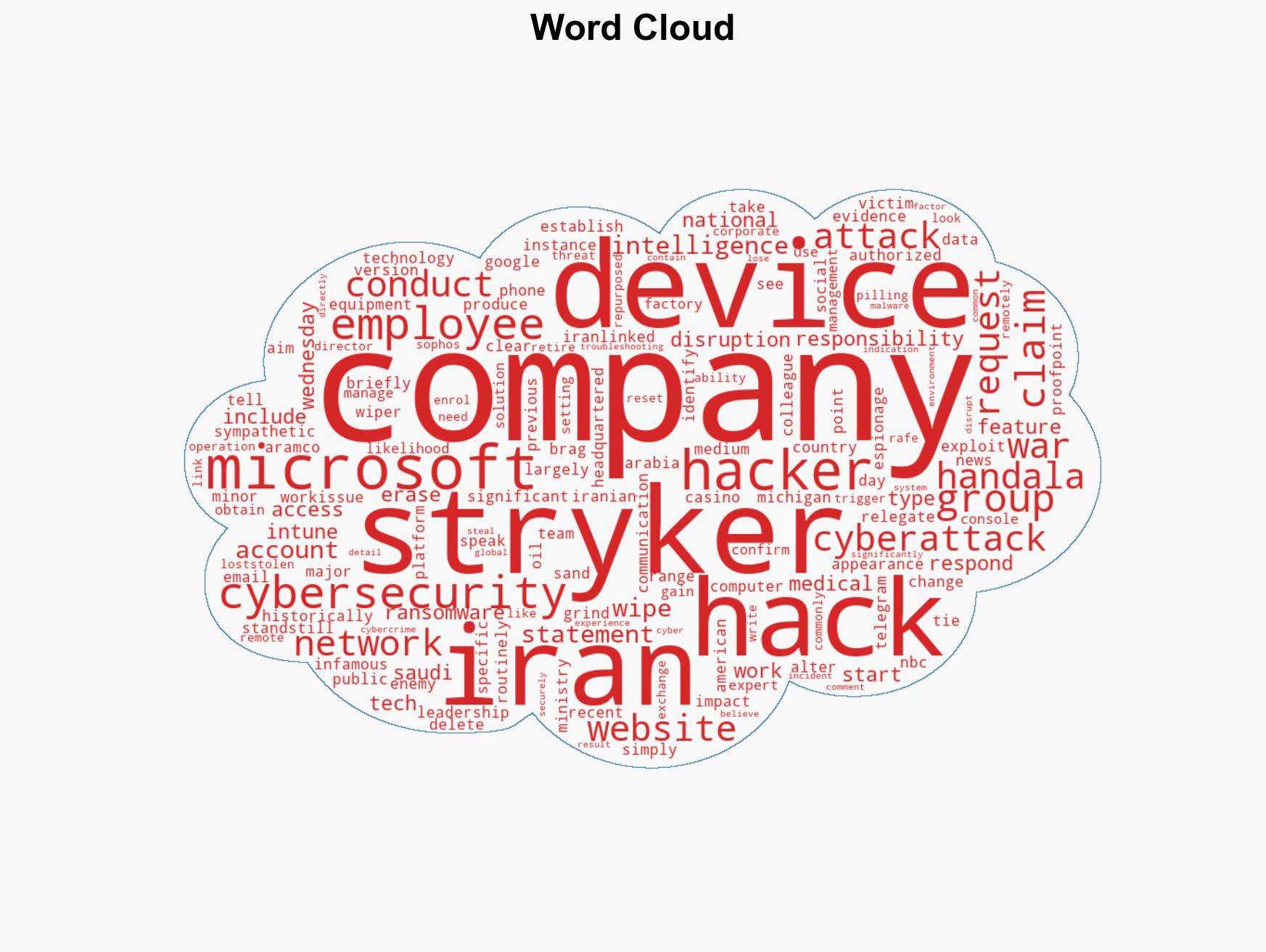
Iran-Linked Hackers Launch Major Cyberattack on US Medical Tech Firm, Marking Escalation Since War Began
Published on: 2026-03-12
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Iran appears to have conducted a significant cyberattack against a US company a first since the war started
1. BLUF (Bottom Line Up Front)
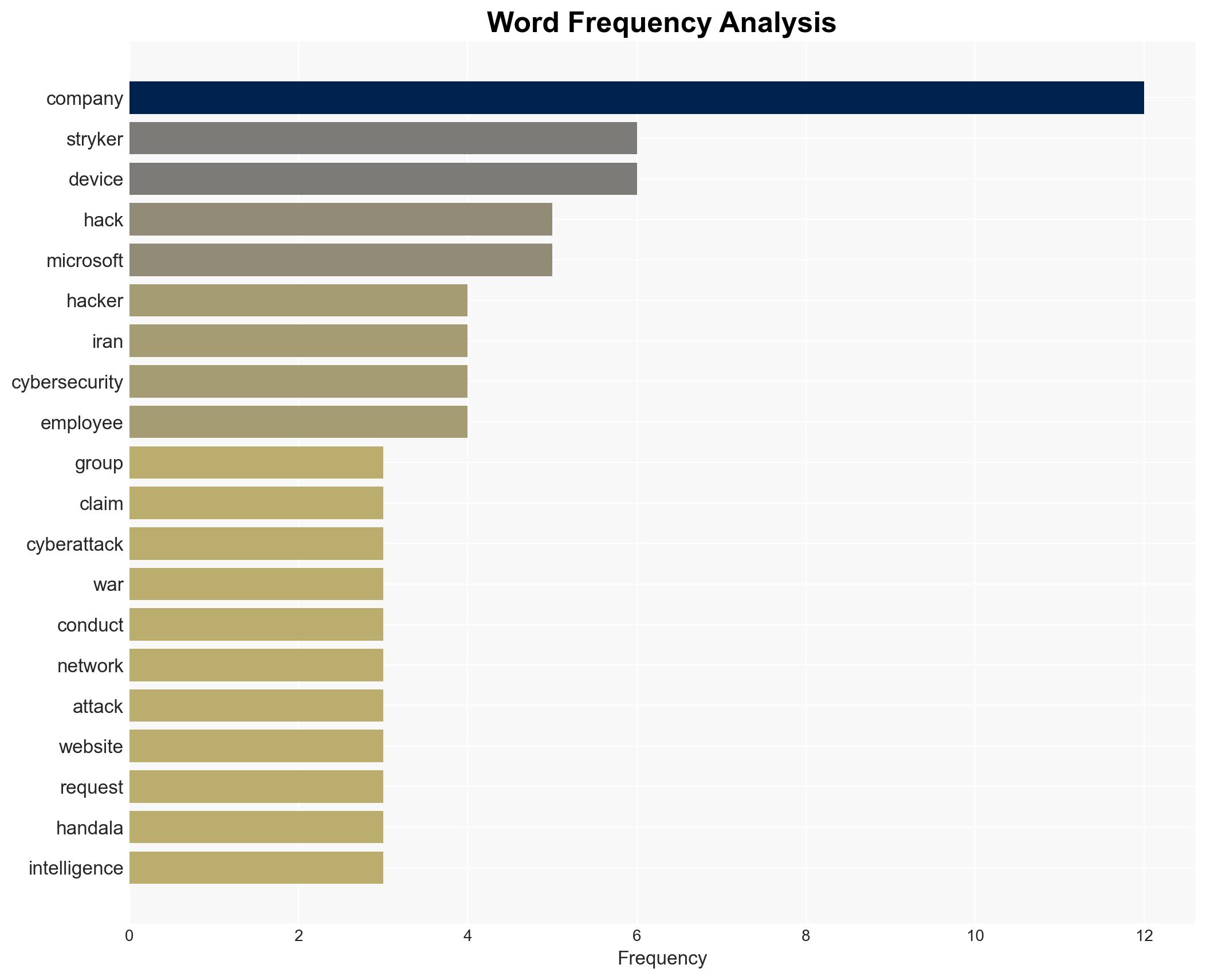
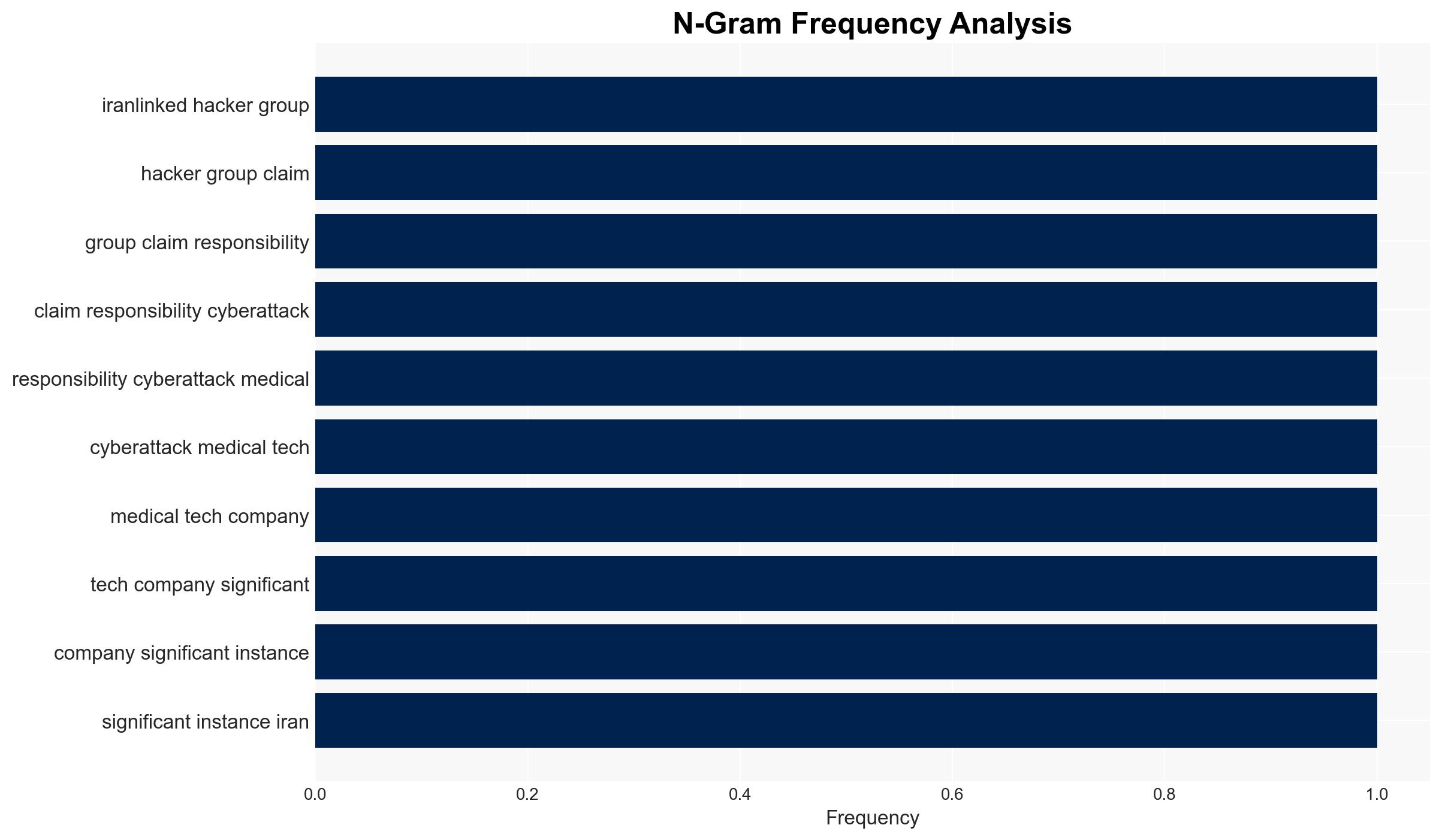
Iran-linked group Handala Team is likely responsible for a significant cyberattack on the US-based medical tech company Stryker, marking a shift in Iran’s cyber operations since the war began. This attack, which disrupted corporate communications and operations, suggests an escalation in tactics. Overall confidence in this assessment is moderate, pending further verification of technical details.
2. Competing Hypotheses
- Hypothesis A: The cyberattack was conducted by the Handala Team, linked to Iran’s Intelligence Ministry, as a deliberate escalation in cyber operations against US interests. Supporting evidence includes the group’s claim of responsibility and the attack’s alignment with Iran’s historical cyber tactics. However, the lack of detailed technical attribution and potential for false claims by the group are uncertainties.
- Hypothesis B: The attack may have been conducted by an independent or non-state actor falsely claiming ties to Iran to advance their own agenda or sow confusion. This is supported by the lack of clear technical evidence directly linking the attack to Iranian state operations. Contradicting this is the group’s established history of similar claims and operations.
