CISA includes critical n8n vulnerability CVE-2025-68613 in its Known Exploited Vulnerabilities list
Published on: 2026-03-12
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
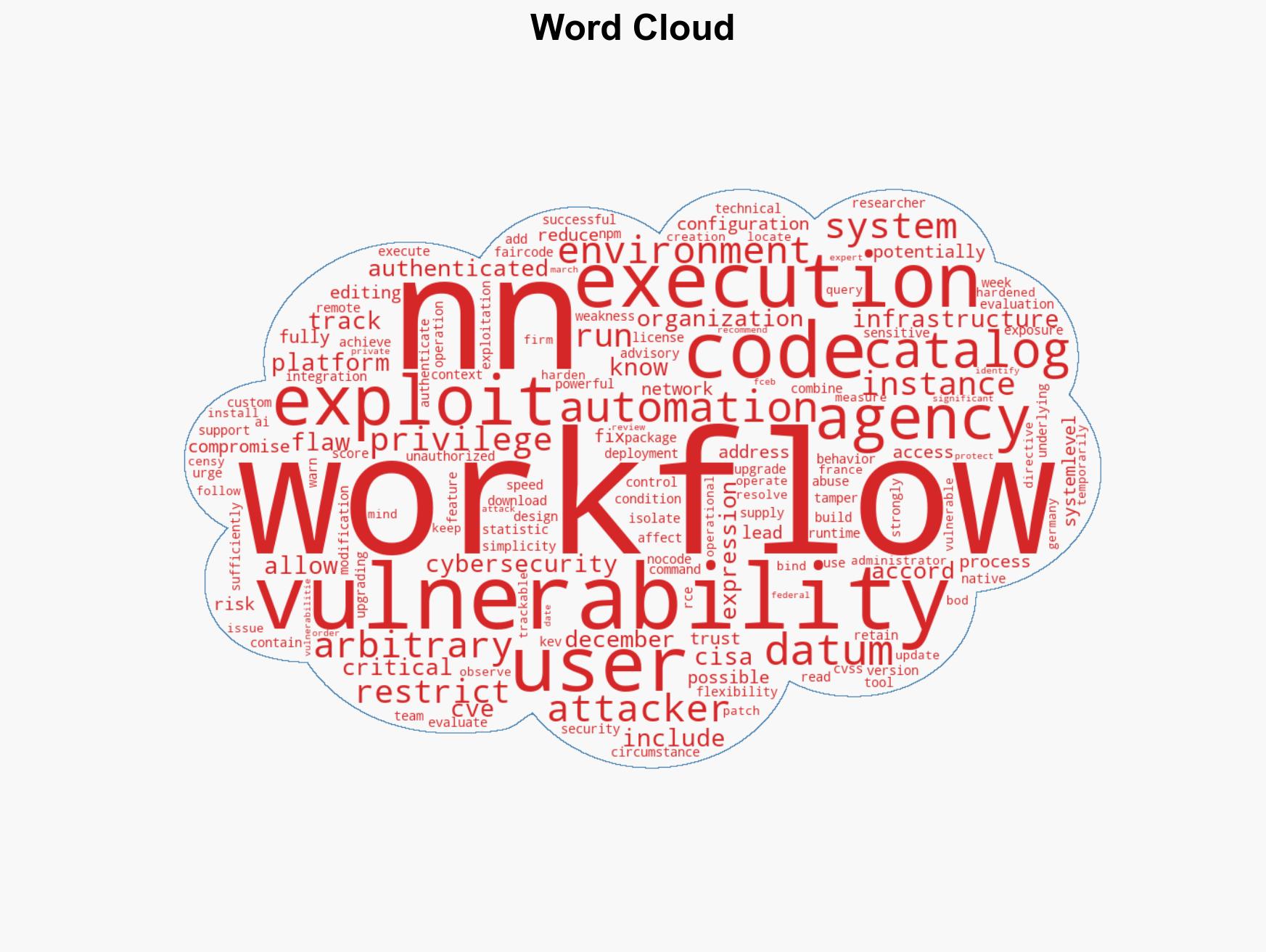
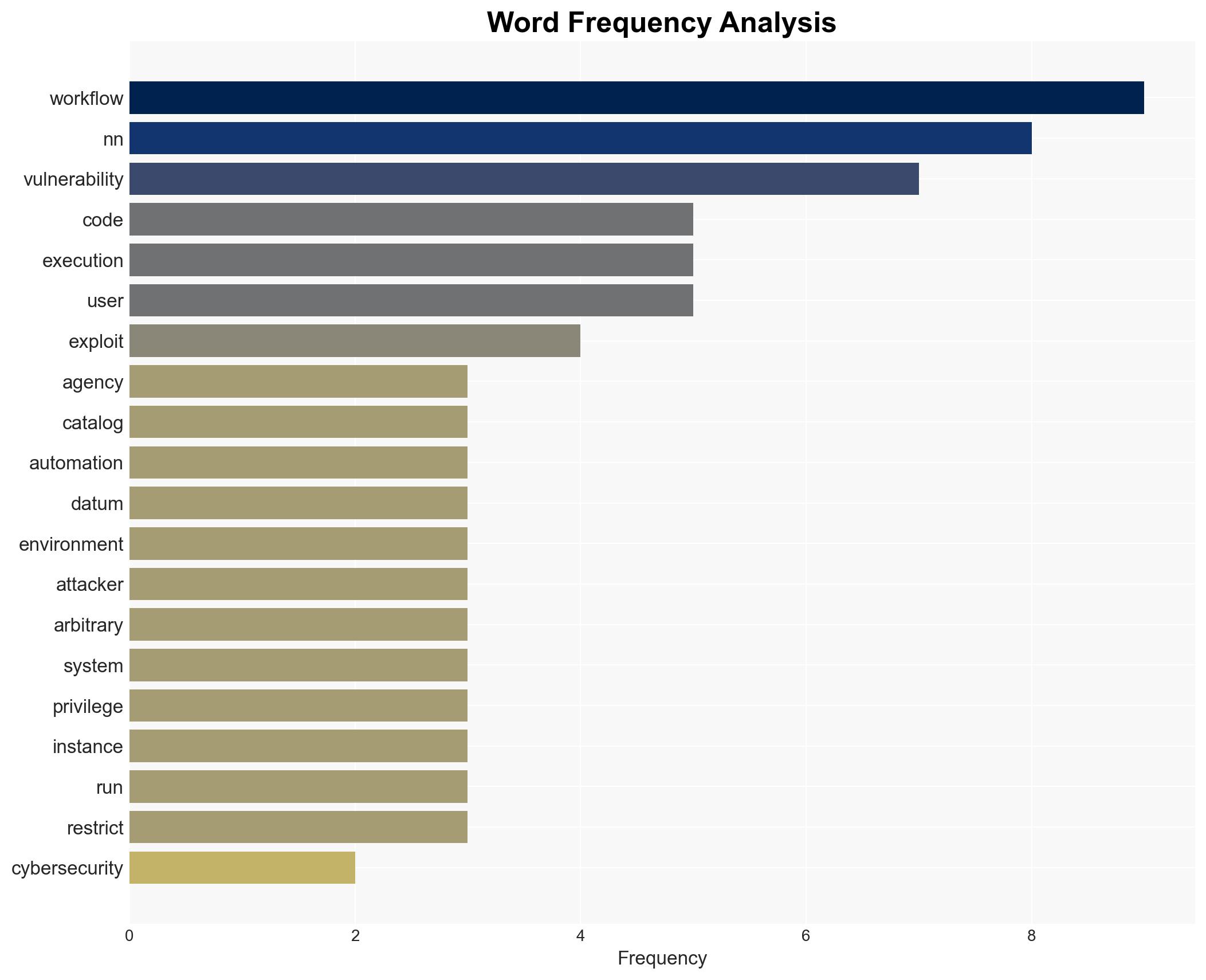
Intelligence Report: US CISA adds a flaw in n8n to its Known Exploited Vulnerabilities catalog
1. BLUF (Bottom Line Up Front)
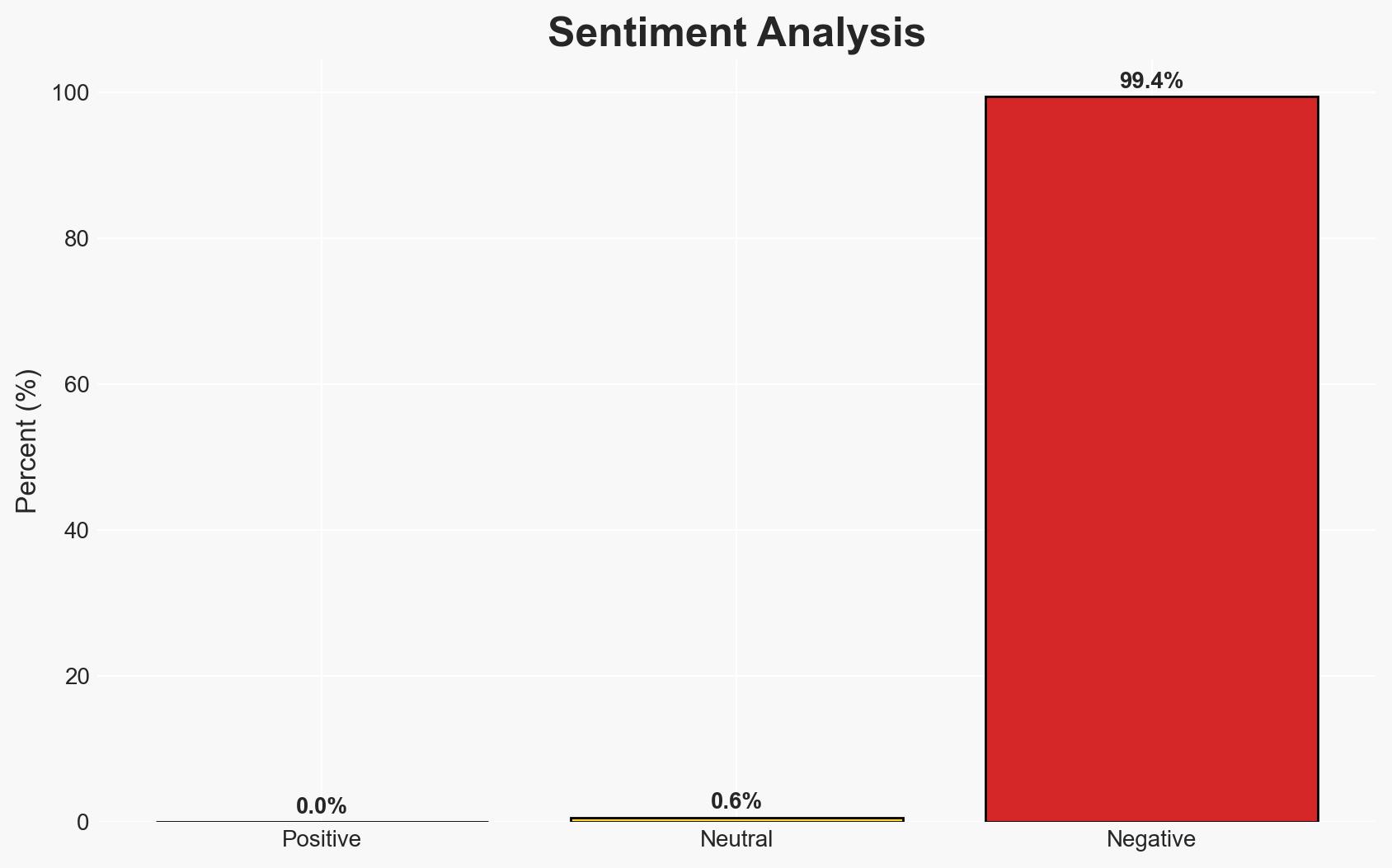
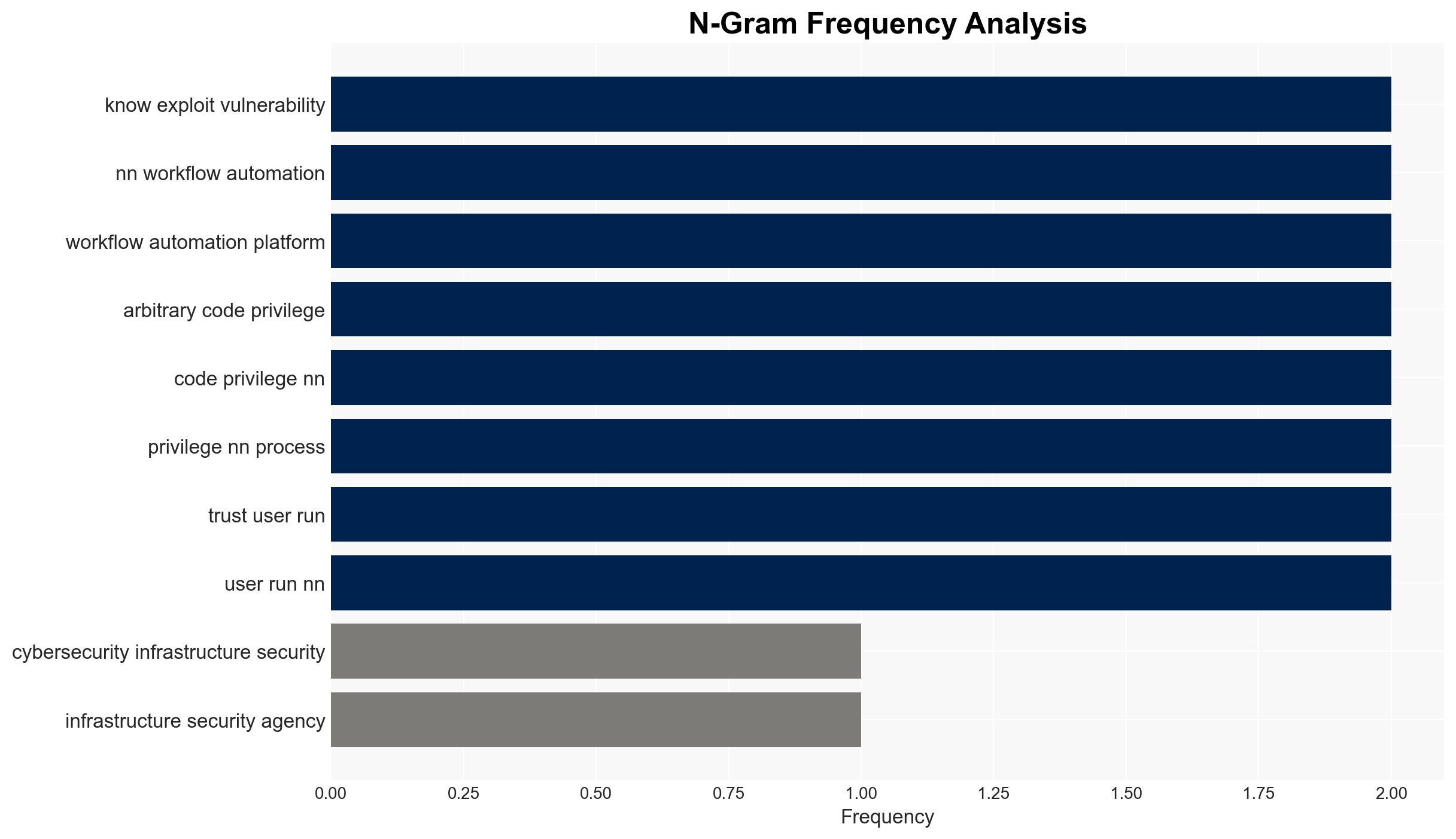
The U.S. CISA has identified a critical vulnerability in the n8n workflow automation platform, which could lead to significant security breaches if exploited. The flaw, CVE-2025-68613, allows for remote code execution by authenticated users, potentially compromising systems and sensitive data. This vulnerability primarily affects organizations using n8n, particularly in the U.S., Germany, and France. Overall confidence in this assessment is moderate, given the current data.
2. Competing Hypotheses
