Assessing the Resilience of Iran’s Proxy Forces Amid Rising Tensions with the U.S. and Israel
Published on: 2026-03-12
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: The Limits of Irans Proxy Empire
1. BLUF (Bottom Line Up Front)
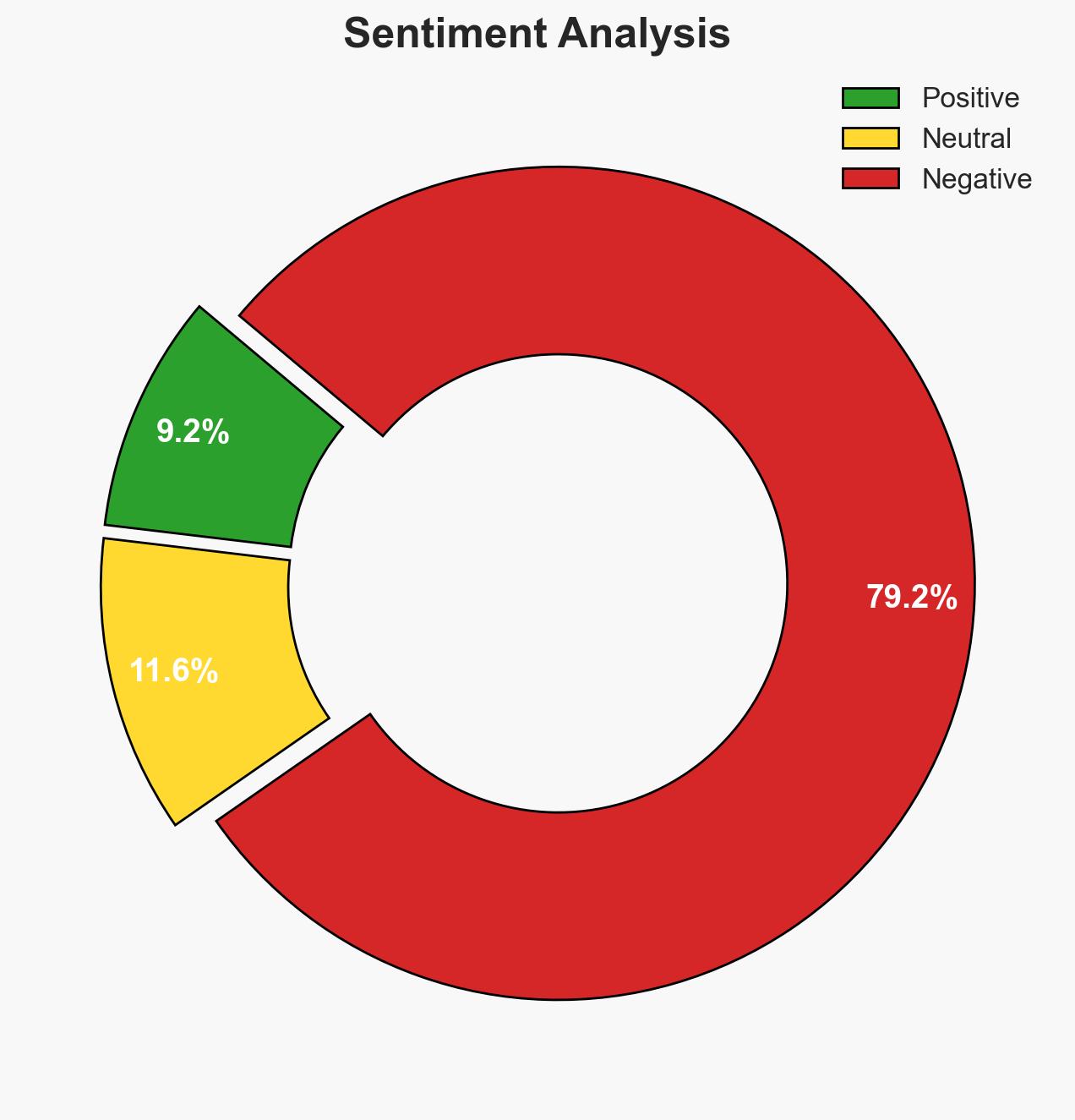
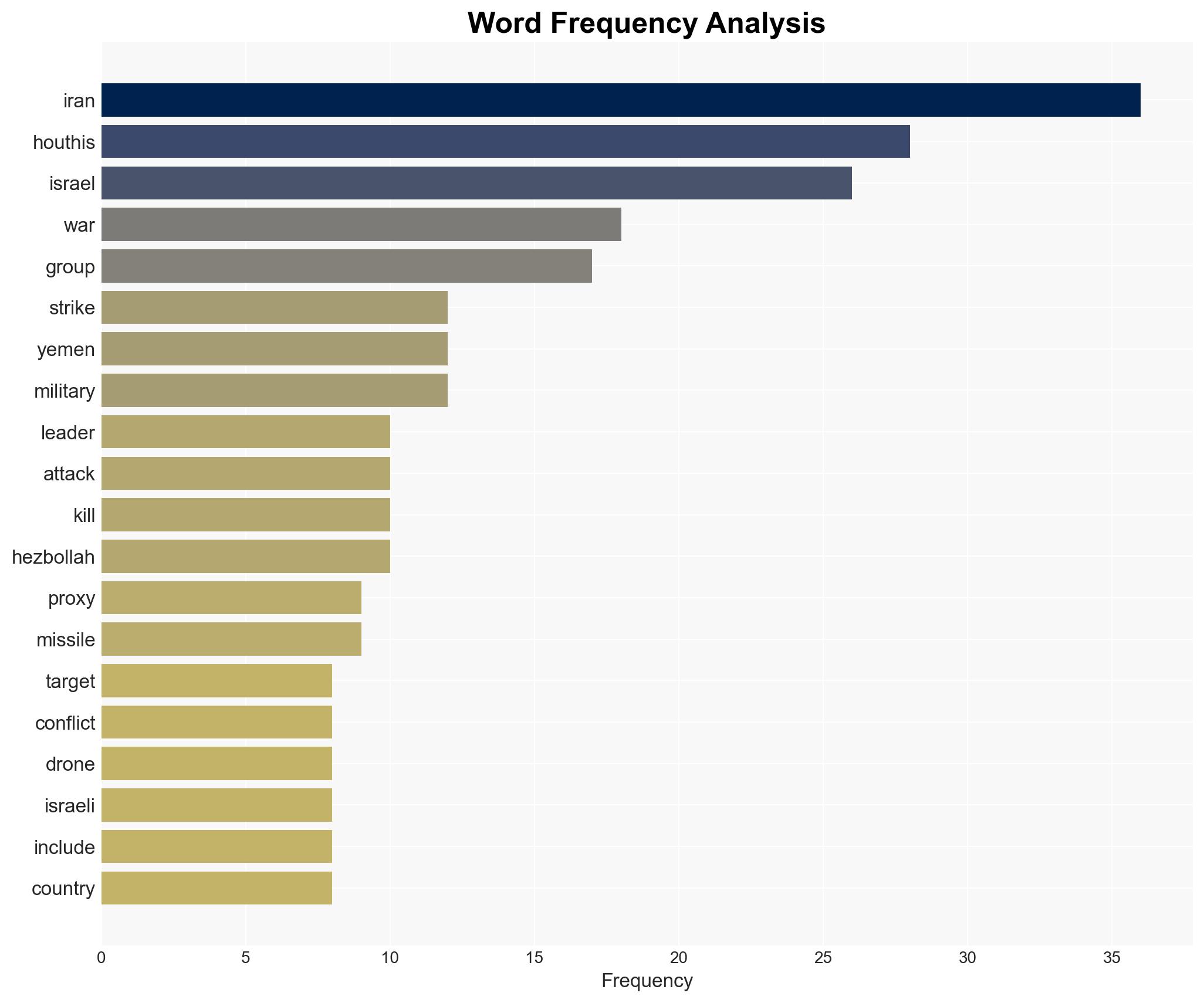
The current engagement of Iran’s proxies in the conflict with the U.S. and Israel is limited and less effective than anticipated, with moderate confidence. The Houthis, despite vocal support, have not taken significant action, while Hezbollah and Iraqi militias have demonstrated limited operational impact. This suggests a potential overestimation of Iran’s proxy capabilities, affecting regional power dynamics and security assessments.
