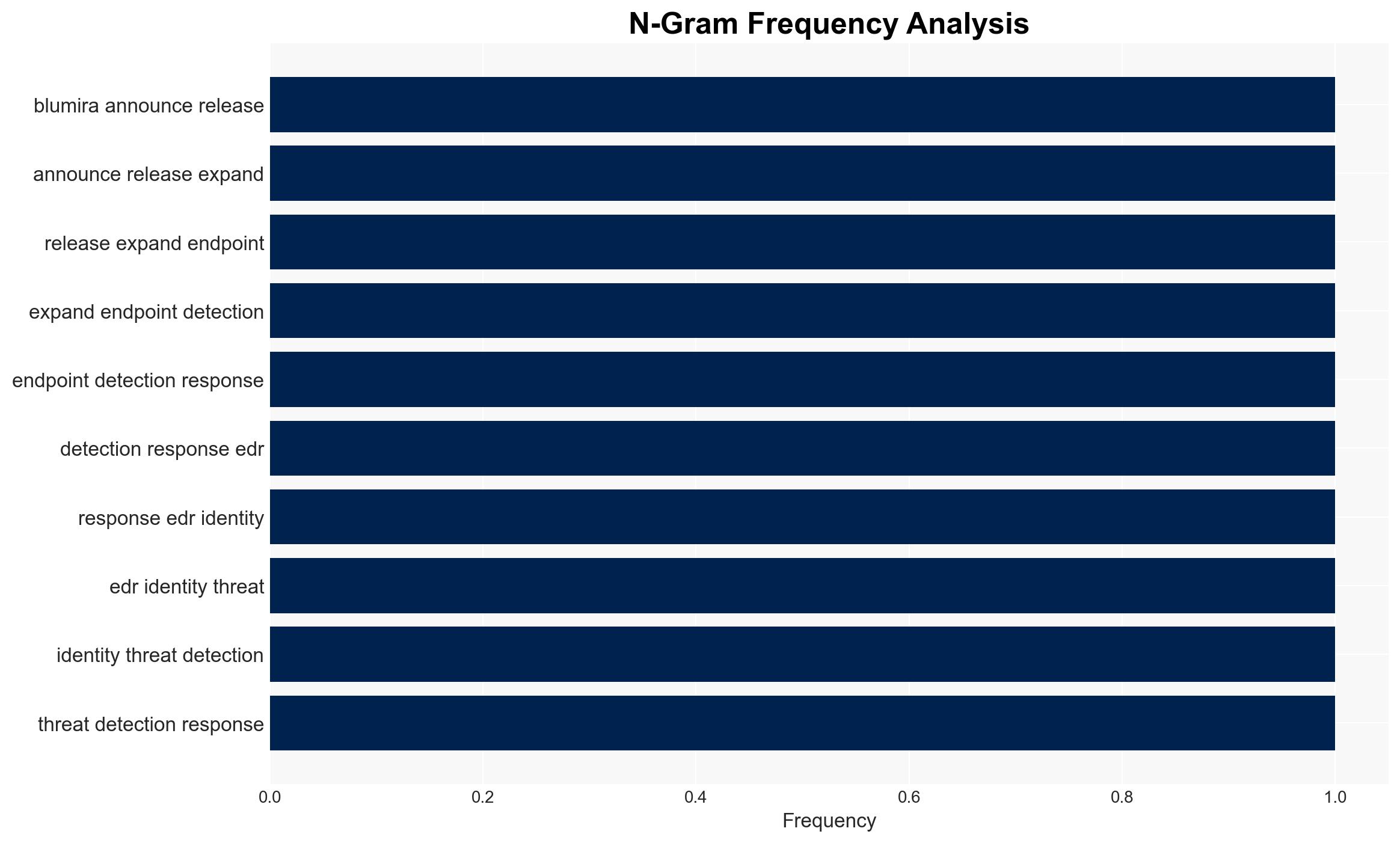
Blumira Introduces Enhanced EDR and ITDR Features for Faster Threat Response and Mitigation
Published on: 2026-03-18
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Blumira enhances EDR and ITDR to speed up threat detection and containment
1. BLUF (Bottom Line Up Front)
Blumira’s enhancement of its EDR and ITDR capabilities is likely to improve threat detection and containment efficiency, particularly against ransomware and identity-based attacks. This development primarily affects IT security teams and managed service providers (MSPs) by streamlining incident response processes. Overall, there is moderate confidence in the assessment that these enhancements will reduce breach response times and improve security posture.
2. Competing Hypotheses
- Hypothesis A: Blumira’s enhancements will significantly improve threat detection and containment, reducing the impact of cyber threats. This is supported by the integration of EDR and ITDR capabilities into a unified platform, which streamlines response processes. However, the effectiveness of these enhancements depends on the actual deployment and user adaptation, which remains uncertain.
- Hypothesis B: The enhancements may have limited impact due to potential integration challenges and user resistance to adopting new workflows. While the unified platform offers theoretical benefits, real-world application may face hurdles such as existing infrastructure compatibility and user training requirements.
