Intuitive Surgical Reports Credential Theft from Phishing Attack, No Operational Impact Noted
Published on: 2026-03-16
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
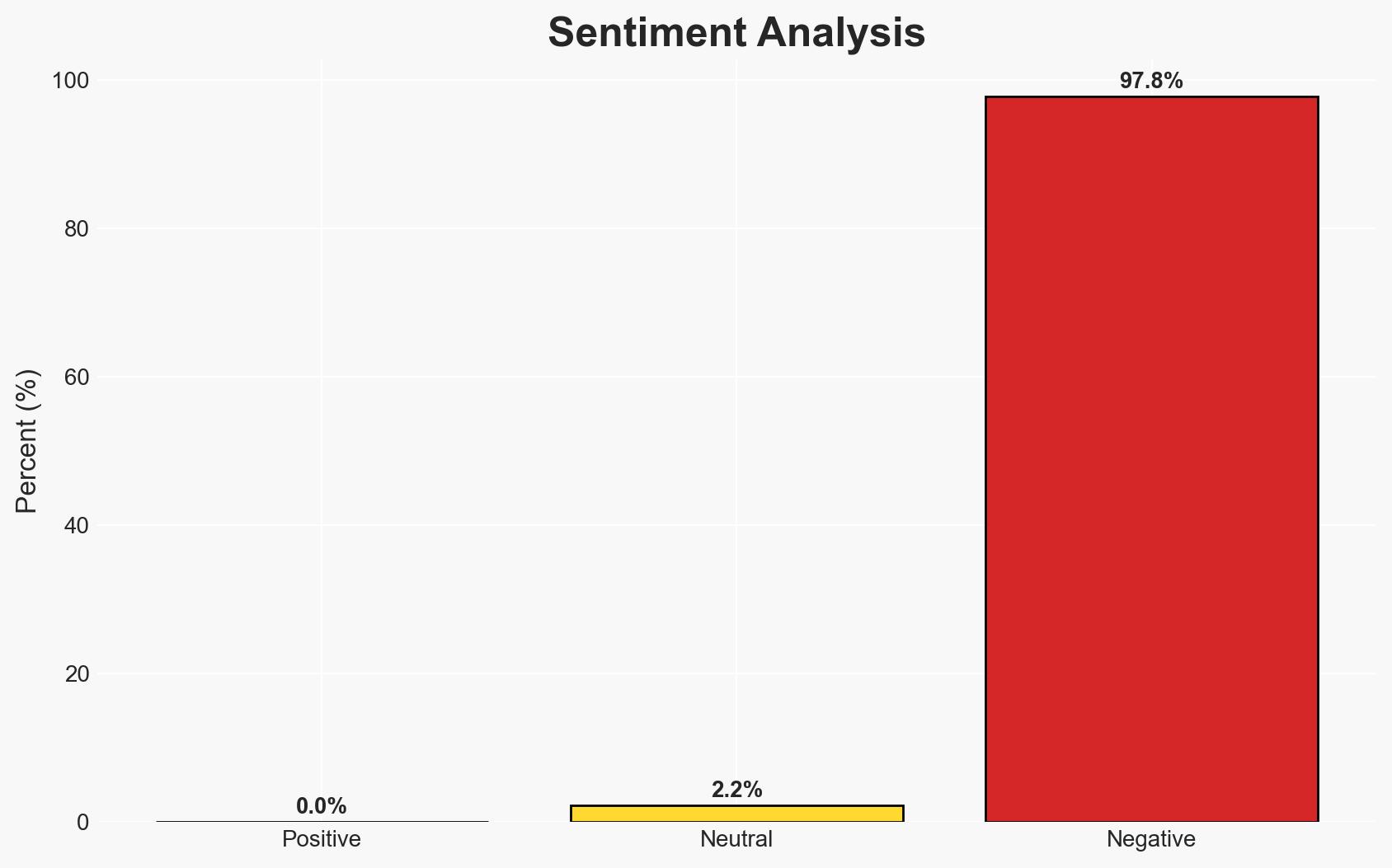
Intelligence Report: Robotics surgical biz Intuitive discloses phishing attack
1. BLUF (Bottom Line Up Front)
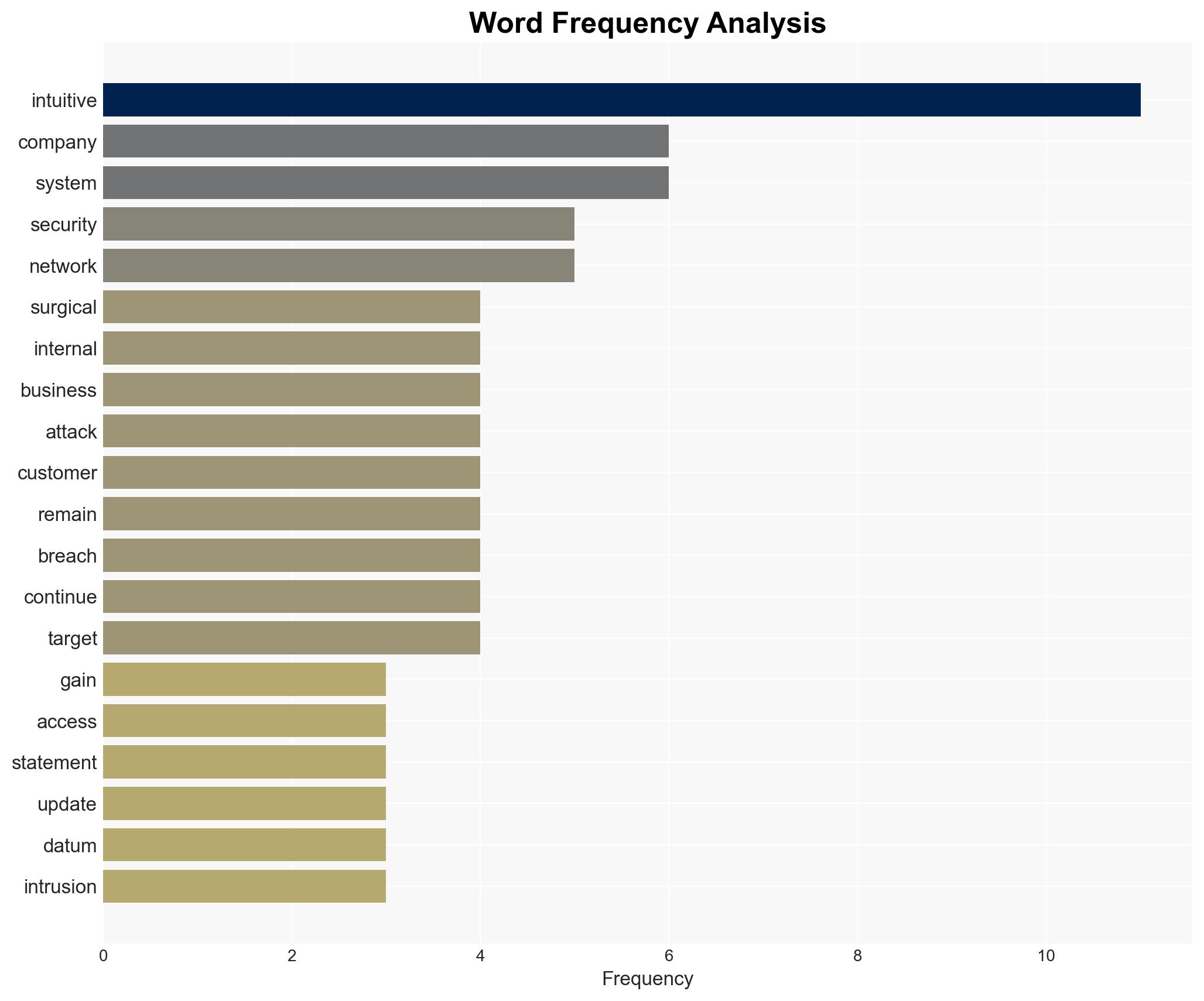
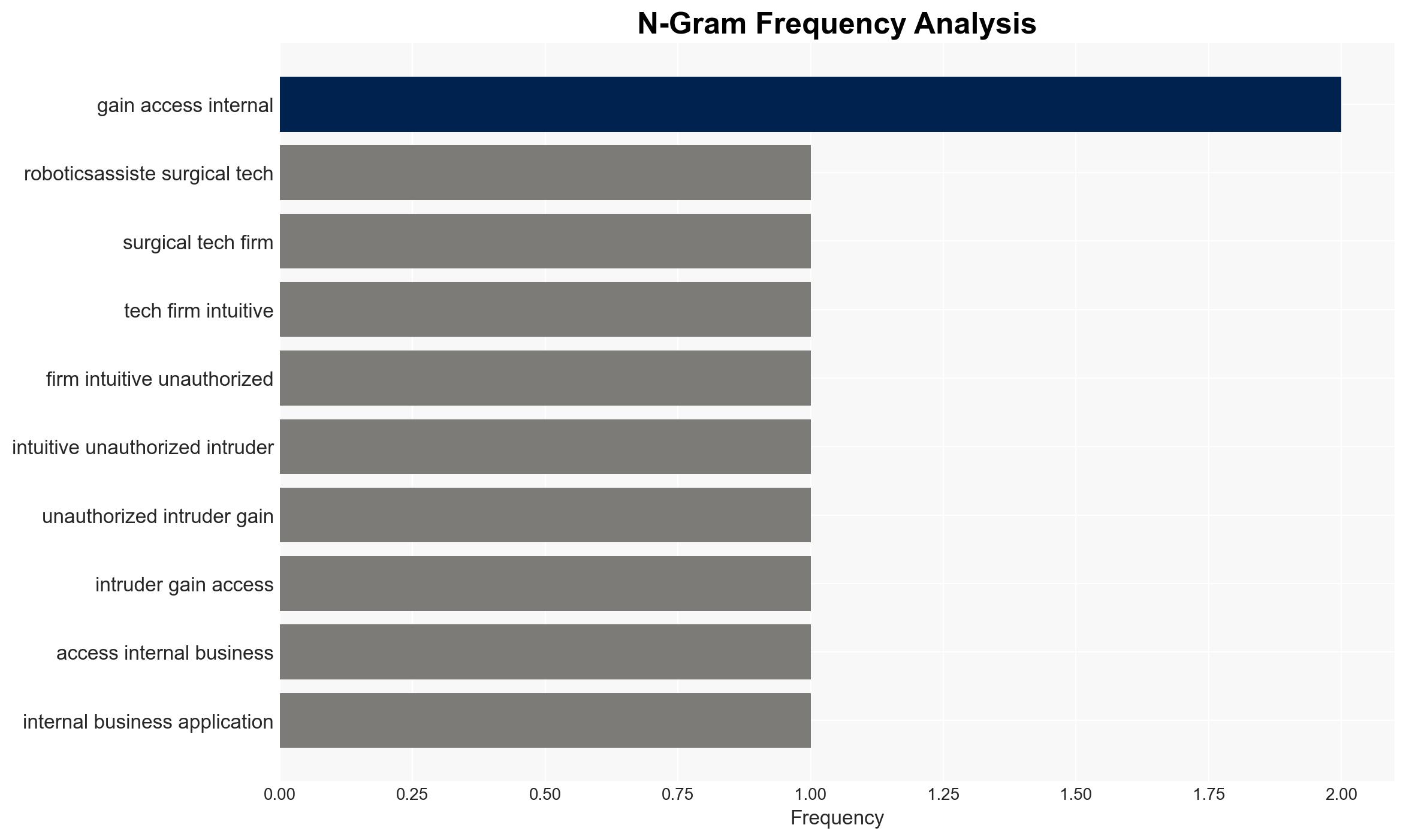
The recent phishing attack on Intuitive, a robotics-assisted surgical technology firm, resulted in unauthorized access to internal IT systems and the theft of sensitive data. Despite no operational impact reported on its robotic systems, the incident highlights vulnerabilities in cybersecurity defenses. The most likely hypothesis is that this was an opportunistic cybercrime rather than a targeted attack by a state-sponsored actor. Overall confidence in this assessment is moderate due to limited available data.
2. Competing Hypotheses
- Hypothesis A: The attack was an opportunistic cybercrime aimed at stealing data for financial gain. Supporting evidence includes the lack of operational impact on robotic systems and the absence of a claim by known state-sponsored groups. Key uncertainties include the identity of the attackers and their specific motivations.
