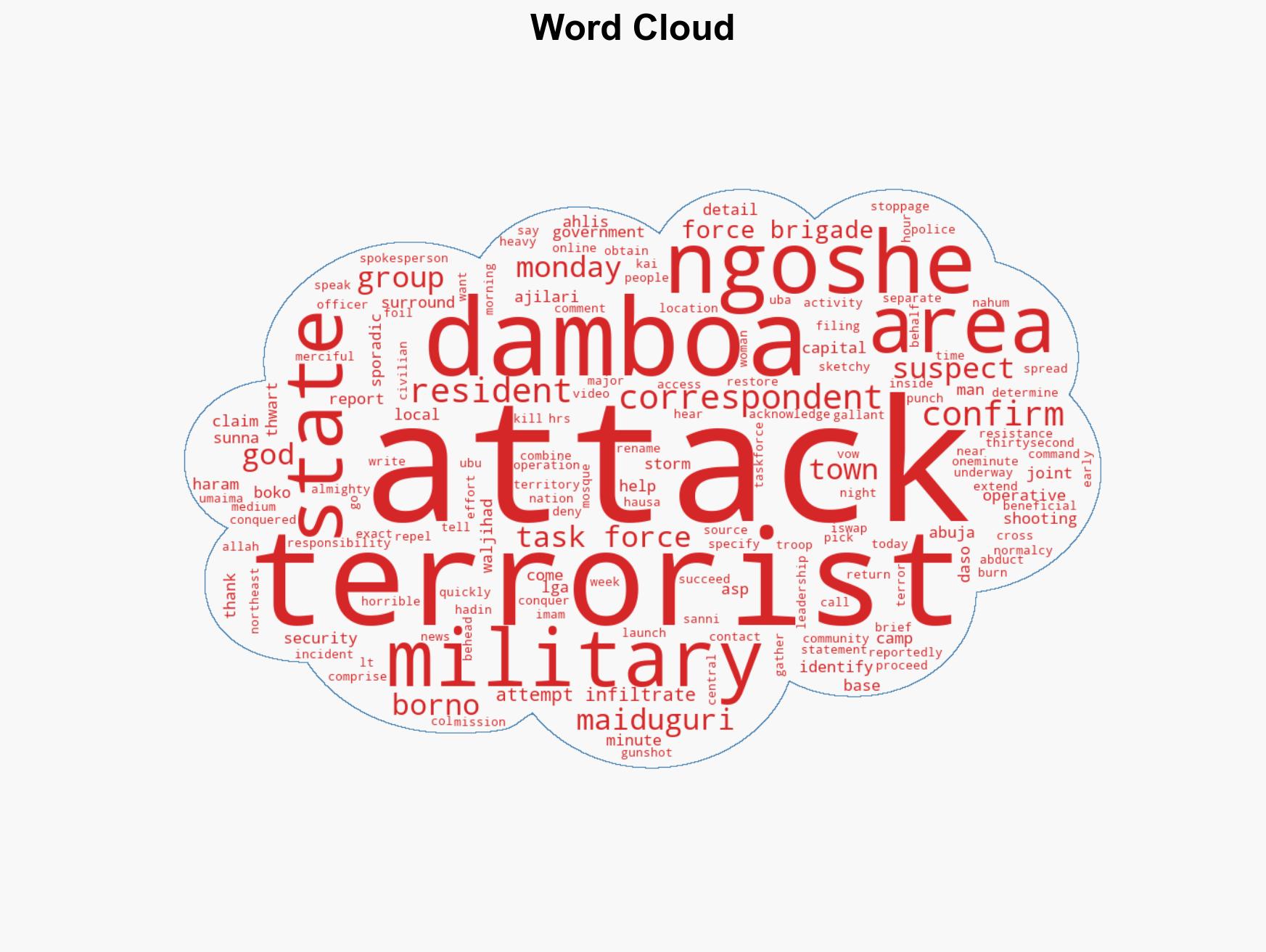
Boko Haram Launches Coordinated Assault on Military Camp and Nearby Areas in Borno State
Published on: 2026-03-16
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Terrorists strike another military camp in Borno
