The Importance of Monitoring Internal Traffic for Electric Grid Cybersecurity
Published on: 2026-03-18
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Why East-West Visibility Matters for Grid Security
1. BLUF (Bottom Line Up Front)
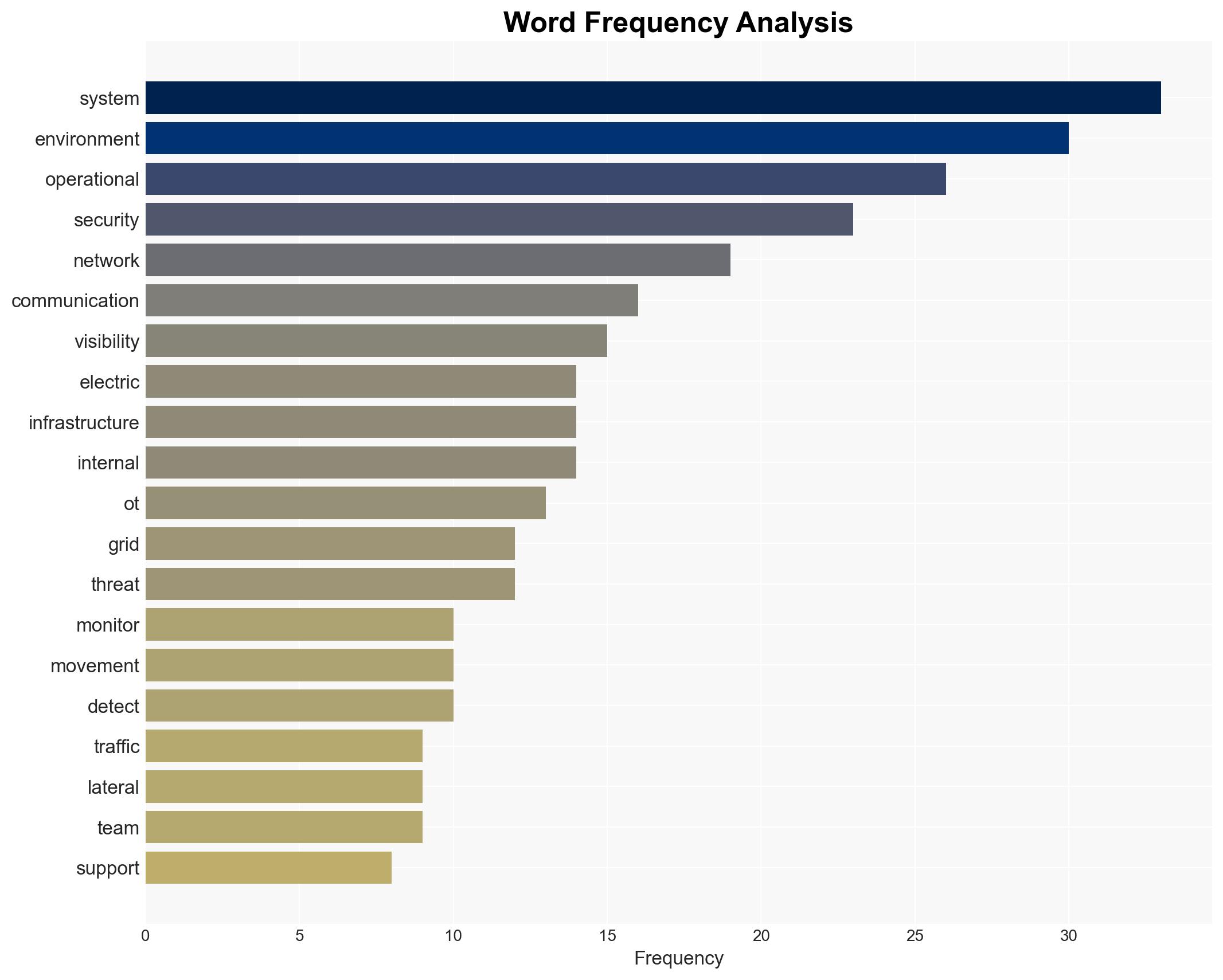
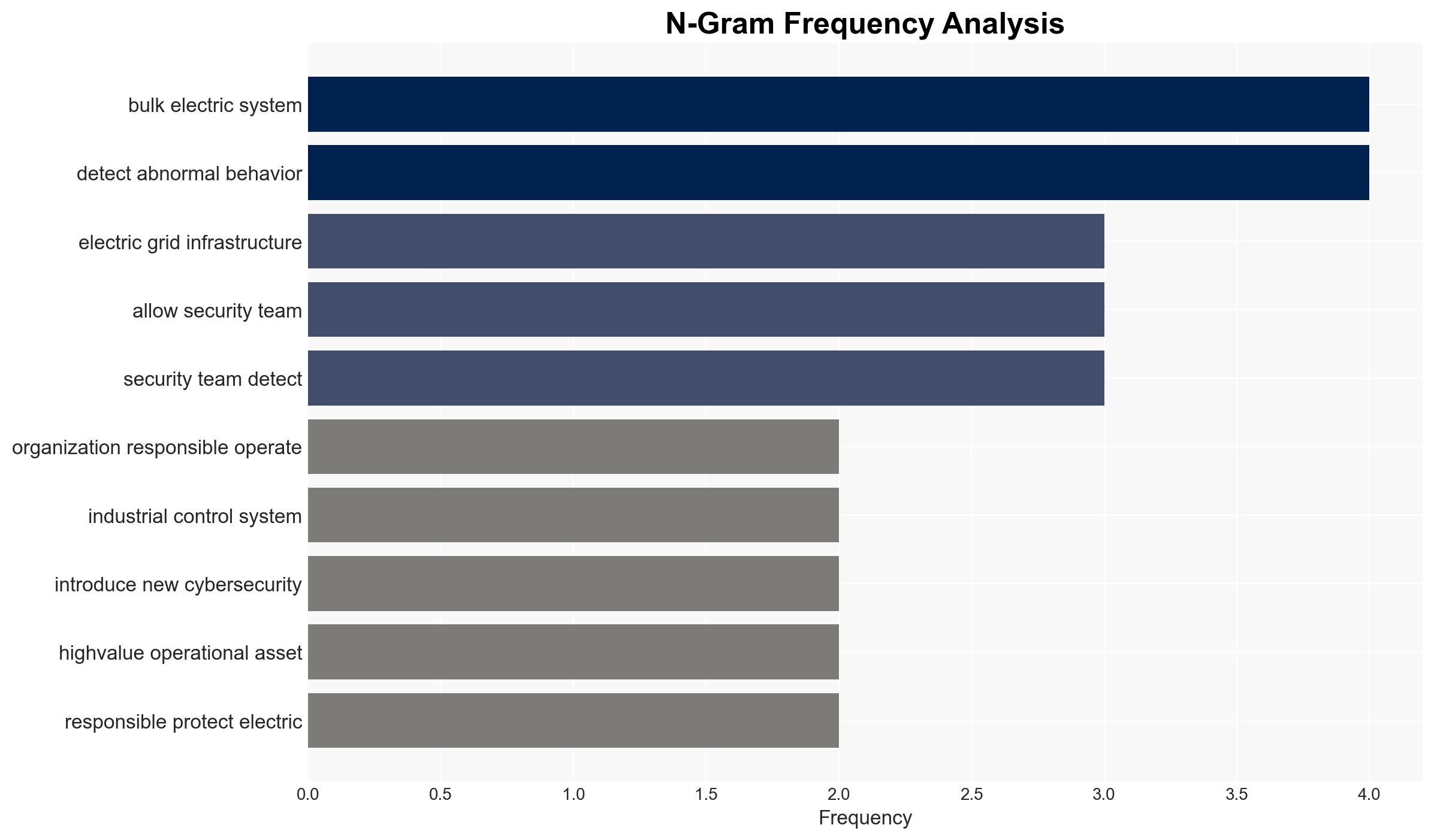
The integration of operational technology and IT systems in electric grid infrastructure increases cybersecurity risks, particularly from lateral movement by attackers. Enhanced visibility into east-west traffic is crucial for mitigating these risks. This development affects electric grid operators and regulatory bodies, with moderate confidence in the assessment due to existing information gaps and potential biases.
