Canada’s Bill C-22 Introduces Comprehensive Metadata Surveillance Provisions for Law Enforcement
Published on: 2026-03-15
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Canada’s Bill C-22 Mandates Mass Metadata Surveillance of Canadians
1. BLUF (Bottom Line Up Front)
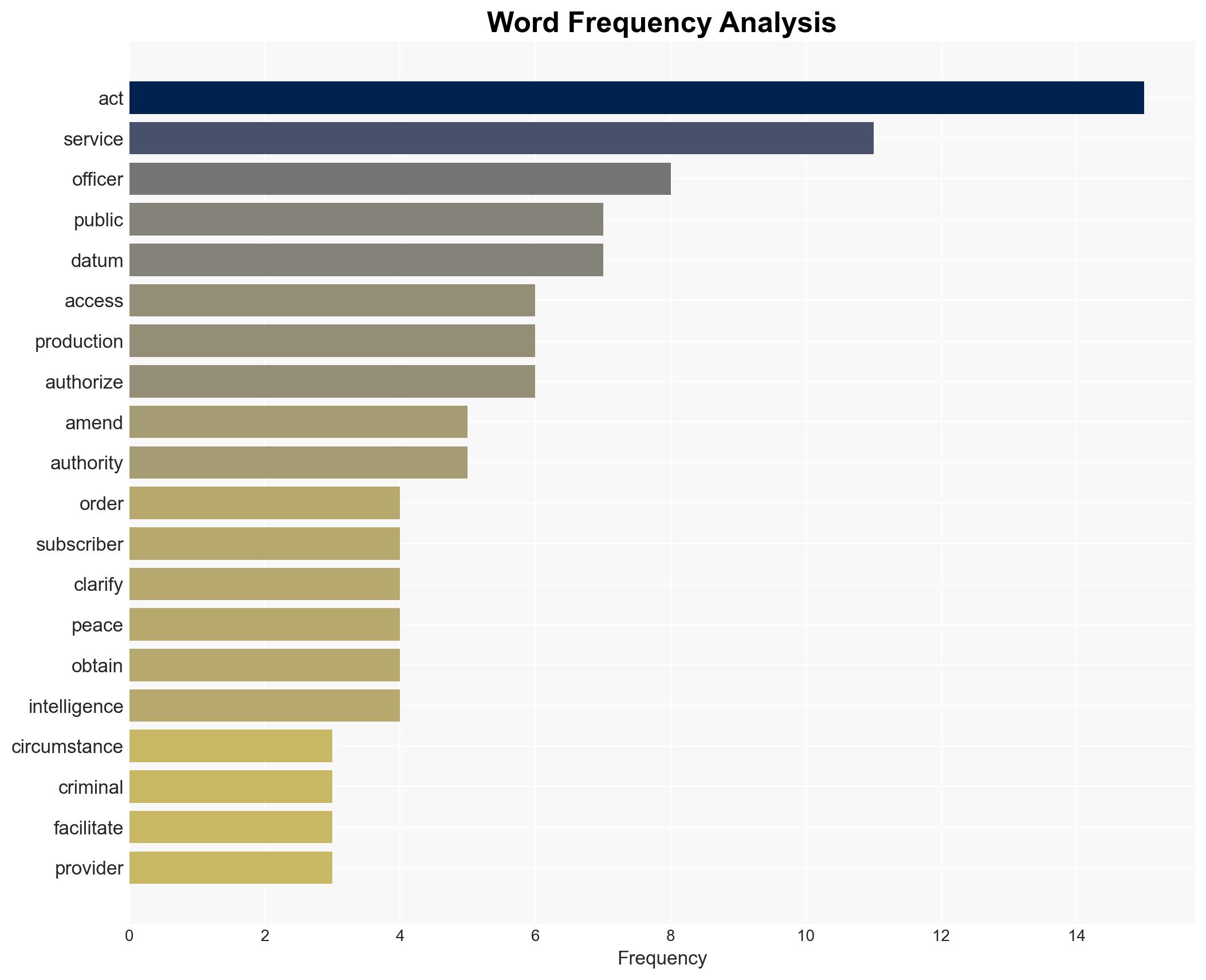
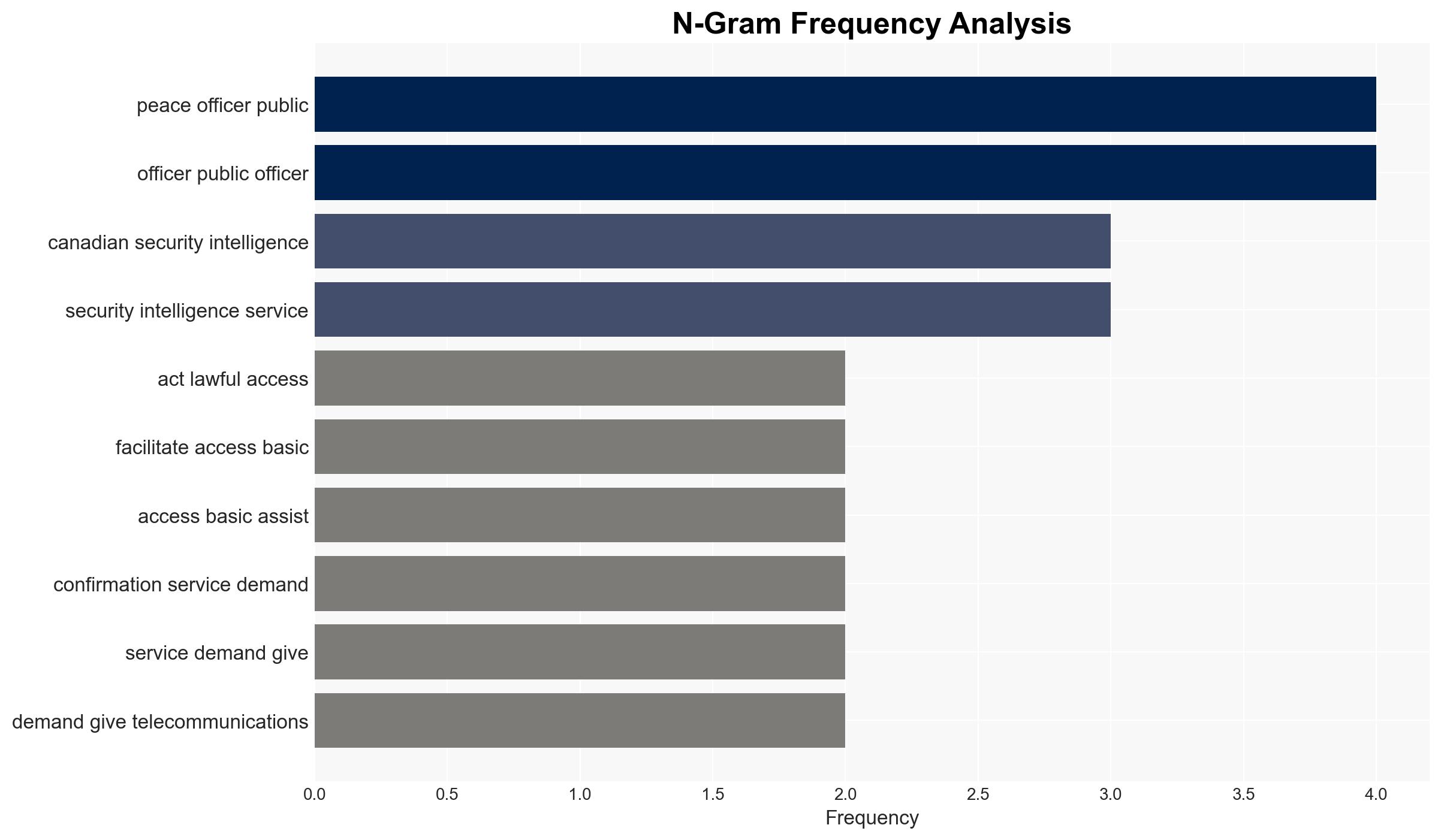
Bill C-22 proposes significant changes to Canadian surveillance laws, expanding the ability of law enforcement and intelligence agencies to access telecommunications metadata. This development is likely to affect privacy rights and operational capabilities of security agencies. The most likely hypothesis is that the bill will enhance investigative efficiency at the cost of increased privacy concerns. Overall confidence in this judgment is moderate due to incomplete information on implementation specifics.
2. Competing Hypotheses
- Hypothesis A: Bill C-22 will primarily enhance national security by streamlining access to critical data for investigations. Supporting evidence includes the bill’s provisions for expedited data access and international cooperation. Key uncertainties involve the potential for misuse and overreach.
