Former National Guardsman with ISIS connections kills ROTC instructor at Old Dominion University before being…
Published on: 2026-03-15
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Former National Guard member with ISIS ties killed after opening fire at Old Dominion University
1. BLUF (Bottom Line Up Front)
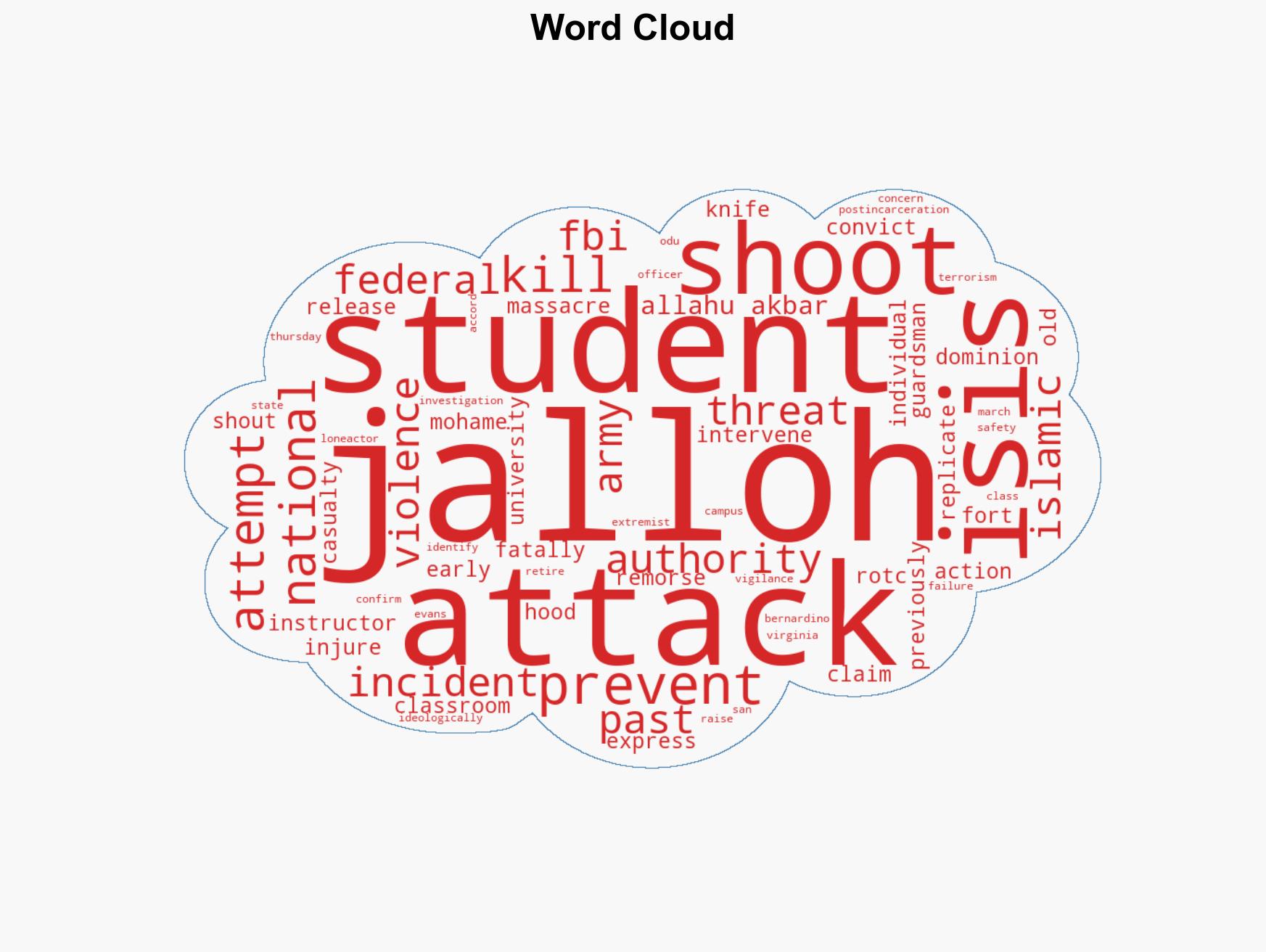
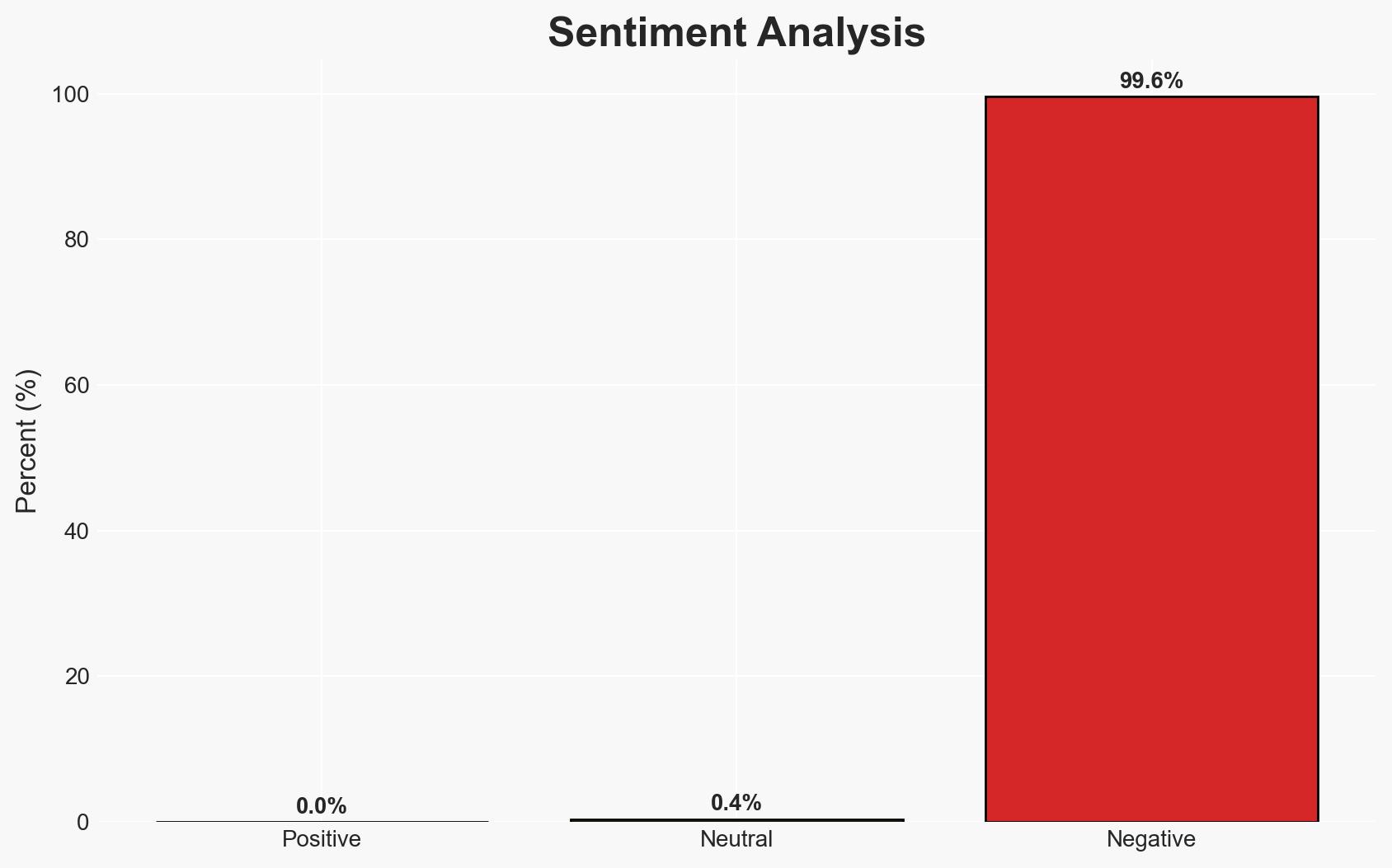
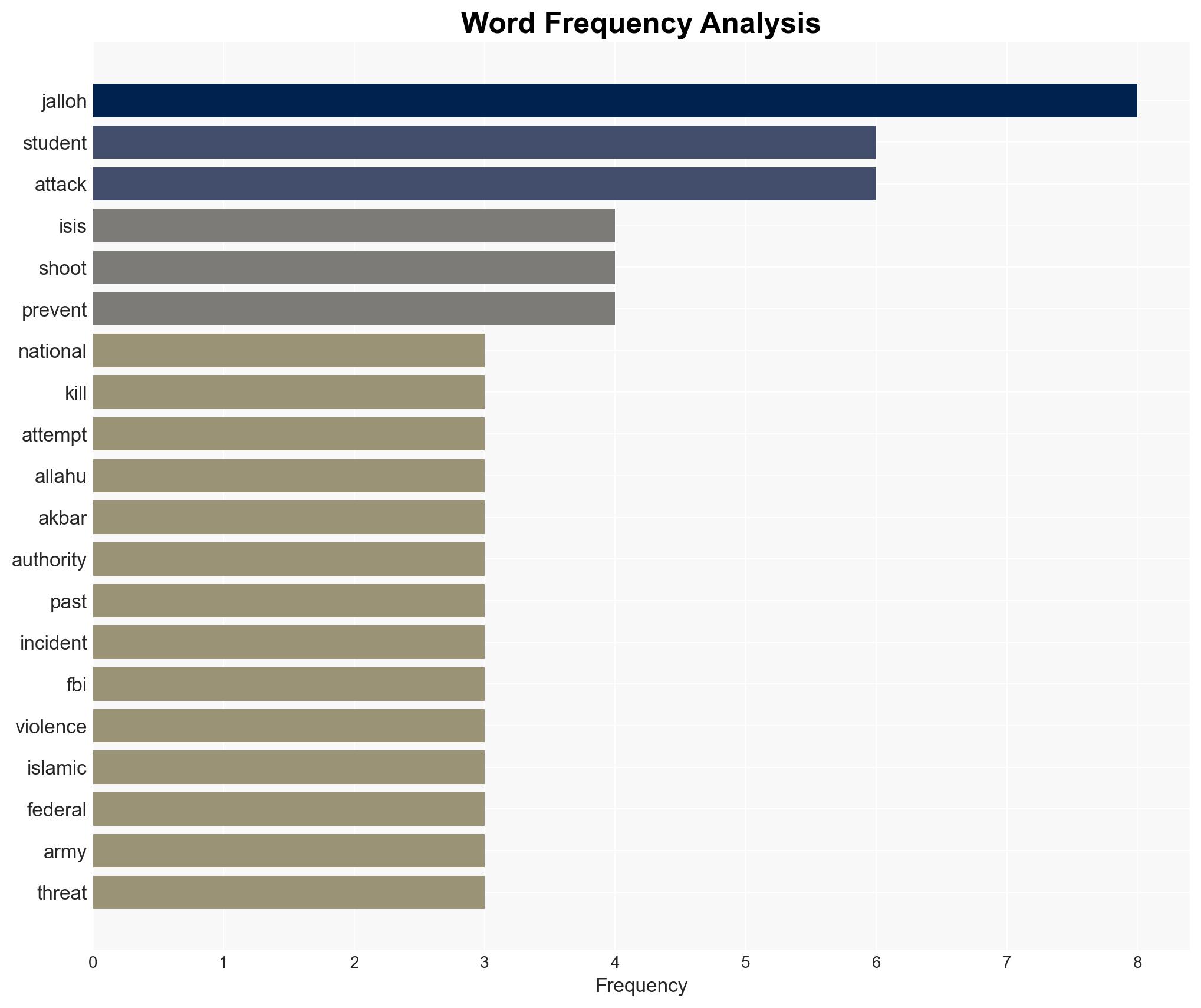
