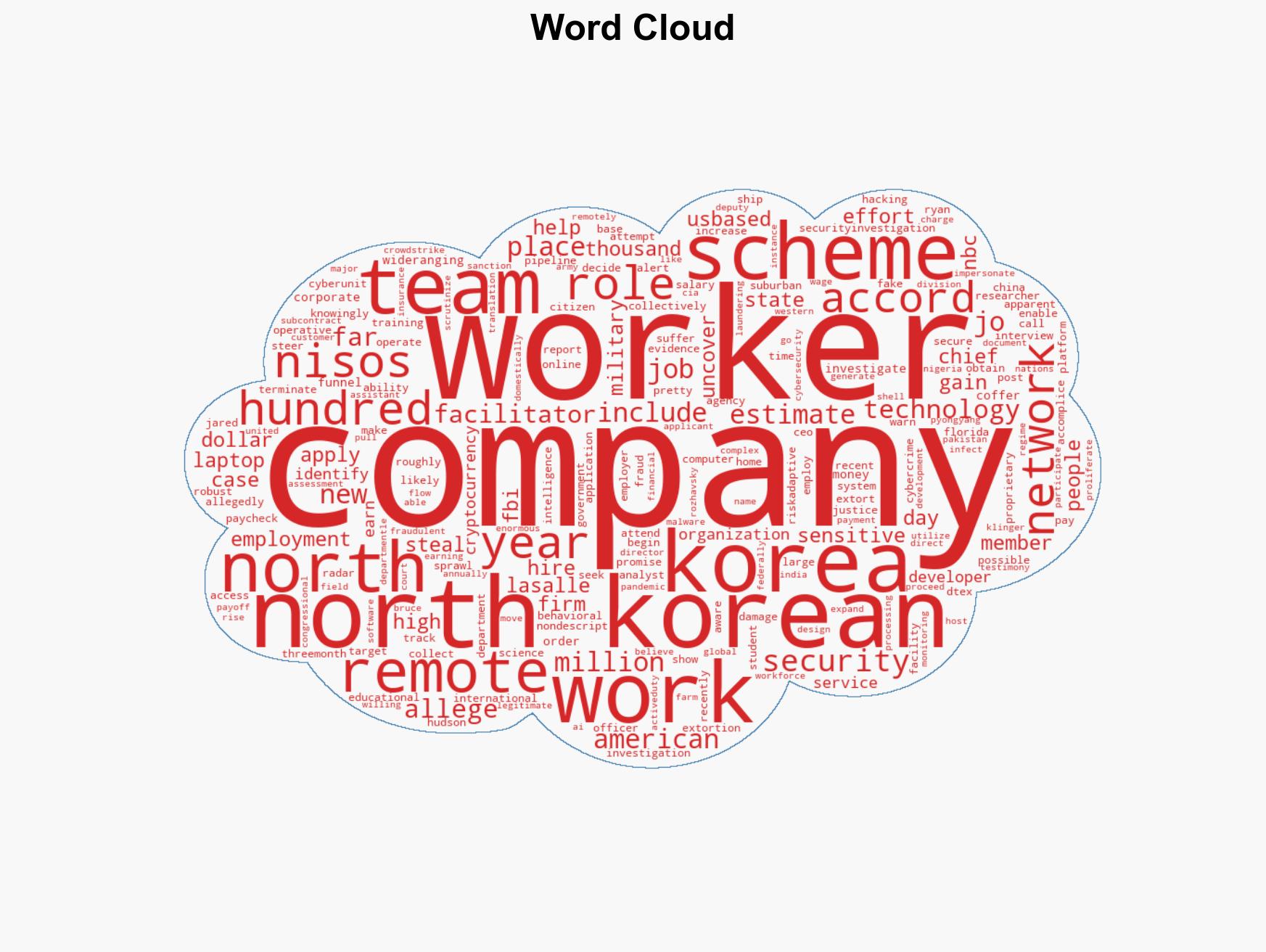
Investigation Reveals North Korea’s Extensive Remote Worker Scheme Targeting U.S. Companies
Published on: 2026-03-15
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: How One Company Finally Exposed North Korea’s Massive Remote Workers Scam
1. BLUF (Bottom Line Up Front)
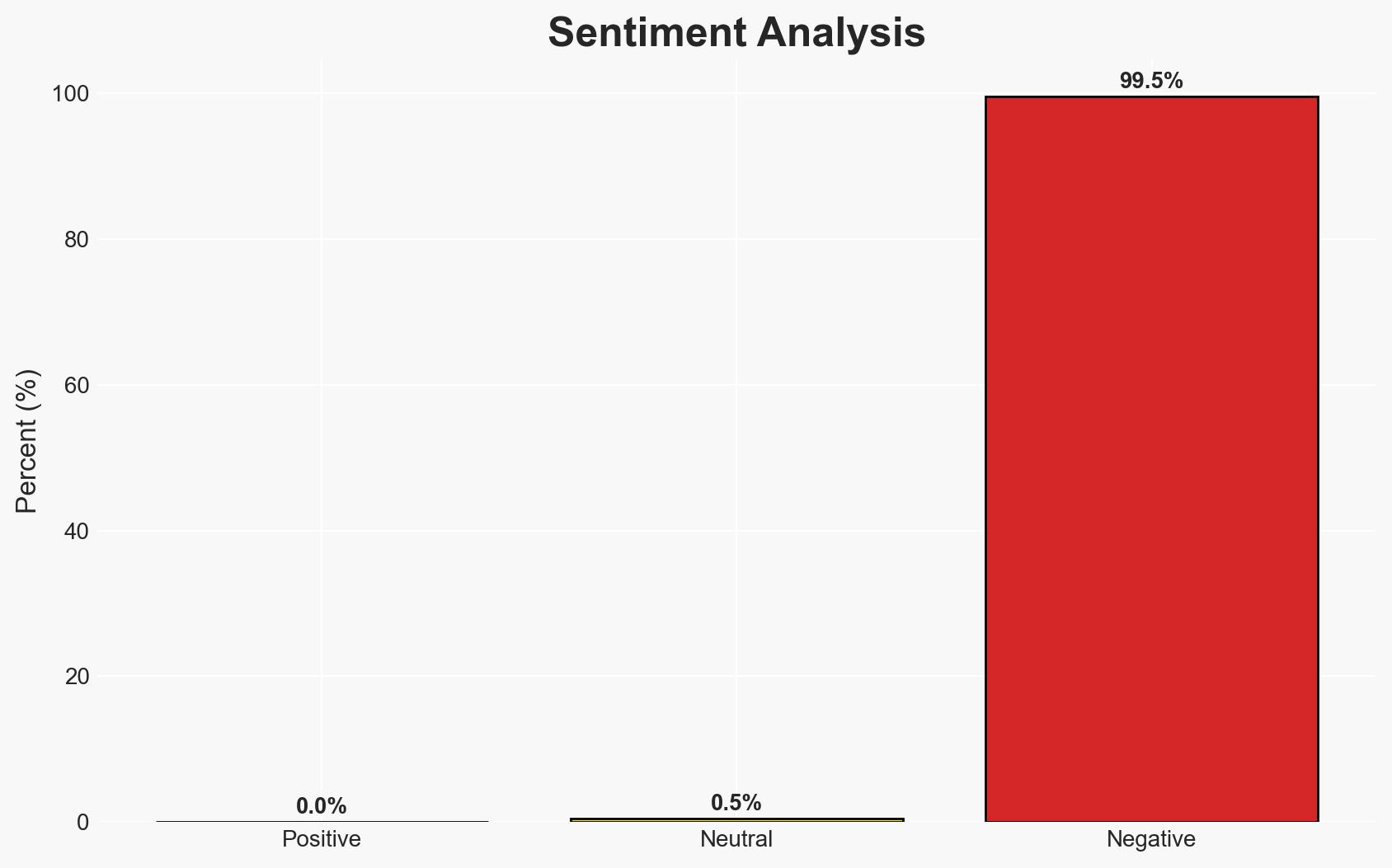
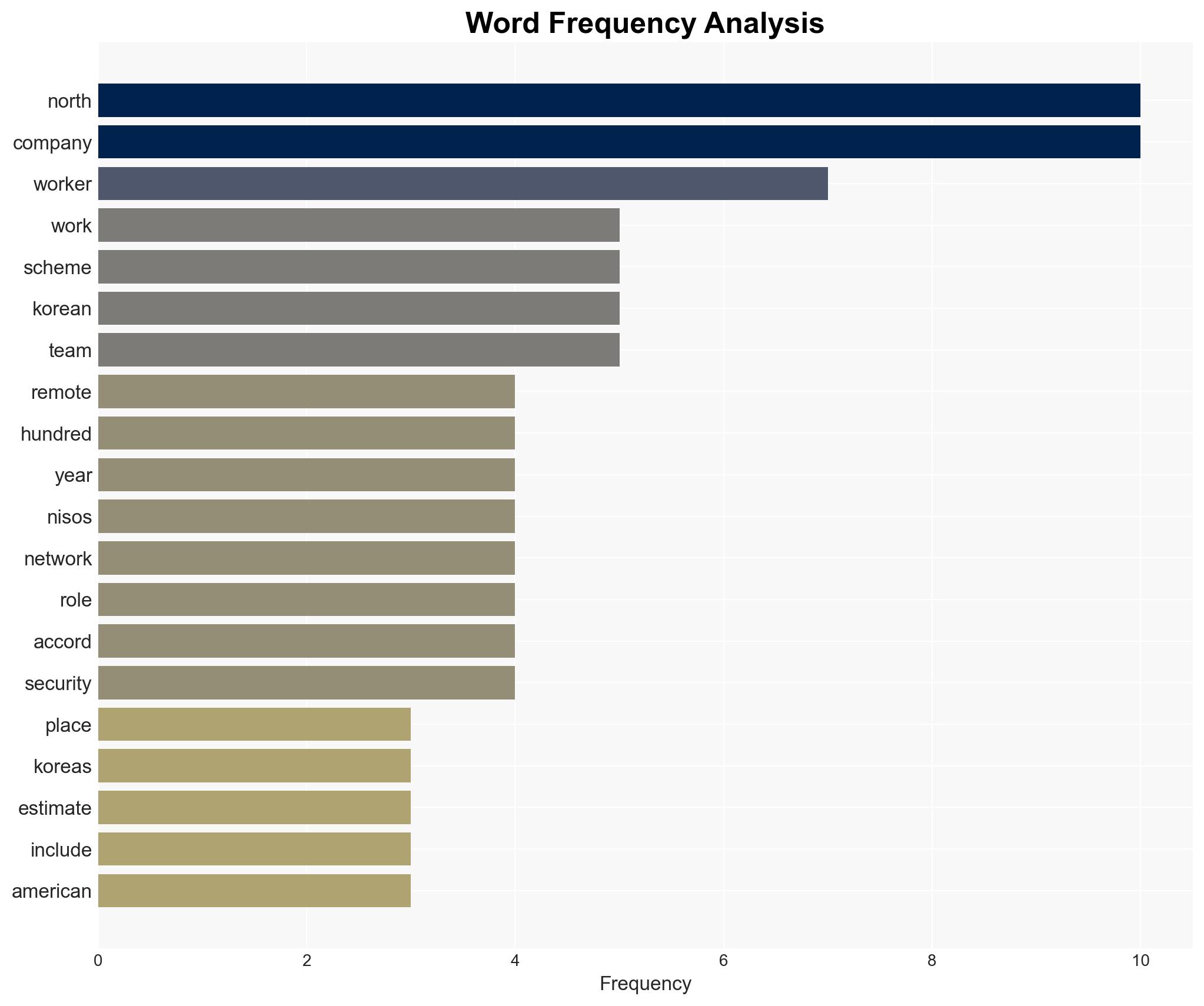
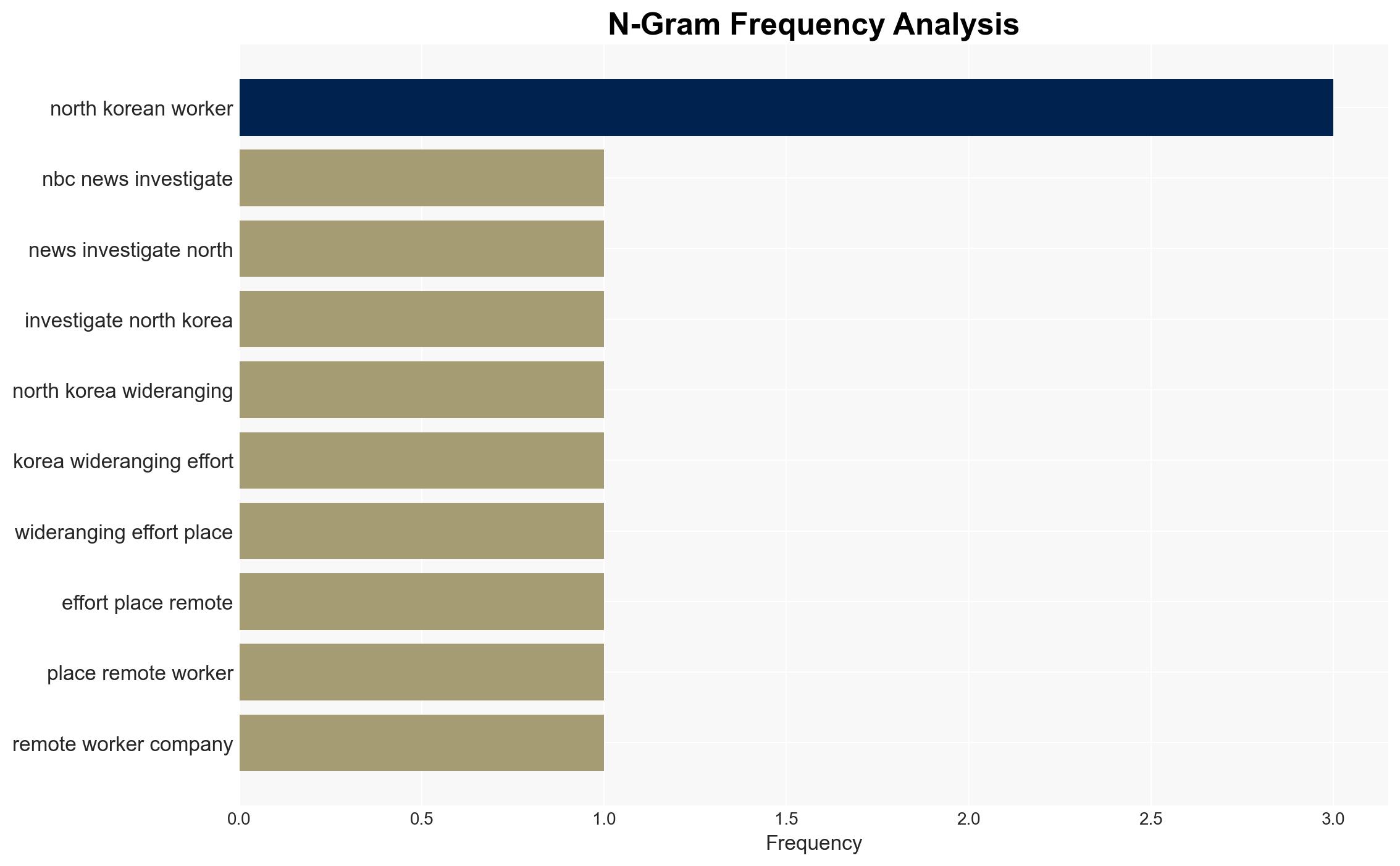
North Korea has been orchestrating a large-scale operation to place remote workers in U.S. companies, aiming to siphon funds and potentially steal sensitive information. This scheme involves thousands of operatives and is estimated to generate hundreds of millions of dollars annually. The exposure of this network by a corporate security firm highlights significant vulnerabilities in corporate hiring processes. Confidence in this assessment is moderate due to the complexity and scale of the operation.
2. Competing Hypotheses