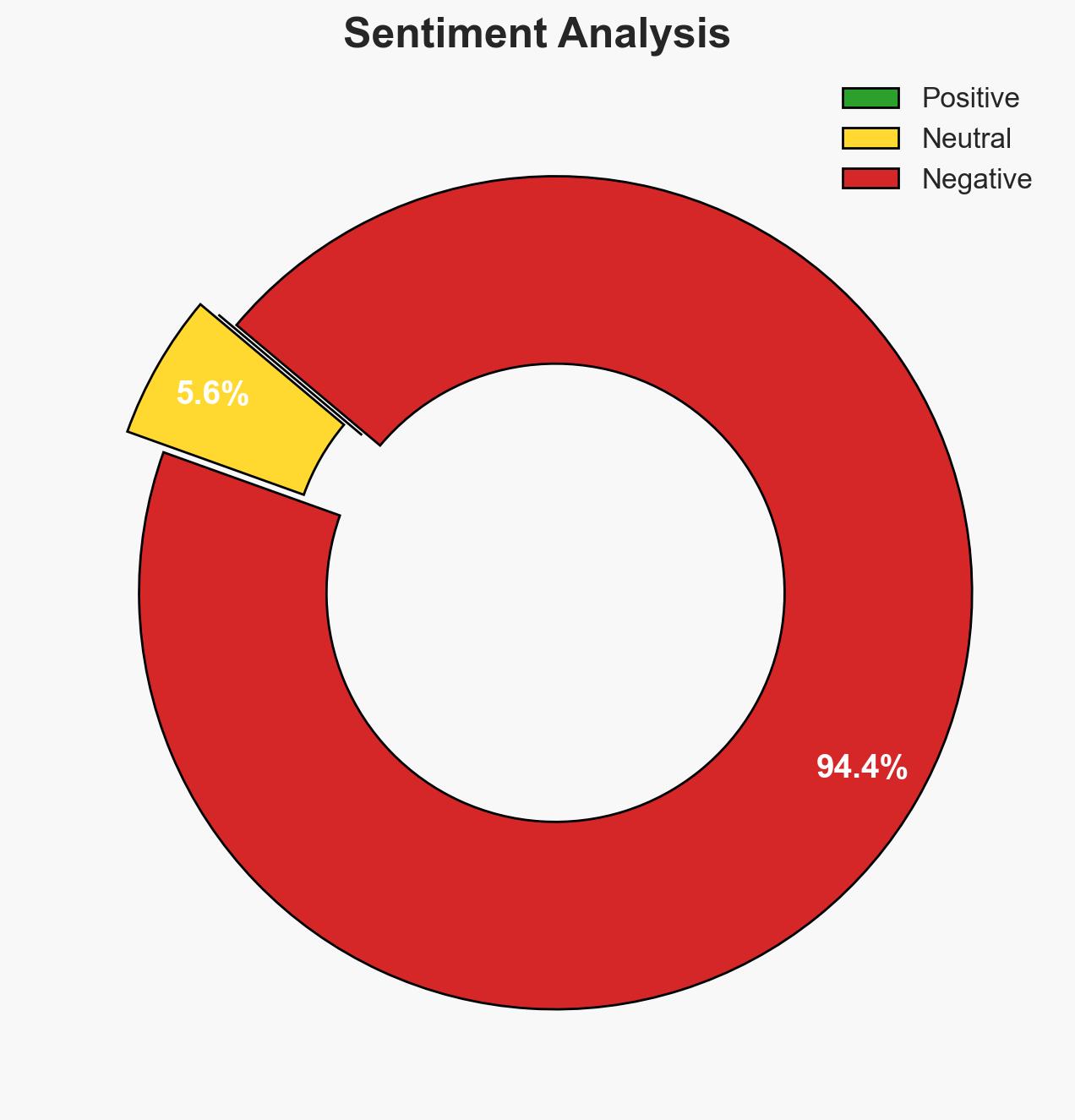
- Hypothesis B: Bill C-22 will significantly undermine privacy rights without proportionate security benefits. This is supported by concerns over mass metadata collection and potential civil liberties infringements. Contradicting evidence includes the legal safeguards mentioned in the bill.
- Assessment: Hypothesis A is currently better supported due to the bill’s focus on modernizing investigative processes and facilitating international cooperation. However, indicators such as public backlash or legal challenges could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The bill will be implemented as written; legal safeguards will be effective; international cooperation will be beneficial.
- Information Gaps: Specific details on oversight mechanisms and the scope of data access are missing.
- Bias & Deception Risks: Potential bias in source material favoring security over privacy; risk of underestimating public opposition.
4. Implications and Strategic Risks
The development of Bill C-22 could lead to increased tensions between privacy advocates and security agencies, influencing legislative and judicial landscapes.
- Political / Geopolitical: Potential strain on Canada’s international relations if perceived as infringing on privacy rights.
- Security / Counter-Terrorism: Enhanced capabilities for threat detection and response, but risk of alienating communities.
- Cyber / Information Space: Increased data collection could make systems more attractive targets for cyber-attacks.