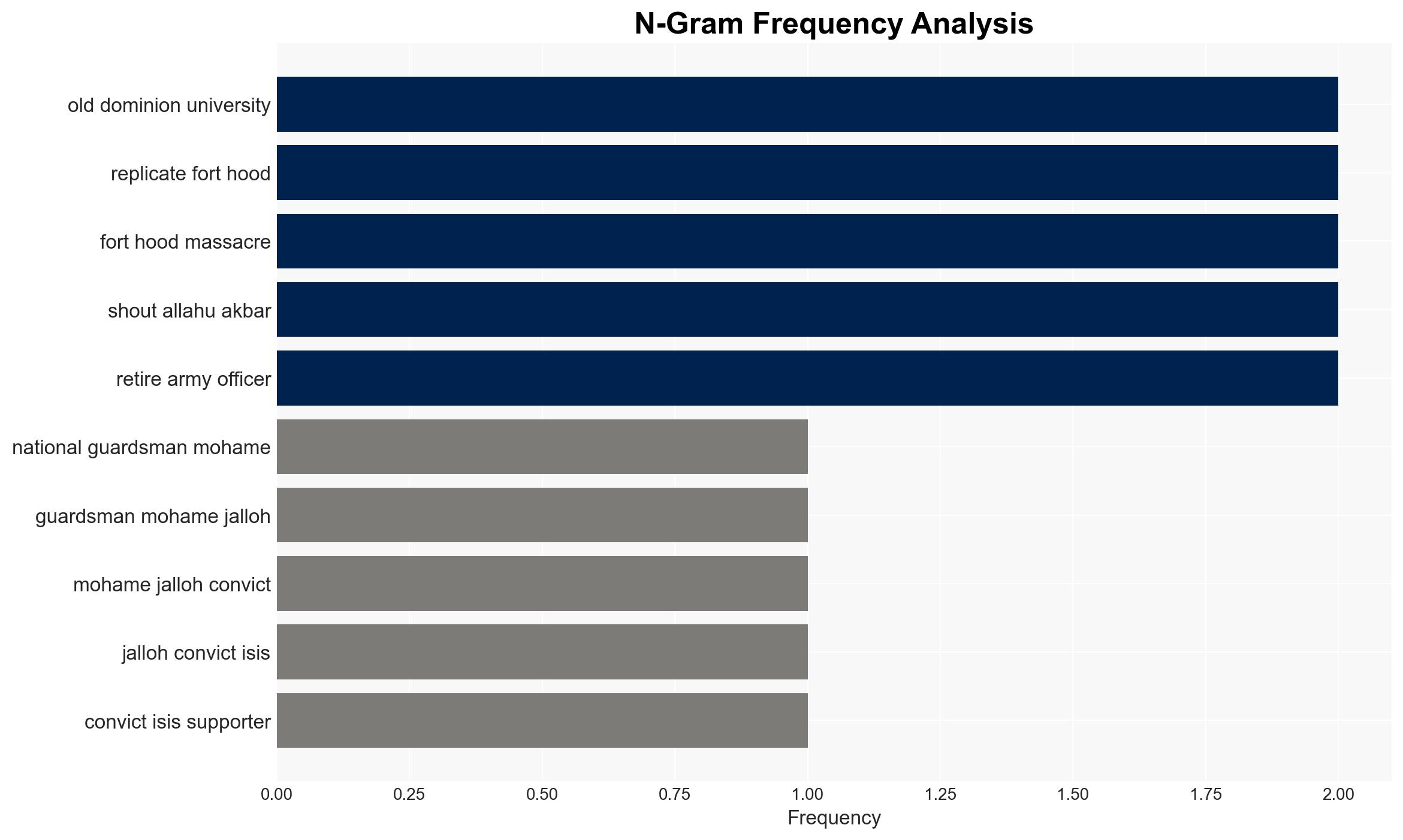
The attack at Old Dominion University by Mohamed Jalloh, a former National Guardsman with ISIS ties, underscores significant gaps in monitoring radicalized individuals post-incarceration. The incident highlights the persistent threat of lone-actor terrorism and the challenges in ensuring campus safety. This assessment is made with moderate confidence, considering the available information and existing uncertainties.
