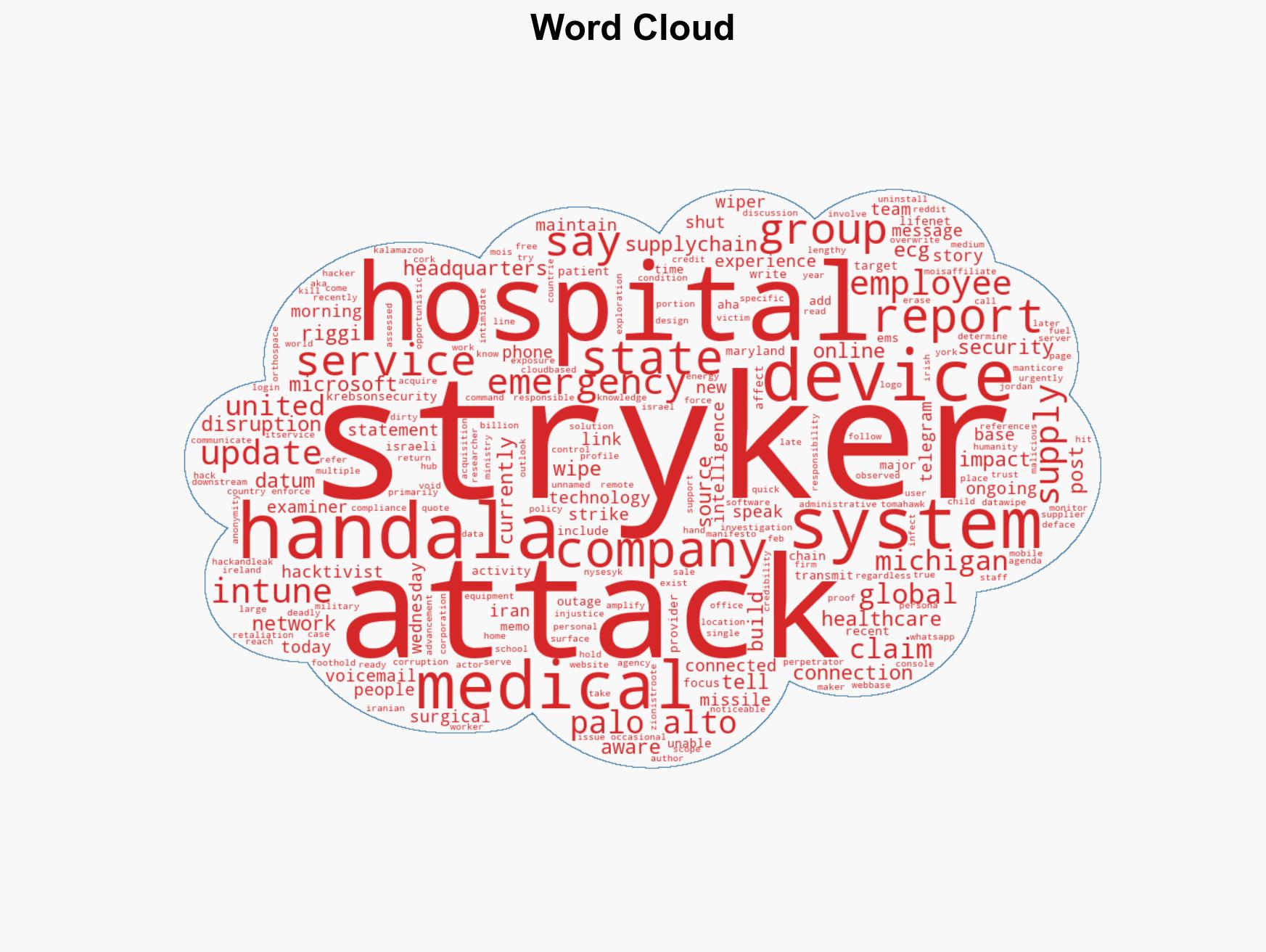
Iran-Linked Hackers Target Stryker in Data-Wiping Attack, Disrupting Operations Globally
Published on: 2026-03-11
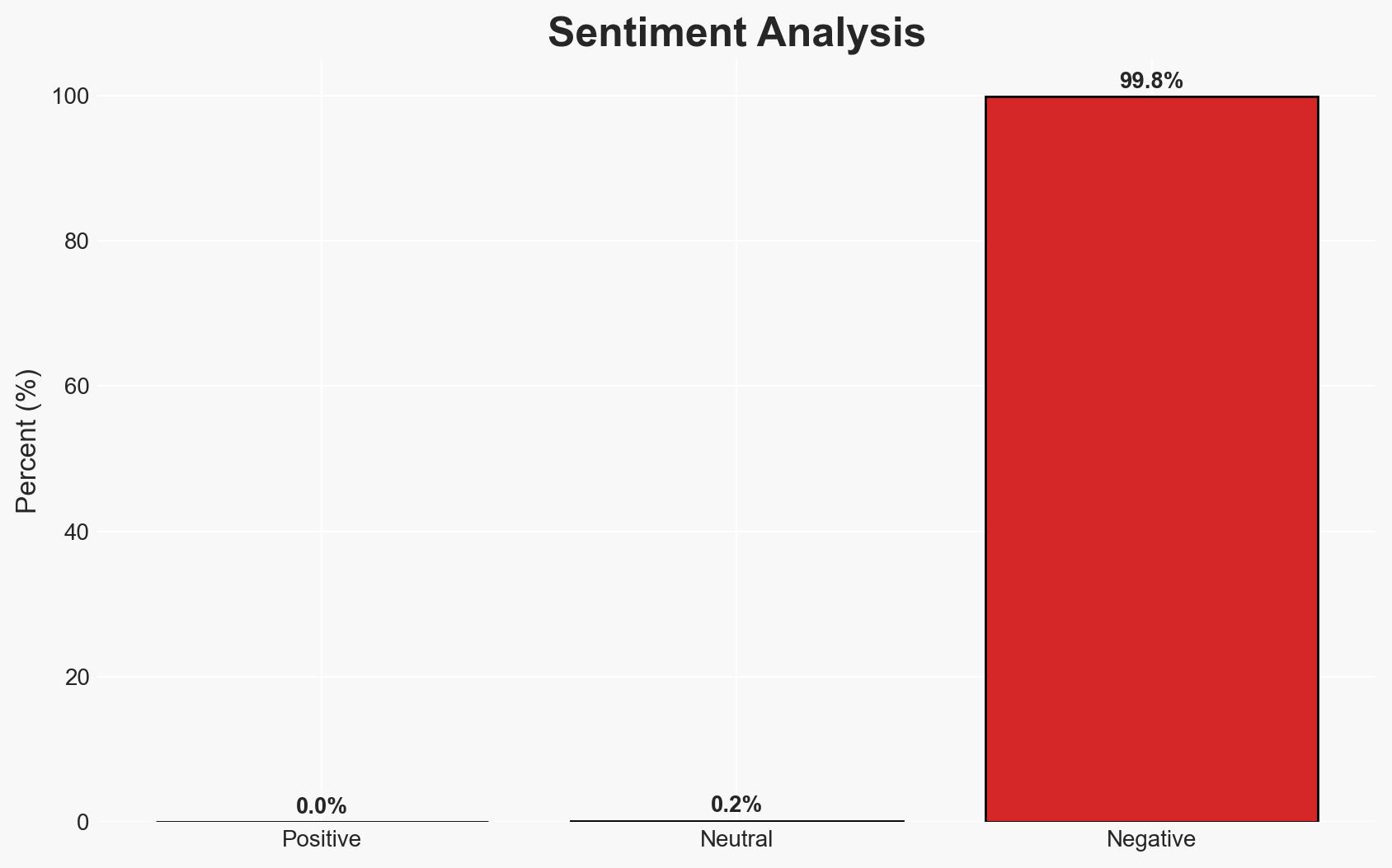
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Iran-Backed Hackers Claim Wiper Attack on Medtech Firm Stryker
1. BLUF (Bottom Line Up Front)
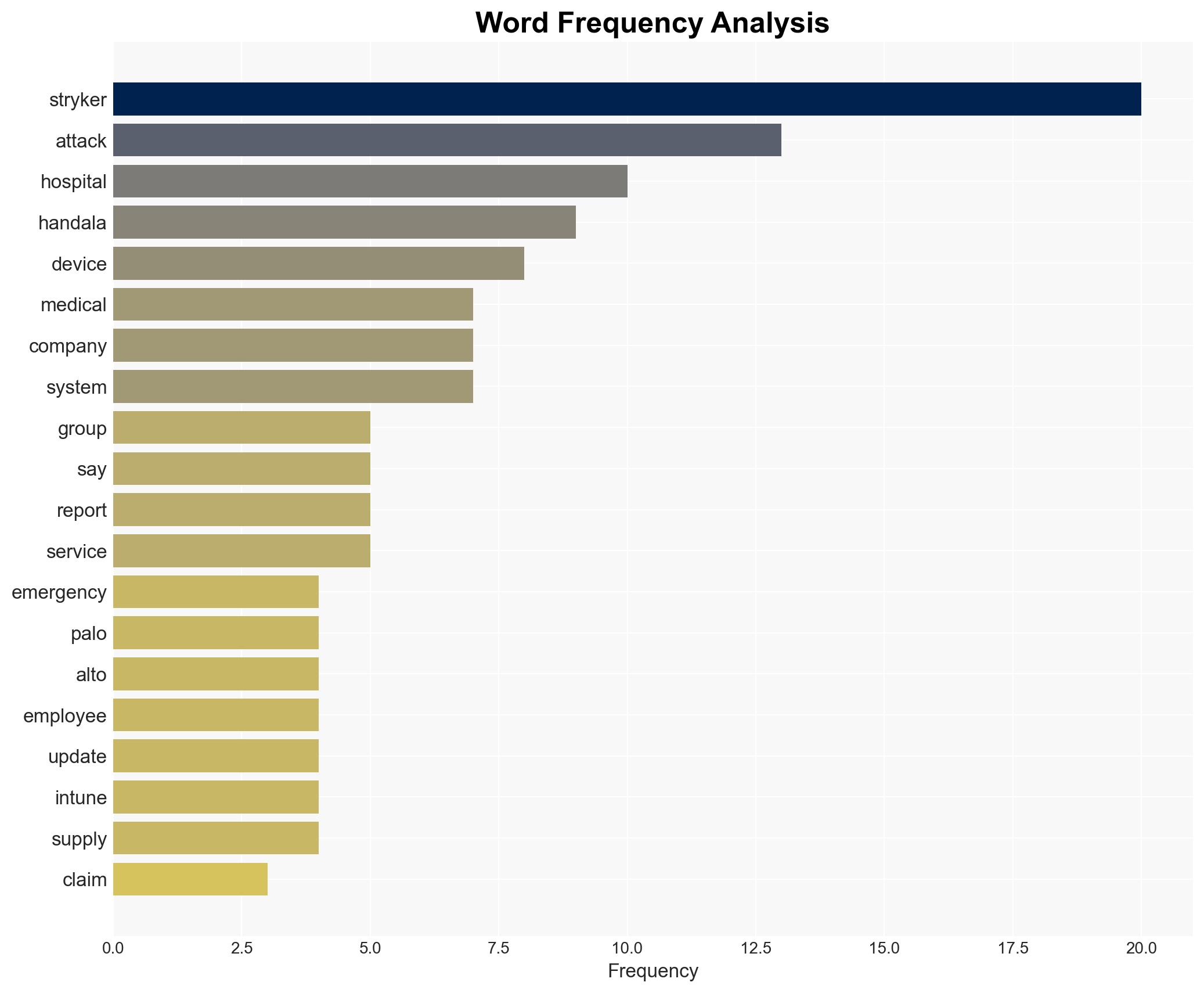
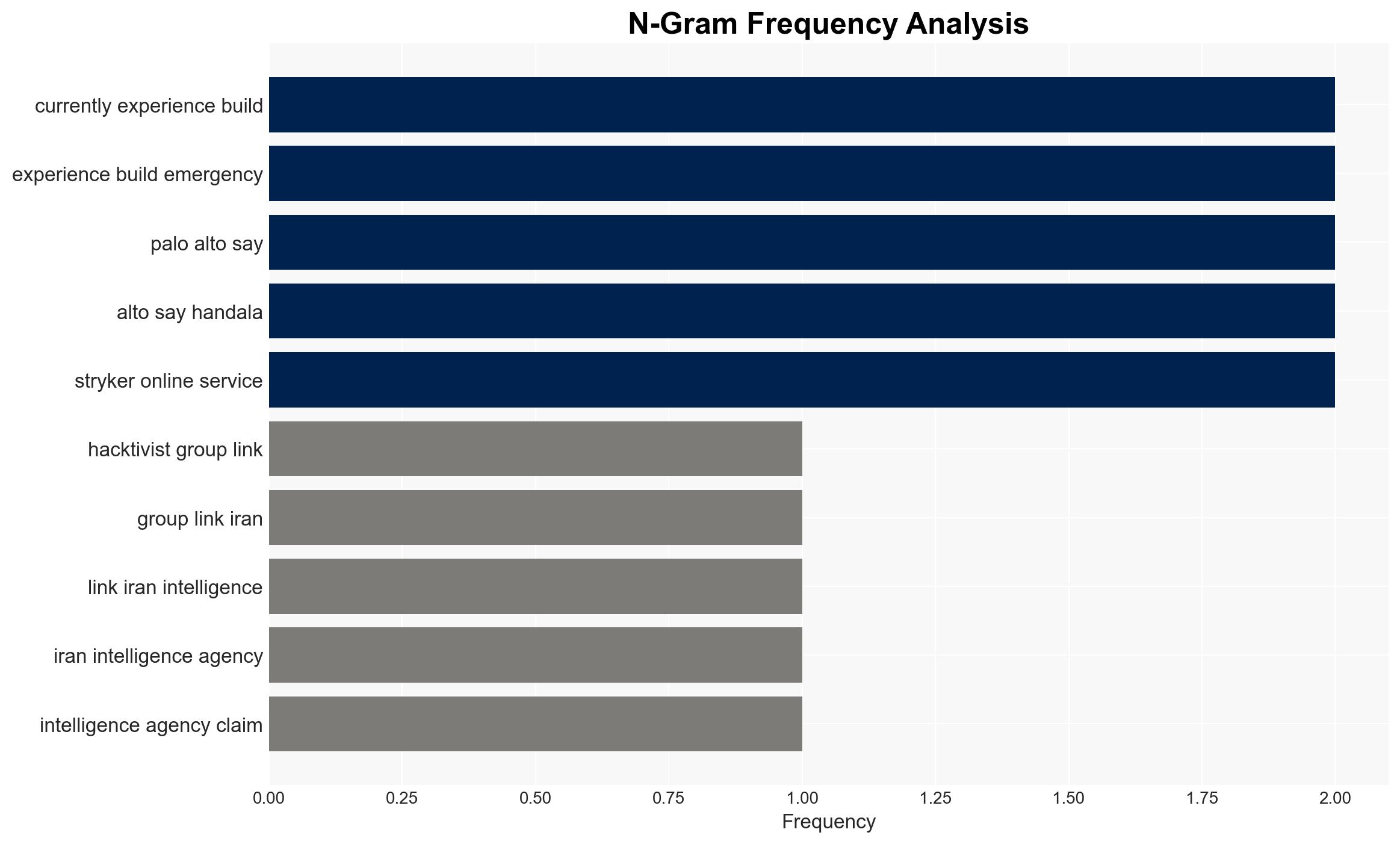
The hacktivist group Handala, linked to Iran’s Ministry of Intelligence and Security, has claimed responsibility for a significant wiper attack on Stryker, a major medical technology firm. This incident has disrupted operations globally, particularly affecting Stryker’s workforce in Ireland. The attack is reportedly in retaliation for a U.S. missile strike in Iran. Overall, there is moderate confidence in the attribution to Handala based on existing links to Iranian intelligence.
2. Competing Hypotheses
