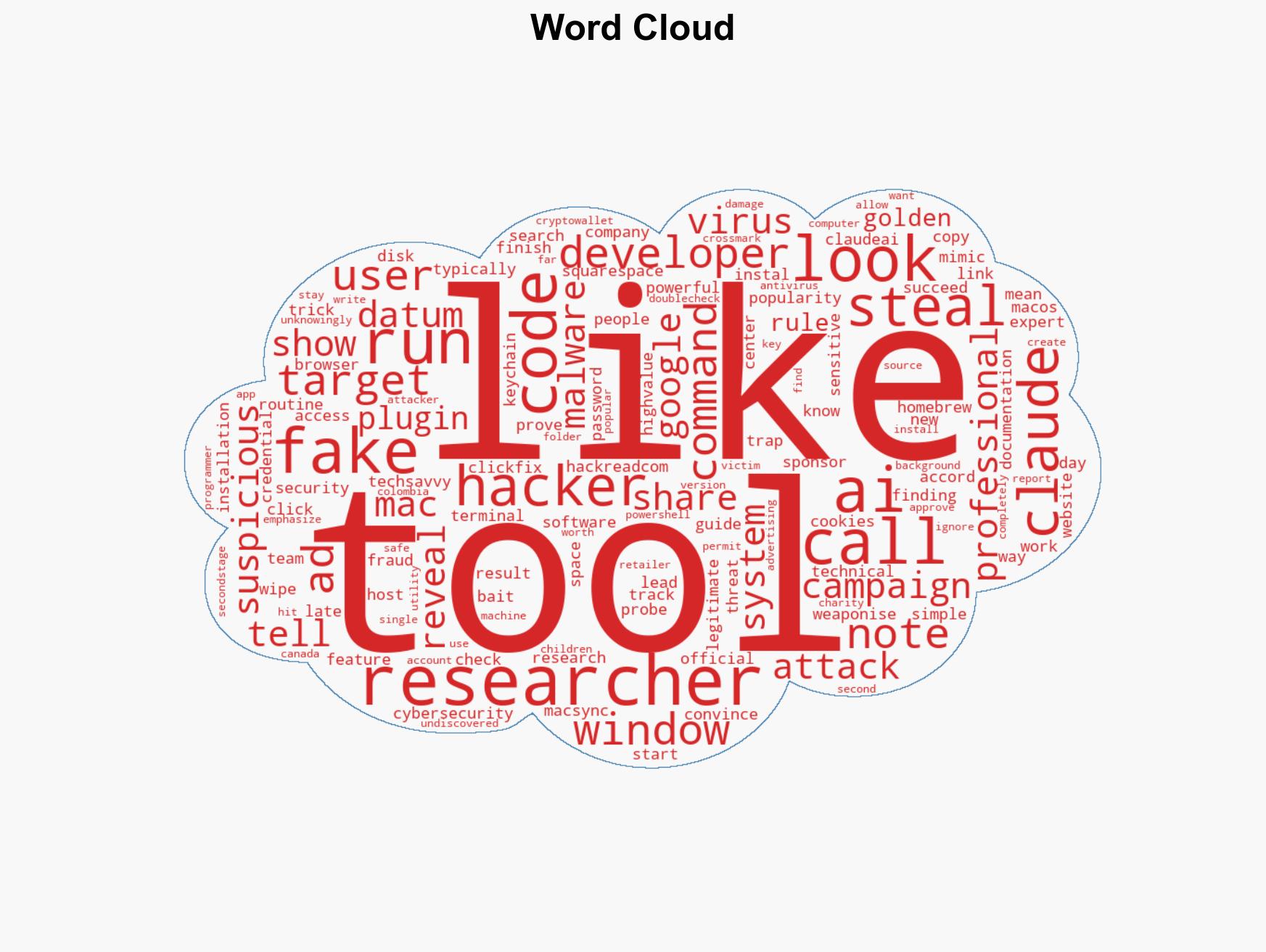
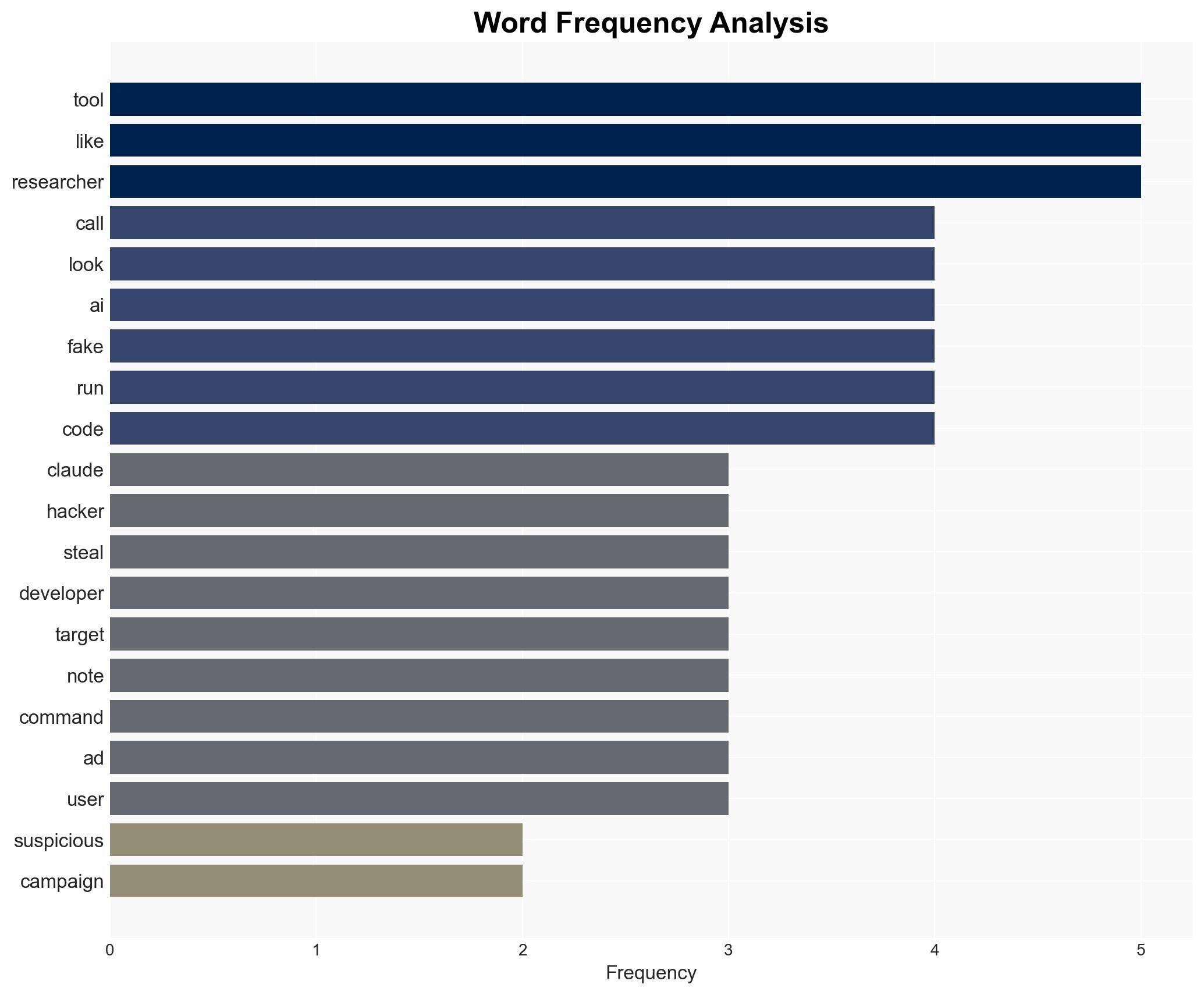
Cyber Attack Exploits AI Tool Popularity, Deploys MacSync Malware to Target Developers
Published on: 2026-03-17
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: ClickFix Attack Targets Devs with MacSync Malware via Fake Claude Tools
1. BLUF (Bottom Line Up Front)
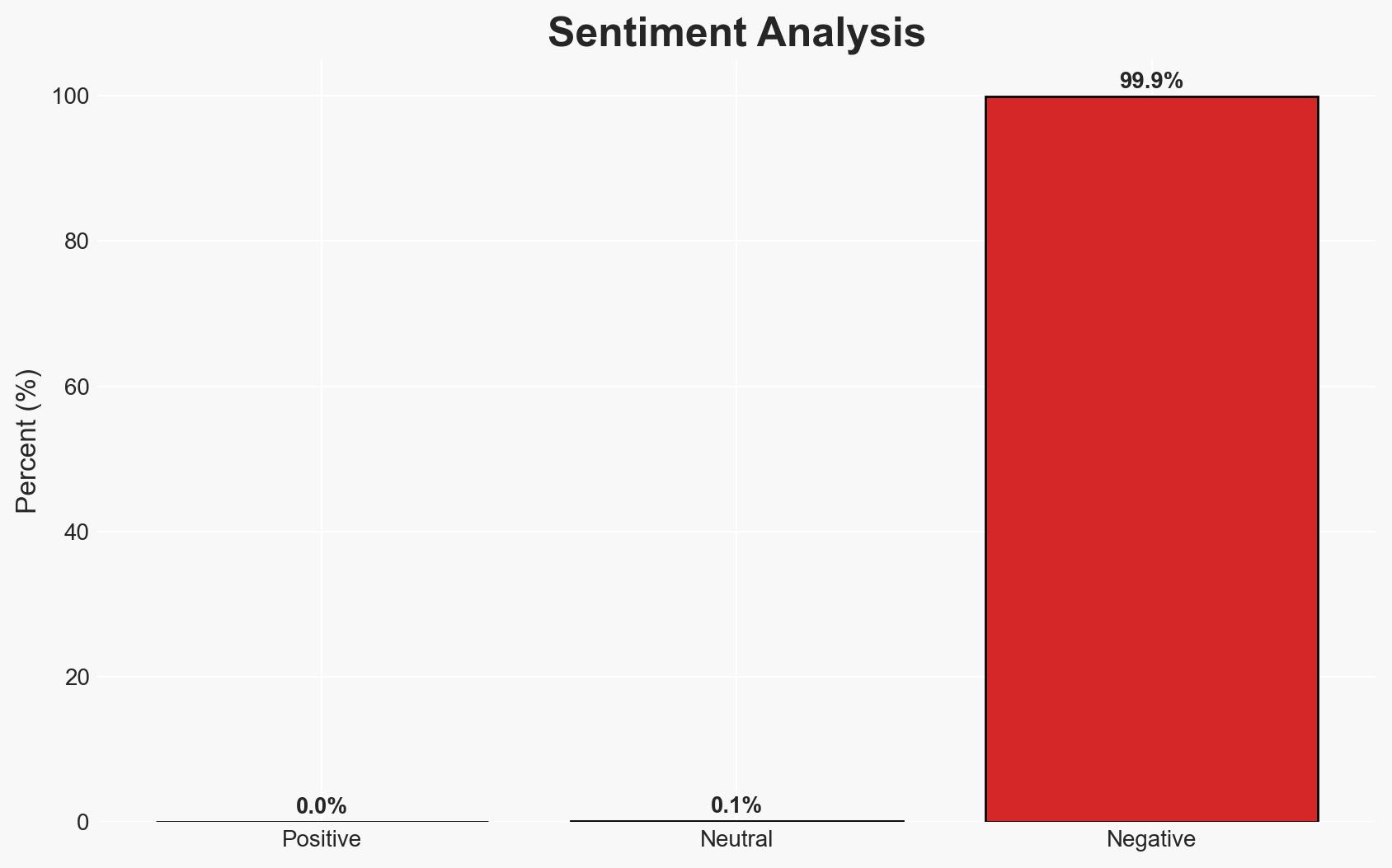
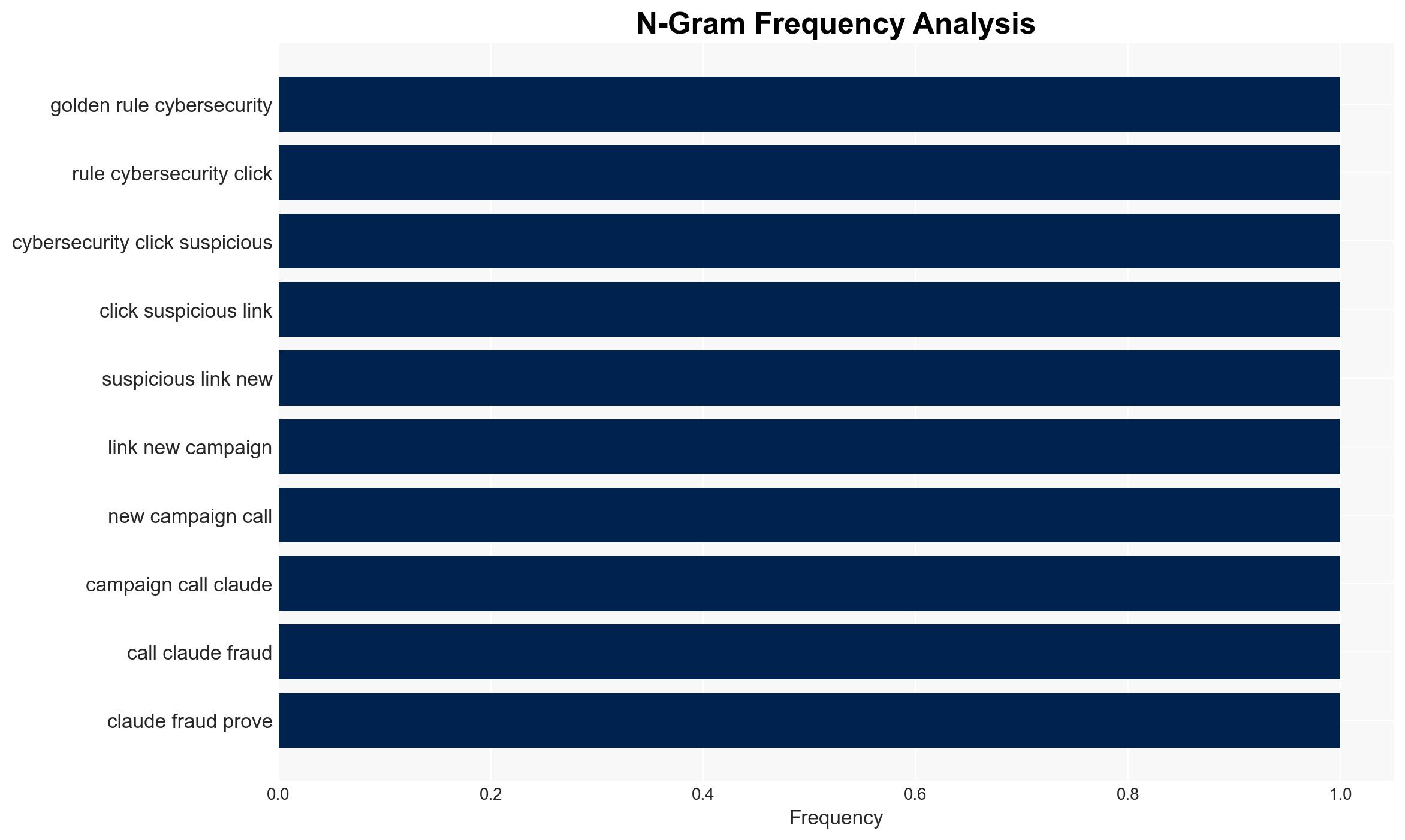
The ClickFix attack leverages fake AI tool advertisements to distribute MacSync malware, targeting developers and security experts. This campaign exploits trust in AI tools and affects both macOS and Windows systems. The operation’s sophistication suggests a well-organized threat actor. Overall confidence in this assessment is moderate, given the detailed but potentially incomplete data.
2. Competing Hypotheses