1. BLUF (Bottom Line Up Front)
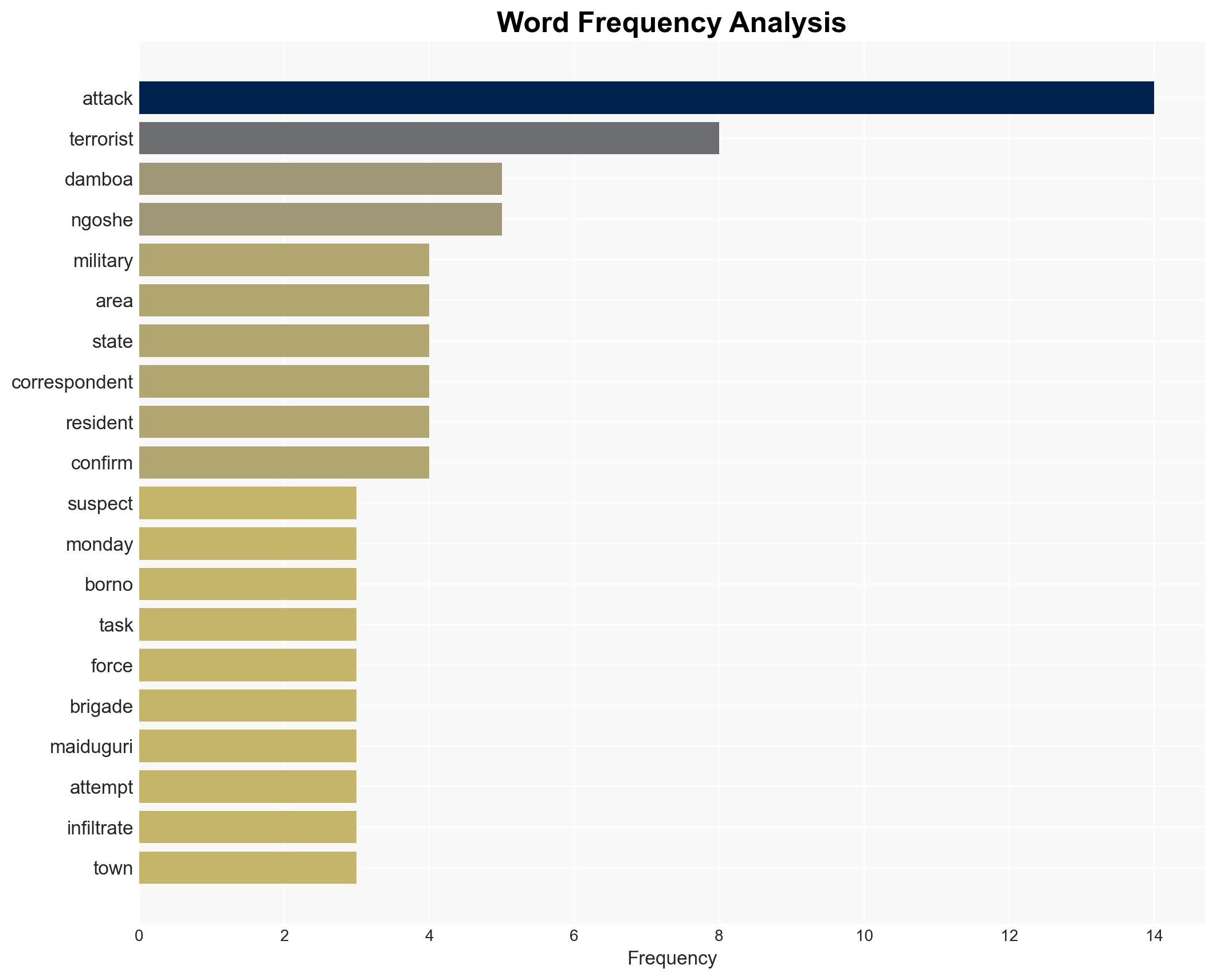
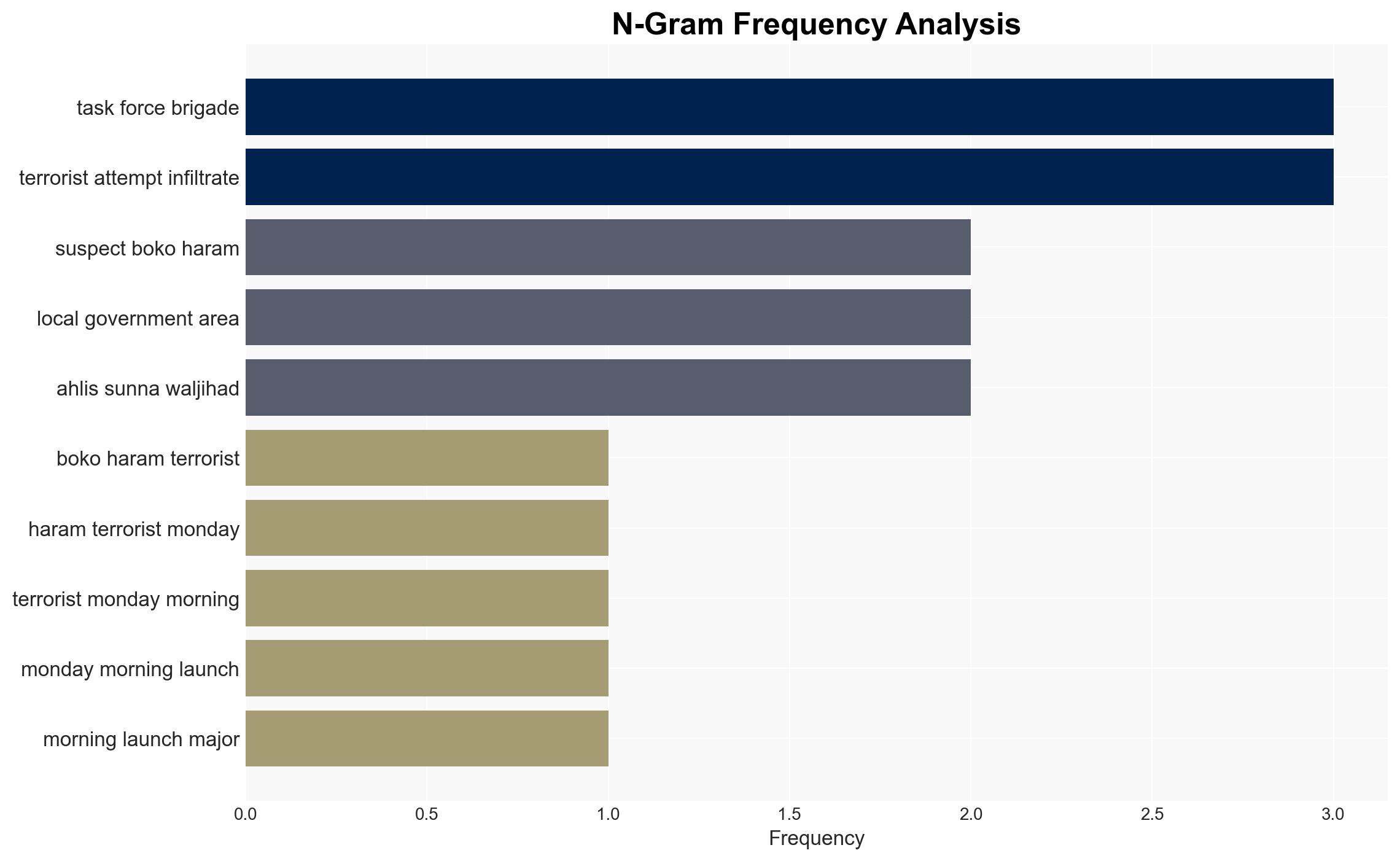
The recent attacks in Borno State, attributed to suspected Boko Haram/ISWAP terrorists, highlight a persistent threat to military and civilian targets in the region. The thwarted attack on the 25 Task Force Brigade in Damboa and the previous attack in Ngoshe suggest a coordinated effort to destabilize the area. This assessment is made with moderate confidence, given the limited details on the attackers’ capabilities and intentions.
