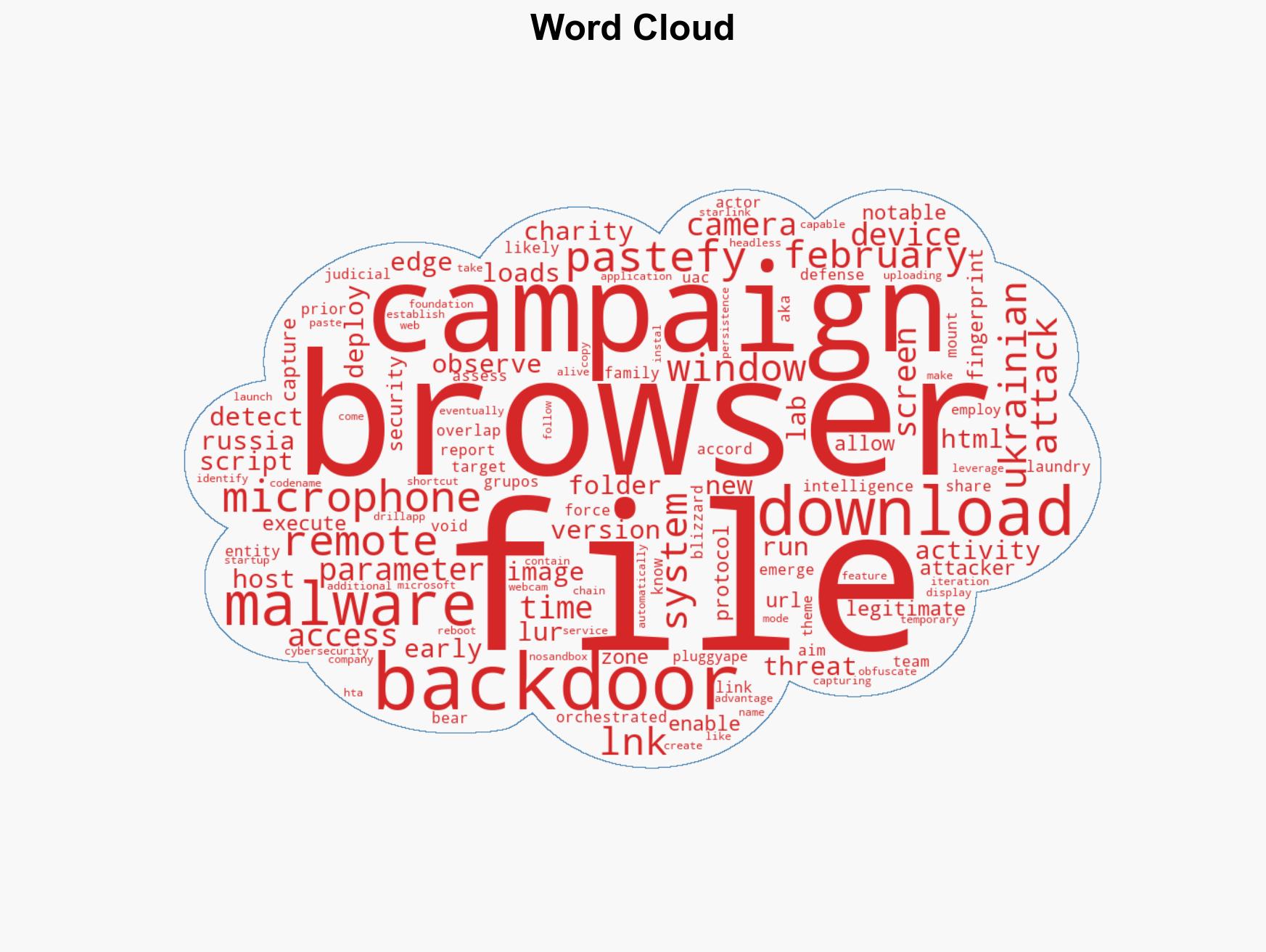
Russian-linked DRILLAPP Backdoor Exploits Microsoft Edge for Espionage Against Ukrainian Targets
Published on: 2026-03-16
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: DRILLAPP Backdoor Targets Ukraine Abuses Microsoft Edge Debugging for Stealth Espionage
1. BLUF (Bottom Line Up Front)
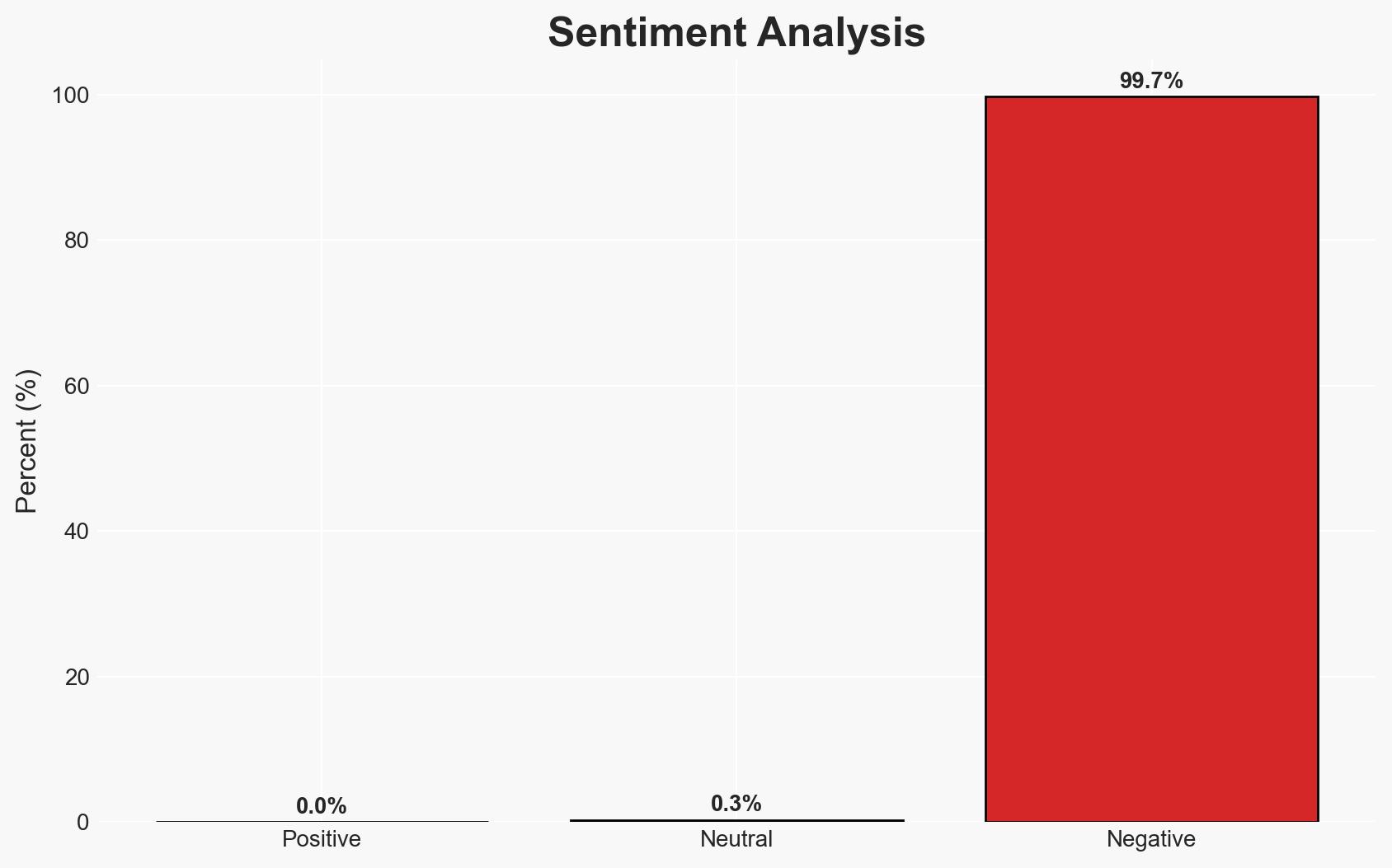
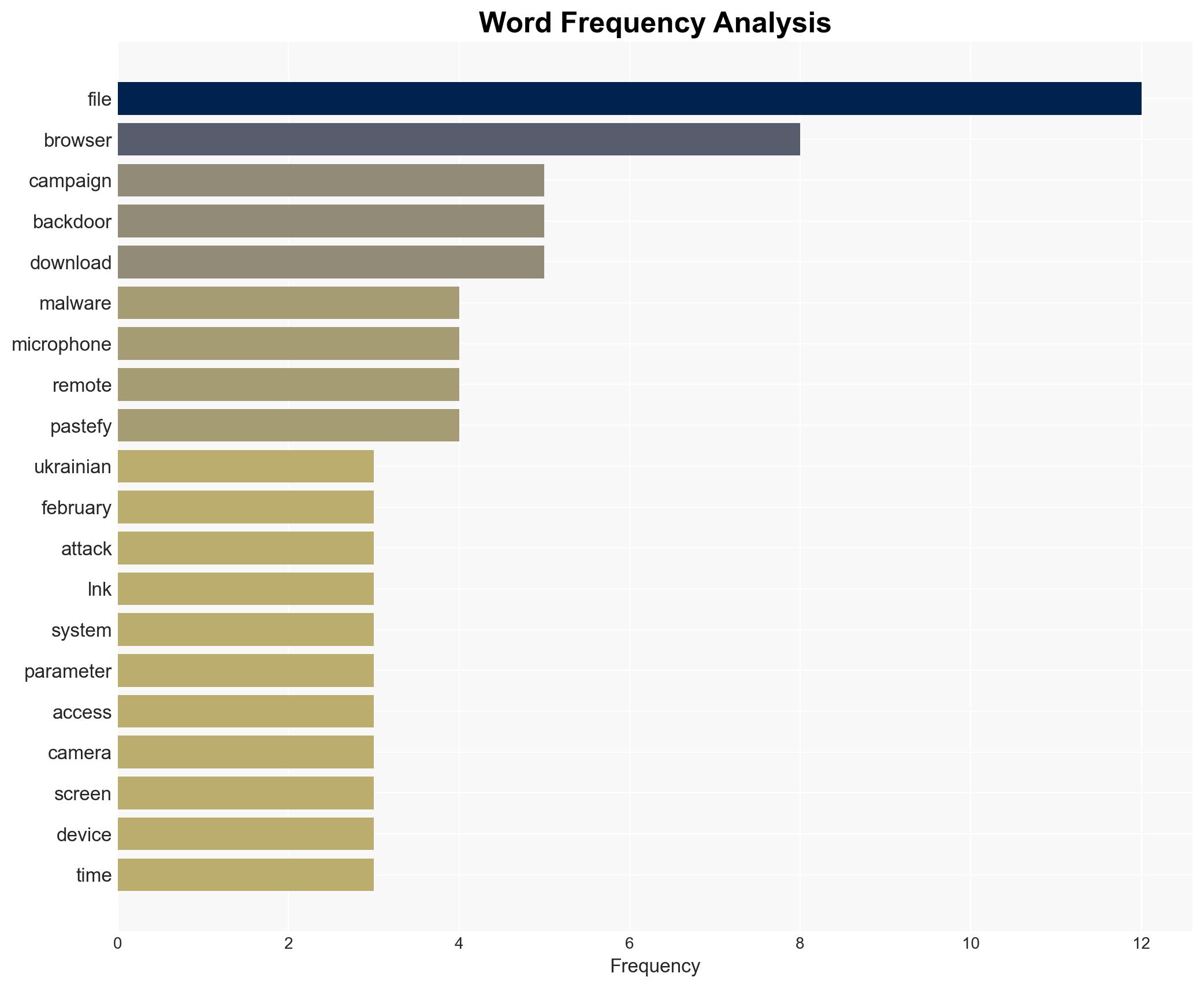
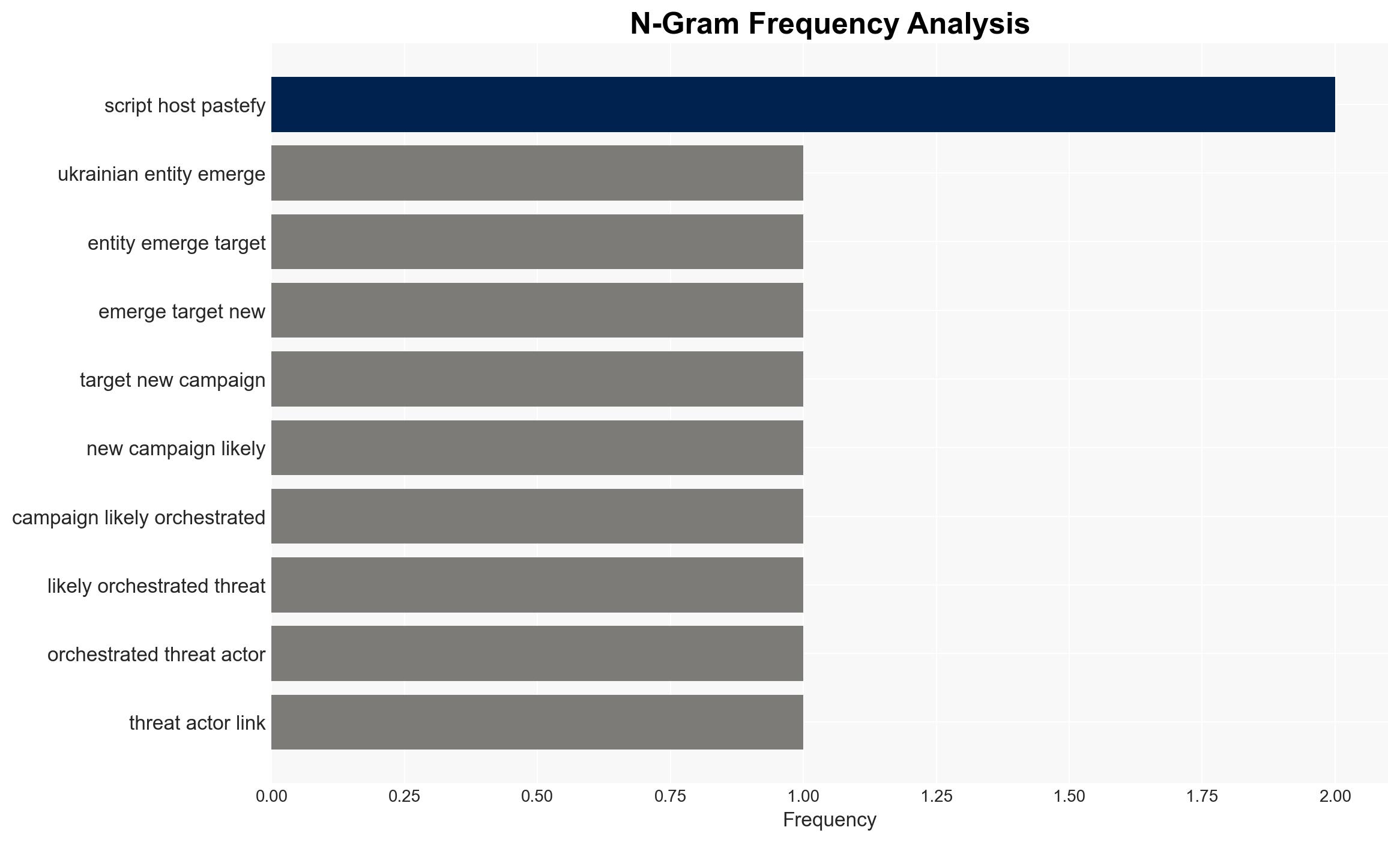
The DRILLAPP malware campaign, likely linked to Russian threat actors, targets Ukrainian entities using Microsoft Edge debugging features for espionage. The campaign’s sophistication and targeting suggest a strategic intent to gather intelligence on Ukrainian defense and civil infrastructure. Overall confidence in this assessment is moderate, based on the available evidence and historical context.
2. Competing Hypotheses
