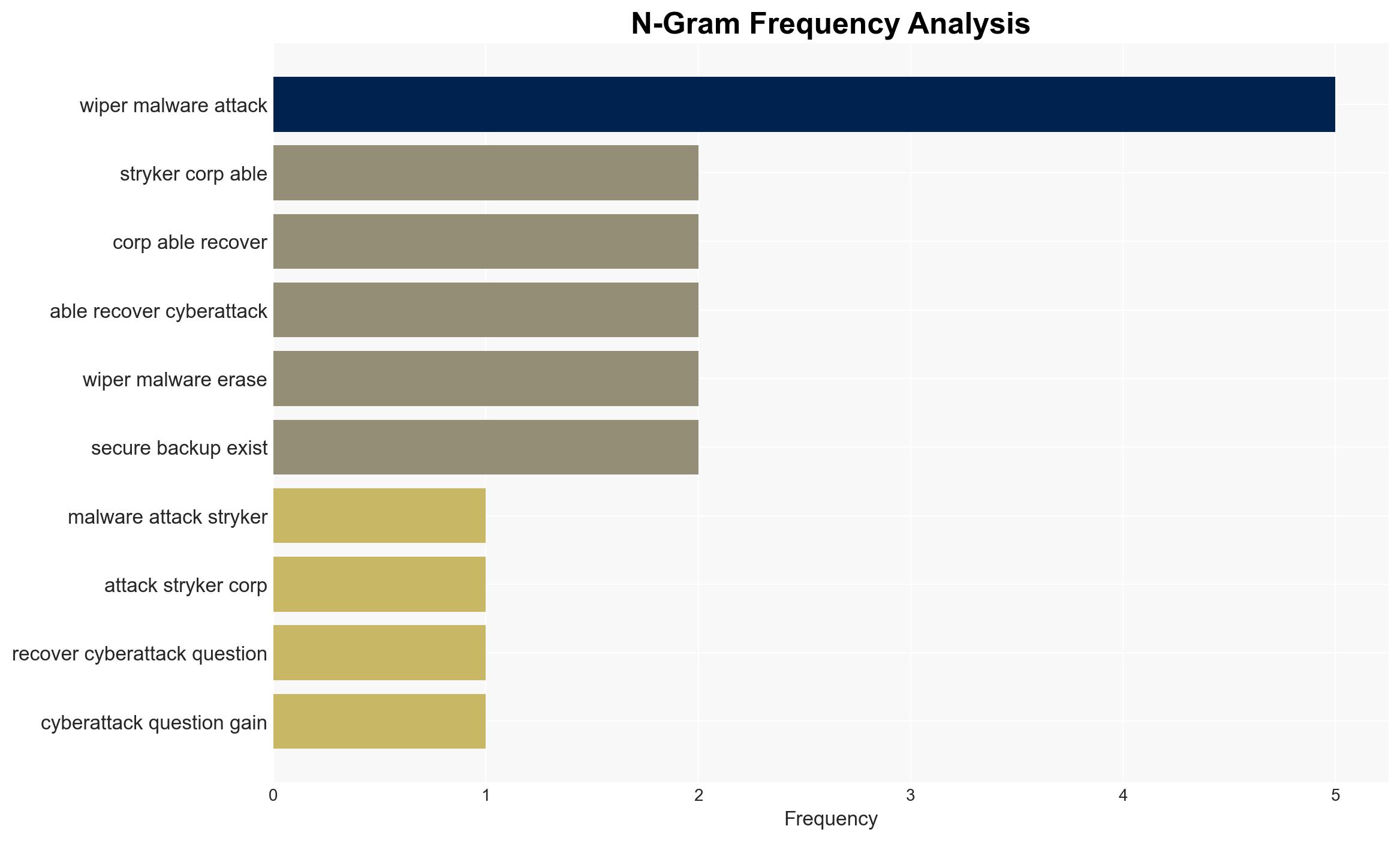
Stryker Corporation has suffered a significant cyberattack involving wiper malware, leading to a global network outage. The attack, claimed by the Handala hacker group, appears to be retaliation for a U.S. military action in Iran. The recovery of Stryker’s operations will depend on the availability of secure backups and the speed of system restoration. Current assessment supports the hypothesis of a politically motivated attack with moderate confidence.
2. Competing Hypotheses
- Hypothesis A: The attack on Stryker was a politically motivated operation by the Handala group in response to U.S. military actions. This is supported by the group’s claims and the geopolitical context. However, the true identity and motivations of Handala remain uncertain.
- Hypothesis B: The attack could be a financially motivated operation disguised as a political statement, possibly involving data theft for future ransom or sale. The claim of data extraction supports this, but the absence of a ransom demand contradicts it.
- Assessment: Hypothesis A is currently better supported due to the explicit political claims by Handala and the lack of financial demands typical of ransomware attacks. Indicators such as further geopolitical statements or similar attacks could reinforce this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The Handala group has the capability to execute such a sophisticated attack; the attack was indeed politically motivated; Stryker’s cybersecurity measures were insufficient to prevent the breach.
- Information Gaps: The exact method of network infiltration; the full extent of data loss or compromise; the authenticity and motivations of the Handala group.
- Bias & Deception Risks: Potential bias in attributing the attack solely based on Handala’s claims; risk of deception if the group is using false flag tactics to obscure true motivations.