2. Competing Hypotheses
- Hypothesis A: The attacks are part of a coordinated campaign by Boko Haram/ISWAP to destabilize Borno State and extend their influence. Supporting evidence includes the timing of multiple attacks and the recent claim of responsibility by Jama’atu Ahlis Sunna Lidda’awati wal-Jihad. However, the exact coordination and command structure remain unclear.
- Hypothesis B: The attacks are opportunistic and not part of a broader strategic campaign. This is supported by the lack of detailed information on the attackers’ long-term objectives and the immediate repulsion of the attacks, suggesting limited operational capacity.
- Assessment: Hypothesis A is currently better supported due to the pattern of recent attacks and the explicit claim of responsibility. Indicators such as increased frequency of attacks or expanded target areas could further support this hypothesis.
3. Key Assumptions and Red Flags
- Assumptions: The attackers are primarily motivated by territorial control; security forces have the capacity to repel further attacks; local intelligence on terrorist movements is accurate.
- Information Gaps: Detailed intelligence on the attackers’ leadership, logistics, and future targets; confirmation of the exact number of attackers and their casualties.
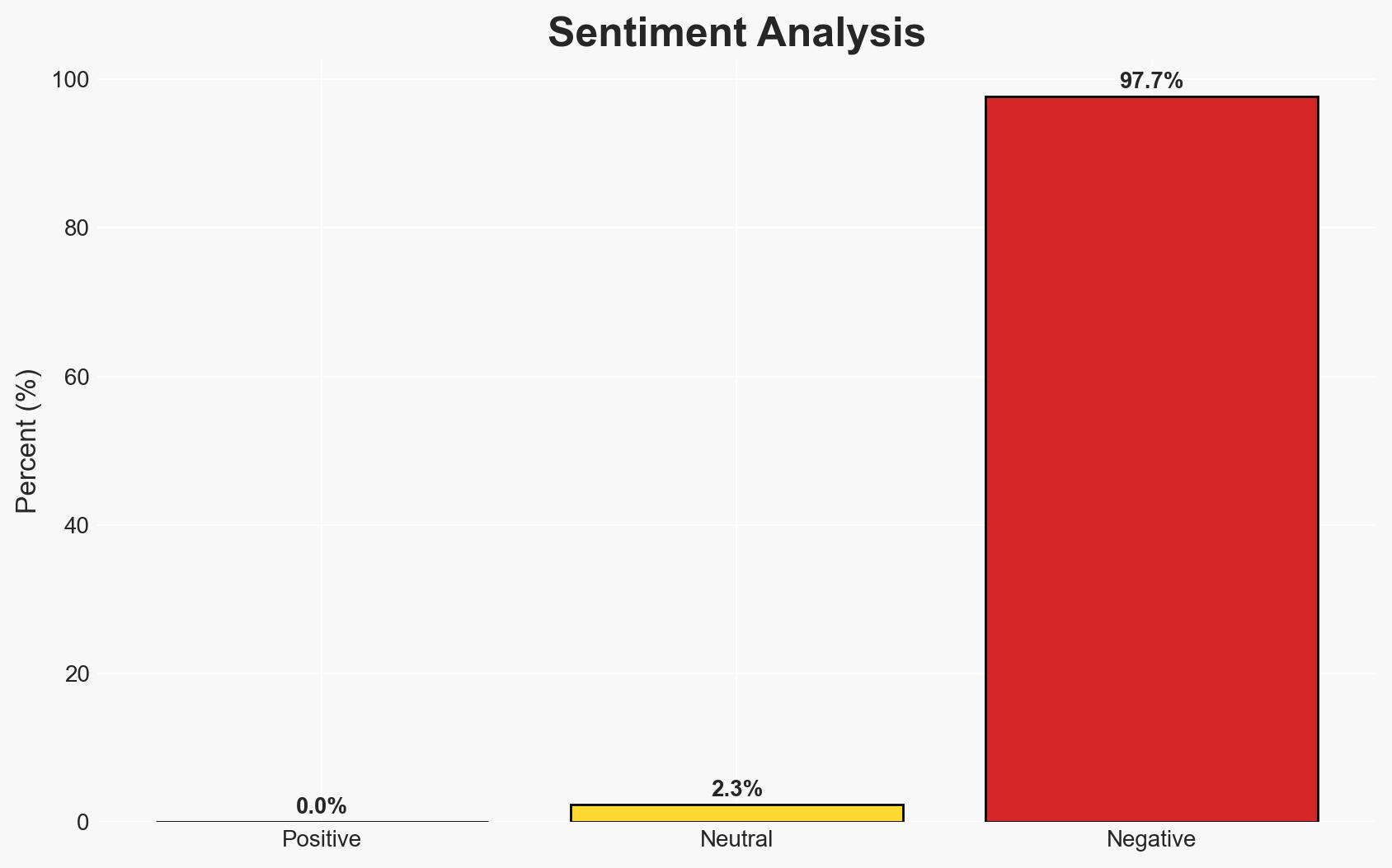
- Bias & Deception Risks: Potential over-reliance on local sources that may underreport or exaggerate events; risk of misinformation from terrorist groups to inflate their perceived strength.
4. Implications and Strategic Risks
The continuation of such attacks could exacerbate instability in Borno State, potentially leading to broader regional insecurity. The situation may evolve into a more entrenched conflict if not addressed effectively.