- Assessment: Hypothesis A is currently better supported due to the group’s historical patterns and the nature of the attack. Key indicators that could shift this judgment include technical forensic evidence linking the attack directly to Iranian state infrastructure or communications.
3. Key Assumptions and Red Flags
- Assumptions: The Handala Team has operational capabilities to access and exploit corporate device management systems; Iran is willing to escalate cyber operations in response to geopolitical tensions; Stryker’s systems were adequately secured prior to the attack.
- Information Gaps: Detailed forensic analysis of the attack vector; confirmation of the Handala Team’s operational control over the attack; broader context of Iran’s strategic cyber objectives.
- Bias & Deception Risks: Potential bias in attributing the attack to Iran based on historical patterns; risk of deception by the Handala Team in claiming responsibility to enhance their perceived capabilities.
4. Implications and Strategic Risks
This development could signal a new phase of cyber aggression from Iran, potentially leading to increased tensions and retaliatory measures. The attack may embolden other state or non-state actors to conduct similar operations.
- Political / Geopolitical: Potential for escalation in US-Iran tensions, impacting diplomatic relations and regional stability.
- Security / Counter-Terrorism: Increased threat to US critical infrastructure and private sector entities from state-sponsored cyber actors.
- Cyber / Information Space: Heightened risk of further cyberattacks targeting US interests, necessitating enhanced cybersecurity measures.
- Economic / Social: Disruption to Stryker’s operations could have economic repercussions, affecting supply chains and market confidence.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of Iranian cyber activities, conduct a thorough forensic investigation of the attack, and strengthen cybersecurity protocols across critical sectors.
- Medium-Term Posture (1–12 months): Develop resilience measures and partnerships with private sector entities to bolster cyber defenses, and engage in diplomatic efforts to address cyber aggression.
- Scenario Outlook:
- Best: De-escalation through diplomatic channels and improved cyber defenses.
- Worst: Escalation of cyberattacks leading to broader conflict and economic disruption.
- Most-Likely: Continued sporadic cyber incidents with incremental improvements in defensive measures.
6. Key Individuals and Entities
- Handala Team
- Stryker
- Iran’s Intelligence Ministry
- Rafe Pilling, Director of Threat Intelligence at Sophos
7. Thematic Tags
cybersecurity, Iran, state-sponsored attacks, cyber-espionage, US-Iran relations, information warfare, critical infrastructure
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us