Massive Data Breach Exposes One Billion Sensitive Identity Records in 26 Countries, Including 203 Million in…
Published on: 2026-03-12
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: One Billion Identity Records Across 26 Countries Exposed in Data Leak
1. BLUF (Bottom Line Up Front)
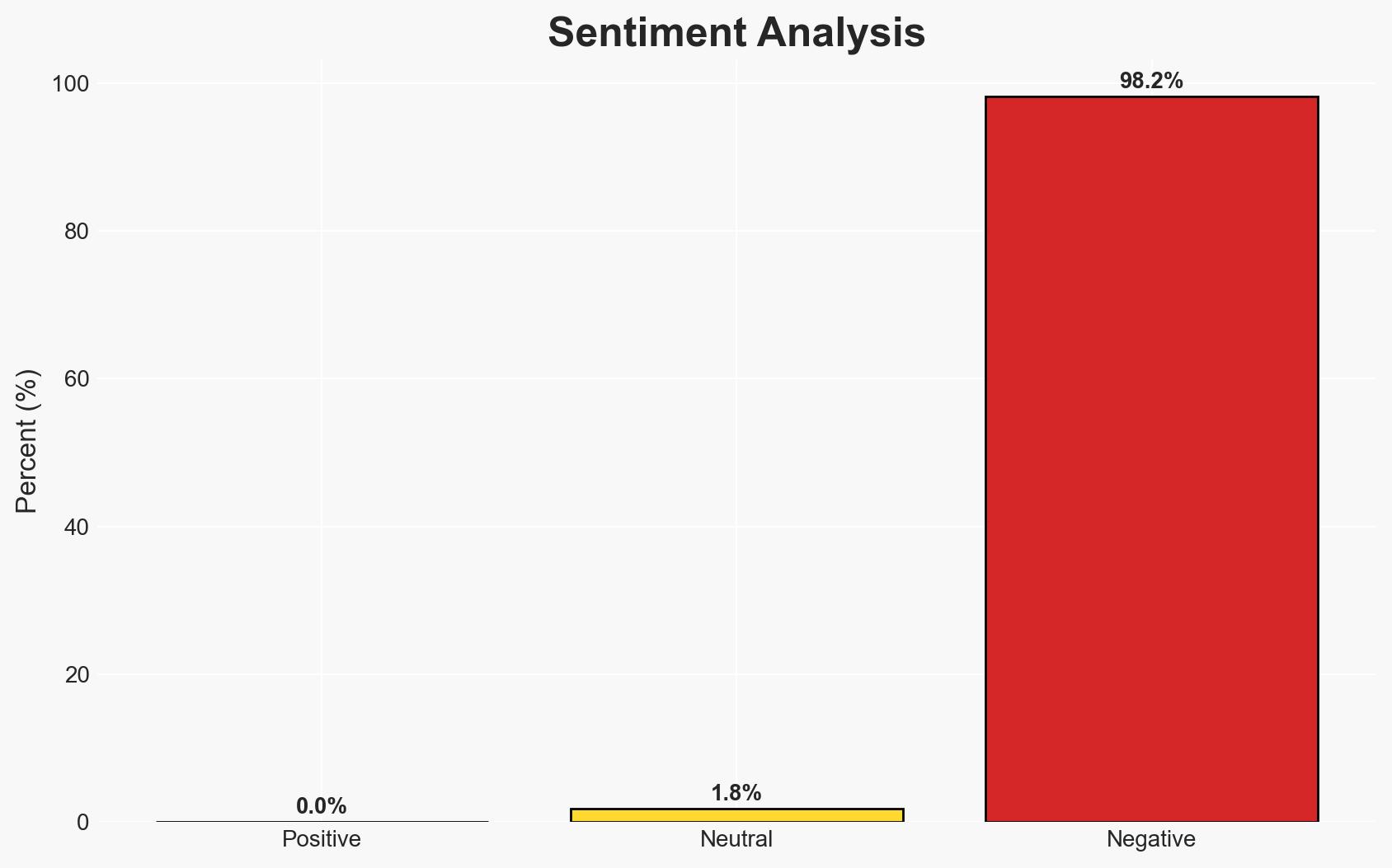
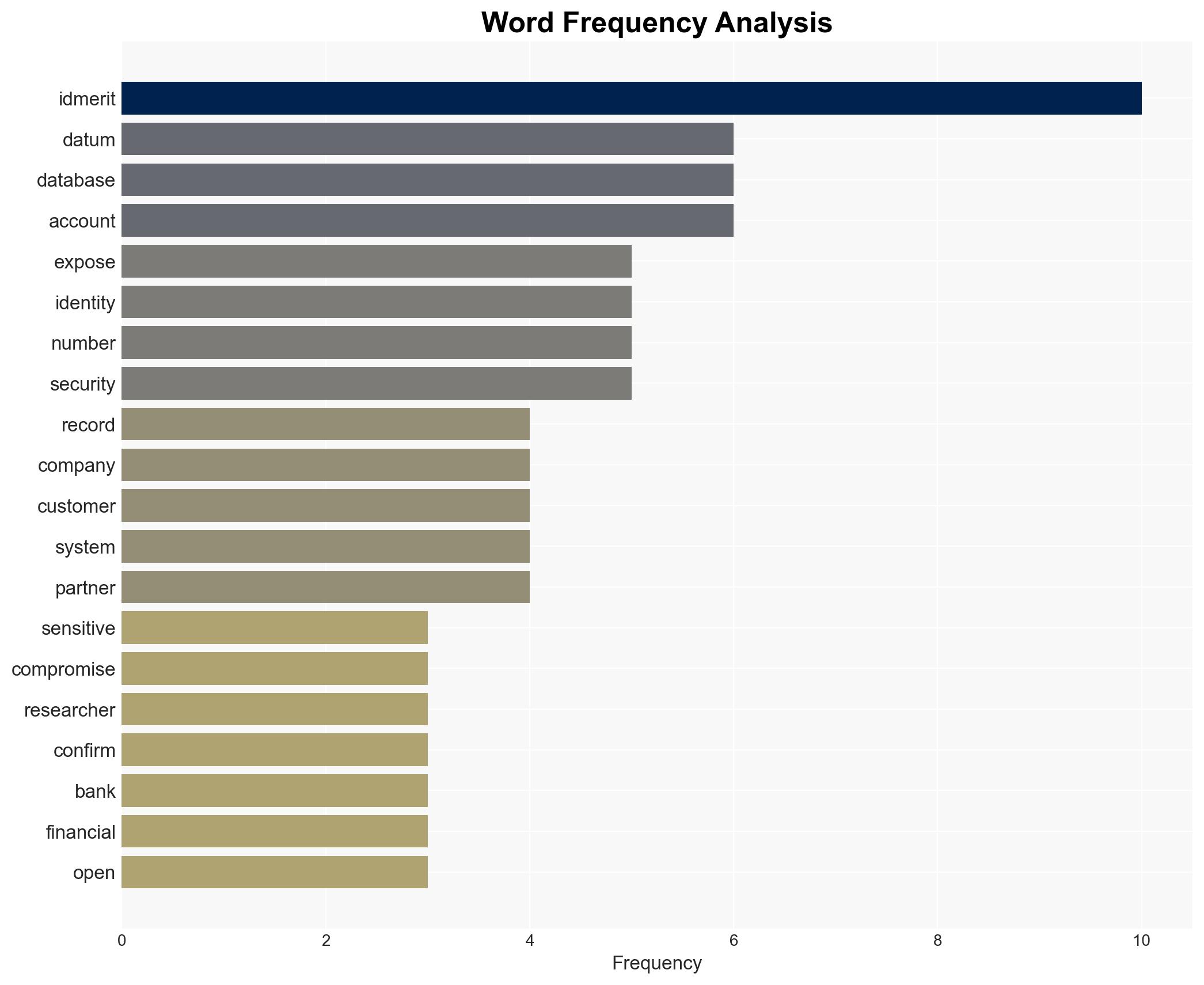
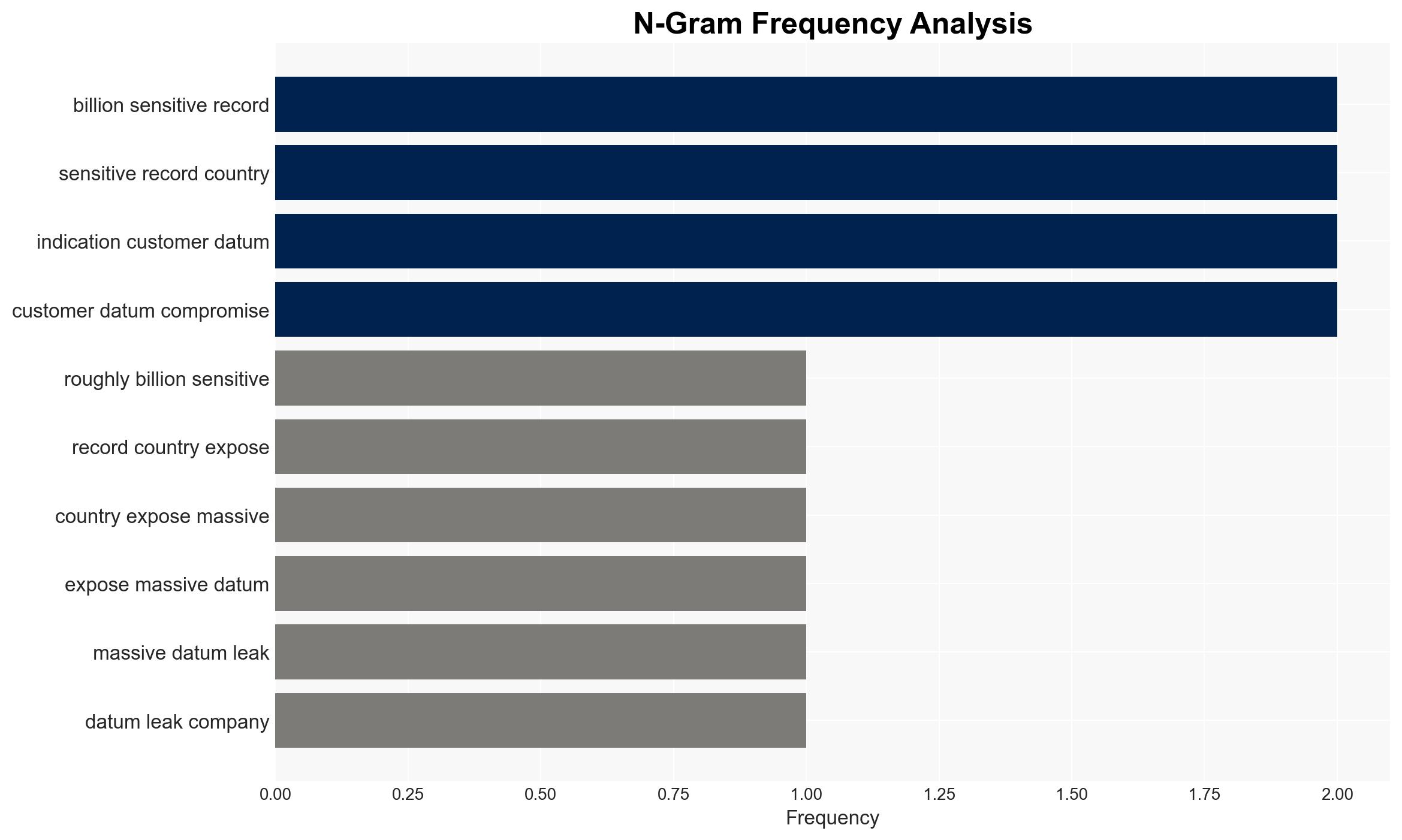
Approximately one billion sensitive records were exposed due to an unprotected database linked to IDMerit, affecting 26 countries. Despite IDMerit’s denial of data compromise, the exposure poses significant risks for identity theft and cybercrime. The most likely hypothesis is that the data was accessed by unauthorized entities, given the lack of database protection. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: The database was accessed by unauthorized parties due to its lack of password protection. This is supported by the nature of the exposure and the rapidity with which automated bots can exploit such vulnerabilities. However, IDMerit’s claim of no detected unauthorized access contradicts this.
