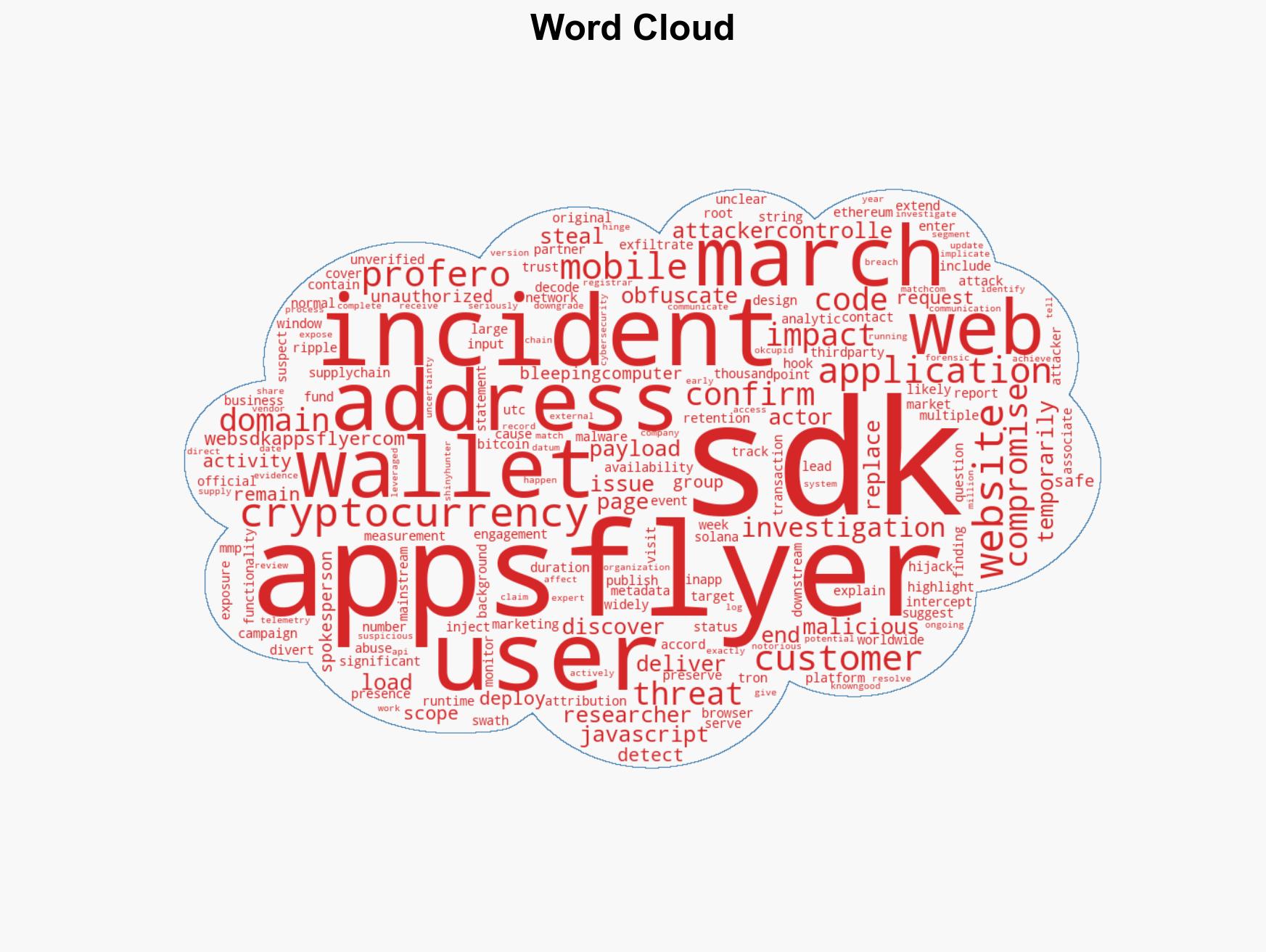
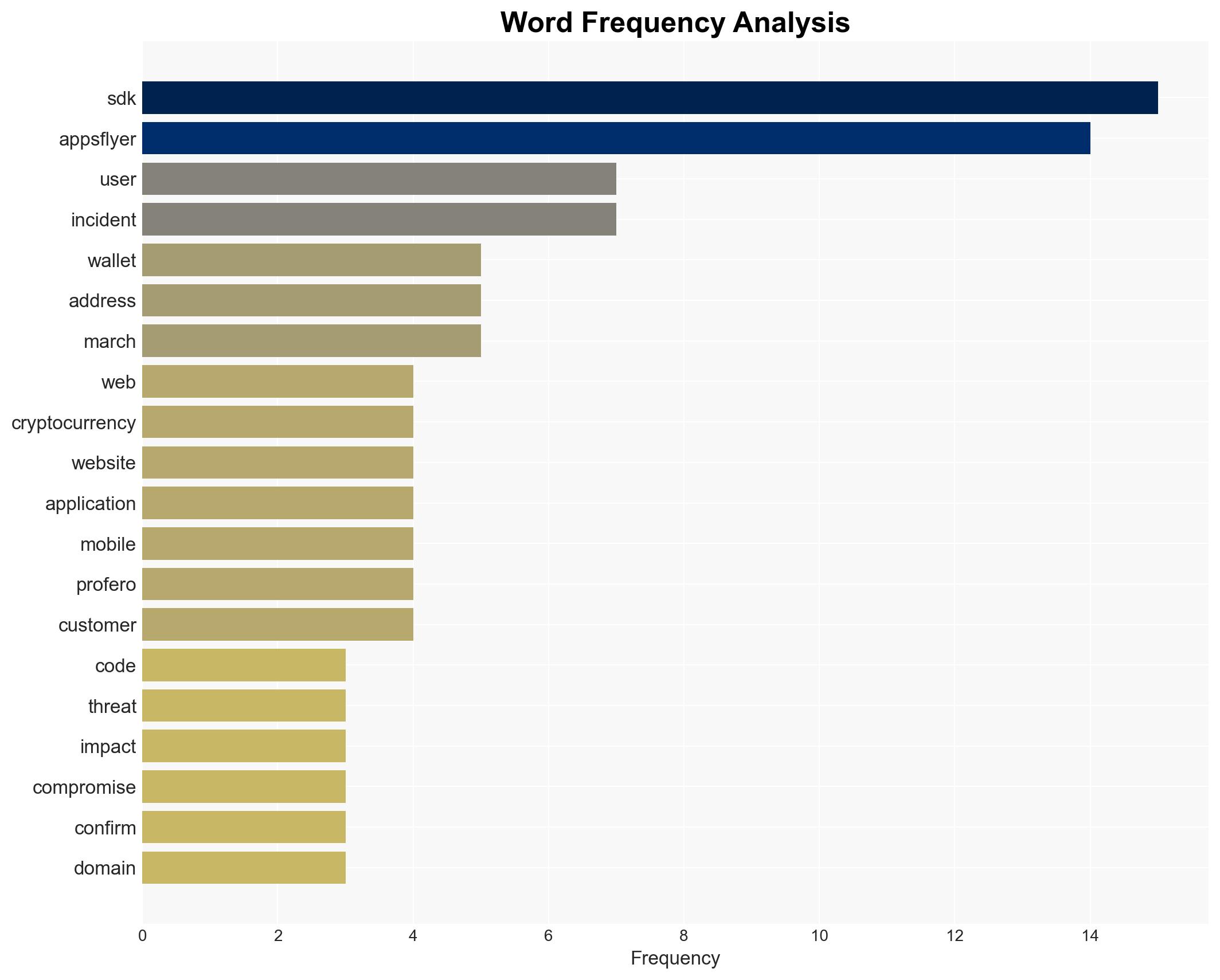
AppsFlyer Web SDK compromised in supply-chain attack to deploy crypto-stealing JavaScript code
Published on: 2026-03-14
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: AppsFlyer Web SDK hijacked to spread crypto-stealing JavaScript code
1. BLUF (Bottom Line Up Front)
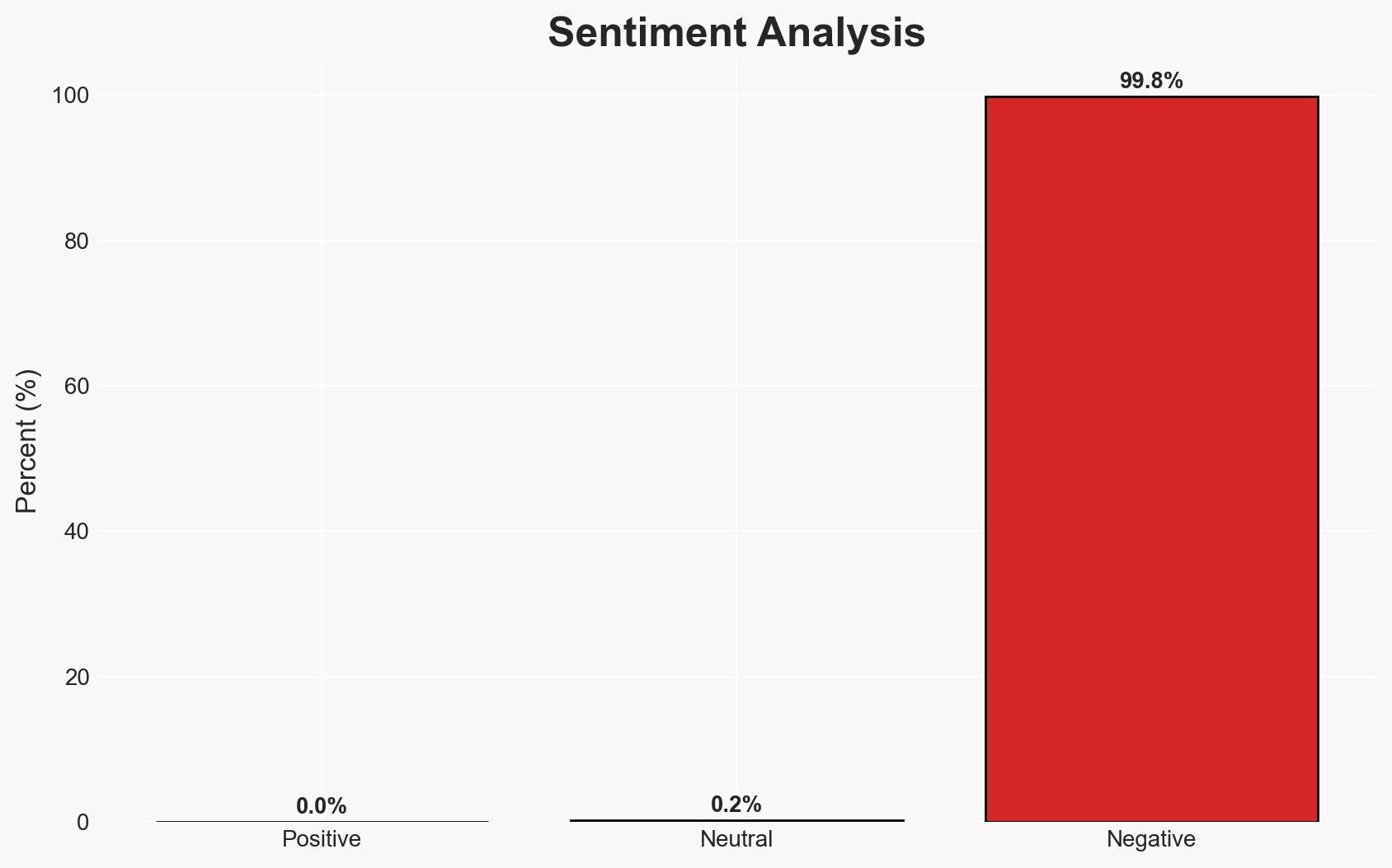
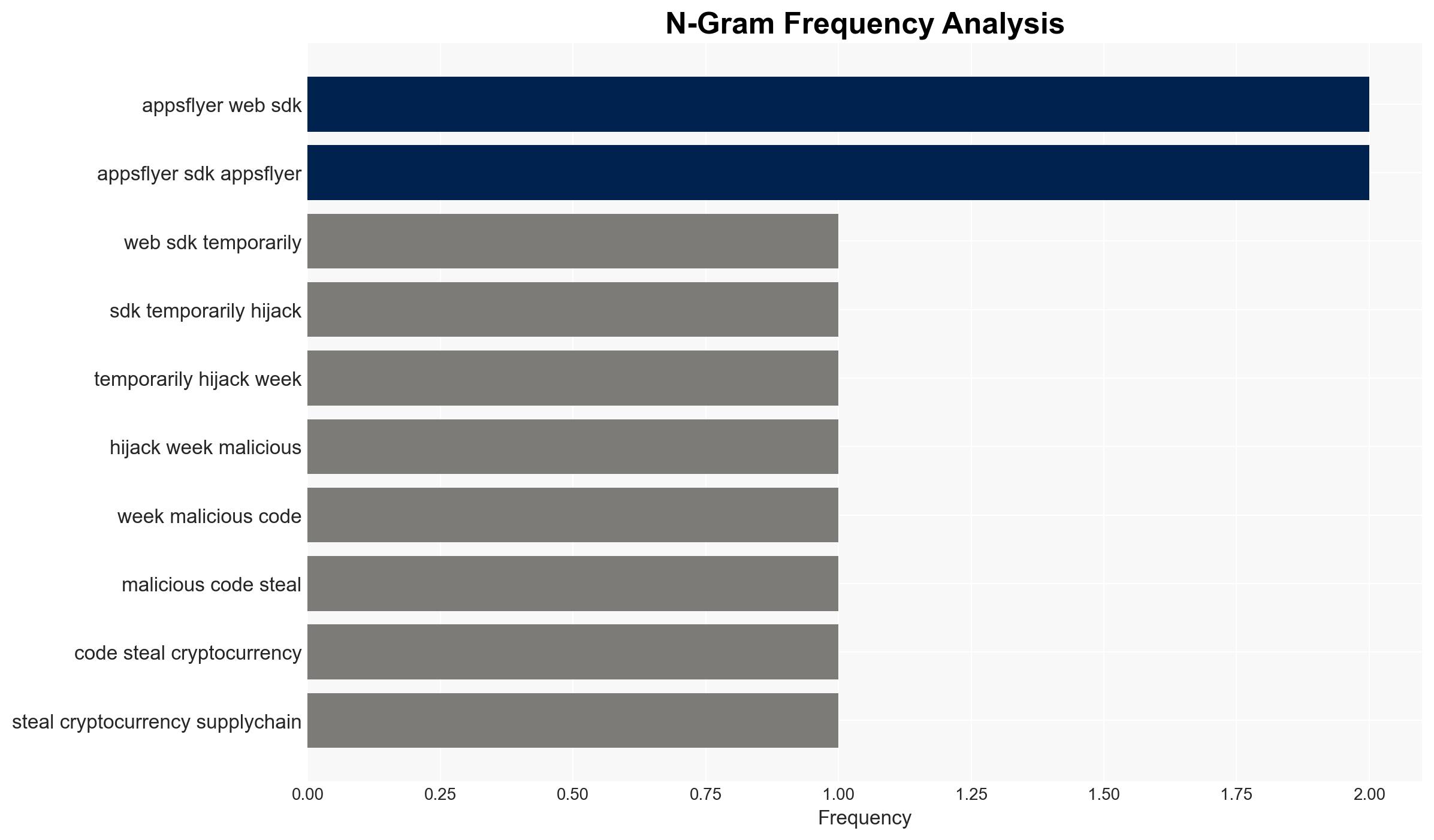
The AppsFlyer Web SDK was compromised in a supply-chain attack, deploying malicious JavaScript to steal cryptocurrency by intercepting wallet addresses. This incident affects thousands of applications and potentially millions of users globally. The most likely hypothesis is that the attack was opportunistic, exploiting a domain registrar vulnerability. Overall confidence in this assessment is moderate due to incomplete information on the attack’s scope and duration.
2. Competing Hypotheses
