Researchers exploit vulnerability in MediaTek devices, breaching Nothing phone’s security in under a minute.
Published on: 2026-03-12
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Security researchers broke into a MediaTek-powered Nothing phone in just 45 seconds
1. BLUF (Bottom Line Up Front)
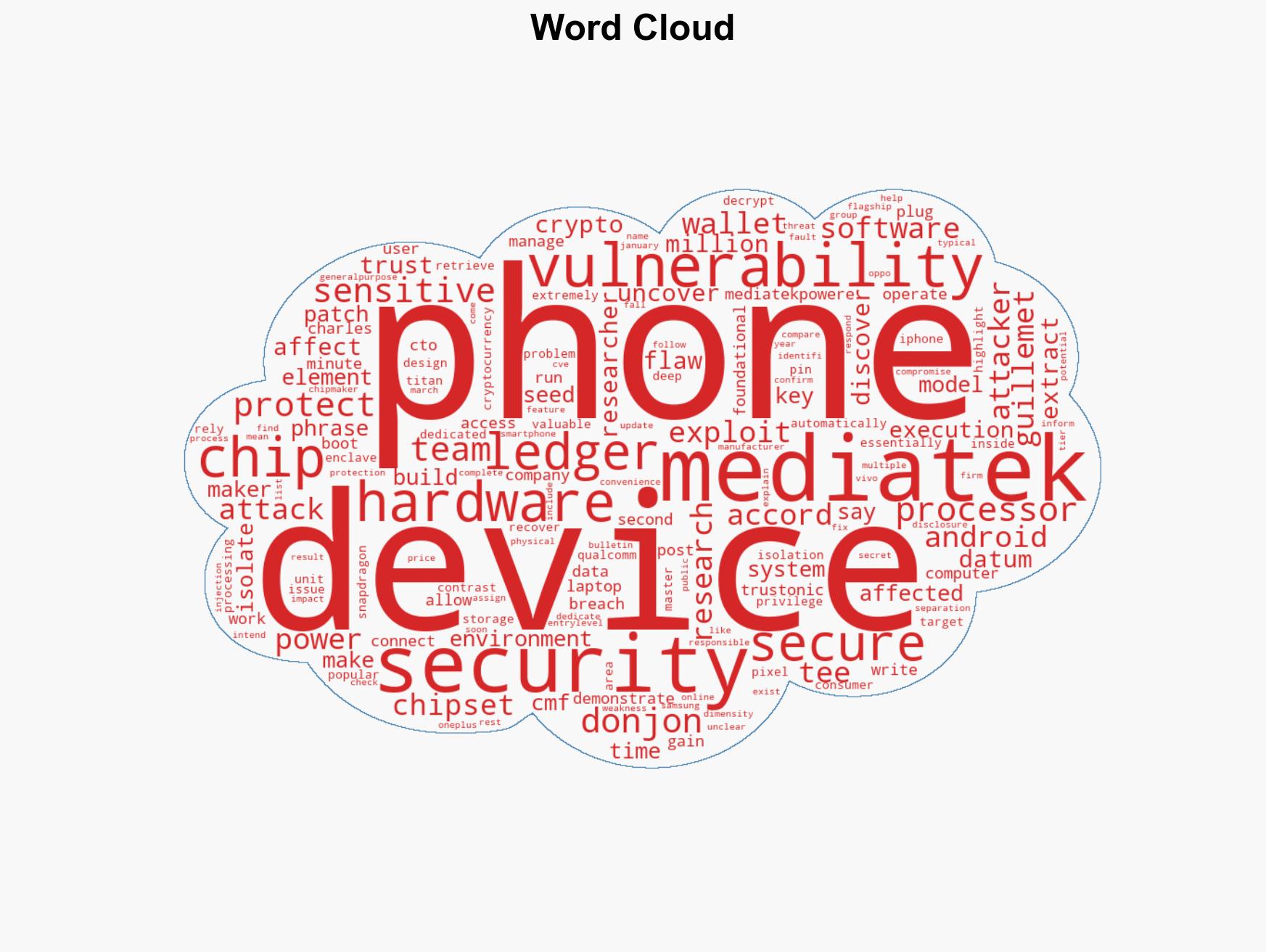
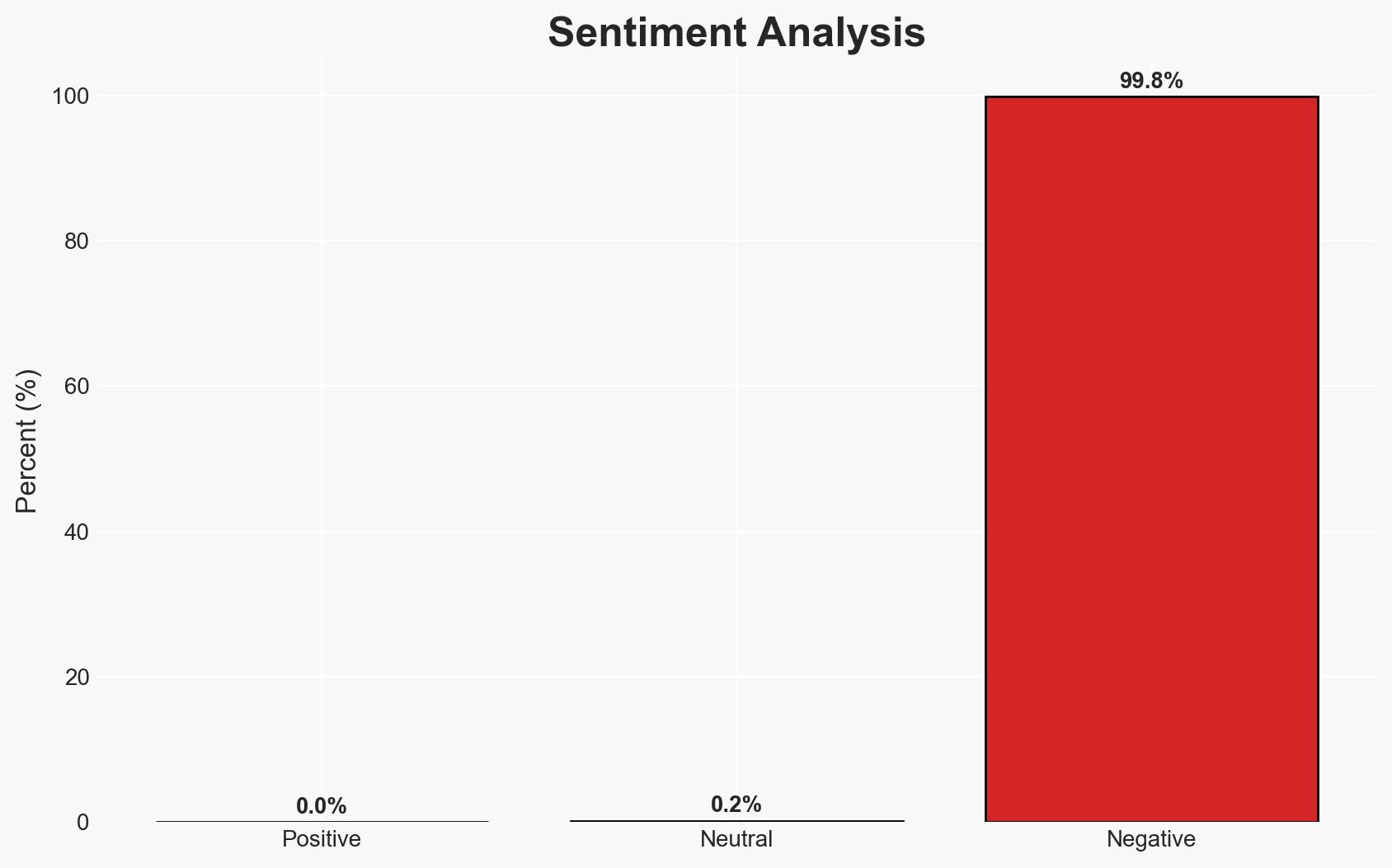
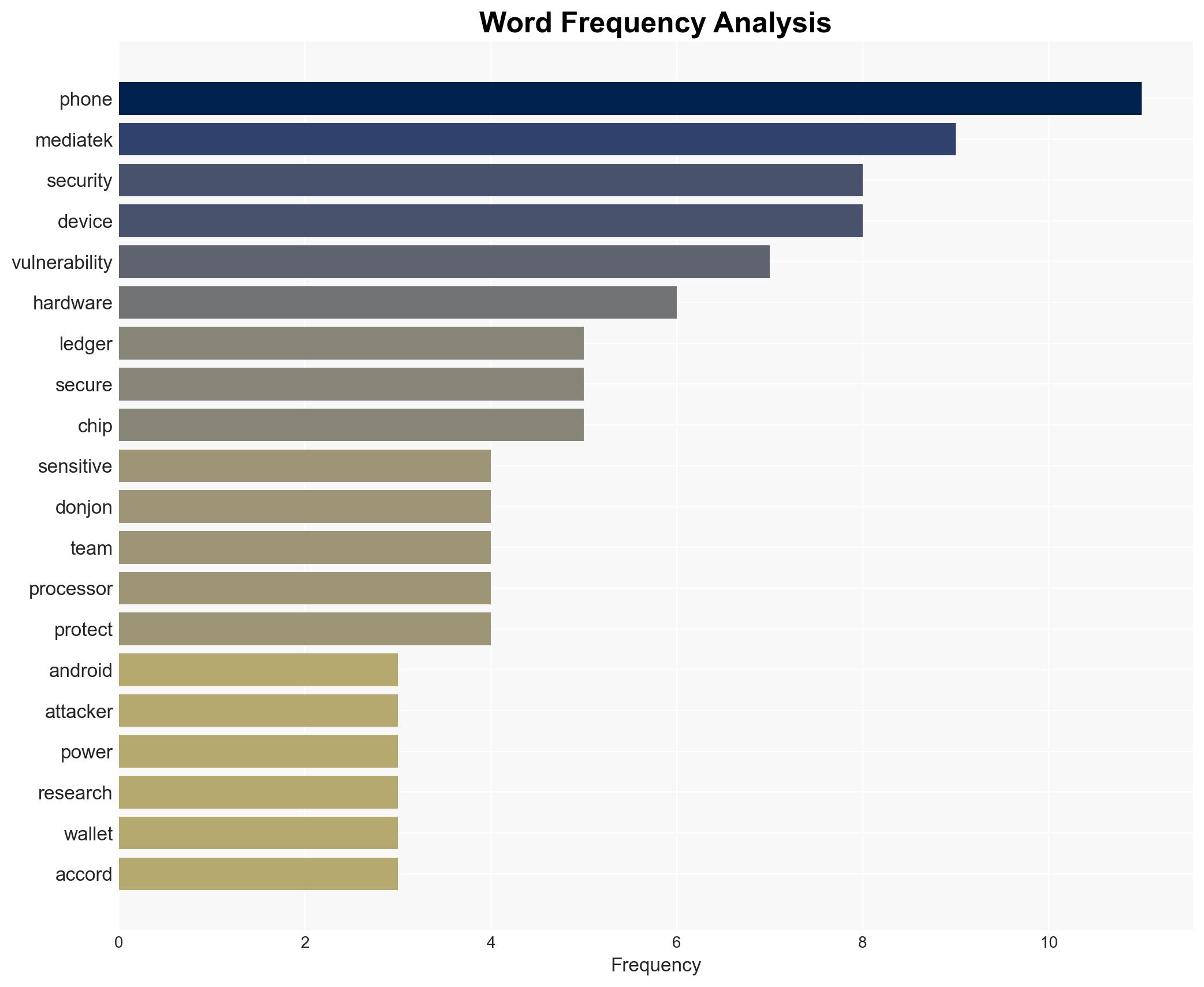
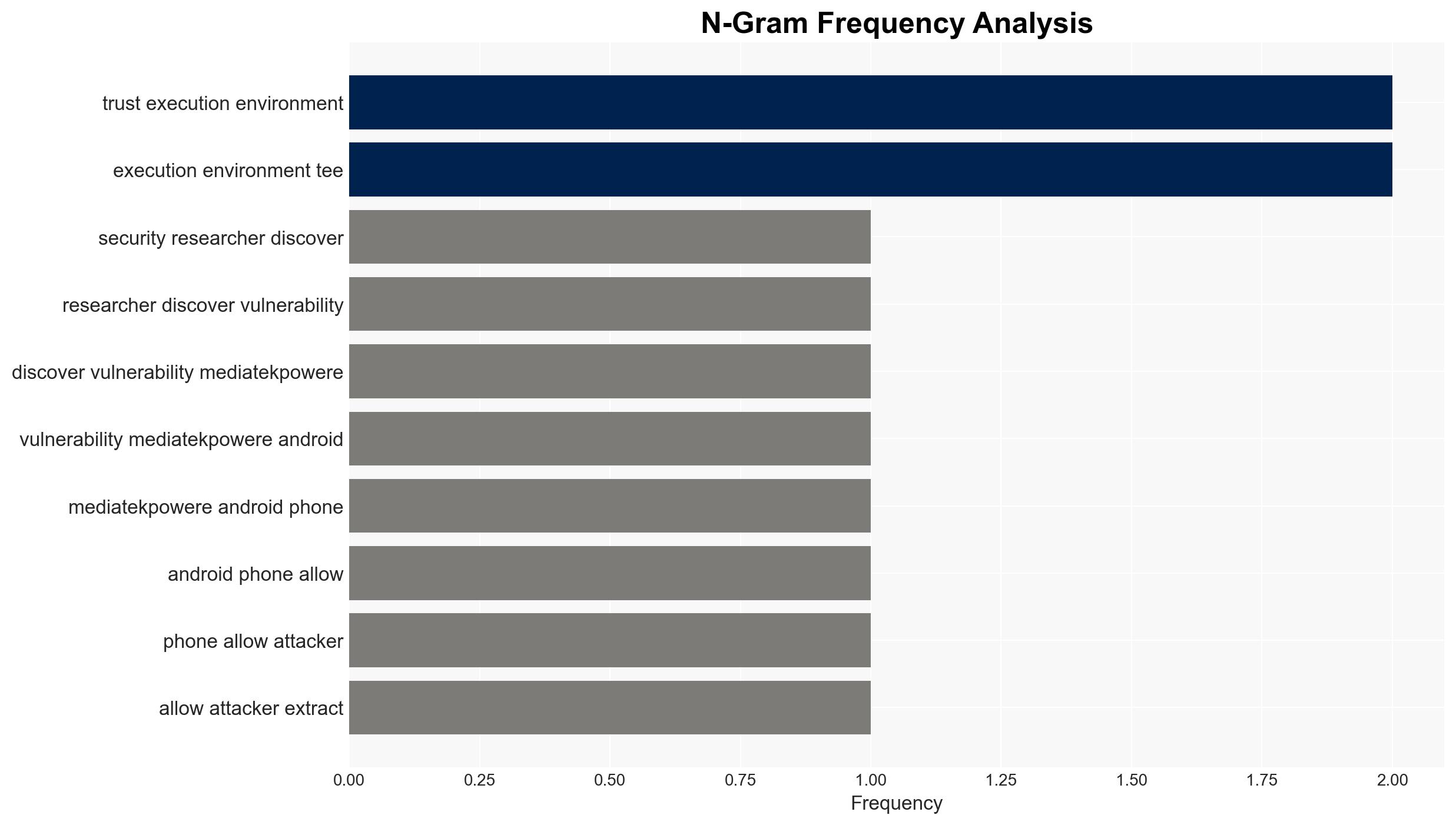
A vulnerability in MediaTek-powered Android phones allows attackers to extract sensitive data even when the device is powered off. This flaw affects millions of devices using Trustonic’s Trusted Execution Environment. The vulnerability, identified as CVE-2026-20435, has been patched, but its exploitation status remains unclear. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: The vulnerability has been exploited by malicious actors prior to patching. Supporting evidence includes the widespread use of MediaTek chips and the high value of the data targeted. Contradicting evidence includes the lack of reported incidents of exploitation.
- Hypothesis B: The vulnerability has not been exploited in the wild. Supporting evidence includes the responsible disclosure process and the rapid patching by MediaTek. Contradicting evidence includes the potential for unreported or undetected exploitation.
- Assessment: Hypothesis B is currently better supported due to the responsible disclosure and patching timeline. However, indicators such as reports of data breaches involving MediaTek devices could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The vulnerability affects all devices using the specified TEE; the patch has been effectively implemented by manufacturers; no significant exploitation has occurred.
- Information Gaps: Specific details on the number of devices patched and any exploitation incidents remain unknown.
- Bias & Deception Risks: Potential bias from the source due to vested interests in highlighting security flaws; lack of independent verification of the vulnerability’s exploitation status.
4. Implications and Strategic Risks
This development could lead to increased scrutiny on device security and influence consumer trust in MediaTek-powered devices.
- Political / Geopolitical: Potential regulatory actions or increased scrutiny on device manufacturers.
- Security / Counter-Terrorism: Heightened risk of data breaches and cyber-attacks targeting vulnerable devices.
- Cyber / Information Space: Increased focus on TEE vulnerabilities and potential shifts in cyber defense strategies.
- Economic / Social: Possible impact on consumer confidence and sales of affected devices, leading to economic repercussions for manufacturers.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor for reports of exploitation, ensure rapid deployment of patches, and communicate risks to stakeholders.
- Medium-Term Posture (1–12 months): Develop partnerships for improved security protocols, invest in Secure Element technology, and enhance consumer awareness.
- Scenario Outlook: Best: Full patch deployment and no exploitation reports. Worst: Widespread exploitation leading to significant data breaches. Most-Likely: Limited exploitation with gradual patch adoption.
6. Key Individuals and Entities
- Charles Guillemet, Ledger CTO
- MediaTek
- Trustonic
- Donjon, Ledger’s hardware security research team
- Device manufacturers (e.g., OPPO, vivo, OnePlus)
7. Thematic Tags
cybersecurity, mobile vulnerabilities, MediaTek, Trusted Execution Environment, data breach, consumer electronics, responsible disclosure
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us