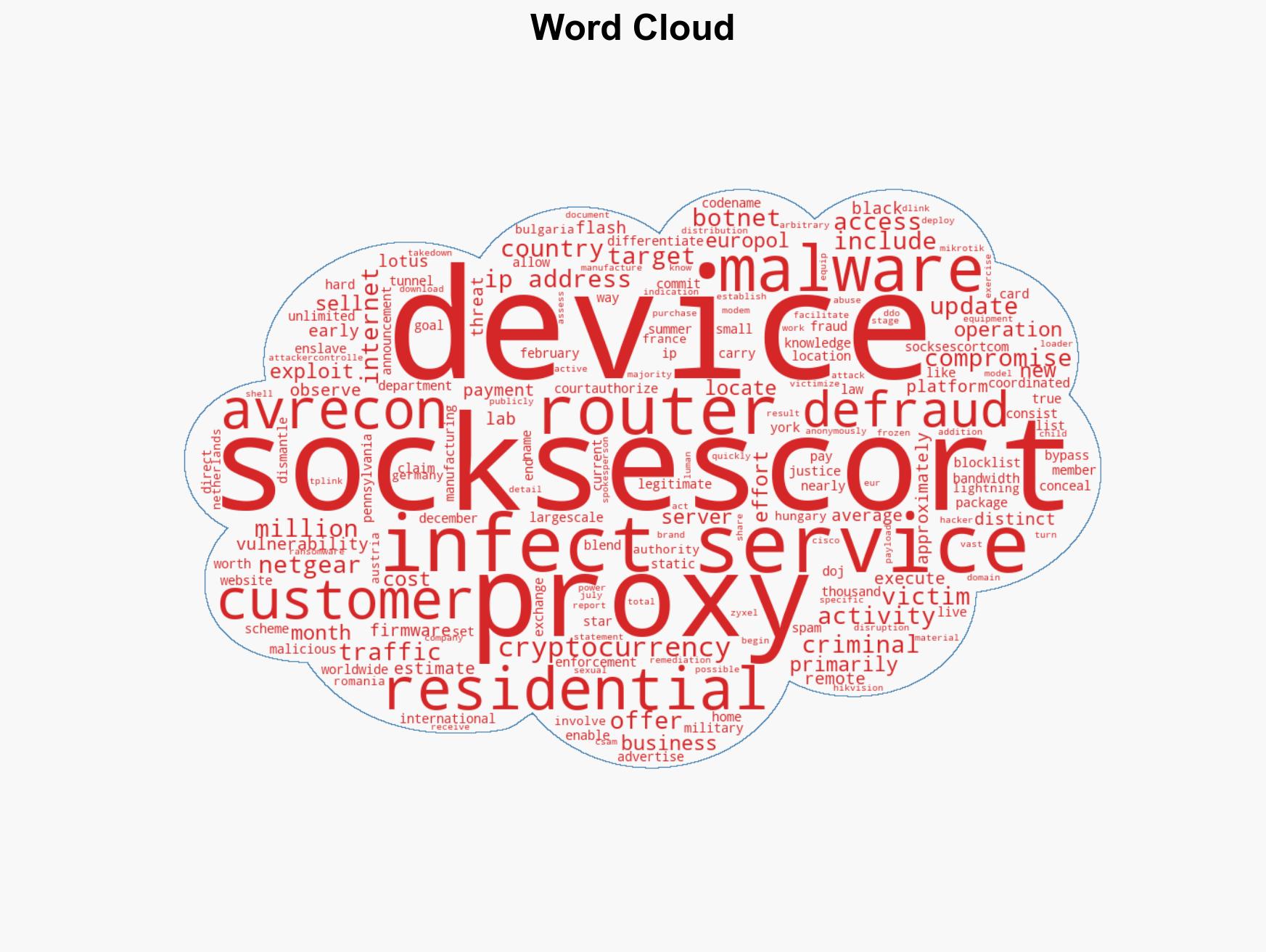
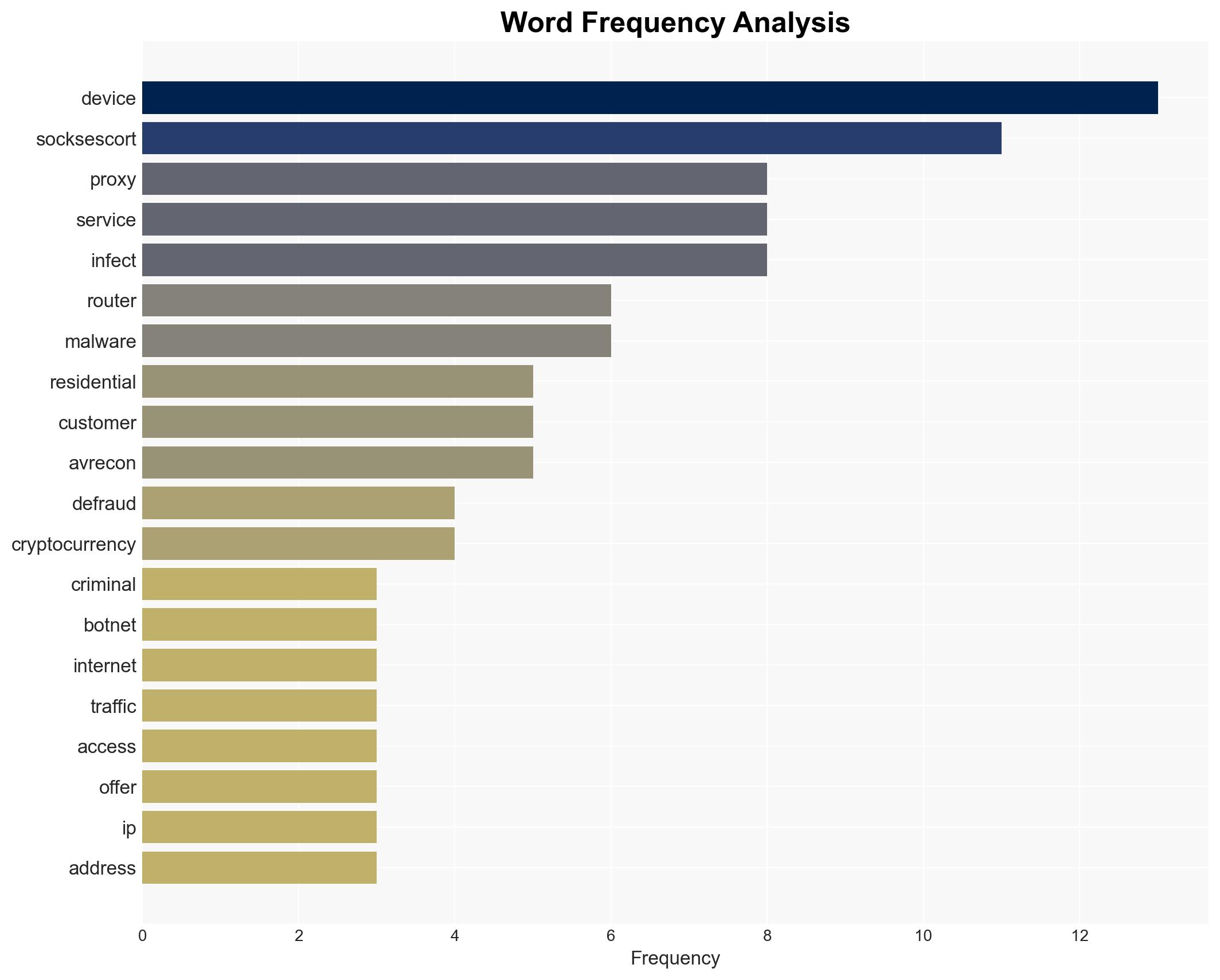
International Law Enforcement Takes Down SocksEscort Botnet Utilizing 369,000 IPs Across 163 Nations
Published on: 2026-03-13
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Authorities Disrupt SocksEscort Proxy Botnet Exploiting 369000 IPs Across 163 Countries
1. BLUF (Bottom Line Up Front)
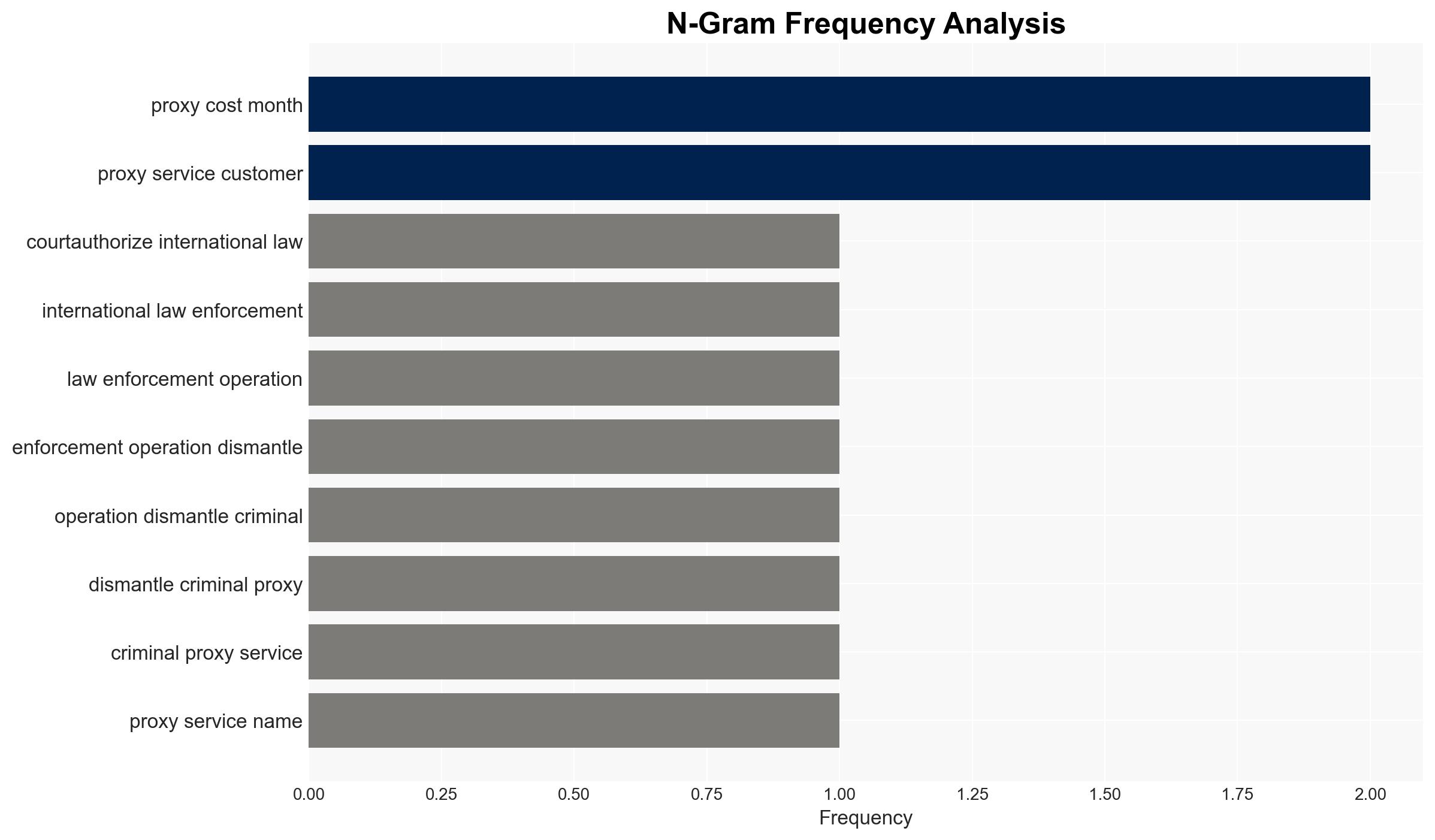
An international law enforcement operation has dismantled the SocksEscort proxy botnet, which exploited 369,000 IPs across 163 countries for criminal activities, including fraud and cyberattacks. This disruption is a significant blow to cybercriminal infrastructure, but the potential for similar networks to emerge remains. Moderate confidence in the assessment due to incomplete data on the full scope of the network’s operations and potential residual threats.
2. Competing Hypotheses
- Hypothesis A: The dismantling of SocksEscort has significantly weakened global cybercriminal capabilities, reducing immediate threats from this network. Supporting evidence includes the takedown of 34 domains and 23 servers, and the freezing of $3.5 million in cryptocurrency. However, uncertainty remains about the full extent of the network’s reach and other undetected nodes.
- Hypothesis B: Despite the disruption, similar proxy networks will quickly fill the void left by SocksEscort, maintaining the level of threat. This is supported by the persistent demand for anonymized internet traffic services and the relatively low cost and technical barriers to establishing such networks. Contradicting evidence includes the significant resources and coordination required to replicate SocksEscort’s scale.