2. Competing Hypotheses
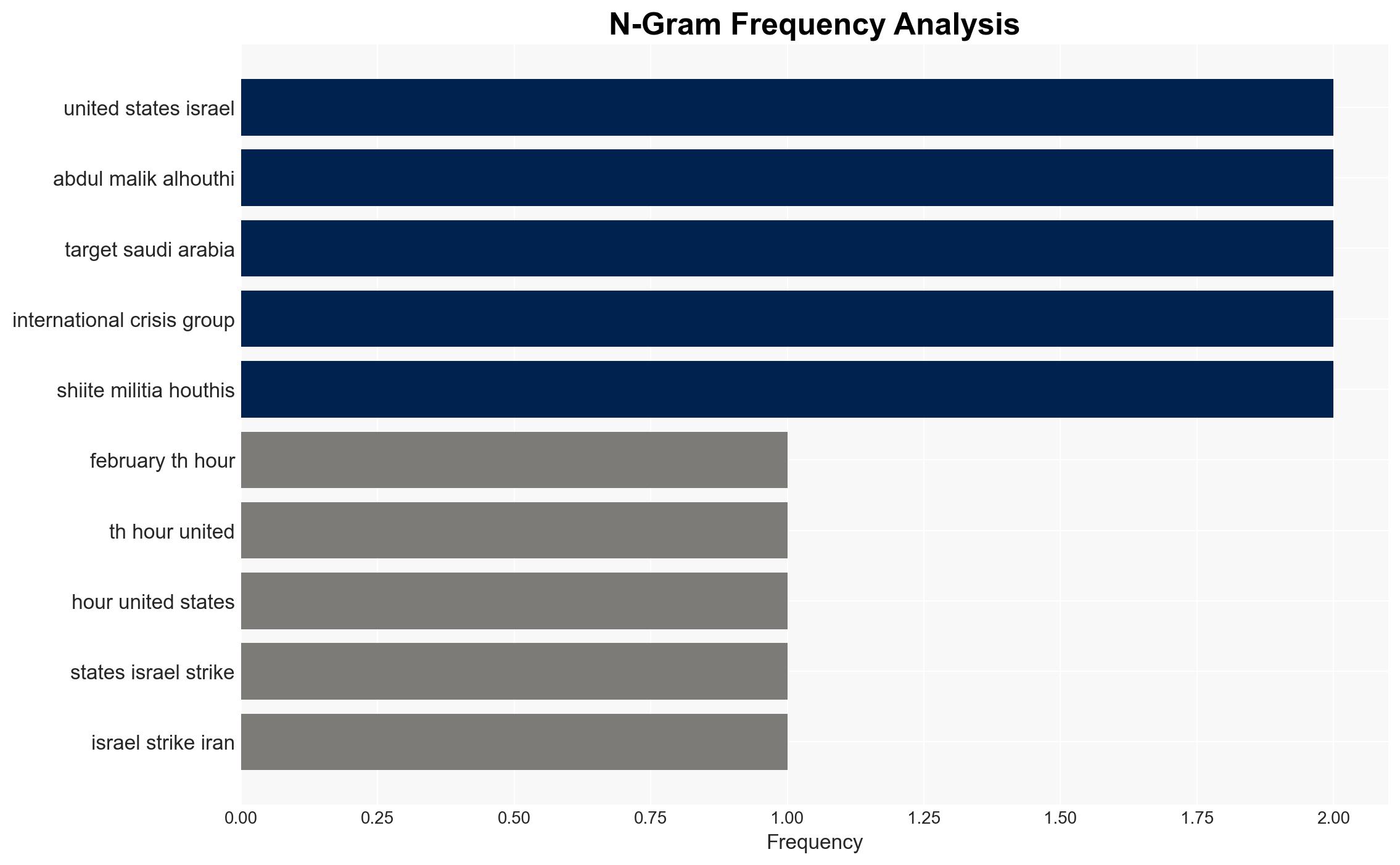
- Hypothesis A: Iran’s proxies are deliberately restrained to avoid escalation and preserve resources for future conflicts. Evidence includes limited engagement from the Houthis and ineffective attacks by Hezbollah and Iraqi militias. Uncertainties involve the true extent of Iran’s control over these groups.