2. Competing Hypotheses
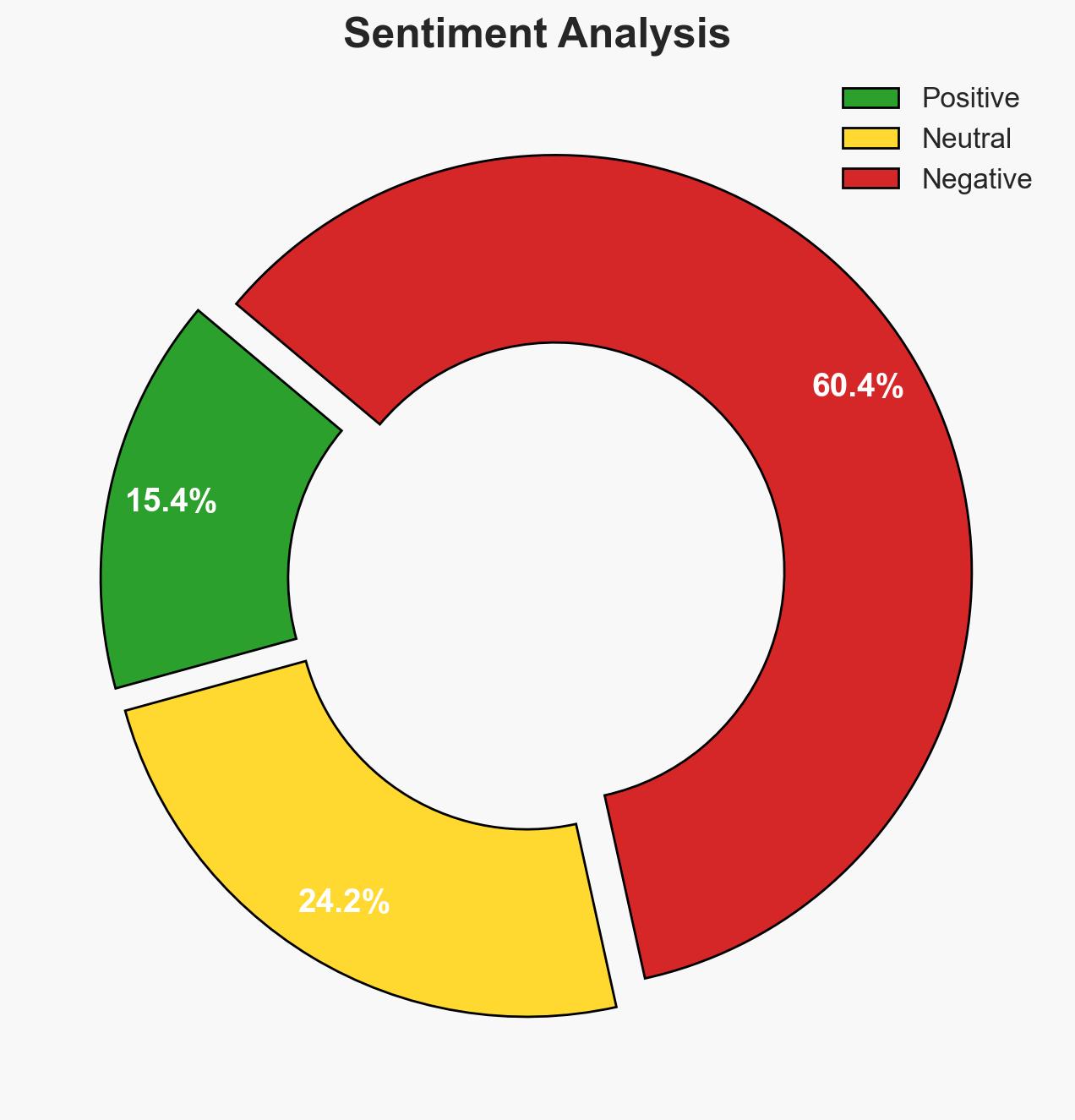
- Hypothesis A: The increased connectivity and integration of OT and IT systems in electric grids significantly elevate the risk of cyber intrusions and lateral movement by attackers, necessitating enhanced internal monitoring. This is supported by the complexity and interconnectivity of modern grid systems, but lacks detailed incident data.
- Hypothesis B: Despite increased connectivity, existing cybersecurity measures and regulatory frameworks are sufficient to manage the risks associated with lateral movement in electric grids. This is contradicted by the evolving threat landscape and the integration of legacy systems with modern IT.
- Assessment: Hypothesis A is currently better supported due to the documented challenges of integrating legacy systems with modern IT and the known vulnerabilities in interconnected systems. Indicators such as increased cyber incidents or regulatory changes could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The integration of OT and IT systems will continue; attackers have the capability to exploit these integrations; regulatory frameworks will adapt to emerging threats.
- Information Gaps: Specific data on recent breaches and the effectiveness of current monitoring solutions are lacking.
- Bias & Deception Risks: Potential bias in reporting from cybersecurity vendors and the possibility of underreported incidents by operators.
4. Implications and Strategic Risks
The evolving cyber threat landscape could lead to increased regulatory scrutiny and investment in cybersecurity measures. This development might influence broader geopolitical dynamics, particularly in regions reliant on interconnected grid systems.
- Political / Geopolitical: Potential for increased international cooperation or conflict over cybersecurity standards and practices.
- Security / Counter-Terrorism: Heightened risk of cyber-attacks on critical infrastructure, necessitating enhanced security protocols.
