Interlock Ransomware Leverages Cisco FMC Zero-Day CVE-2026-20131 for Unauthorized Root Access
Published on: 2026-03-18
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Interlock Ransomware Exploits Cisco FMC Zero-Day CVE-2026-20131 for Root Access
1. BLUF (Bottom Line Up Front)
The Interlock ransomware group has exploited a critical zero-day vulnerability in Cisco Secure Firewall Management Center software, potentially impacting numerous organizations globally. This exploitation allows for unauthorized root access, posing significant security risks. The most likely hypothesis is that the group aims to leverage this access for widespread ransomware deployment. Overall confidence in this assessment is moderate due to limited visibility into the full scope of affected entities.
2. Competing Hypotheses
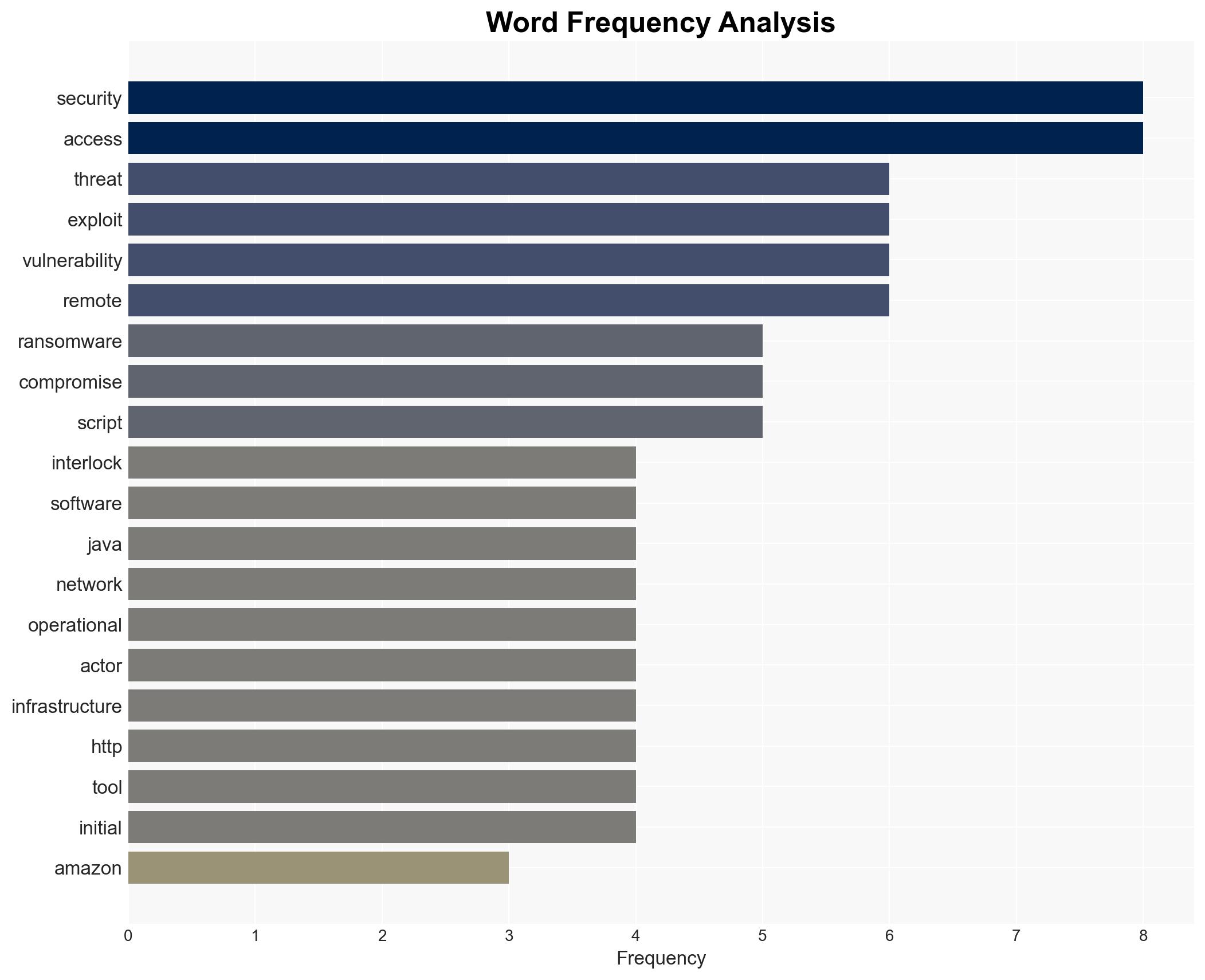
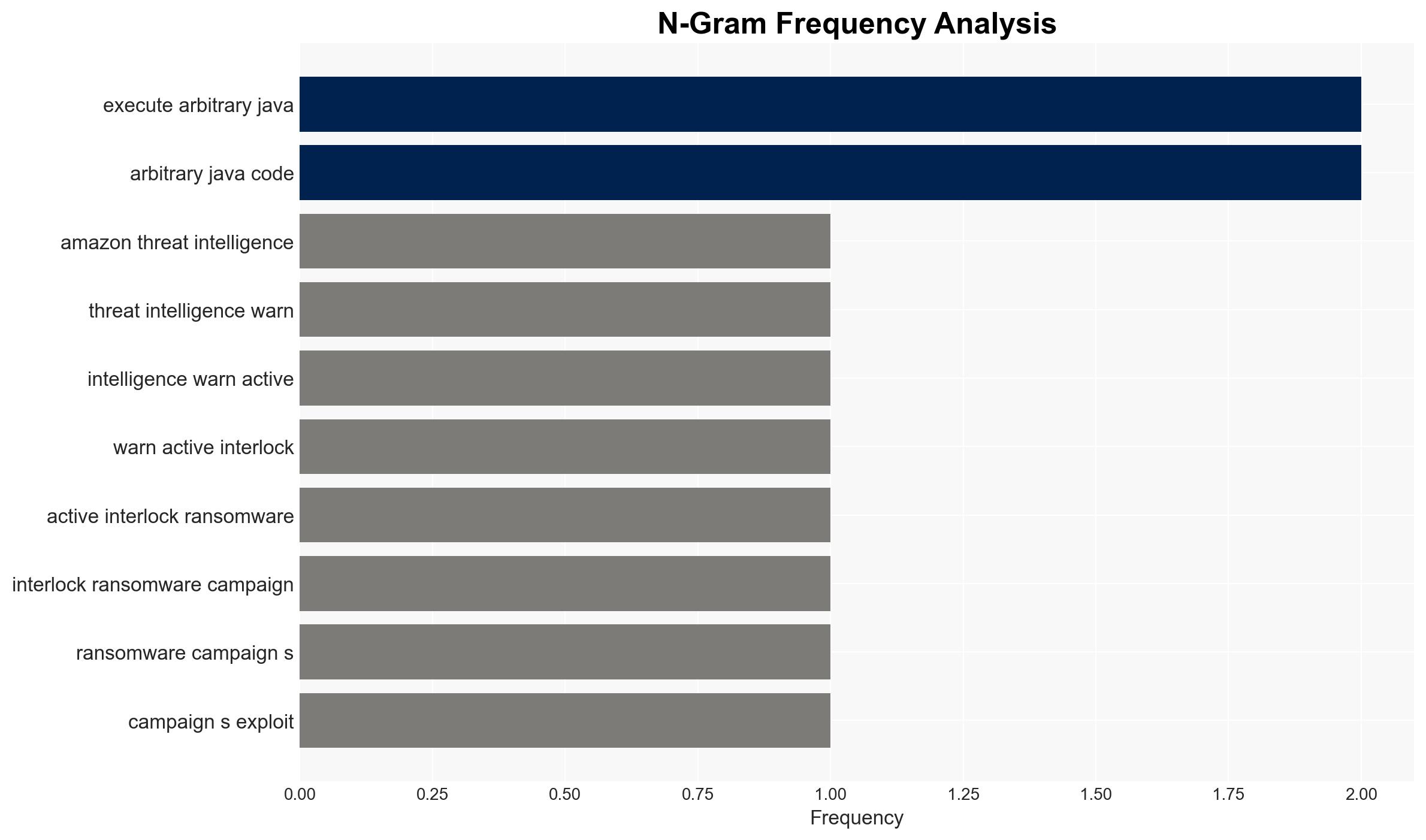
- Hypothesis A: Interlock ransomware is primarily using the zero-day exploit to gain root access for ransomware deployment. This is supported by the detailed attack chain and tools identified, including reconnaissance and remote access capabilities. Key uncertainties include the full extent of compromised systems and whether financial gain is the sole motive.
- Hypothesis B: The exploitation is part of a broader cyber-espionage campaign, with ransomware deployment serving as a cover. This hypothesis is less supported due to the operational focus on ransomware tools and the absence of evidence pointing to data exfiltration or espionage activities.
- Assessment: Hypothesis A is currently better supported due to the nature of the tools and attack chain identified, which align with ransomware operations. Indicators such as a shift towards data exfiltration or targeting of specific high-value entities could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The vulnerability affects a significant number of Cisco FMC deployments; Interlock’s primary motive is financial gain; the zero-day was unknown to Cisco prior to disclosure.
- Information Gaps: Precise number of affected organizations; detailed timeline of Interlock’s access and activities; potential secondary motives beyond ransomware.