- Hypothesis B: Iran’s proxies are unable to effectively engage due to logistical, strategic, or operational constraints. Supporting evidence includes the lack of significant damage from attacks and the absence of coordinated efforts. Contradicting evidence could emerge if proxies suddenly increase their operational tempo.
- Assessment: Hypothesis B is currently better supported due to the observed ineffectiveness and lack of coordinated proxy actions. Key indicators that could shift this judgment include a sudden increase in proxy activity or evidence of strategic restraint directives from Iran.
3. Key Assumptions and Red Flags
- Assumptions: Iran maintains significant influence over its proxies; proxies possess the capability to escalate conflict; regional actors are monitoring proxy activities closely.
- Information Gaps: Detailed intelligence on internal communications between Iran and its proxies; specific operational capabilities and readiness of each proxy group.
- Bias & Deception Risks: Potential overreliance on open-source information; risk of Iranian or proxy misinformation campaigns to mislead adversaries.
4. Implications and Strategic Risks
The limited engagement of Iran’s proxies could lead to a reassessment of Iran’s regional influence and military strategy. This development might alter power balances and provoke recalibrations in U.S. and Israeli defense postures.
- Political / Geopolitical: Potential for decreased Iranian influence if proxies remain ineffective, leading to shifts in regional alliances.
- Security / Counter-Terrorism: Possible reduction in immediate threat levels from proxy groups, but risk of future escalations remains.
- Cyber / Information Space: Increased likelihood of cyber operations as proxies may resort to asymmetric tactics to compensate for military shortcomings.
- Economic / Social: Continued instability could exacerbate humanitarian crises, particularly in Yemen and Lebanon, impacting regional economic conditions.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Intensify intelligence collection on proxy communications and movements; enhance defensive measures for potential cyber threats.
- Medium-Term Posture (1–12 months): Strengthen regional partnerships to counter potential proxy resurgence; invest in counter-proxy capabilities and intelligence-sharing frameworks.
- Scenario Outlook:
- Best: Proxies remain inactive, leading to reduced regional tensions.
- Worst: Proxies escalate operations, prompting broader conflict.
- Most-Likely: Continued low-level proxy activity with sporadic escalations.