- Hypothesis A: The DRILLAPP campaign is a state-sponsored operation by Russian-linked actors aimed at strategic intelligence collection in Ukraine. This is supported by the targeting of Ukrainian entities, the use of sophisticated malware, and historical patterns of Russian cyber operations. However, the lack of direct attribution to a specific Russian state entity remains a key uncertainty.
- Hypothesis B: The campaign is conducted by non-state actors or cybercriminals seeking financial gain or to sell intelligence to interested parties. While plausible, this is less supported due to the strategic nature of the targets and the absence of financial exploitation indicators.
- Assessment: Hypothesis A is currently better supported due to the alignment with known Russian cyber tactics and the geopolitical context. Indicators that could shift this judgment include evidence of financial motives or attribution to non-state actors.
3. Key Assumptions and Red Flags
- Assumptions: The campaign’s primary goal is intelligence collection; Russian state actors are involved; Ukrainian defense and civil sectors are the main targets.
- Information Gaps: Direct attribution to a specific Russian entity; detailed technical analysis of the malware’s origin; confirmation of the campaign’s impact on Ukrainian infrastructure.
- Bias & Deception Risks: Potential confirmation bias towards attributing cyber activities to Russia; reliance on a single source (S2 Grupo’s LAB52) may introduce source bias.
4. Implications and Strategic Risks
The DRILLAPP campaign could exacerbate tensions between Ukraine and Russia, potentially leading to increased cyber conflict and impacting regional stability.
- Political / Geopolitical: Escalation of cyber hostilities could strain diplomatic relations and provoke retaliatory measures.
- Security / Counter-Terrorism: Increased cyber threat to Ukrainian national security infrastructure, necessitating enhanced defensive measures.
- Cyber / Information Space: Potential for further cyber operations targeting critical infrastructure and information warfare tactics.
- Economic / Social: Disruption of services and erosion of public trust in digital systems could have economic and social repercussions.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of Ukrainian cyber infrastructure; issue alerts to potential targets; collaborate with international cyber defense partners.
- Medium-Term Posture (1–12 months): Develop resilience measures, including cybersecurity training and incident response capabilities; strengthen international partnerships for intelligence sharing.
- Scenario Outlook:
- Best: Successful mitigation and attribution lead to diplomatic resolutions.
- Worst: Escalation into broader cyber conflict affecting regional stability.
- Most-Likely: Continued low-level cyber skirmishes with periodic escalations.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, cyber-espionage, Ukraine, Russia, malware, national security, information warfare
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us