- Economic / Social: Possible impact on public trust in government and telecommunications providers.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor public and political reactions; assess legal challenges; engage with privacy advocates.
- Medium-Term Posture (1–12 months): Develop oversight frameworks; strengthen cybersecurity measures; foster public dialogue on privacy and security balance.
- Scenario Outlook: Best: Enhanced security with minimal privacy impact; Worst: Legal challenges and public unrest; Most-Likely: Gradual implementation with ongoing privacy debates.
6. Key Individuals and Entities
- Minister of Public Safety
- Canadian Security Intelligence Service (CSIS)
- Telecommunications Service Providers
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
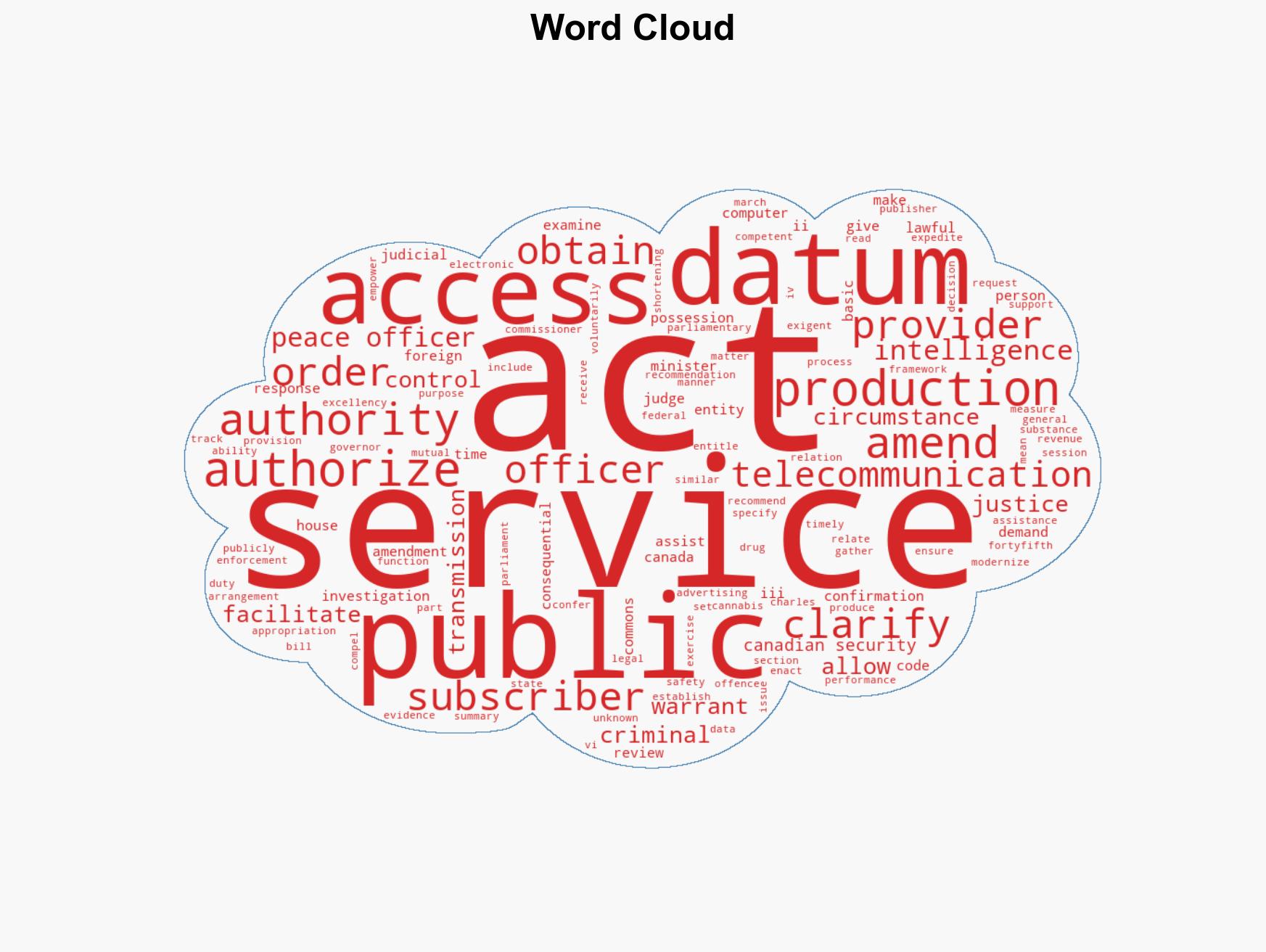
cybersecurity, national security, privacy rights, metadata surveillance, legal reform, telecommunications, international cooperation, public safety
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us