Iranian-affiliated hackers escalate cyberattacks on U.S. and allies amid ongoing conflict, threatening critic…
Published on: 2026-03-12
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Iran-linked hackers take aim at US and other targets raising risk of cyberattacks during war
1. BLUF (Bottom Line Up Front)
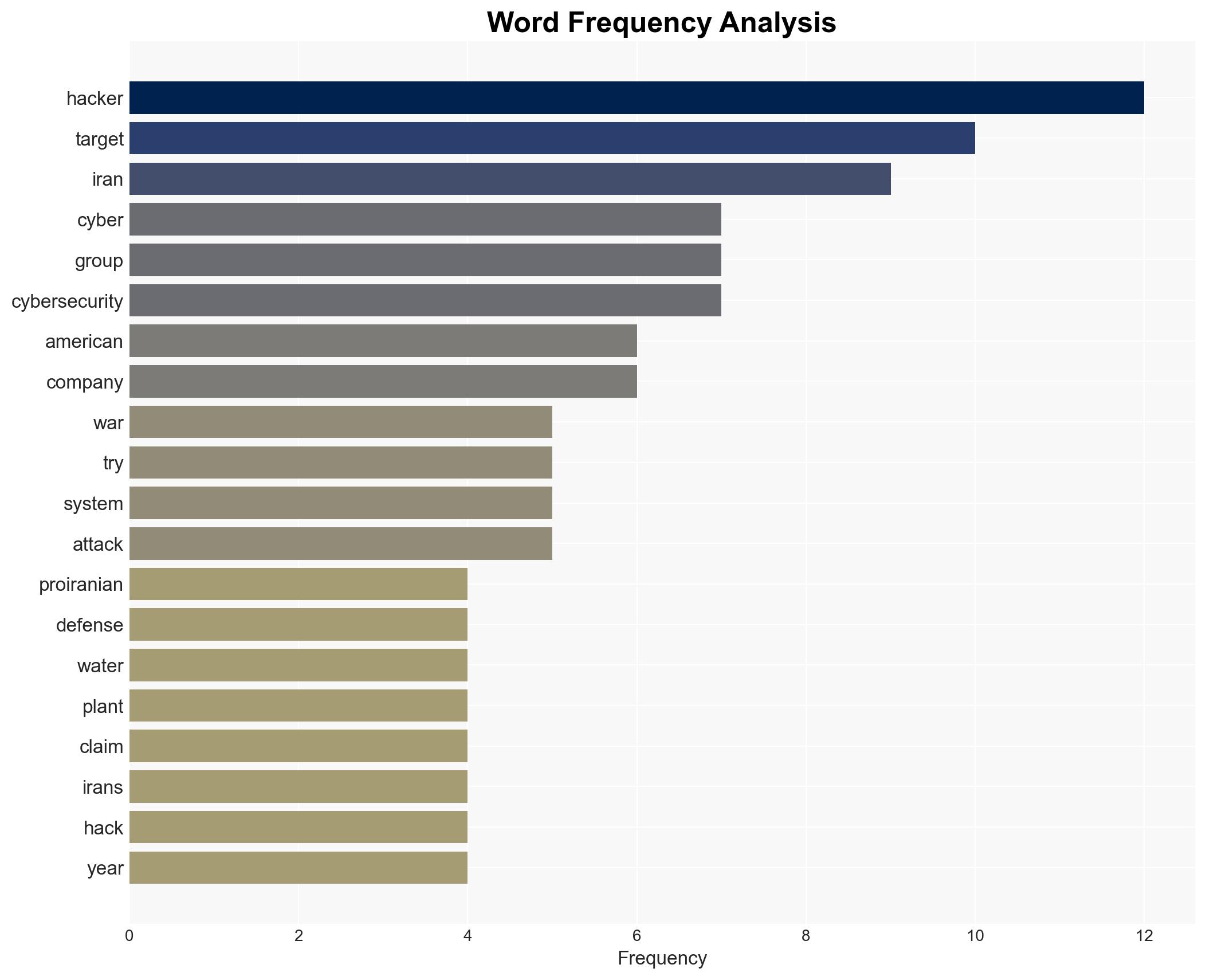
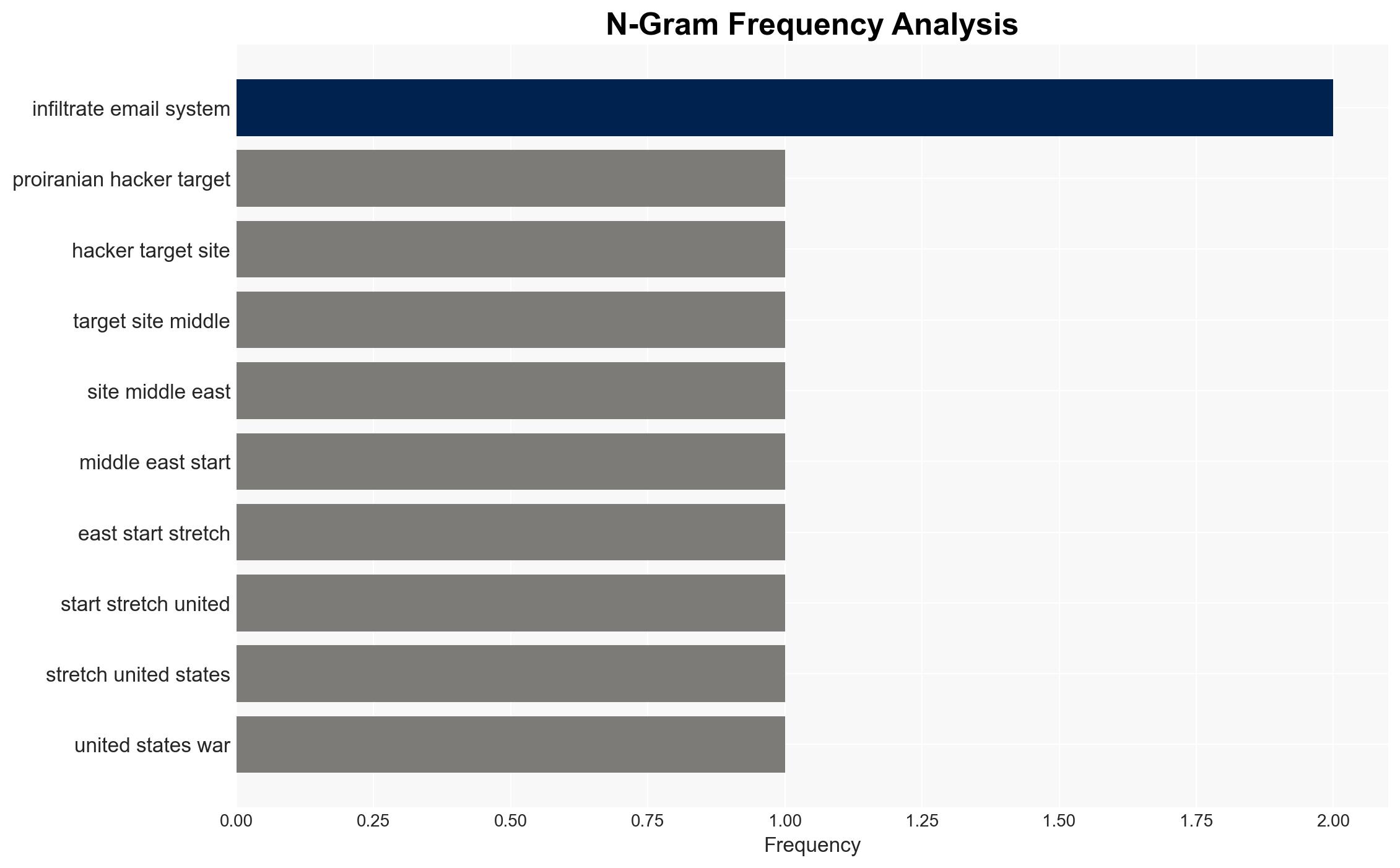
Iran-linked hackers are targeting U.S. and Middle Eastern entities, increasing the risk of cyberattacks on critical infrastructure and defense sectors. The most likely hypothesis is that these activities are part of a broader strategy to disrupt U.S. operations and alliances. This assessment is made with moderate confidence due to the complexity of cyber attribution and potential for misinformation.