- Hypothesis A: North Korea is using remote work schemes primarily for financial gain and to fund its regime. The evidence includes the large number of applications and the focus on obtaining salaries. However, the potential for espionage cannot be discounted.
- Hypothesis B: The primary goal of the scheme is to conduct cyber-espionage and gather sensitive information, with financial gain as a secondary objective. This is supported by instances of sensitive information theft and the targeting of technology roles.
- Assessment: Hypothesis A is currently better supported due to the scale of job applications and the financial focus. However, indicators such as the theft of military technology could shift this judgment towards Hypothesis B.
3. Key Assumptions and Red Flags
- Assumptions: North Korea has the capability to manage and coordinate a large number of operatives; U.S. companies lack robust mechanisms to detect such infiltration; financial motivations are primary.
- Information Gaps: The full extent of North Korea’s network and the precise roles of American accomplices remain unclear.
- Bias & Deception Risks: There is a risk of underestimating the espionage component due to the focus on financial aspects; potential manipulation of data by North Korean operatives to mislead investigators.
4. Implications and Strategic Risks
This development could lead to increased scrutiny on remote hiring practices and a reevaluation of cybersecurity protocols across industries. The exposure of this scheme may prompt North Korea to adapt its tactics, potentially escalating cyber threats.
- Political / Geopolitical: Increased tensions between the U.S. and North Korea, potential diplomatic repercussions.
- Security / Counter-Terrorism: Heightened threat environment for U.S. companies, particularly those in technology sectors.
- Cyber / Information Space: Potential for more sophisticated cyber operations and increased targeting of cryptocurrency firms.
- Economic / Social: Potential economic impact on companies affected by fraud and data breaches, leading to reputational damage and financial losses.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Strengthen vetting processes for remote hires, enhance cybersecurity measures, and increase awareness among corporate security teams.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms for threat intelligence sharing, invest in employee training on recognizing social engineering tactics.
- Scenario Outlook:
- Best: Enhanced security measures mitigate the threat, reducing North Korea’s ability to exploit remote work schemes.
- Worst: North Korea adapts tactics, leading to successful espionage operations and significant data breaches.
- Most-Likely: Continued attempts by North Korea with periodic successes, prompting ongoing adjustments in security protocols.
6. Key Individuals and Entities
- Jared Hudson, Nisos’ Chief Technology Officer
- Ryan LaSalle, Nisos’ CEO
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, cyber-espionage, remote work, North Korea, financial fraud, national security, corporate security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us