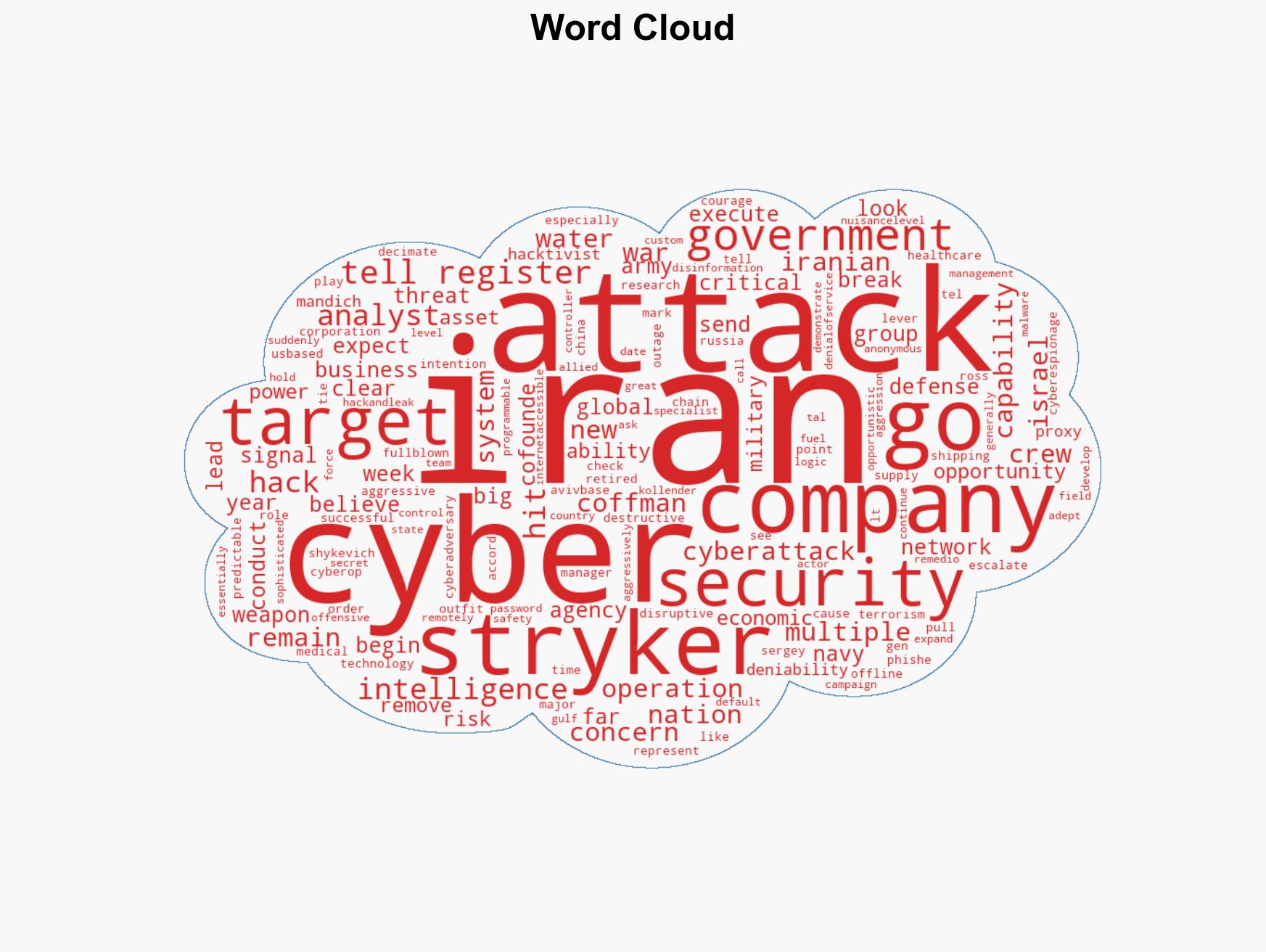
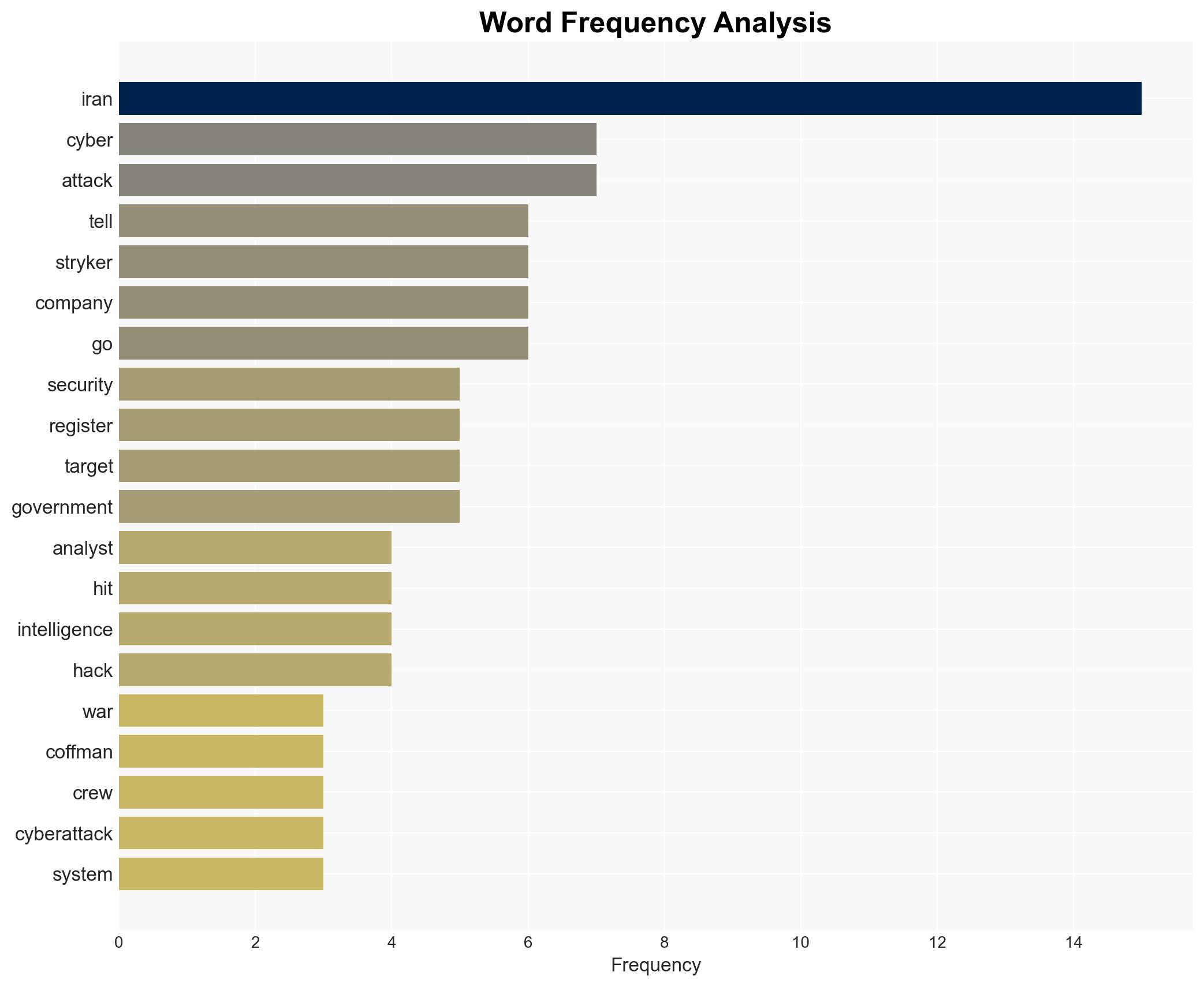
Iran’s Cyber Assault on Stryker Signals Escalation in Aggressive Operations Against U.S. Firms
Published on: 2026-03-18
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Iran’s cyberattack against med tech firm is ‘just the beginning’
1. BLUF (Bottom Line Up Front)
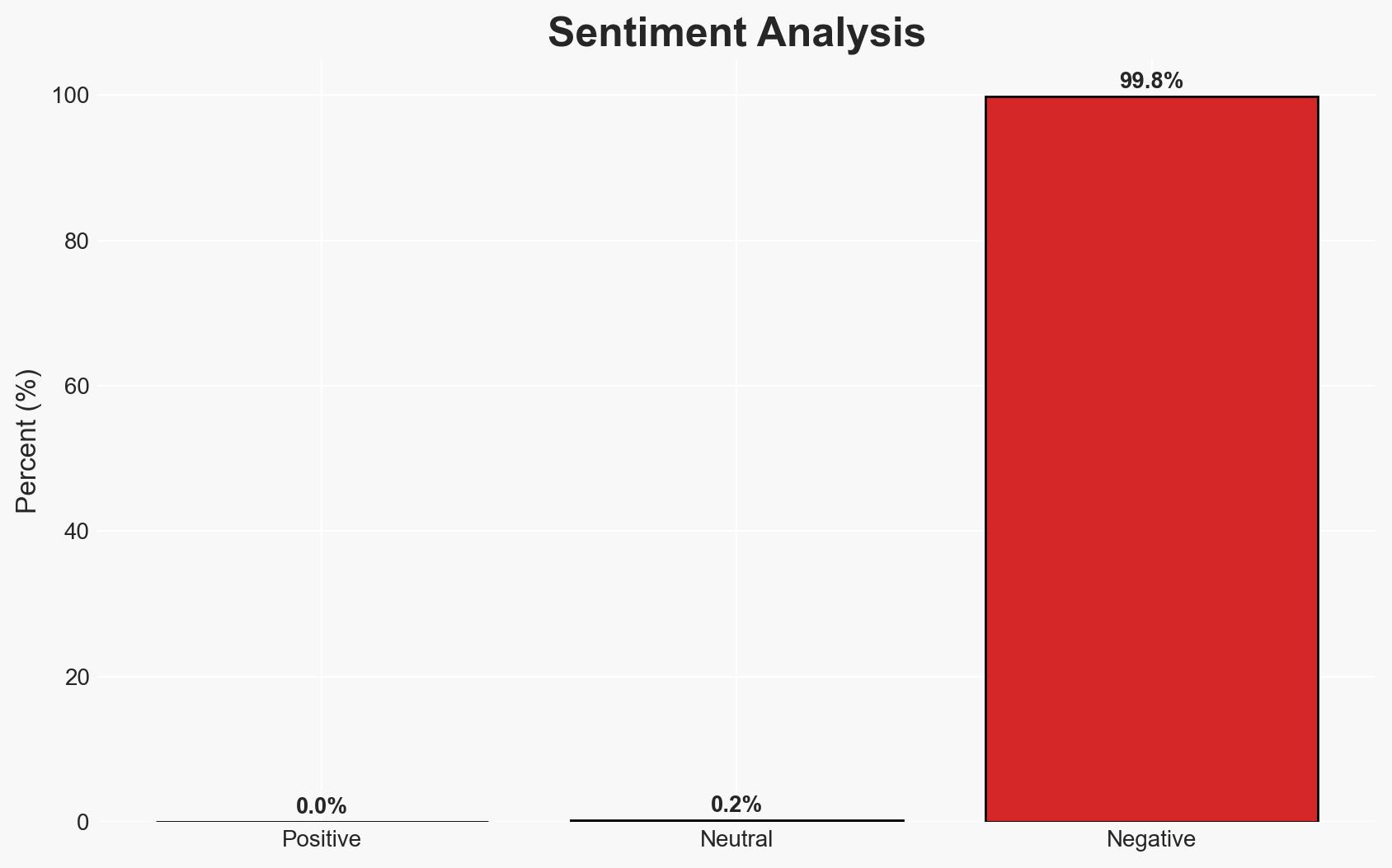
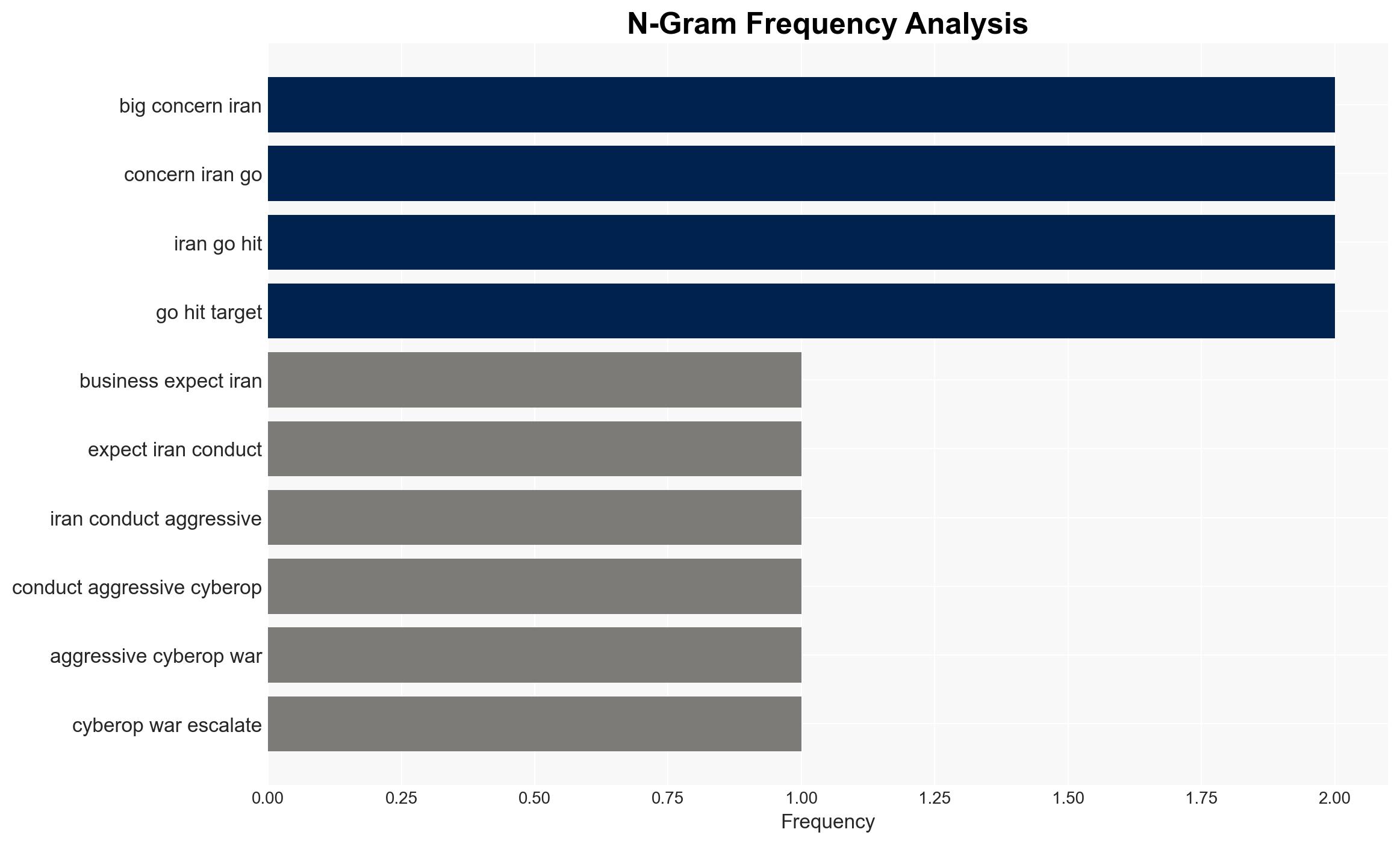
Iran’s recent cyberattack on a US-based medical technology firm signifies an escalation in its cyber operations, likely as a response to military setbacks. This attack highlights Iran’s intent to target critical infrastructure, with a moderate confidence level that similar operations will expand to other sectors and regions. The primary affected parties include US corporations and allied nations.
2. Competing Hypotheses
- Hypothesis A: Iran’s cyberattack on Stryker is a strategic shift towards more aggressive and destructive cyber operations targeting critical infrastructure. Supporting evidence includes the attack’s timing following military losses and its impact on healthcare supply chains. Contradicting evidence is Iran’s historically opportunistic cyber behavior.