- Hypothesis A: The attack was opportunistic, exploiting a domain registrar vulnerability to inject malicious code into the AppsFlyer SDK. Supporting evidence includes the timing of the domain availability issue and the rapid containment by AppsFlyer. However, the full scope and duration remain unclear.
- Hypothesis B: The attack was a targeted operation by a sophisticated threat actor aiming to exploit the widespread use of the AppsFlyer SDK for financial gain. This is contradicted by the lack of evidence suggesting a broader strategic objective beyond financial theft.
- Assessment: Hypothesis A is currently better supported due to the nature of the domain registrar issue and the absence of indicators suggesting a targeted campaign. Key indicators that could shift this judgment include evidence of coordination with other cyber operations or a pattern of similar attacks.
3. Key Assumptions and Red Flags
- Assumptions: The attack was limited to the Web SDK; the mobile SDK was unaffected. The malicious code was primarily aimed at financial theft rather than broader espionage or disruption.
- Information Gaps: Precise details on the duration of the compromise and the number of affected users remain unknown. The identity and motivations of the threat actors are also unclear.
- Bias & Deception Risks: There is a risk of confirmation bias in assuming the attack was opportunistic without considering more complex threat actor strategies. Source bias may exist if AppsFlyer underreports the incident’s impact.
4. Implications and Strategic Risks
The incident underscores vulnerabilities in third-party SDKs and the potential for widespread impact through supply-chain attacks. This could lead to increased scrutiny and regulatory pressure on SDK providers.
- Political / Geopolitical: Potential for increased international cooperation on cybersecurity standards and supply-chain security.
- Security / Counter-Terrorism: Heightened awareness of supply-chain vulnerabilities could lead to improved security protocols among affected businesses.
- Cyber / Information Space: The incident may prompt other threat actors to explore similar vulnerabilities, increasing the frequency of such attacks.
- Economic / Social: Financial losses for users and businesses could erode trust in digital financial transactions and third-party platforms.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct thorough audits of third-party SDKs, enhance monitoring of domain registrar activities, and communicate transparently with affected users.
- Medium-Term Posture (1–12 months): Develop partnerships for information sharing on supply-chain threats, and invest in resilience measures for SDK security.
- Scenario Outlook:
- Best: Improved security measures prevent future incidents, restoring trust.
- Worst: Similar attacks proliferate, causing significant financial and reputational damage.
- Most-Likely: Incremental improvements in security practices reduce but do not eliminate the risk of such attacks.
6. Key Individuals and Entities
- AppsFlyer
- Profero researchers
- BleepingComputer
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, supply-chain attack, cryptocurrency theft, cyber security, SDK vulnerability, financial crime, digital trust, information security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us