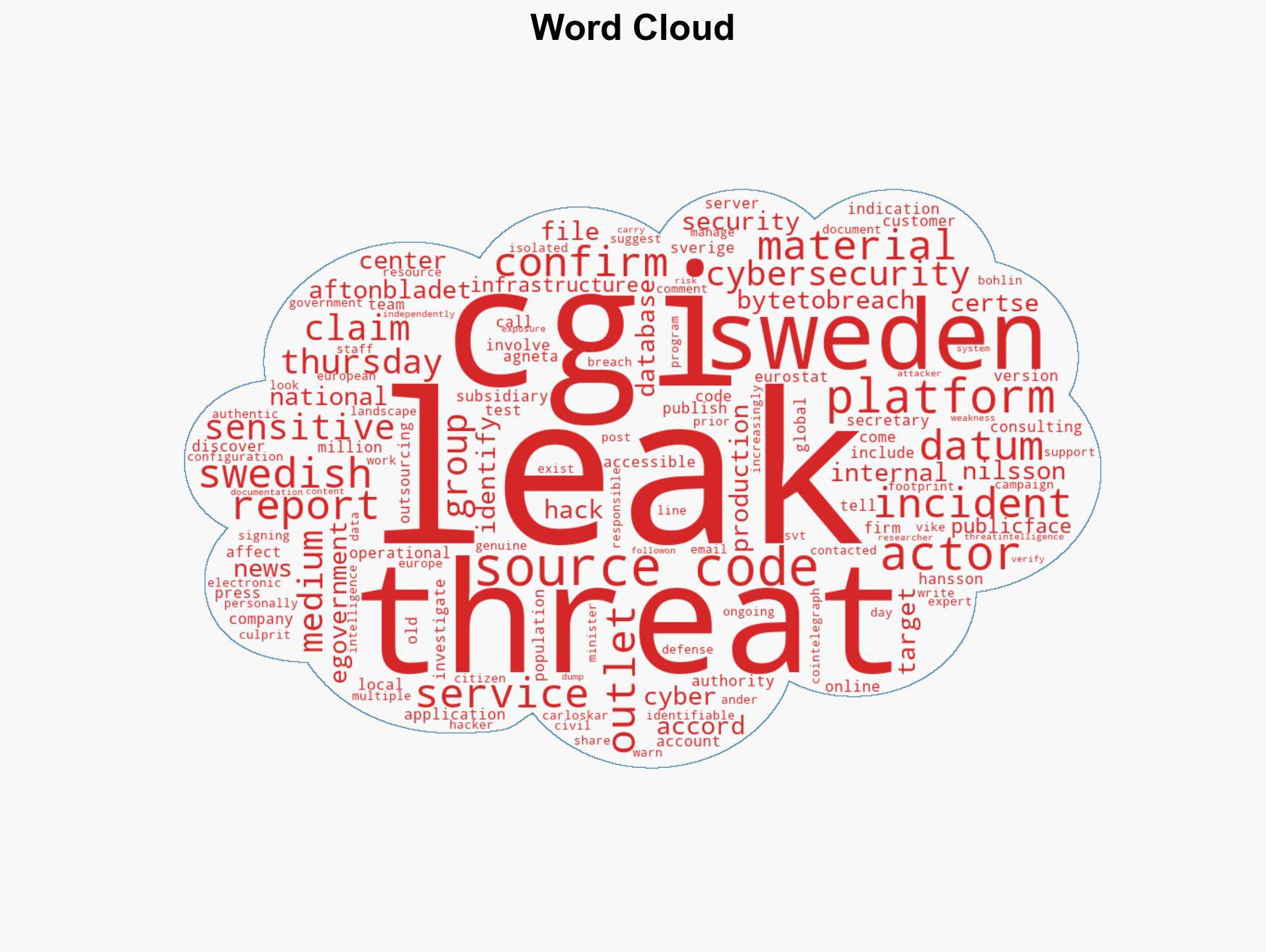
Swedish authorities investigate potential leak of e-government platform source code by threat actor ByteToBre…
Published on: 2026-03-13
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Sweden probes reported leak of e-government platform source code
1. BLUF (Bottom Line Up Front)
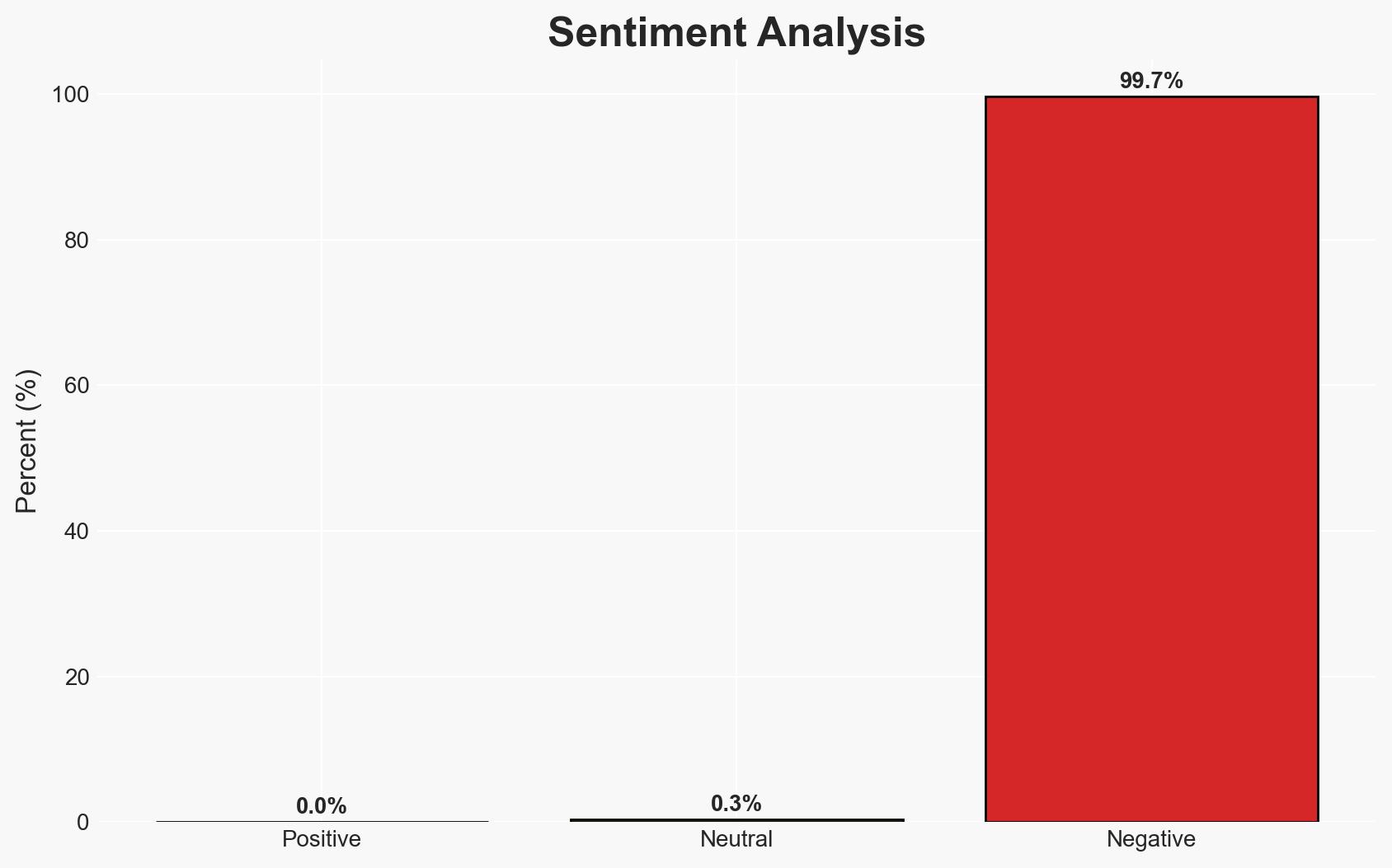
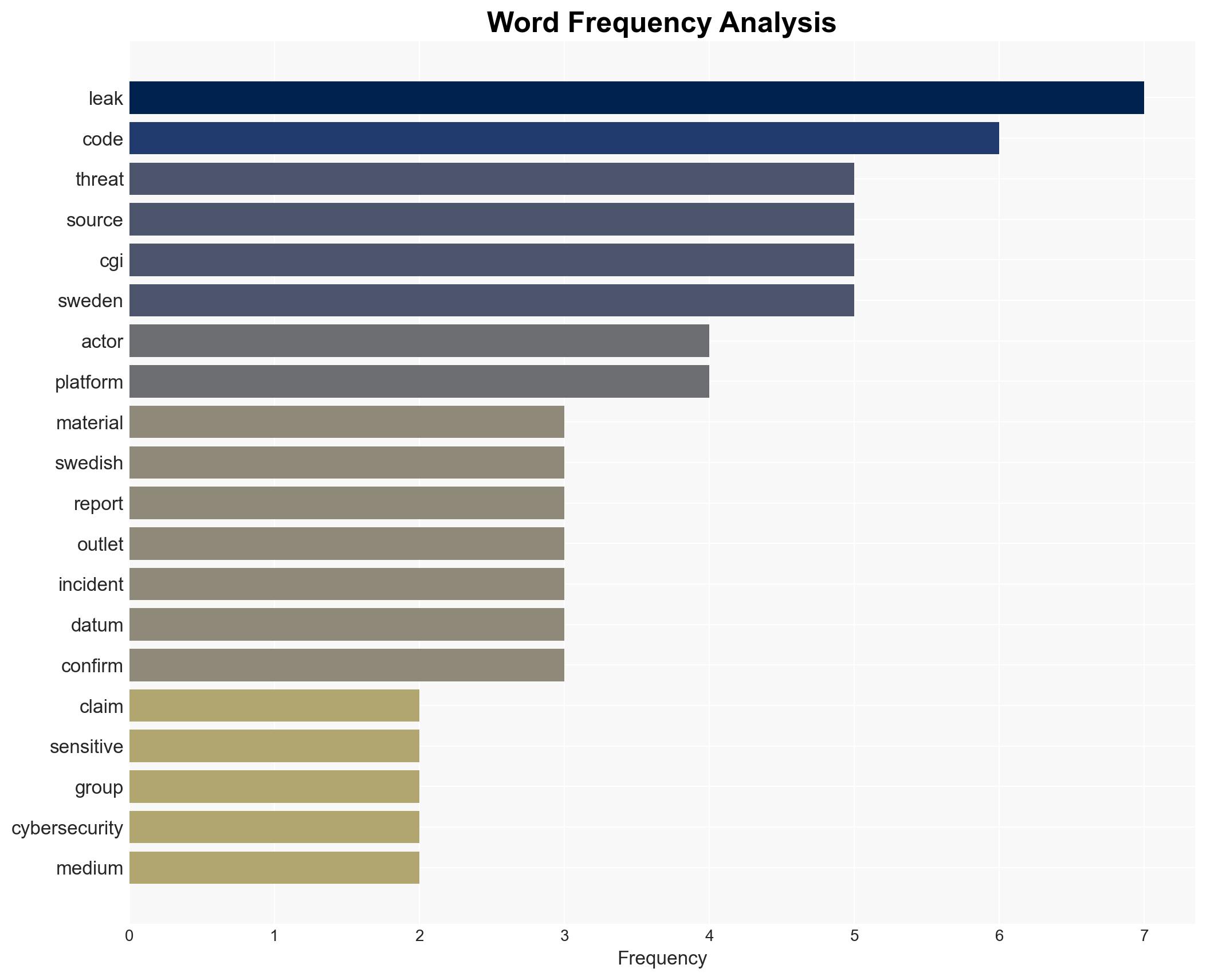
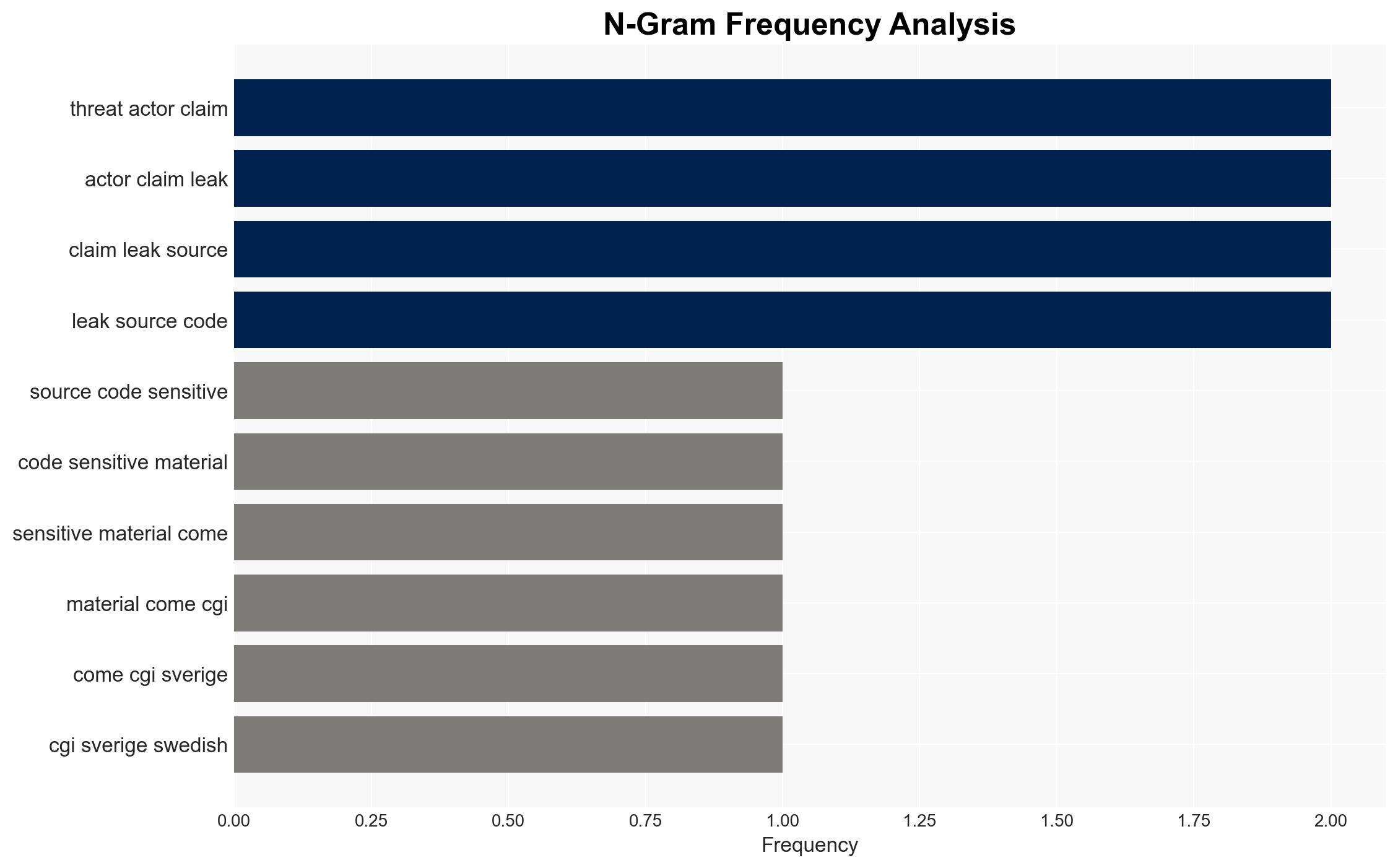
The reported leak of source code from CGI Sverige, potentially involving Sweden’s e-government platform, poses significant cybersecurity and national security risks. The claim by the threat actor ByteToBreach, if verified, could expose vulnerabilities in public-facing systems. The Swedish government is actively investigating, indicating a serious response. Overall confidence in the assessment is moderate due to incomplete verification of the leaked materials.
2. Competing Hypotheses
- Hypothesis A: The leak is genuine, and ByteToBreach has successfully accessed and distributed sensitive source code from CGI Sverige. Supporting evidence includes the confirmation of