- Hypothesis B: The attack on Stryker is an isolated incident, not indicative of a broader strategic shift, but rather a continuation of Iran’s opportunistic cyber tactics. Supporting evidence includes Iran’s past cyber activities and the lack of sophistication in the attack. Contradicting evidence is the scale and impact of the attack, suggesting a potential strategic pivot.
- Assessment: Hypothesis A is currently better supported due to the strategic nature of the target and the timing of the attack. Key indicators that could shift this judgment include evidence of similar attacks on other critical infrastructure or increased sophistication in future operations.
3. Key Assumptions and Red Flags
- Assumptions: Iran has the capability and intent to conduct further cyberattacks; Iran perceives cyber operations as a viable tool to counter military disadvantages; US and allied critical infrastructure remain vulnerable to such attacks.
- Information Gaps: Detailed intelligence on Iran’s cyber capabilities and strategic objectives; confirmation of Iranian state involvement in the Stryker attack; potential targets of future operations.
- Bias & Deception Risks: Potential overestimation of Iran’s capabilities due to source bias; underestimation of Iran’s strategic restraint due to cognitive biases; possibility of Iran using deception to mask true capabilities or intentions.
4. Implications and Strategic Risks
This development could lead to increased tensions and cyber conflict escalation, potentially drawing in more state and non-state actors.
- Political / Geopolitical: Potential for increased geopolitical tensions between Iran and the US, with possible spillover effects in the Gulf region.
- Security / Counter-Terrorism: Heightened threat environment for US and allied critical infrastructure, necessitating increased cybersecurity measures.
- Cyber / Information Space: Potential for more sophisticated cyberattacks and increased cyber defense posturing by targeted nations.
- Economic / Social: Disruption of critical supply chains, particularly in healthcare, could impact economic stability and public trust.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of critical infrastructure networks; increase information sharing between government and private sectors; conduct vulnerability assessments.
- Medium-Term Posture (1–12 months): Develop resilience measures and incident response plans; strengthen international partnerships to counter cyber threats; invest in cybersecurity capabilities.
- Scenario Outlook:
- Best Case: Iran refrains from further escalation, and diplomatic efforts lead to de-escalation.
- Worst Case: Iran conducts multiple high-impact cyberattacks, leading to significant geopolitical tensions.
- Most-Likely: Continued sporadic cyberattacks targeting critical infrastructure, with moderate impact.
6. Key Individuals and Entities
- Retired US Army Lt. Gen. Ross Coffman
- Stryker Corporation
- Sergey Shykevich, Check Point Research
- Tal Kollender, Remedio
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, Iran, critical infrastructure, cyber-espionage, geopolitical tensions, healthcare supply chain
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us