- Assessment: Hypothesis A is currently better supported due to the immediate impact of the operation and the resources seized. However, indicators such as the emergence of new proxy services or increased cybercriminal activity could shift this judgment towards Hypothesis B.
3. Key Assumptions and Red Flags
- Assumptions: The operation has effectively dismantled the central infrastructure of SocksEscort; the demand for such services will not immediately lead to the creation of an equally large network; law enforcement will continue to monitor and respond to emerging threats.
- Information Gaps: Details on the specific vulnerabilities exploited in the routers, the identity of key operators behind SocksEscort, and the full list of affected victims and their losses.
- Bias & Deception Risks: Potential underestimation of the network’s resilience or the operators’ ability to reconstitute operations; reliance on law enforcement sources may introduce bias if not cross-verified with independent cyber threat intelligence.
4. Implications and Strategic Risks
The dismantling of SocksEscort may temporarily disrupt cybercriminal activities but could lead to adaptive strategies by threat actors. The operation highlights the ongoing vulnerabilities in consumer-grade network devices.
- Political / Geopolitical: Strengthened international cooperation in cybercrime enforcement could enhance diplomatic relations but may also provoke retaliatory cyber activities from affected criminal networks.
- Security / Counter-Terrorism: Reduced capability for cybercriminals to conduct large-scale fraud and cyberattacks; however, potential for increased sophistication in future operations.
- Cyber / Information Space: Increased awareness of vulnerabilities in residential routers; potential for heightened cybersecurity measures and public awareness campaigns.
- Economic / Social: Potential economic impact on businesses previously targeted by SocksEscort; increased consumer demand for secure networking solutions.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of known SocksEscort IPs for residual activity; conduct public awareness campaigns on securing residential routers.
- Medium-Term Posture (1–12 months): Develop partnerships with tech companies to address router vulnerabilities; invest in cyber threat intelligence capabilities to detect emerging proxy networks.
- Scenario Outlook:
- Best: Sustained disruption of proxy networks, leading to a decrease in cybercriminal activities.
- Worst: Rapid emergence of new, more sophisticated proxy networks, maintaining or increasing current threat levels.
- Most-Likely: Gradual reconstitution of similar networks, with intermittent disruptions by law enforcement.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, cybercrime, law enforcement, botnet disruption, international cooperation
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us