an incident by CGI and the apparent authenticity of the materials as noted by IT security expert Anders Nilsson. However, the full contents of the leak remain unverified, creating uncertainty.
- Hypothesis B: The leak is exaggerated or fabricated, possibly as a deception tactic by ByteToBreach to create disruption or gain notoriety. Contradicting evidence includes the lack of independent verification of the full data dump and potential motives for deception.
- Assessment: Hypothesis A is currently better supported due to the corroboration by multiple sources, including CGI’s acknowledgment of an incident. Indicators that could shift this judgment include independent verification of the leaked data’s contents or discovery of evidence indicating a hoax.
3. Key Assumptions and Red Flags
- Assumptions: The leaked data includes sensitive information relevant to Sweden’s e-government platform; CGI’s internal security measures were bypassed; ByteToBreach has the capability to exploit the leaked data.
- Information Gaps: Full verification of the leaked data’s contents; the extent of potential vulnerabilities exposed by the leak; the identity and motivations of ByteToBreach.
- Bias & Deception Risks: Potential bias in media reporting; possible exaggeration by ByteToBreach to enhance their perceived threat level; risk of confirmation bias in initial assessments.
4. Implications and Strategic Risks
This development could lead to increased cyber threats against Swedish and European infrastructure, impacting national security and public trust in digital services. The incident may prompt a reevaluation of cybersecurity protocols and collaboration among European nations.
- Political / Geopolitical: Potential for diplomatic tensions if foreign actors are involved; increased scrutiny on international cybersecurity cooperation.
- Security / Counter-Terrorism: Heightened alert for further cyber-attacks; potential exploitation by terrorist groups of exposed vulnerabilities.
- Cyber / Information Space: Increased cyber defense measures; potential for further data breaches if vulnerabilities are not addressed.
- Economic / Social: Possible economic impact from disrupted services; erosion of public confidence in digital governance.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a thorough forensic analysis of the breach; enhance monitoring of critical infrastructure; engage with international cybersecurity partners for support.
- Medium-Term Posture (1–12 months): Strengthen cybersecurity frameworks; invest in staff training and awareness; develop contingency plans for potential future breaches.
- Scenario Outlook:
- Best Case: Leak is contained with minimal impact; vulnerabilities are patched swiftly.
- Worst Case: Widespread exploitation of vulnerabilities leads to significant disruptions and economic damage.
- Most-Likely: Moderate disruptions occur, prompting increased cybersecurity measures and international cooperation.
6. Key Individuals and Entities
- ByteToBreach (threat actor)
- CGI Sverige (Swedish subsidiary of CGI Group)
- Anders Nilsson (IT security expert)
- Carl-Oskar Bohlin (Sweden’s minister of civil defense)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, data breach, national security, e-government, cyber threat, Sweden, information security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us