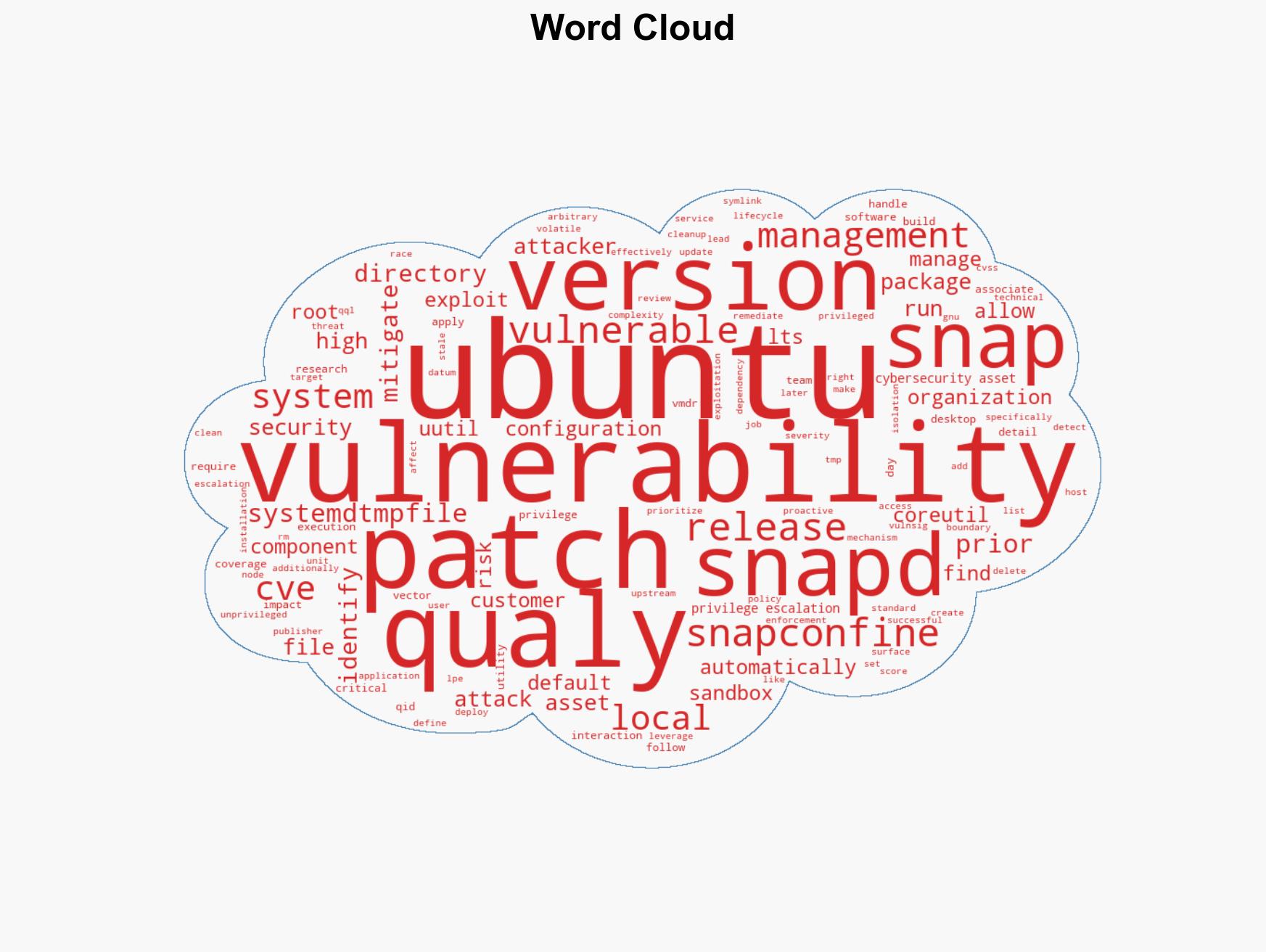
Local Privilege Escalation Vulnerability Discovered in Ubuntu Desktop Versions 24.04 and Later
Published on: 2026-03-18
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: CVE-2026-3888 Important Snap Flaw Enables Local Privilege Escalation to Root
1. BLUF (Bottom Line Up Front)
The CVE-2026-3888 vulnerability in Ubuntu Desktop versions 24.04 and later allows local privilege escalation to root, posing a significant security risk. The most likely hypothesis is that this vulnerability will be actively exploited by threat actors targeting Ubuntu systems. This assessment is made with moderate confidence due to the technical complexity of the exploit and the specific timing required for successful execution.
2. Competing Hypotheses
- Hypothesis A: The vulnerability will be actively exploited by cybercriminals and state-sponsored actors due to its potential to provide root access. Supporting evidence includes the critical nature of the flaw and the widespread use of Ubuntu systems. However, the requirement for a specific timing window may limit exploitation opportunities.
- Hypothesis B: The vulnerability will have limited exploitation due to the technical complexity and timing constraints involved. Contradicting evidence includes the high skill level required to exploit the flaw and the potential for rapid patch deployment by affected organizations.
- Assessment: Hypothesis A is currently better supported due to the high value of root access on Ubuntu systems for malicious actors. Indicators that could shift this judgment include the release of a widely available exploit tool or increased patch adoption rates.
3. Key Assumptions and Red Flags
- Assumptions:
- Organizations will not immediately patch the vulnerability.
- Threat actors have the capability to exploit the vulnerability within the timing window.
- Ubuntu systems are a valuable target for cybercriminals.
- Information Gaps: The exact number of systems vulnerable to CVE-2026-3888 and the speed of patch deployment across affected networks.
- Bias & Deception Risks: Potential bias in overestimating the capability of threat actors to exploit the vulnerability; reliance on vendor-provided information may overlook undisclosed vulnerabilities.
4. Implications and Strategic Risks
This vulnerability could lead to significant security breaches if exploited, affecting multiple domains over time.
- Political / Geopolitical: Potential for increased tensions if state-sponsored actors are implicated in exploiting the vulnerability.
- Security / Counter-Terrorism: Heightened risk of cyber-attacks on critical infrastructure and sensitive data breaches.
- Cyber / Information Space: Increased activity in the cyber threat landscape, with potential for new attack vectors and tools.
- Economic / Social: Potential financial losses for affected organizations and erosion of trust in open-source software security.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Urgently patch affected systems, monitor for signs of exploitation, and increase awareness among IT staff.
- Medium-Term Posture (1–12 months): Develop resilience measures, enhance partnerships with cybersecurity entities, and invest in capability development for vulnerability management.
- Scenario Outlook:
- Best Case: Rapid patch deployment mitigates most risks, with minimal exploitation.
- Worst Case: Widespread exploitation leads to significant data breaches and operational disruptions.
- Most-Likely: Moderate exploitation occurs, with some organizations failing to patch promptly.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, vulnerability management, open-source software, privilege escalation, Ubuntu, threat intelligence, patch management
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us