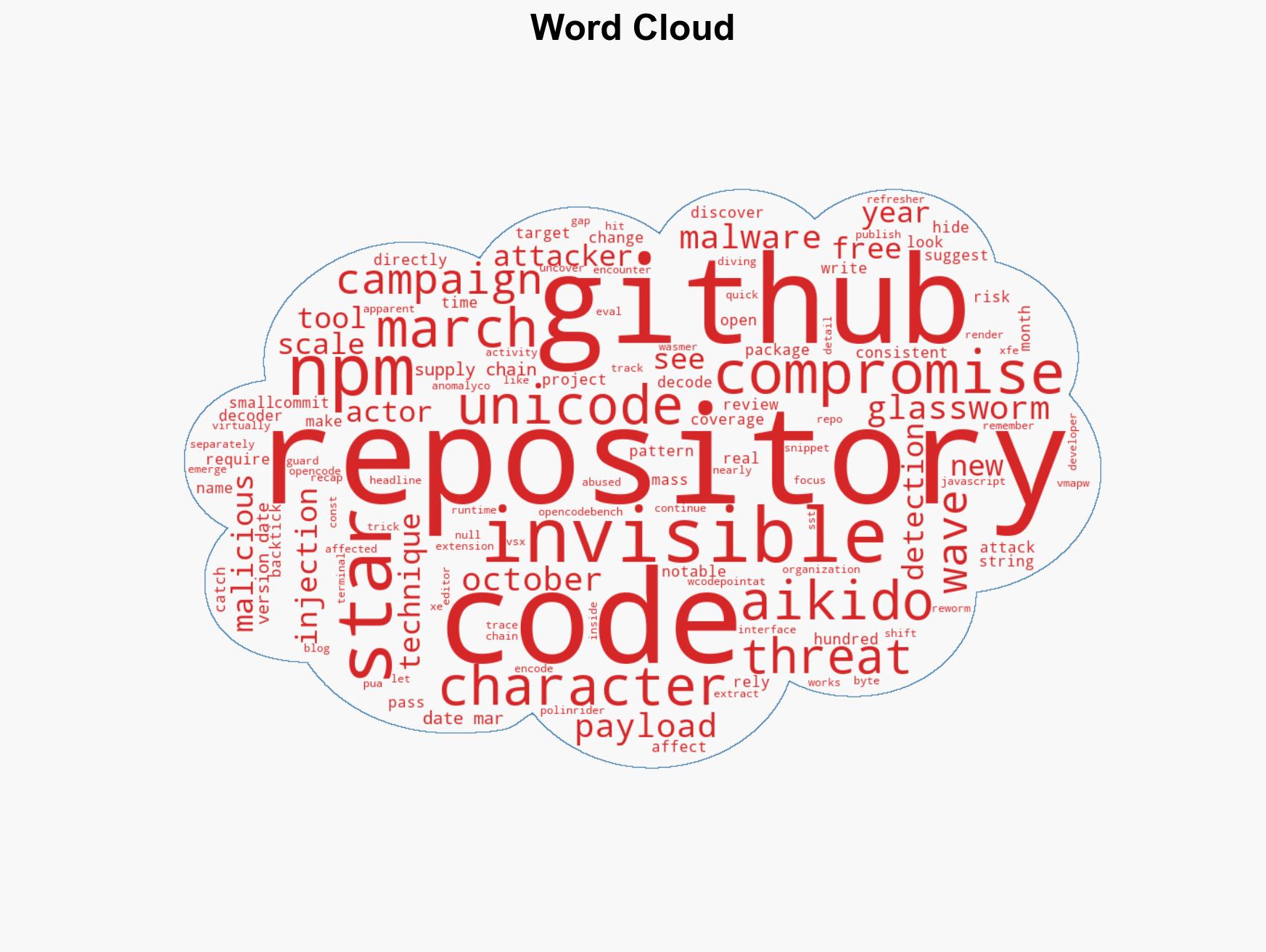
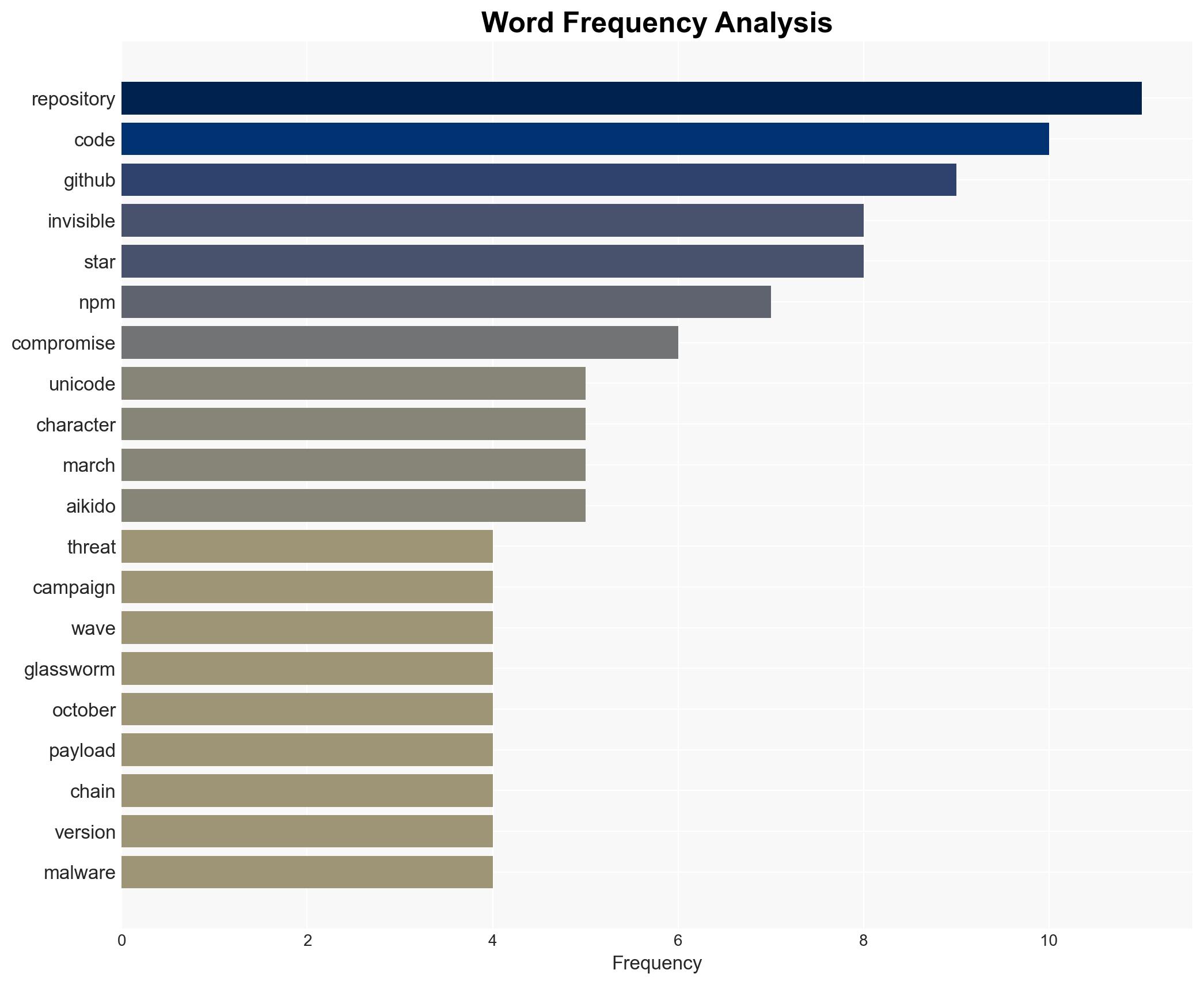
New Surge of Glassworm Attacks Targets GitHub, npm, and VS Code with Invisible Unicode Exploits
Published on: 2026-03-15
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Glassworm Is Back A New Wave of Invisible Unicode Attacks Hits Repositories
1. BLUF (Bottom Line Up Front)
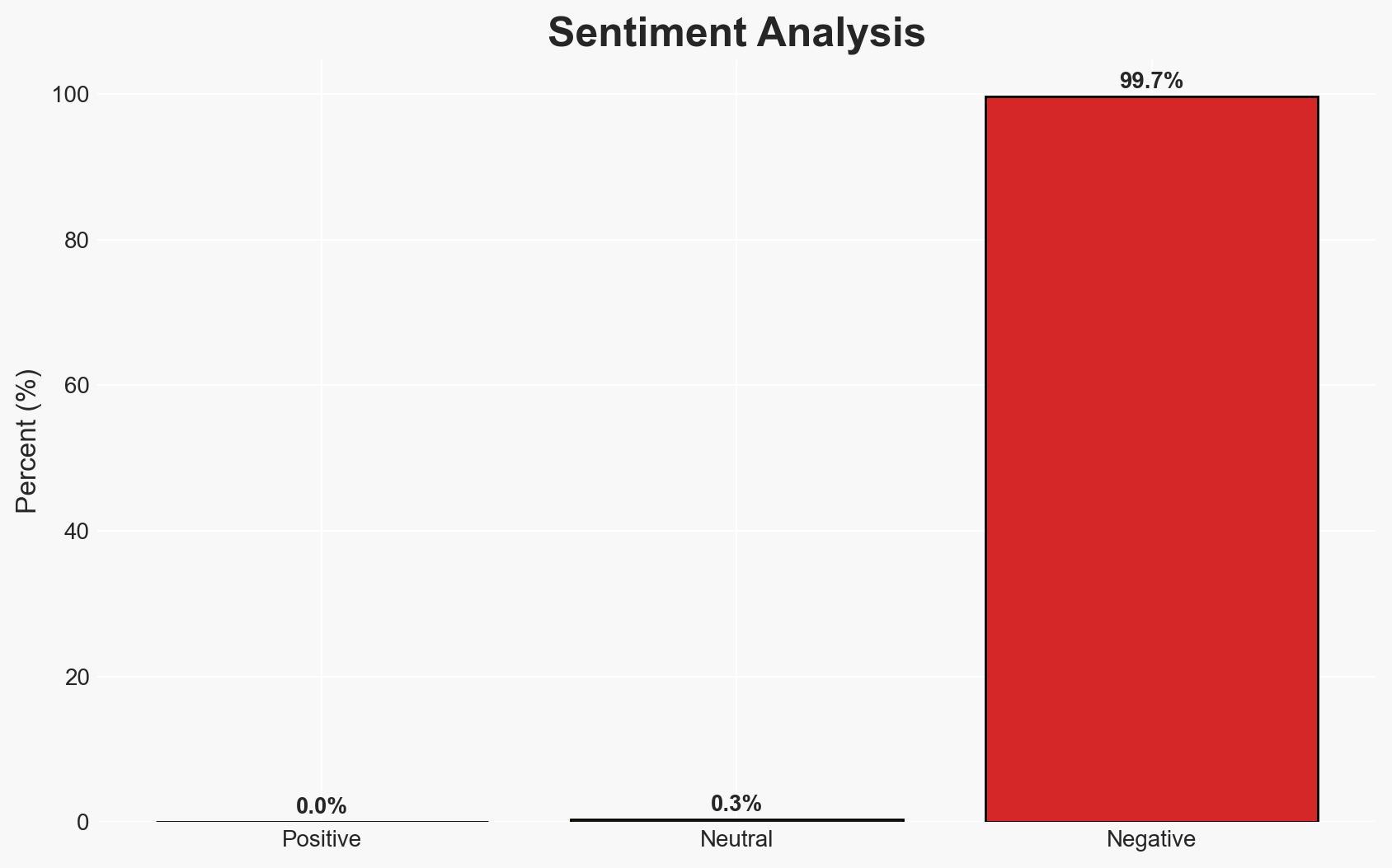
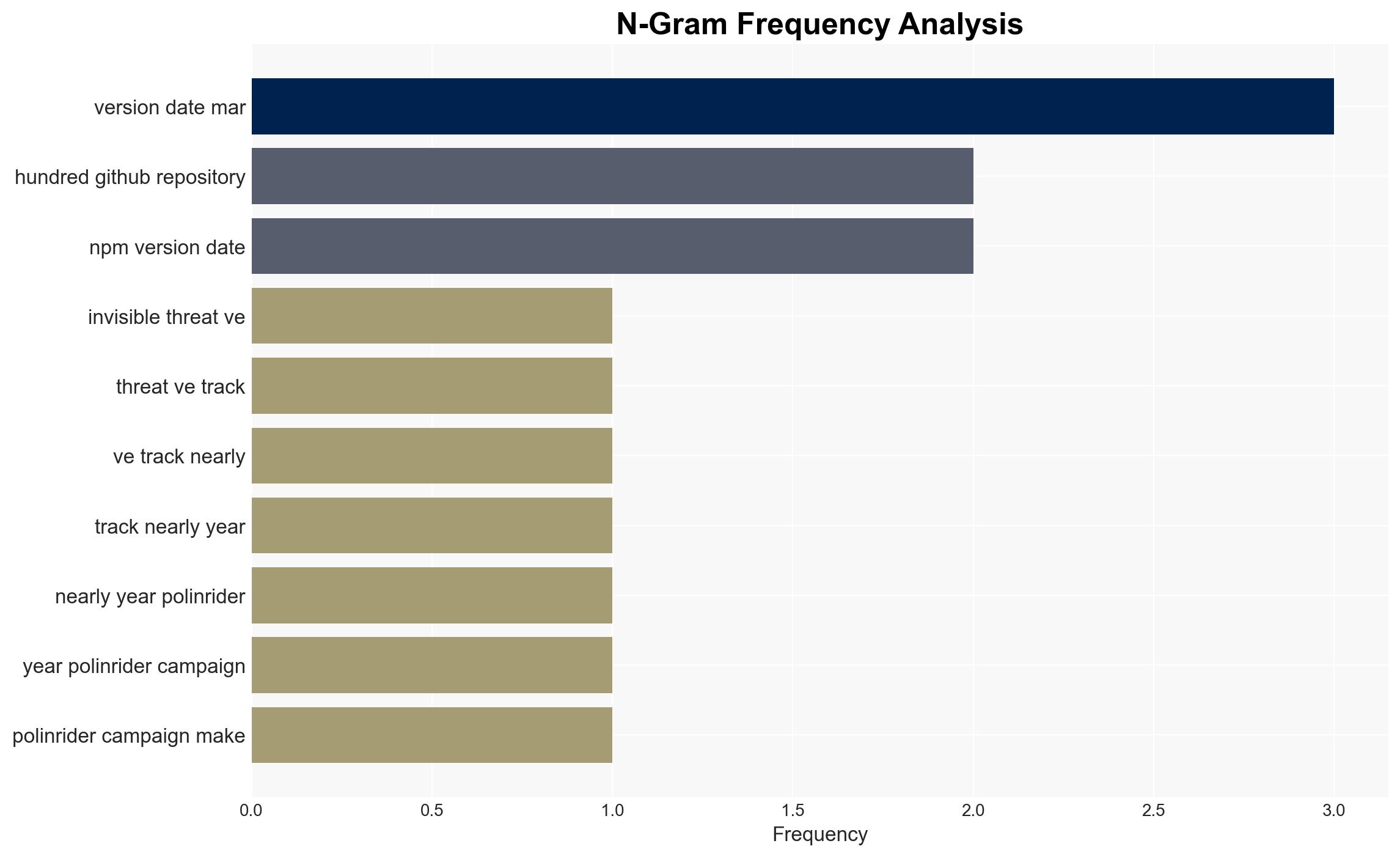
The Glassworm threat actor has launched a new wave of attacks using invisible Unicode characters to compromise open source repositories, notably affecting GitHub, npm, and VS Code. This campaign poses a significant risk to software supply chains and developer environments. The most likely hypothesis is that Glassworm aims to exploit these platforms for broader cyber-espionage or financial gain. Overall confidence in this assessment is moderate due to existing information gaps and potential for deception.
2. Competing Hypotheses