- Hypothesis B: The database exposure did not result in unauthorized access, as claimed by IDMerit, possibly due to quick remediation efforts. This hypothesis is less supported due to the inherent risk and commonality of automated exploitation of exposed databases.
- Assessment: Hypothesis A is currently better supported due to the high likelihood of automated scanning and exploitation of unprotected databases. Indicators such as evidence of data misuse or further breaches could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The database was indeed accessible without protection; automated bots are actively scanning for such vulnerabilities; IDMerit’s internal review was comprehensive and accurate.
- Information Gaps: Specific details on whether any data was actually accessed or used maliciously remain unknown; the exact timeline and scope of the exposure are unclear.
- Bias & Deception Risks: IDMerit’s denial may reflect a bias to protect corporate reputation; there is a risk of underreporting the extent of the breach.
4. Implications and Strategic Risks
This data leak could lead to increased identity theft and cybercrime, affecting financial institutions and individuals globally. The incident highlights vulnerabilities in data protection practices.
- Political / Geopolitical: Potential for increased regulatory scrutiny and international cooperation on data protection standards.
- Security / Counter-Terrorism: Enhanced risk of identity-based fraud and exploitation by criminal networks.
- Cyber / Information Space: Likely increase in phishing and SIM-swap attacks leveraging exposed data.
- Economic / Social: Potential financial losses for individuals and institutions, erosion of trust in digital identity verification services.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a thorough forensic analysis of the incident; enhance monitoring of affected data; notify potentially impacted individuals and entities.