4. Implications and Strategic Risks
This cyberattack could set a precedent for politically motivated cyber operations against private sector entities, potentially escalating geopolitical tensions.
- Political / Geopolitical: Potential escalation in cyber warfare tactics linked to geopolitical conflicts, particularly involving U.S. interests.
- Security / Counter-Terrorism: Increased threat to critical infrastructure from politically motivated cyber groups.
- Cyber / Information Space: Highlighted vulnerabilities in corporate cybersecurity, potential for copycat attacks.
- Economic / Social: Disruption in medical supply chains, potential impact on healthcare services globally.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of Stryker’s network for further breaches, collaborate with international cybersecurity agencies, and verify the integrity of backups.
- Medium-Term Posture (1–12 months): Strengthen cybersecurity protocols, develop partnerships for threat intelligence sharing, and conduct comprehensive security audits.
- Scenario Outlook:
- Best: Rapid recovery with minimal data loss, improved cybersecurity posture.
- Worst: Prolonged disruption with significant data compromise, leading to financial and reputational damage.
- Most-Likely: Gradual recovery with some data loss, increased focus on cybersecurity improvements.
6. Key Individuals and Entities
- Handala hacker group (claimed responsibility)
- Stryker Corporation (targeted entity)
- Not clearly identifiable from open sources in this snippet (specific individuals)
7. Thematic Tags
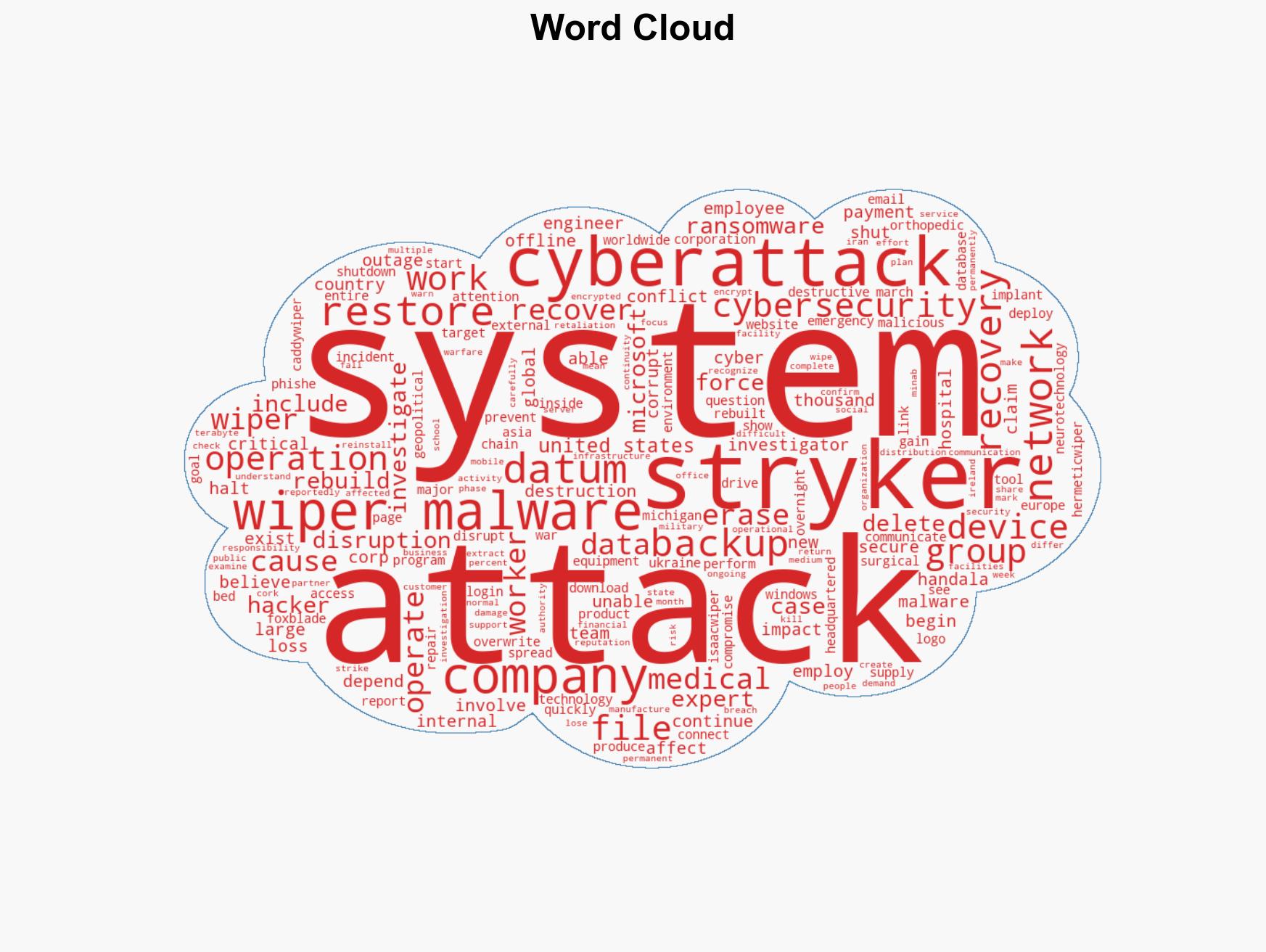
cybersecurity, wiper malware, geopolitical conflict, cyber warfare, healthcare disruption, data breach, cyber resilience
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us