2. Competing Hypotheses
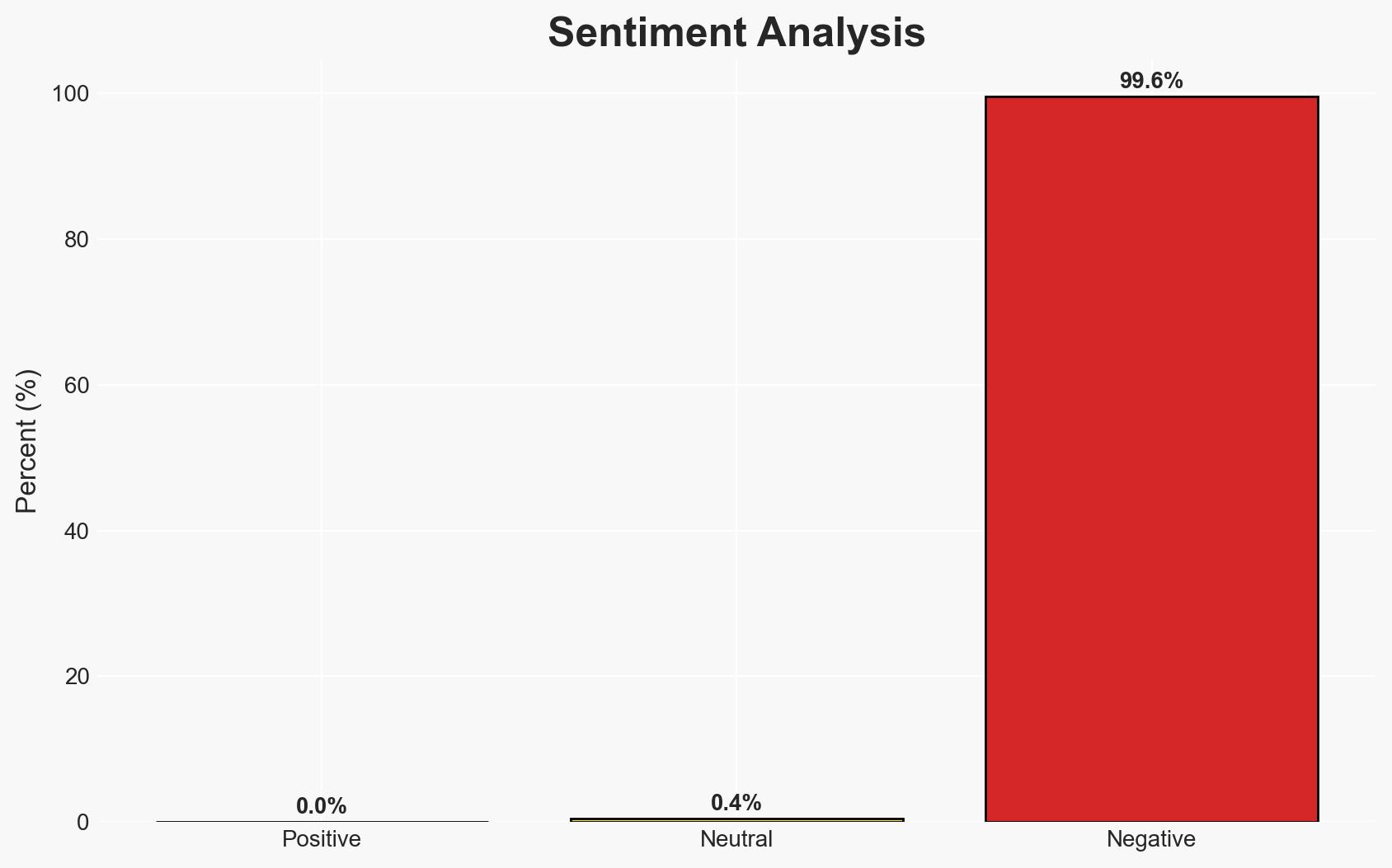
- Hypothesis A: The cyberattacks are a coordinated effort by Iran and its allies to weaken U.S. military and economic capabilities during the ongoing conflict. This is supported by the pattern of targeting critical infrastructure and defense-related entities. However, the extent of coordination with Tehran is uncertain.
- Hypothesis B: The attacks are primarily opportunistic actions by ideologically motivated hackers with loose affiliations to Iran, rather than a centrally coordinated campaign. The lack of direct financial gain and focus on data destruction supports this view, but it contradicts the strategic targeting of military and economic assets.
- Assessment: Hypothesis A is currently better supported due to the strategic nature of the targets and historical context of Iran’s cyber activities. Indicators such as increased sophistication or direct links to Iranian state actors could further substantiate this hypothesis.
3. Key Assumptions and Red Flags
- Assumptions: Iran has the capability and intent to conduct cyber operations against U.S. interests; Pro-Iranian groups are acting with some level of state support or approval; The current geopolitical tensions are a catalyst for increased cyber activity.
- Information Gaps: Precise attribution of cyberattacks to Iranian state actors; Detailed understanding of the command and control structure of pro-Iranian hacking groups; Real-time intelligence on planned future targets.
- Bias & Deception Risks: Potential confirmation bias in attributing attacks to Iran without conclusive evidence; Risk of information manipulation by hacking groups to exaggerate their capabilities or intentions.
4. Implications and Strategic Risks
The escalation of cyberattacks linked to Iran could lead to heightened geopolitical tensions and retaliatory actions, impacting regional stability and international relations.
- Political / Geopolitical: Potential for increased sanctions or diplomatic isolation of Iran; Risk of military escalation if cyberattacks are perceived as acts of war.
- Security / Counter-Terrorism: Increased threat to critical infrastructure and defense sectors; Need for enhanced cybersecurity measures and intelligence sharing.
- Cyber / Information Space: Potential for widespread disruption of digital services; Increased cyber espionage and intelligence gathering activities.
- Economic / Social: Potential economic impact due to disruptions in critical infrastructure; Public fear and uncertainty could affect social cohesion.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of critical infrastructure networks; Increase information sharing with allies; Conduct cybersecurity audits and drills.