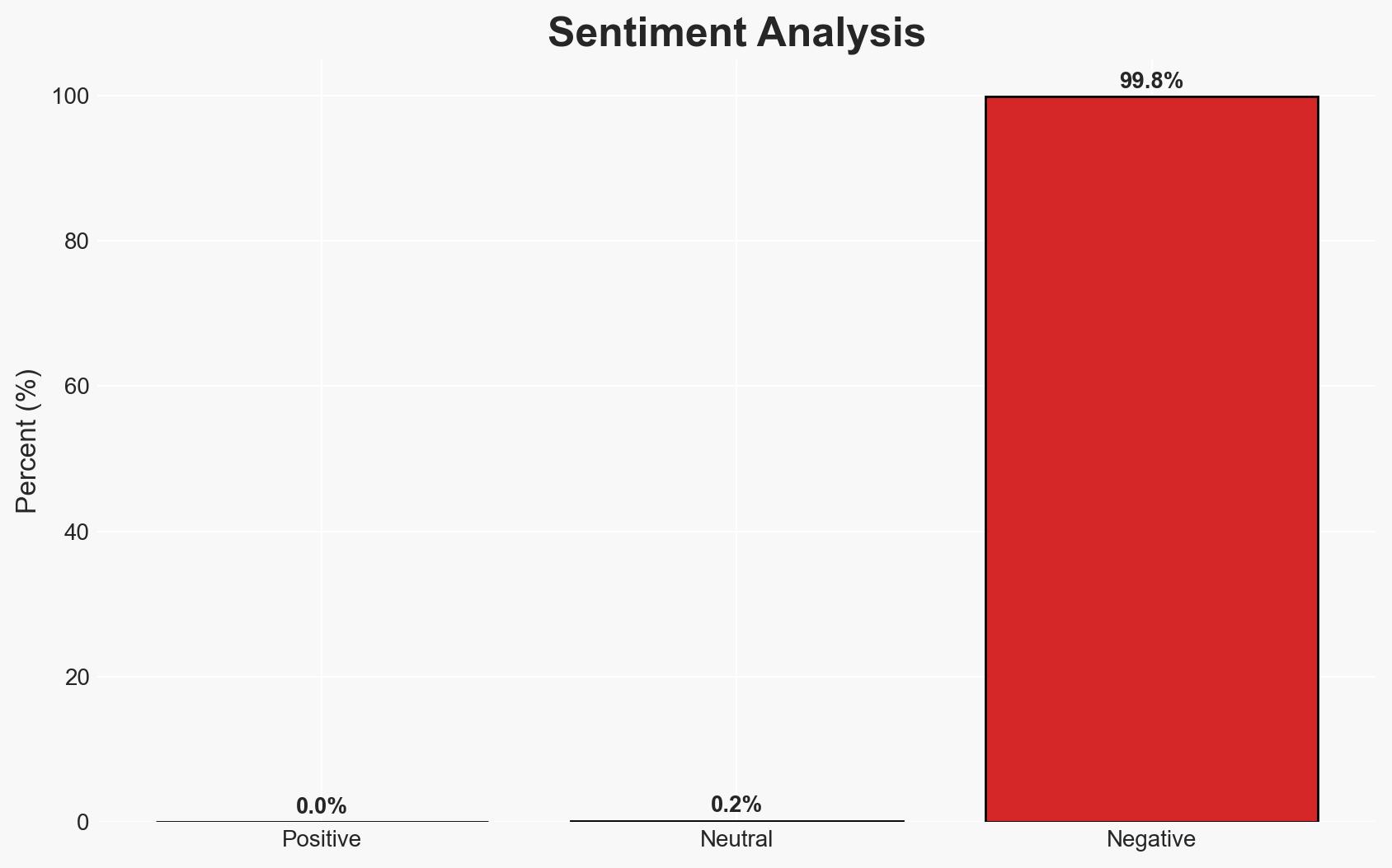
- Bias & Deception Risks: Potential bias in reporting from Amazon Threat Intelligence; risk of Interlock using deception to obscure true motives or targets.
4. Implications and Strategic Risks
The exploitation of this zero-day vulnerability by Interlock could lead to increased ransomware incidents, affecting organizational operations and data integrity. The broader implications could involve heightened scrutiny on Cisco’s security practices and increased demand for cybersecurity solutions.
- Political / Geopolitical: Potential diplomatic tensions if state actors are suspected of involvement or if critical infrastructure is impacted.
- Security / Counter-Terrorism: Increased threat level for organizations using Cisco FMC, necessitating enhanced defensive measures.
- Cyber / Information Space: Potential for increased cyber threat activity as other groups may exploit similar vulnerabilities.
- Economic / Social: Economic impact on affected organizations, potential loss of consumer trust, and increased cybersecurity insurance costs.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Urgently patch affected systems; enhance monitoring for signs of exploitation; share threat intelligence with relevant stakeholders.