- Hypothesis A: Glassworm is primarily targeting open source repositories to facilitate cyber-espionage, leveraging compromised code to infiltrate larger networks. This is supported by the sophisticated use of invisible Unicode and the targeting of widely used platforms. However, the specific objectives beyond initial compromise remain unclear.
- Hypothesis B: The attacks are financially motivated, aiming to steal credentials and tokens for monetary gain. The use of Solana as a delivery channel for second-stage payloads supports this, but the broad scope of repository compromises suggests a more strategic intent.
- Assessment: Hypothesis A is currently better supported due to the strategic targeting of prominent repositories and the complexity of the attack vector, indicating a higher likelihood of espionage objectives. Indicators such as new targets or changes in payloads could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Glassworm has the capability to maintain and expand its operations; the use of invisible Unicode is a deliberate obfuscation tactic; affected platforms are not fully aware of all compromised repositories.
- Information Gaps: The full extent of compromised repositories and the specific objectives of Glassworm remain unknown; the identity and affiliations of Glassworm are not clearly established.
- Bias & Deception Risks: There is a risk of confirmation bias in attributing all similar attacks to Glassworm; potential for Glassworm to use false flags to mislead attribution efforts.
4. Implications and Strategic Risks
The resurgence of Glassworm’s activities could lead to increased vulnerabilities in software supply chains, affecting both developers and end-users. The campaign’s evolution may influence broader cyber defense strategies and international cybersecurity policies.
- Political / Geopolitical: Potential for increased tensions if state-sponsored links are identified, leading to diplomatic confrontations.
- Security / Counter-Terrorism: Heightened alertness in cybersecurity operations, with possible shifts in resource allocation to counter such threats.
- Cyber / Information Space: Increased scrutiny on open source platforms and potential regulatory responses to enhance security measures.
- Economic / Social: Disruption to businesses relying on compromised software, leading to economic losses and reduced trust in digital infrastructure.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of affected platforms, issue alerts to developers, and collaborate with cybersecurity firms to identify and mitigate threats.
- Medium-Term Posture (1–12 months): Develop resilience measures, strengthen partnerships with tech companies, and invest in research to counter obfuscation techniques.
- Scenario Outlook: Best: Rapid containment and patching of vulnerabilities; Worst: Widespread exploitation leading to significant data breaches; Most-Likely: Continued sporadic attacks with gradual improvements in detection and response.
6. Key Individuals and Entities
- Glassworm (threat actor)
- GitHub (platform)
- npm (platform)
- VS Code (platform)
- Wasmer, Reworm, anomalyco (affected entities)
7. Thematic Tags
cybersecurity, software supply chain, cyber-espionage, open source, invisible Unicode, threat actor, cyber defense
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us