- Assessment: Hypothesis A is currently better supported due to the reported improvements in response times and user testimonials. Key indicators that could shift this judgment include reports of integration issues or lack of user adoption.
3. Key Assumptions and Red Flags
- Assumptions: Blumira’s platform is compatible with existing IT infrastructure; Users will effectively adopt the new capabilities; Ransomware and identity-based attacks will remain prevalent threats.
- Information Gaps: Detailed user feedback on the deployment process and integration challenges; Quantitative data on the reduction in breach incidents post-implementation.
- Bias & Deception Risks: Potential bias in user testimonials due to vested interests; Over-reliance on vendor-reported improvements without independent verification.
4. Implications and Strategic Risks
This development could lead to broader adoption of integrated security platforms, influencing industry standards and competitive dynamics. However, it may also prompt adversaries to adapt their tactics, potentially escalating the cyber threat landscape.
- Political / Geopolitical: Limited direct implications, but could influence national cybersecurity policy priorities.
- Security / Counter-Terrorism: Enhanced detection and response capabilities may deter certain cyber threat actors, altering the threat environment.
- Cyber / Information Space: Potential shift towards more sophisticated cyber threats as adversaries adapt to improved defenses.
- Economic / Social: Improved security could enhance business continuity and trust in digital services, but may require investment in training and infrastructure upgrades.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor user feedback and integration outcomes; Engage with Blumira for detailed deployment guidance.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity vendors; Invest in training for IT teams to maximize platform benefits.
- Scenario Outlook: Best: Enhanced security posture reduces breach incidents; Worst: Integration challenges limit effectiveness; Most-Likely: Gradual improvement in response times with ongoing adaptation.
6. Key Individuals and Entities
- Matt Warner, CEO of Blumira
- Matt Timm, Network Operations Center Team Lead at TR Computer Sales
- Blumira
- TR Computer Sales
- Verizon (referenced in DBIR 2025 report)
7. Thematic Tags
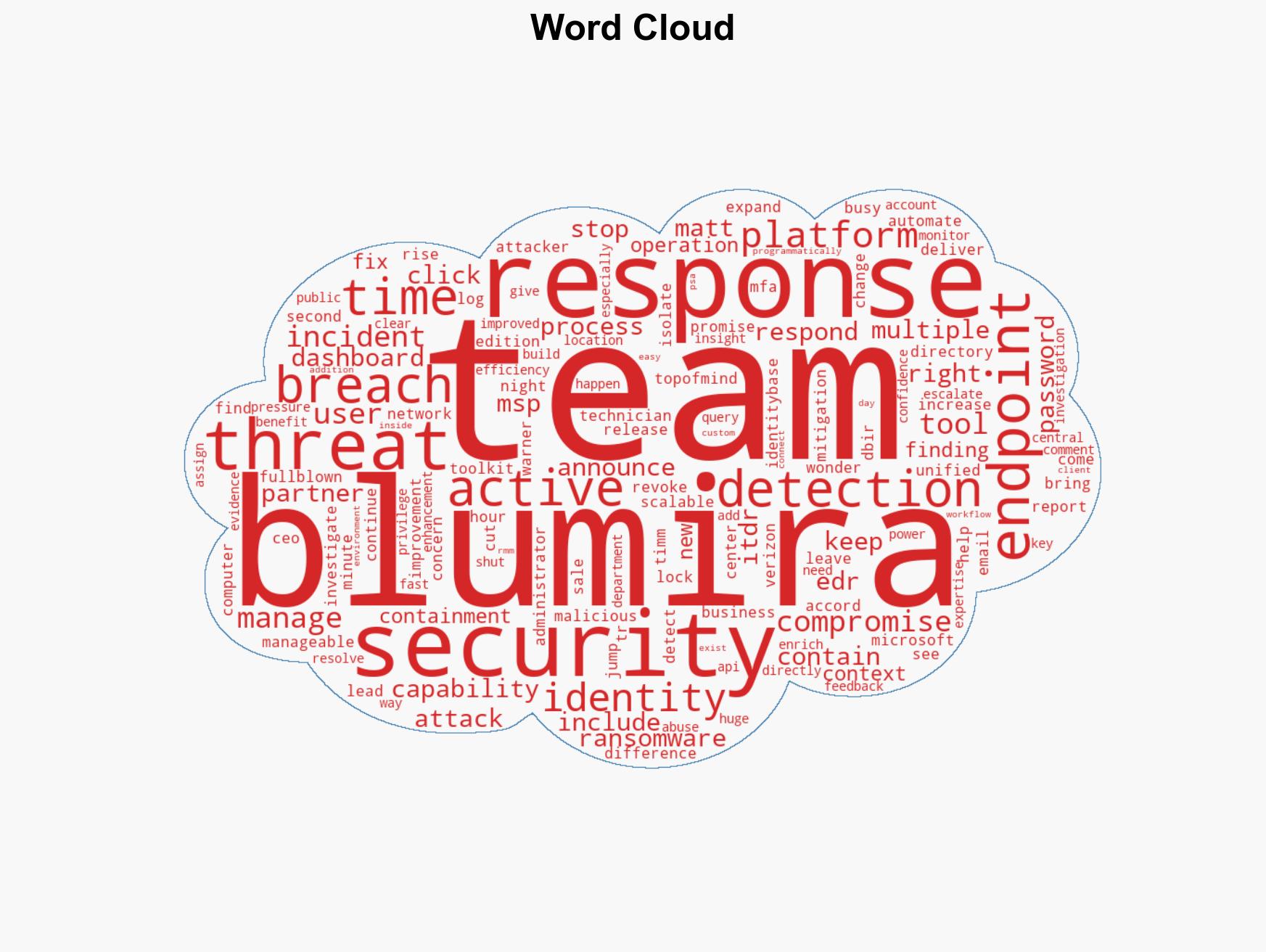
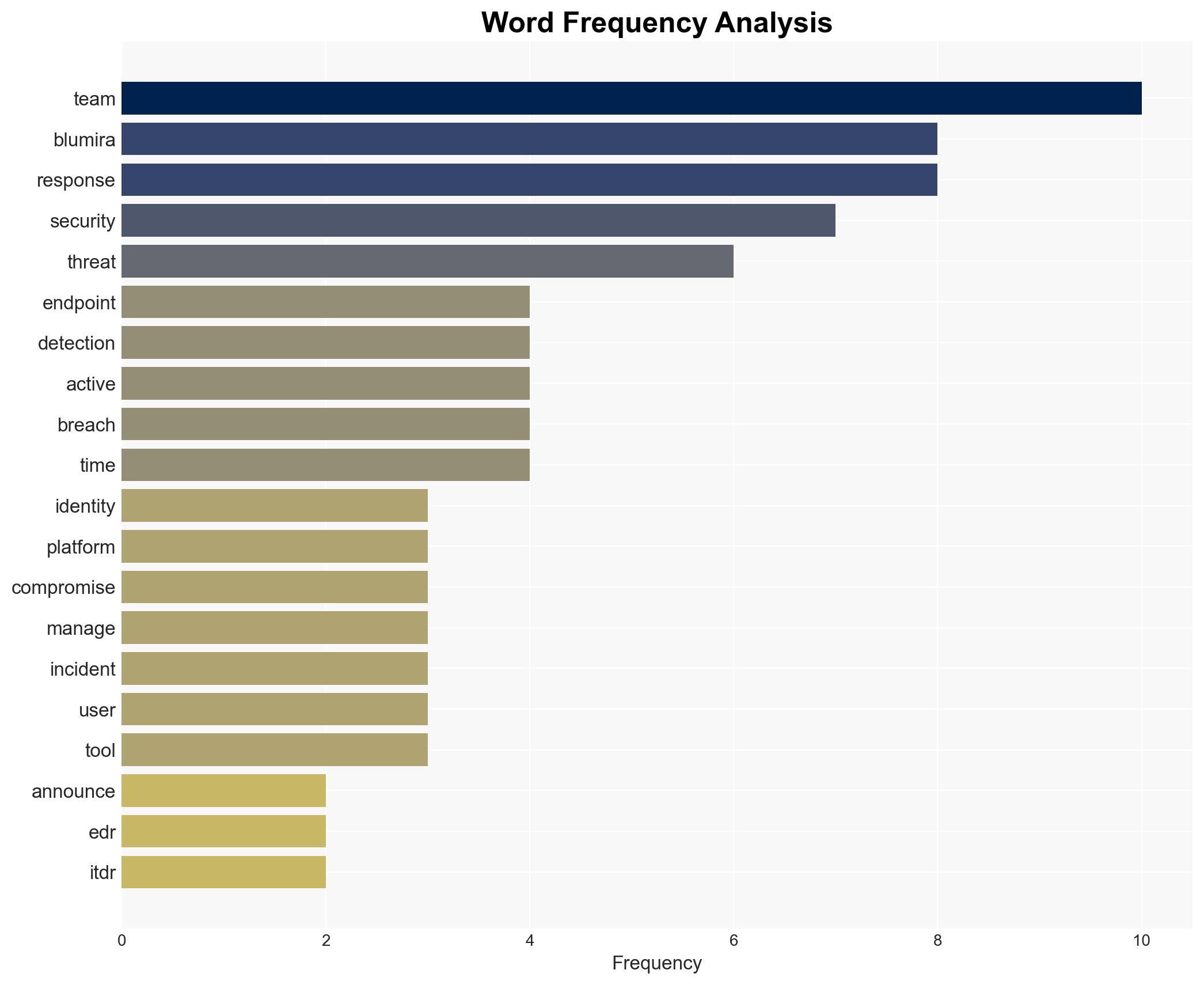
cybersecurity, threat detection, ransomware, identity-based attacks, EDR, ITDR, incident response
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us