- Medium-Term Posture (1–12 months): Develop resilience measures, including regular security audits and staff training; strengthen partnerships with cybersecurity firms for threat intelligence sharing.
- Scenario Outlook:
- Best: Rapid patching and response contain the threat with minimal impact.
- Worst: Widespread exploitation leads to significant operational disruptions and financial losses.
- Most-Likely: Continued exploitation attempts with varying degrees of success, leading to increased cybersecurity awareness and investment.
6. Key Individuals and Entities
- CJ Moses, Chief Information Security Officer, Amazon Integrated Security
- Interlock Ransomware Group
- Cisco Systems
7. Thematic Tags
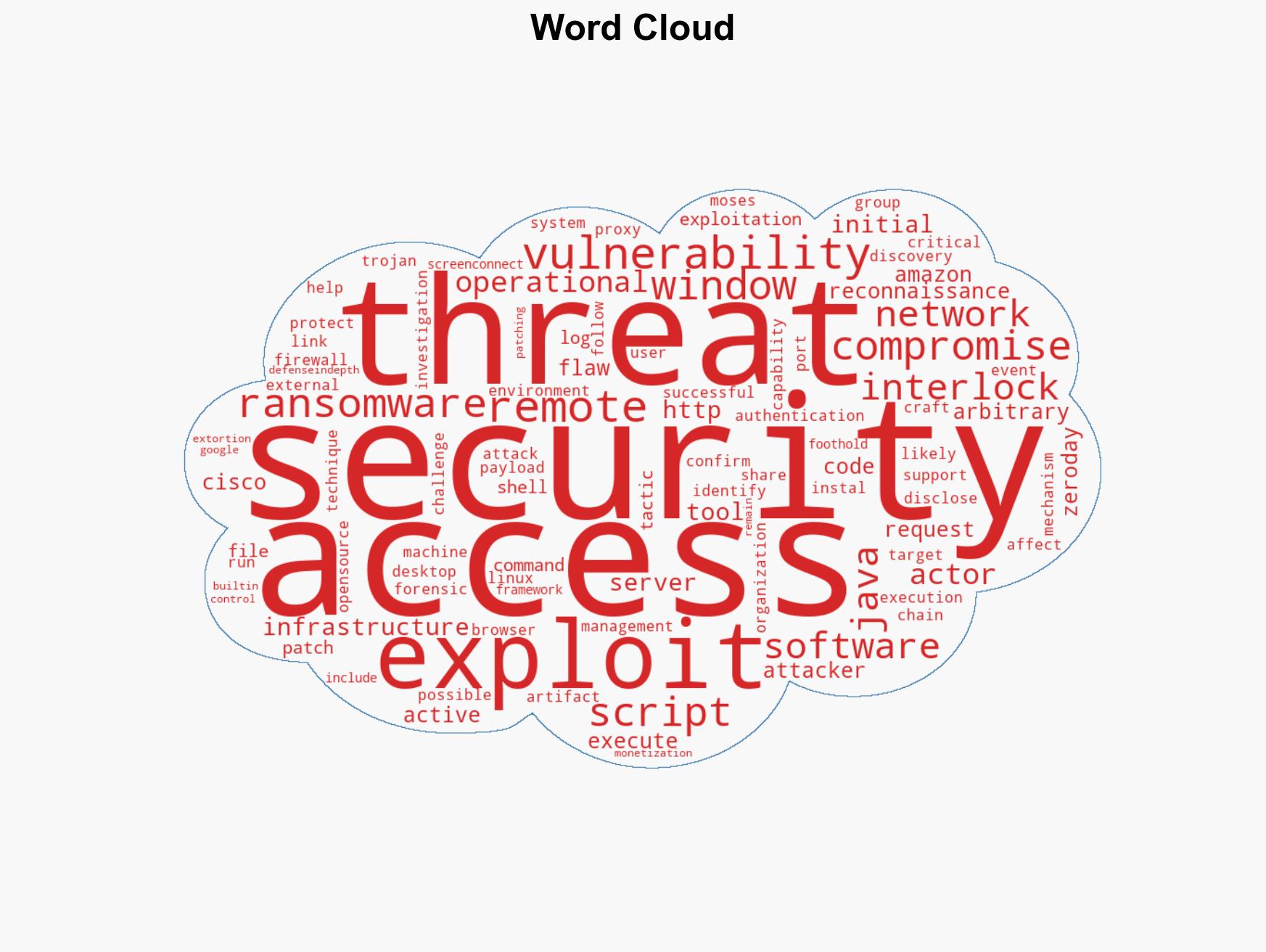
cybersecurity, ransomware, zero-day vulnerability, Cisco, threat intelligence, cybercrime, information security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us