- Medium-Term Posture (1–12 months): Strengthen partnerships with cybersecurity firms; invest in advanced data protection technologies; review and update data handling policies.
- Scenario Outlook:
- Best: No significant misuse of data occurs; improved security measures prevent future incidents.
- Worst: Widespread identity theft and financial fraud; significant regulatory penalties and loss of business for IDMerit.
- Most-Likely: Some misuse of data leads to moderate financial and reputational impacts; gradual recovery with enhanced security measures.
6. Key Individuals and Entities
- IDMerit (global identity verification provider)
- Cybernews (cybersecurity news and research publication)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
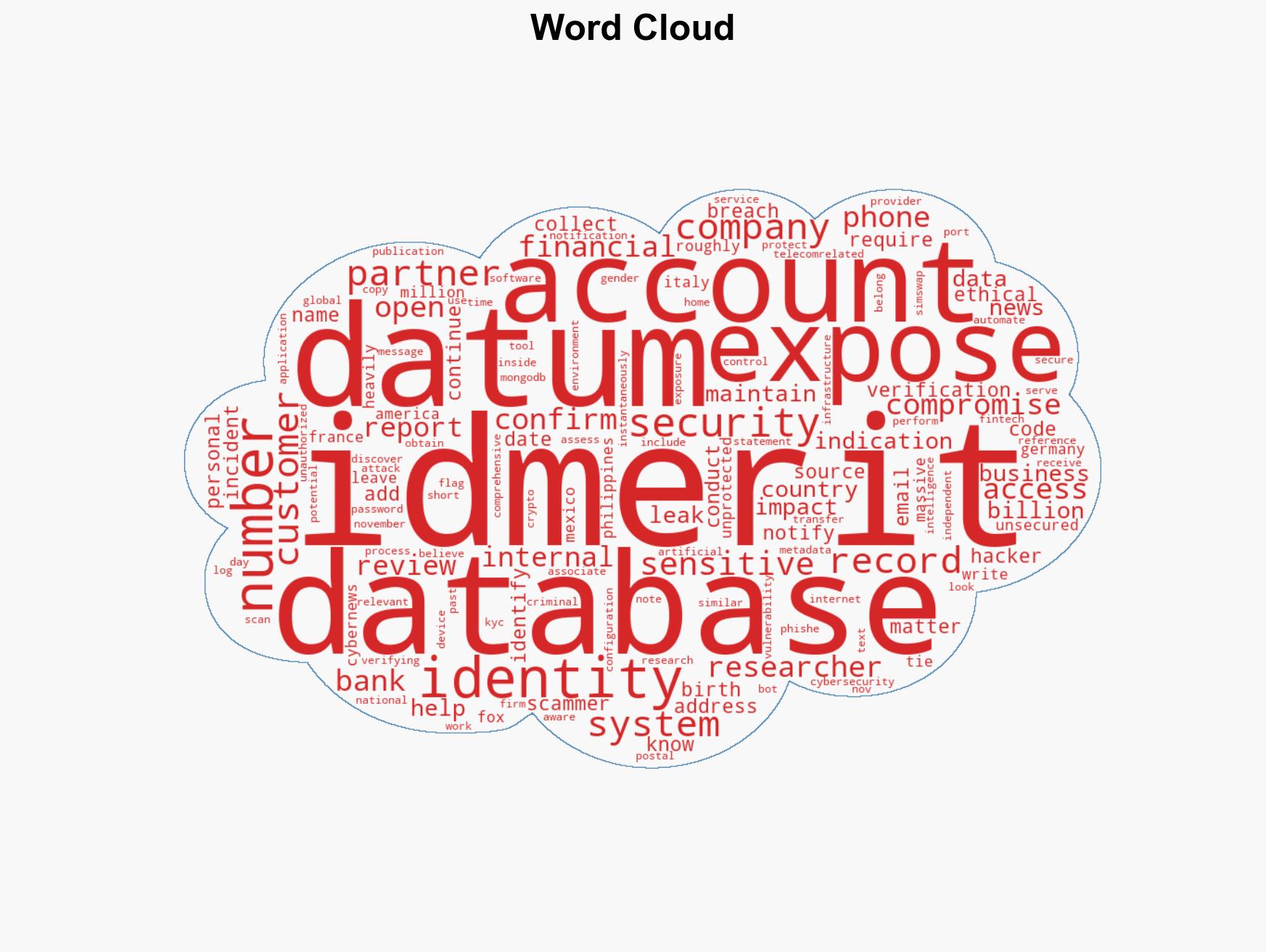
cybersecurity, data breach, identity theft, financial services, regulatory compliance, digital identity, cybercrime
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us