- Cyber / Information Space: Increased focus on developing advanced monitoring and detection technologies to counter lateral movement threats.
- Economic / Social: Potential economic impacts from disruptions in power supply, affecting social stability and trust in infrastructure.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of east-west traffic, conduct vulnerability assessments, and review compliance with NERC CIP standards.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms, invest in training for grid operators, and update legacy systems.
- Scenario Outlook: Best: Improved cybersecurity posture with minimal incidents; Worst: Major breach causing widespread outages; Most-Likely: Incremental improvements with occasional minor incidents, triggered by regulatory changes or new threat intelligence.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
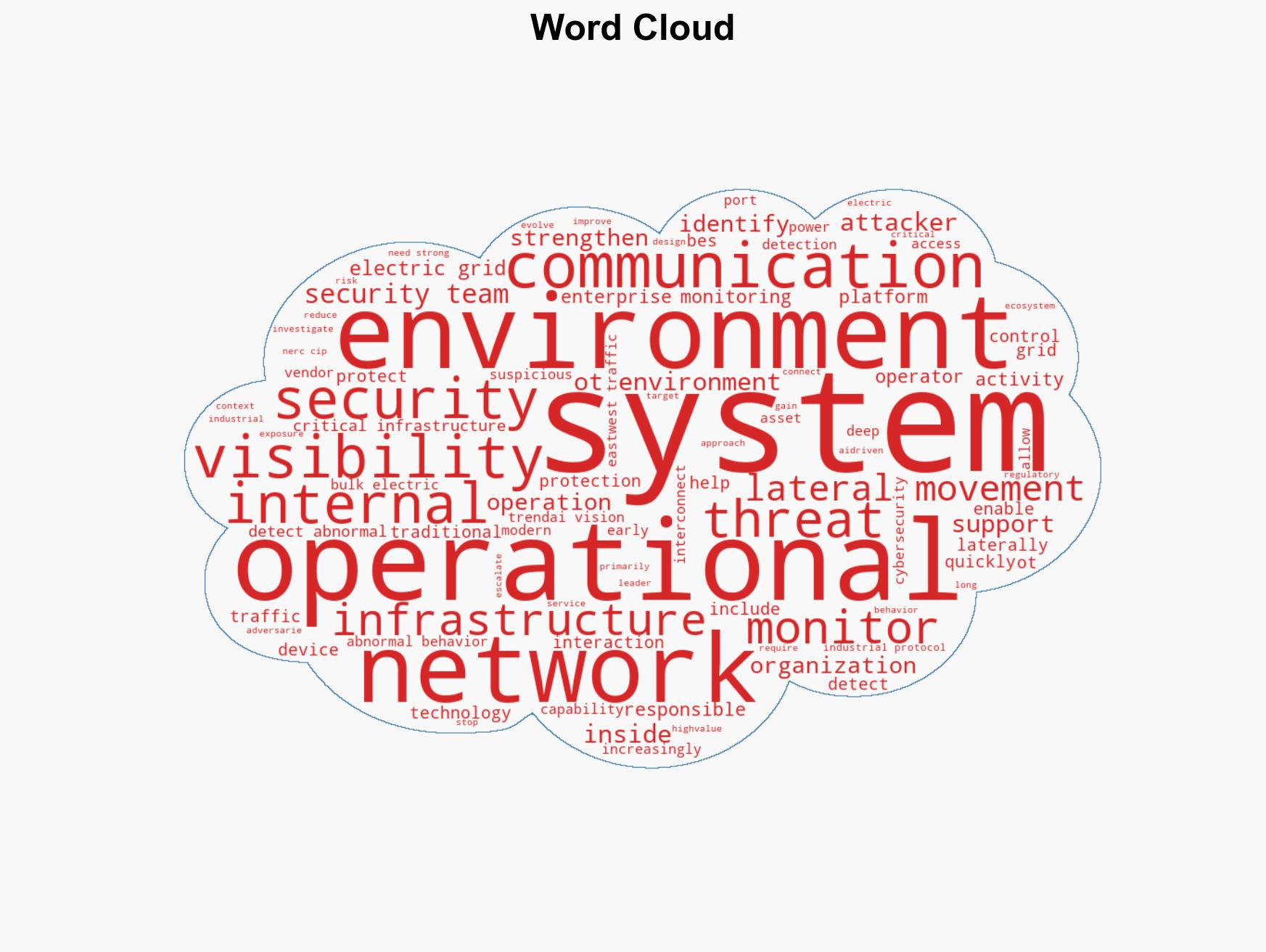
cybersecurity, electric grid, operational technology, lateral movement, regulatory compliance, critical infrastructure, cyber threats
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us