- Hypothesis A: The vulnerability in n8n will be rapidly exploited by cybercriminals, leading to widespread breaches. This is supported by the high CVSS score and the large number of potentially vulnerable instances. However, the requirement for authenticated access may limit immediate exploitation.
- Hypothesis B: Organizations will quickly patch the vulnerability, minimizing potential exploitation. This is supported by the availability of patches and CISA’s directive for immediate action. However, the delay in patch application and the high number of instances may hinder this outcome.
- Assessment: Hypothesis A is currently better supported due to the high number of vulnerable instances and the critical nature of the flaw. Indicators such as reports of exploitation or patch adoption rates could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Organizations will prioritize patching based on CISA’s directive; the vulnerability requires authenticated access to exploit; n8n users are aware of the vulnerability and the associated risks.
- Information Gaps: The exact number of instances that have been patched; the speed at which organizations are responding to the vulnerability; detailed exploitation attempts or successes.
- Bias & Deception Risks: Potential underreporting of successful exploits; reliance on vendor-provided patch data; confirmation bias in assessing the threat level based on prior vulnerabilities.
4. Implications and Strategic Risks
This vulnerability could lead to significant security incidents if not addressed, impacting organizational operations and data integrity.
- Political / Geopolitical: Potential for increased tensions if state actors exploit the vulnerability for espionage or sabotage.
- Security / Counter-Terrorism: Heightened risk of cyber-attacks targeting critical infrastructure and sensitive data repositories.
- Cyber / Information Space: Increased activity in cyber forums discussing exploitation techniques; potential for misinformation regarding the vulnerability’s impact.
- Economic / Social: Financial losses from data breaches; reputational damage to affected organizations; potential regulatory scrutiny.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Urge organizations to apply patches immediately; monitor for signs of exploitation; restrict workflow editing to trusted users.
- Medium-Term Posture (1–12 months): Develop resilience measures, including enhanced monitoring and incident response capabilities; foster partnerships for information sharing.
- Scenario Outlook:
- Best Case: Rapid patch adoption prevents major incidents.
- Worst Case: Widespread exploitation leads to significant data breaches and operational disruptions.
- Most-Likely: Mixed response with some incidents occurring, but major breaches are contained.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, vulnerability management, remote code execution, CISA, n8n, patch management, information security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us