- Political / Geopolitical: Potential for increased military intervention and international attention; risk of spillover into neighboring regions.
- Security / Counter-Terrorism: Increased pressure on security forces; potential for escalated military responses and civilian displacement.
- Cyber / Information Space: Potential use of digital platforms by terrorists for propaganda and recruitment; need for enhanced cyber monitoring.
- Economic / Social: Disruption to local economies and social services; increased humanitarian needs and potential for refugee flows.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Strengthen intelligence-sharing mechanisms; increase patrols and security presence in vulnerable areas; engage with local communities to gather actionable intelligence.
- Medium-Term Posture (1–12 months): Develop resilience measures, including community-based security initiatives; enhance regional cooperation and partnerships for counter-terrorism efforts.
- Scenario Outlook: Best: Successful containment of terrorist activities with improved security; Worst: Escalation into broader conflict affecting regional stability; Most-Likely: Continued sporadic attacks with gradual security improvements.
6. Key Individuals and Entities
- Jama’atu Ahlis Sunna Lidda’awati wal-Jihad
- Imam Ubu Umaima
- ASP Nahum Daso
- Lt Col Sanni Uba
7. Thematic Tags
Counter-Terrorism, Boko Haram, ISWAP, military operations, regional security, intelligence analysis, Borno State
Structured Analytic Techniques Applied
- ACH 2.0: Reconstruct likely threat actor intentions via hypothesis testing and structured refutation.
- Indicators Development: Track radicalization signals and propaganda patterns to anticipate operational planning.
- Narrative Pattern Analysis: Analyze spread/adaptation of ideological narratives for recruitment/incitement signals.
Explore more:
Counter-Terrorism Briefs ·
Daily Summary ·
Support us