6. Key Individuals and Entities
- Abdul Malik al-Houthi – Leader of Yemen’s Houthi movement
- Hezbollah – Lebanese paramilitary group
- Iranian Government – Not explicitly detailed in the snippet
- U.S. and Israeli Governments – Adversaries in the conflict
7. Thematic Tags
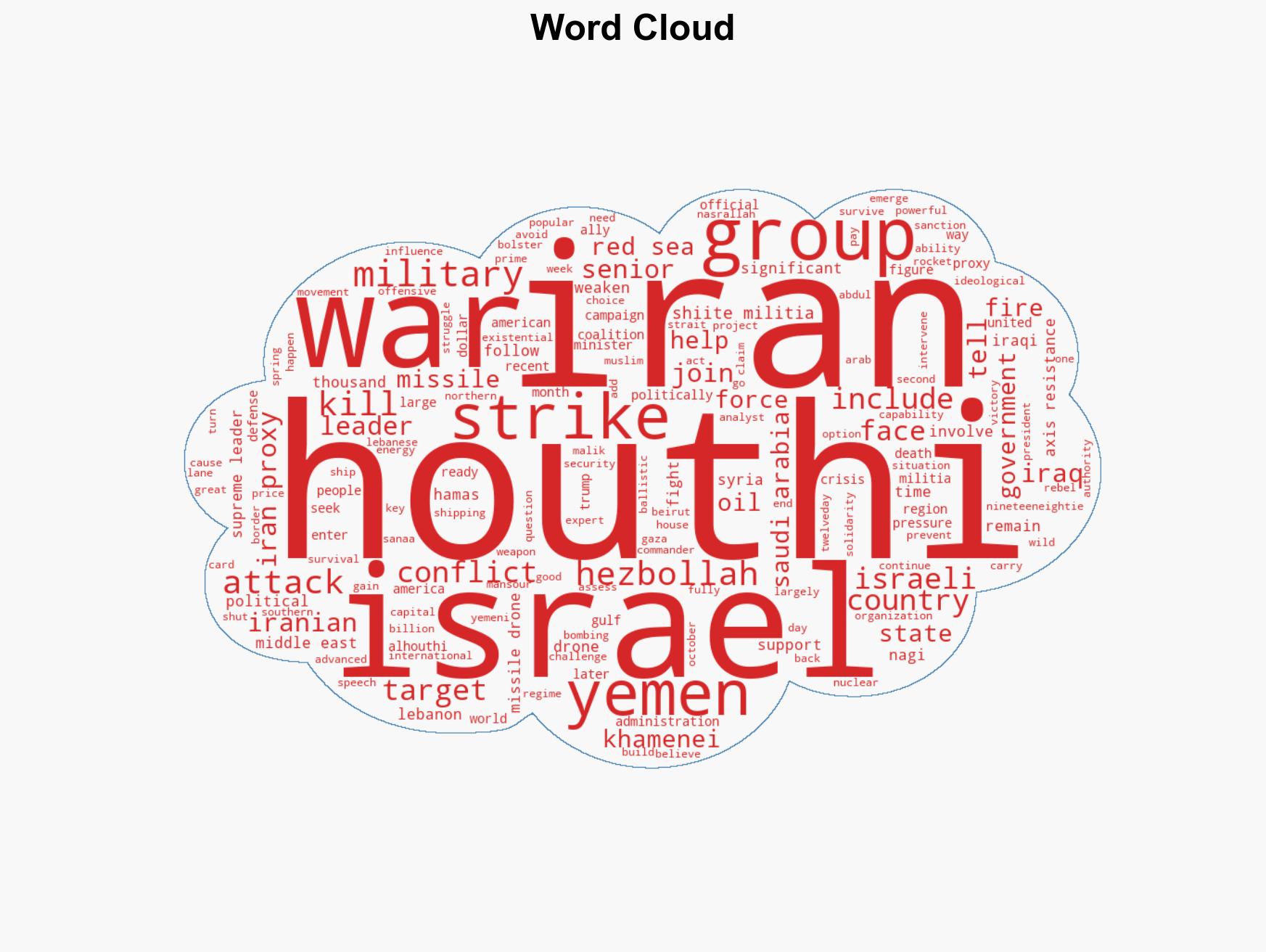
Counter-Terrorism, Iranian proxies, Middle East conflict, regional security, Axis of Resistance, geopolitical dynamics, asymmetric warfare
Structured Analytic Techniques Applied
- ACH 2.0: Reconstruct likely threat actor intentions via hypothesis testing and structured refutation.
- Indicators Development: Track radicalization signals and propaganda patterns to anticipate operational planning.
- Narrative Pattern Analysis: Deconstruct and track propaganda or influence narratives.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Counter-Terrorism Briefs ·
Daily Summary ·
Support us