- Medium-Term Posture (1–12 months): Strengthen public-private partnerships in cybersecurity; Develop rapid response capabilities; Invest in cyber resilience and workforce training.
- Scenario Outlook:
- Best Case: Diplomatic efforts lead to de-escalation and reduced cyber activity.
- Worst Case: Cyberattacks escalate into broader conflict, causing significant economic and security damage.
- Most Likely: Continued low to moderate intensity cyber operations targeting U.S. and allied interests, with periodic spikes in activity.
6. Key Individuals and Entities
- Kevin Mandia (Founder of Mandiant and Armadin)
- Ismael Valenzuela (Vice President of Threat Intelligence, Arctic Wolf)
- Handala (Pro-Iranian hacking group)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
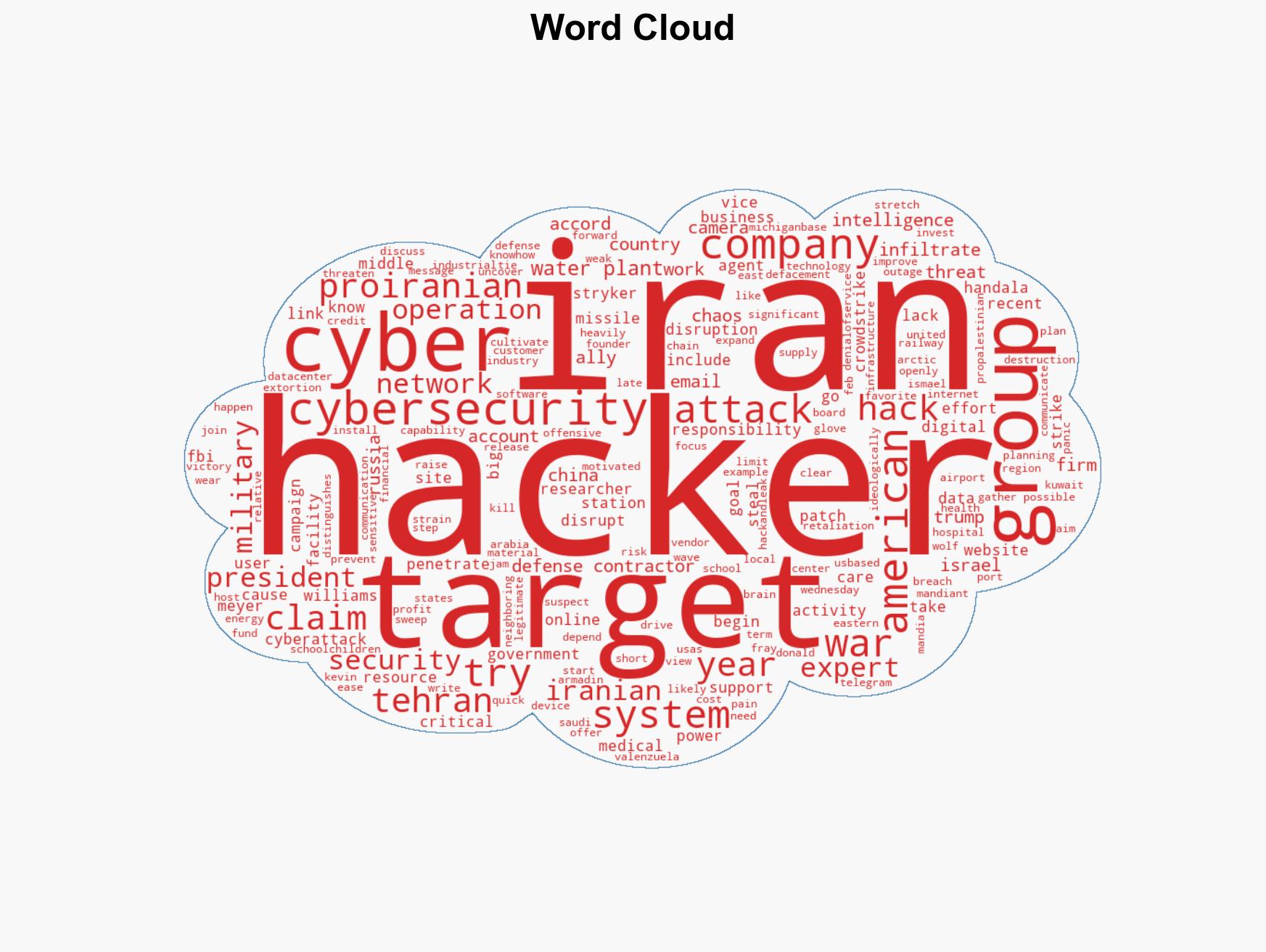
cybersecurity, Iran, critical infrastructure, cyber-espionage, geopolitical tensions, cyber warfare, national security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us