2. Competing Hypotheses
- Hypothesis A: Jalloh acted independently, motivated by personal grievances and extremist ideology, without direct operational support from ISIS. This is supported by the lack of evidence linking him to current ISIS operations and his history of expressing intent to replicate past attacks. However, uncertainties remain regarding potential online radicalization or indirect encouragement.
- Hypothesis B: Jalloh was part of a broader network or received direct encouragement from ISIS affiliates. This hypothesis is less supported due to the absence of evidence indicating recent contact with ISIS operatives or networks, but cannot be entirely ruled out without further investigation into his communications.
- Assessment: Hypothesis A is currently better supported given the lack of direct links to ISIS and the nature of the attack. Indicators such as digital communication records or financial transactions could shift this judgment if they reveal external influence.
3. Key Assumptions and Red Flags
- Assumptions: Jalloh acted alone; his early release did not involve comprehensive risk assessment; campus security protocols were insufficient to prevent the attack.
- Information Gaps: Details on Jalloh’s communications and activities post-release; the extent of his ideological commitment and potential contacts with extremist networks.
- Bias & Deception Risks: Potential bias in interpreting Jalloh’s motives based on his past convictions; risk of overestimating the role of ISIS without concrete evidence.
4. Implications and Strategic Risks
This incident may lead to increased scrutiny of post-incarceration monitoring practices and campus security measures. It could also influence public perception of domestic terrorism threats.
- Political / Geopolitical: Potential for policy debates on counter-terrorism and criminal justice reform.
- Security / Counter-Terrorism: Heightened alertness to lone-actor threats and potential copycat incidents.
- Cyber / Information Space: Possible exploitation of the incident by extremist groups for propaganda purposes.
- Economic / Social: Increased anxiety and demand for security measures on campuses, potentially affecting enrollment and campus life.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of released individuals with extremist ties; review and strengthen campus security protocols.
- Medium-Term Posture (1–12 months): Develop partnerships between educational institutions and law enforcement for threat assessments; invest in deradicalization programs.
- Scenario Outlook:
- Best: Improved monitoring prevents similar incidents, leading to enhanced public safety.
- Worst: Failure to address gaps results in further attacks, increasing public fear and policy overreach.
- Most-Likely: Incremental improvements in monitoring and security, with ongoing challenges in balancing security and civil liberties.
6. Key Individuals and Entities
- Mohamed Jalloh – Former National Guardsman and attacker
- Lt. Col. Brandon Shah – Victim, retired Army officer
- FBI – Investigating agency
- Virginia National Guard – Jalloh’s former affiliation
- Old Dominion University – Location of the incident
7. Thematic Tags
Counter-Terrorism, lone-actor terrorism, campus security, radicalization, ISIS, post-incarceration monitoring, domestic extremism
Structured Analytic Techniques Applied
- ACH 2.0: Reconstruct likely threat actor intentions via hypothesis testing and structured refutation.
- Indicators Development: Track radicalization signals and propaganda patterns to anticipate operational planning.
- Narrative Pattern Analysis: Analyze spread/adaptation of ideological narratives for recruitment/incitement signals.
Explore more:
Counter-Terrorism Briefs ·
Daily Summary ·
Support us