- Hypothesis A: Handala, an Iran-linked hacktivist group, executed the attack as retaliation for the U.S. missile strike. This is supported by their public claim and known affiliations with Iranian intelligence. However, the extent of the group’s capabilities and the full scope of Iranian state involvement remain uncertain.
- Hypothesis B: The attack was conducted by a non-state actor or a separate group using Handala as a cover to obscure their identity. This hypothesis is less supported due to the lack of evidence contradicting Handala’s claim and the group’s known history of similar activities.
- Assessment: Hypothesis A is currently better supported due to the direct claim by Handala and their established connections to Iranian intelligence. Key indicators that could shift this judgment include evidence of different malware origins or credible claims from other groups.
3. Key Assumptions and Red Flags
- Assumptions: The attack was technically feasible for Handala; the group has operational support from Iranian intelligence; the U.S. missile strike is the genuine motive.
- Information Gaps: Detailed forensic analysis of the malware used; confirmation of the extent of data compromised; clarity on the Iranian government’s direct involvement.
- Bias & Deception Risks: Potential bias in attributing the attack to Iran due to geopolitical tensions; possible deception by Handala to amplify their perceived capabilities.
4. Implications and Strategic Risks
This development could exacerbate geopolitical tensions between the U.S. and Iran, potentially leading to further cyber confrontations. The incident highlights vulnerabilities in critical infrastructure and the growing threat of state-linked cyber operations.
- Political / Geopolitical: Increased tensions between the U.S. and Iran, potential for retaliatory actions.
- Security / Counter-Terrorism: Heightened alert for further cyber-attacks on U.S. and allied assets.
- Cyber / Information Space: Potential for copycat attacks and increased cyber threat levels globally.
- Economic / Social: Disruption to Stryker’s operations could impact medical supply chains and economic stability in affected regions.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of Iranian-linked cyber activities, strengthen Stryker’s cybersecurity posture, and engage in diplomatic channels to mitigate escalation.
- Medium-Term Posture (1–12 months): Develop resilience measures for critical infrastructure, foster international cybersecurity partnerships, and invest in threat intelligence capabilities.
- Scenario Outlook: Best: Diplomatic resolution reduces tensions; Worst: Escalation leads to further cyber-attacks; Most-Likely: Continued low-level cyber skirmishes with periodic escalations.
6. Key Individuals and Entities
- Handala (a.k.a. Handala Hack Team)
- Void Manticore
- Stryker Corporation
- Iran’s Ministry of Intelligence and Security (MOIS)
- Palo Alto Networks
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, Iran, hacktivism, wiper attack, critical infrastructure, geopolitical tensions, cyber-espionage
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us