- Hypothesis B: The attack was a targeted operation by a state-sponsored actor, potentially linked to recent similar incidents in the medical-tech sector. Contradicting evidence includes the lack of claims by known groups and the statement by Cisco’s Talos that the healthcare sector is not at increased risk from Iran-linked actors.
- Assessment: Hypothesis A is currently better supported due to the absence of indicators suggesting state-sponsored involvement and the opportunistic nature of phishing attacks. Indicators that could shift this judgment include attribution to a known state actor or evidence of strategic targeting.
3. Key Assumptions and Red Flags
- Assumptions: The attack was not state-sponsored; Intuitive’s network segmentation effectively protected operational systems; the breach was primarily for data theft.
- Information Gaps: Exact timing of the breach, detailed attacker profile, and specific data compromised.
- Bias & Deception Risks: Potential bias in Intuitive’s public statements to minimize perceived impact; lack of independent verification of attack details.
4. Implications and Strategic Risks
This development underscores the persistent threat of cybercrime in the healthcare technology sector, with potential implications for data privacy and corporate reputation.
- Political / Geopolitical: Minimal direct impact, but could contribute to broader narratives about cybersecurity vulnerabilities in critical sectors.
- Security / Counter-Terrorism: No immediate changes, but highlights the need for improved cybersecurity measures.
- Cyber / Information Space: May prompt increased scrutiny and regulatory pressure on cybersecurity practices in the healthcare sector.
- Economic / Social: Potential reputational damage to Intuitive, affecting customer trust and market position.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of Intuitive’s network for further intrusions, conduct a comprehensive forensic investigation, and engage with cybersecurity experts to assess vulnerabilities.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms for ongoing threat intelligence sharing and invest in employee cybersecurity training programs.
- Scenario Outlook:
- Best: Breach contained with no further incidents; improved cybersecurity posture.
- Worst: Additional breaches occur, leading to operational disruptions and regulatory penalties.
- Most-Likely: No further incidents, but increased scrutiny and pressure to enhance cybersecurity measures.
6. Key Individuals and Entities
- Intuitive (Robotics-assisted surgical tech firm)
- Stryker (Medical-tech company previously breached)
- Handala (Hacktivist group linked to MOIS)
- Cisco’s Talos (Cybersecurity research team)
7. Thematic Tags
cybersecurity, phishing, healthcare technology, data breach, cybercrime, network segmentation, state-sponsored threats
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us