- Hypothesis A: The ClickFix attack is orchestrated by a financially motivated cybercriminal group targeting high-value tech professionals to steal sensitive credentials and financial data. Supporting evidence includes the use of stolen advertising accounts and sophisticated malware. However, the exact identity and origin of the group remain uncertain.
- Hypothesis B: The attack is part of a broader state-sponsored cyber-espionage campaign aimed at infiltrating tech companies for strategic advantage. This is less supported due to the financial nature of the data targeted and lack of direct state involvement indicators.
- Assessment: Hypothesis A is currently better supported due to the financial targeting and use of stolen advertising accounts, which align with typical cybercriminal activities. Indicators such as targeting of strategic data or geopolitical tensions could shift this judgment towards Hypothesis B.
3. Key Assumptions and Red Flags
- Assumptions: The attackers are primarily financially motivated; developers and security experts are the main targets; the malware’s primary function is credential theft.
- Information Gaps: The identity and location of the threat actors; the full scope of the campaign’s impact; potential connections to other known cybercriminal groups.
- Bias & Deception Risks: Potential bias in source reporting due to reliance on a single research team; deception risk from attackers using legitimate platforms to host malicious content.
4. Implications and Strategic Risks
This development could lead to increased scrutiny and regulation of online advertising and AI tool distribution. It may also prompt tech companies to enhance security measures and user awareness.
- Political / Geopolitical: Potential for international cooperation in cybercrime investigations if cross-border elements are identified.
- Security / Counter-Terrorism: Increased threat to tech sector security, necessitating enhanced cybersecurity protocols.
- Cyber / Information Space: Highlights vulnerabilities in digital advertising and AI tool ecosystems, possibly leading to new security standards.
- Economic / Social: Potential financial losses for affected companies and individuals; erosion of trust in AI tools and online platforms.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Increase monitoring of online ads for malicious content; conduct awareness campaigns for developers and IT professionals.
- Medium-Term Posture (1–12 months): Develop partnerships with tech companies to improve ad vetting processes; invest in advanced threat detection capabilities.
- Scenario Outlook: Best: Rapid identification and dismantling of the threat actor group; Worst: Expansion of the campaign to broader targets; Most-Likely: Continued targeting of tech professionals with gradual improvements in detection and prevention.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, malware, cybercrime, AI tools, digital advertising, macOS, Windows systems
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us